Comprehensive Threat Exposure Management Platform
A vulnerability scanner tells you where the cracks are in your defenses, but it doesn’t tell you which ones an attacker will actually use. To truly understand your exposure, you need to see your network from their perspective. How can a low-severity flaw on one server be combined with a misconfiguration on another to create a path to your crown jewels? Answering this question is the difference between a reactive and a proactive security strategy. This is where a risk-based vulnerability management platform becomes essential, integrating threat intelligence and attack simulation to reveal hidden attack paths and validate your security controls against real-world threats.
Risk-based vulnerability management (RBVM) is a smarter way to handle security flaws. Instead of treating every vulnerability as a five-alarm fire, this approach helps you focus on the ones that pose a genuine threat to your organization. It moves beyond just technical severity scores to consider the bigger picture: Is a vulnerability being actively exploited? How critical is the affected asset to your business? What would the impact of a breach be? By answering these questions, you can prioritize your team’s time and resources on fixing the issues that truly matter, turning a chaotic, reactive process into a proactive, strategic one.
This method is all about context. It combines data about your specific IT environment with real-world threat intelligence to create a prioritized to-do list. Think of it as a filter that cuts through the noise of thousands of alerts to show you the handful of vulnerabilities that attackers are most likely to target. This allows your security teams to work more efficiently, reduce the overall risk to the business, and stop wasting cycles on low-risk issues. It’s a fundamental shift from asking “Is it vulnerable?” to asking “Is it exploitable and a risk to us?”
A risk-based approach works by layering business context and threat intelligence on top of raw vulnerability data. It starts by understanding your unique environment, identifying your most critical assets, and mapping out your entire attack surface. Then, it pulls in external data, like information on which vulnerabilities are currently being used in active attack campaigns.
By combining these internal and external factors, the approach creates a dynamic risk score for each vulnerability. This score reflects the actual likelihood and potential impact of an exploit in your specific setting. This means a vulnerability with a “critical” CVSS score on a non-essential server might be ranked lower than a “high” severity vulnerability on a public-facing application that is being actively targeted. This contextual vulnerability and threat prioritization ensures your team is always working on the most urgent threats first.
The biggest difference between traditional and risk-based approaches lies in how they define “priority.” Traditional vulnerability management often relies heavily on static, generic metrics like the Common Vulnerability Scoring System (CVSS). While CVSS is a helpful starting point, it doesn’t account for real-world threat activity or the importance of the asset. This can lead to security teams facing a massive backlog of thousands of “critical” vulnerabilities, creating alert fatigue and making it impossible to know where to start.
A risk-based approach is far more dynamic. It enriches CVSS data with timely threat intelligence and business context. Instead of just seeing a score, you see the full story: this vulnerability is on a critical server, it’s being actively exploited by a known threat group, and we have no compensating controls in place. This transforms your vulnerability list from an overwhelming mountain of data into a clear, actionable roadmap for risk reduction.
A modern risk-based vulnerability management platform acts as your central command center for threat exposure. It should start by ingesting data from all your scanning tools to provide a complete and unified view of your total attack surface. This includes everything from your cloud environments and on-premise servers to your web applications and IoT devices.
The heart of the platform is its ability to correlate this asset and vulnerability data with high-fidelity threat intelligence. This intelligence provides the crucial context needed to accurately assess risk. Finally, a robust platform doesn’t just point out problems; it helps you solve them. It should offer clear remediation guidance and integrate with your existing IT and security workflows, like ticketing systems and patch management tools, to streamline the entire process from detection to resolution.
When you’re looking for a risk-based vulnerability management platform, it’s easy to get lost in a sea of features. But a few core capabilities truly separate the effective platforms from the rest. These features work together to give you a clear, continuous, and contextualized view of your risk, helping your team move from chasing every vulnerability to proactively reducing your real-world exposure. Let’s look at the key features you should expect from a modern platform.
You can’t protect what you don’t know you have. An effective platform begins with a complete and continuous inventory of every asset across your entire IT environment, from on-premise servers to cloud instances and remote endpoints. This automated discovery process is the foundation of a strong security program, providing a full picture of your total attack surface. By understanding every component of your unique environment, you can begin to assess vulnerabilities in the context of your business. This initial step ensures that no asset is left unmonitored and that your vulnerability management efforts are comprehensive from the start.
For years, security teams have relied on the Common Vulnerability Scoring System (CVSS), but these static scores lack critical context. An intelligent platform moves beyond CVSS by incorporating multiple risk factors, including asset criticality and real-time threat data. This creates a dynamic risk score that reflects the actual likelihood of a vulnerability being exploited in your specific environment. This approach to vulnerability and threat prioritization allows your team to stop wasting time on low-risk issues and focus their limited resources on fixing the flaws that pose a genuine threat to your organization.
A vulnerability is one thing; a vulnerability with an active, in-the-wild exploit is another. Integrated threat intelligence provides the real-world context needed to understand which vulnerabilities are being targeted by attackers right now. A top-tier platform will pull data from multiple sources, including its own research teams like HiveForce Labs, to enrich vulnerability data with information on active threat campaigns, malware associations, and known exploited vulnerabilities. This intelligence transforms your prioritization process, helping you distinguish between theoretical risks and immediate dangers that require your urgent attention. It’s the key to making truly risk-informed decisions.
Your attack surface is not static. New devices come online, software is updated, and configurations change every day. That’s why vulnerability management can’t be a point-in-time activity. An effective platform provides continuous monitoring to keep pace with your dynamic environment, constantly scanning for new assets and vulnerabilities. This proactive strategy ensures you always have an up-to-date view of your security posture. With a platform like Uni5 Xposure, you can move away from periodic scans and adopt a continuous approach that identifies and assesses risks as they emerge, not weeks or months later.
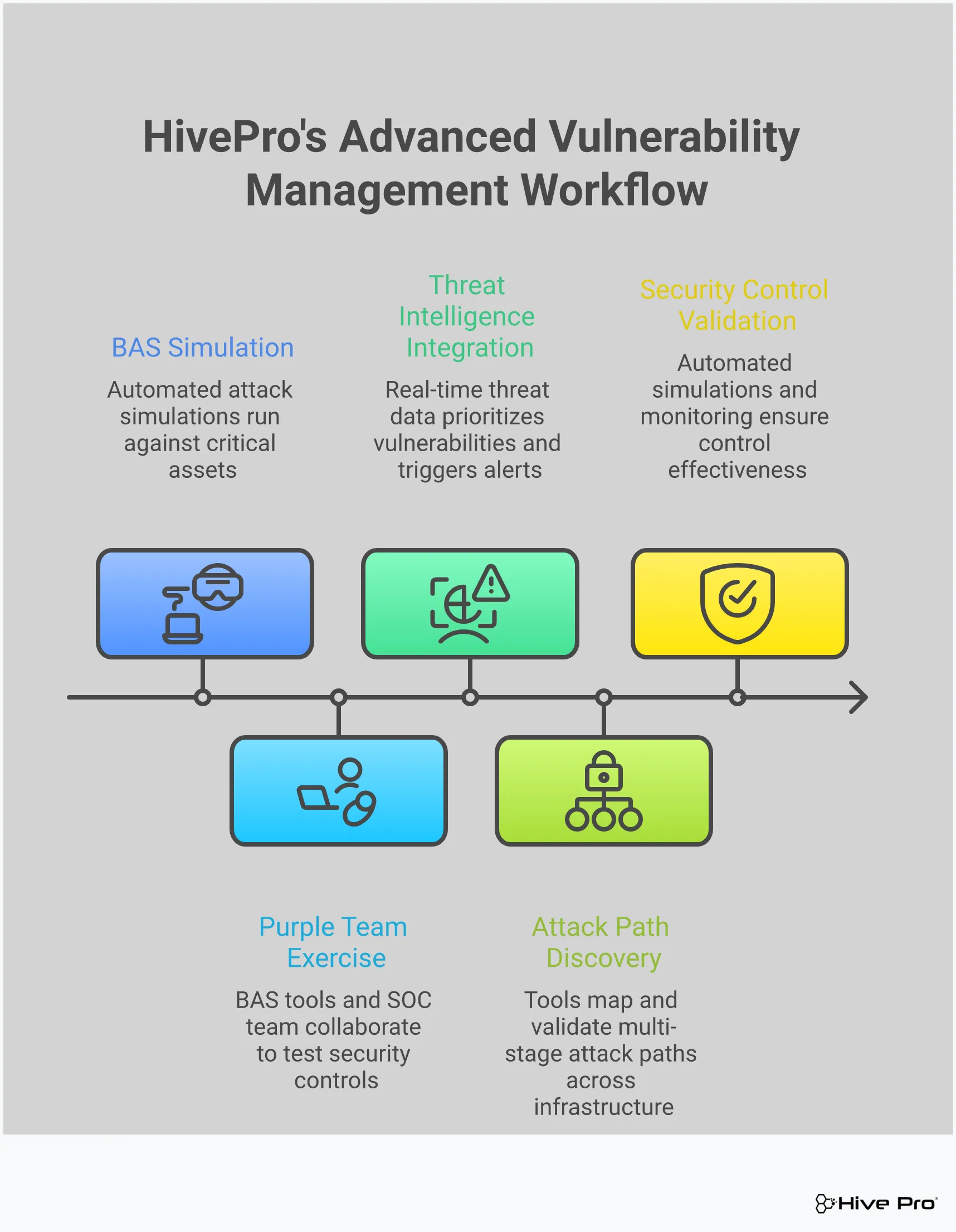
Finding vulnerabilities is only half the battle. You also need to know if your security controls can actually stop an attack. This is where Breach and Attack Simulation (BAS) comes in. By safely simulating real-world attack techniques, BAS capabilities allow you to test the effectiveness of your defenses, from firewalls to endpoint detection and response (EDR) tools. This form of adversarial exposure validation helps you identify hidden gaps in your security posture and confirm that your remediation efforts are working as intended. It answers the critical question: “Are we truly protected against the threats we face?”
Once you’ve decided to adopt a risk-based approach, the next step is finding the right platform. With so many options available, it’s easy to get lost in feature lists and marketing jargon. To cut through the noise, focus your evaluation on four key areas that will directly impact your team’s success and your organization’s security posture.
Your vulnerability management platform is only as good as what it can see. Look for a solution that provides complete visibility across your entire attack surface, including cloud environments, IoT devices, and remote endpoints. A platform that only scans on-premise servers leaves you with significant blind spots. You need a tool that offers total attack surface management and considers the unique context of your IT environment to give you a full picture of your exposure. A comprehensive view ensures you aren’t missing critical risks hiding in forgotten corners of your network.
Don’t get stuck in the CVSS trap. While the Common Vulnerability Scoring System is a useful starting point, it lacks the context needed for effective prioritization. A modern platform moves beyond static scores by incorporating business context and real-time threat intelligence. This approach provides true vulnerability and threat prioritization, allowing your team to focus on the handful of vulnerabilities that pose a genuine threat to your organization. This saves countless hours by preventing your team from chasing down thousands of low-risk issues that attackers are not actively exploiting.
A new tool shouldn’t create more work. The right platform will slide seamlessly into your existing security stack and workflows. Check for pre-built integrations with your vulnerability scanners, SIEM, SOAR, and ticketing systems. The goal of a unified exposure platform is to ingest data from all your tools, correlate it with threat intelligence, and help automate remediation workflows. A strong integration ecosystem prevents data silos and helps your team operate more efficiently, turning insights into action much faster.
Finally, consider the logistics. Most modern platforms are SaaS-based, which simplifies deployment, but it’s still important to understand the pricing model. Is it based on the number of assets, users, or data volume? Look for a transparent pricing structure that can scale with your organization as it grows. Some solutions may have different costs depending on whether they use historical data or provide real-time insights. Be sure to ask for a clear breakdown of all costs to avoid surprises down the road and ensure the investment aligns with your budget.
If you’ve ever felt buried under a mountain of vulnerability alerts, you know that fixing everything is simply not an option. The sheer volume is overwhelming, and frankly, not all vulnerabilities pose the same level of threat. This is where threat intelligence comes in. It cuts through the noise by showing you which vulnerabilities are being actively targeted by attackers. Instead of chasing every potential weakness, you can focus your resources on the ones that present a clear and present danger to your organization, making your vulnerability and threat prioritization efforts far more effective.
Threat intelligence transforms your vulnerability management program from a reactive, checklist-driven exercise into a proactive, threat-informed defense. It provides the context needed to understand your true risk. By knowing which vulnerabilities are part of an active exploit, which are being used by specific threat actor groups, and which are trending in the wild, you can make smarter, faster decisions. This approach allows your team to address the most critical threats first, significantly reducing your exposure to an actual breach.
The Common Vulnerability Scoring System (CVSS) provides a useful baseline for severity, but it doesn’t tell the whole story. A vulnerability with a high CVSS score might be difficult to exploit and largely ignored by attackers. Conversely, a medium-severity flaw could be a favorite tool for threat actors. Real-world exploit data bridges this gap by adding a critical layer of context. It answers the most important question: Is anyone actually using this vulnerability to attack systems? By integrating this data, you can see which vulnerabilities have moved from theoretical risks to practical threats, allowing you to prioritize them accordingly.
Threats don’t exist in isolation. They are often part of broader, coordinated efforts by threat actors. A single vulnerability might be the entry point for a larger campaign aimed at your industry or region. High-quality threat intelligence allows you to monitor these active campaigns and understand the tactics, techniques, and procedures (TTPs) being used. When a vulnerability in your environment is linked to a known campaign, its risk profile changes dramatically. This insight helps you connect the dots between a specific weakness and a potential business-impacting event, giving you a powerful reason to escalate its remediation.
If you need a place to start, look no further than the vulnerabilities that are already being exploited. CISA’s Known Exploited Vulnerabilities (KEV) catalog is an essential resource that lists vulnerabilities with confirmed, active exploits. Focusing your remediation efforts on the KEV list is one of the most efficient ways to reduce risk. These aren’t theoretical problems; they are proven entry points for attackers. A modern vulnerability management platform should automatically flag KEVs in your environment, pushing them to the top of your to-do list so you can close the door on attackers before they get in.
Ultimately, threat intelligence provides the critical context that turns raw data into actionable insight. A true risk score is more than just a CVSS rating. It’s a dynamic calculation that considers the business criticality of the affected asset, the severity of the vulnerability, and real-time threat intelligence about its exploitability. This holistic view helps you understand the actual risk a vulnerability poses to your specific organization. By combining these elements, you can create a unified view of cyber risk that empowers your team to focus on what matters most and communicate that risk effectively to business leaders.
Your vulnerability management program is great at telling you where the cracks are in your foundation. It gives you a list of CVEs, assigns them scores, and helps you understand your theoretical weaknesses. But how do you know which cracks an attacker will actually try to squeeze through? And more importantly, will your security defenses stop them if they do? This is where Breach and Attack Simulation (BAS) comes in.
Pairing BAS with vulnerability management shifts your perspective from reactive to proactive. Instead of just knowing you have a vulnerability, you can safely simulate an attack against it to see what would happen. It’s like having a dedicated red team on-demand, constantly testing your defenses against the latest threats. This approach provides hard evidence of your security effectiveness, helping you move beyond assumptions and make data-driven decisions. By combining the “what” from vulnerability scanning with the “how” from BAS, you get a complete and actionable picture of your true exposure.
You’ve invested heavily in firewalls, EDR, and other security tools. But are they configured correctly? Are they actually working as expected? A clean audit or a green dashboard doesn’t always tell the whole story. BAS provides the proof by running real-world attack scenarios to see if your controls detect and block them. This continuous validation helps you find misconfigurations and gaps before an attacker does. It answers critical questions like, “Did our new firewall rule block that specific malware?” or “Can we detect this lateral movement technique?” This process of adversarial exposure validation ensures your security stack is performing optimally and gives you confidence that your investments are paying off.
Patching is a critical part of vulnerability management, but it’s often a “patch and pray” situation. You apply the fix and hope it worked. BAS changes this by allowing you to test your remediation efforts. Before you patch, you can run a simulation to confirm a vulnerability is exploitable in your environment. After you apply the fix, you can run the same simulation again to verify that the attack path is now closed. This provides concrete evidence that your team’s hard work was successful and the risk has been neutralized. It’s a simple, powerful way to close the loop on your remediation workflow and ensure you’re focusing on fixes that make a real impact on your vulnerability and threat prioritization.
Attackers rarely exploit a single vulnerability in isolation. They chain together multiple weaknesses, moving laterally across your network to reach high-value assets. A vulnerability scanner might flag these issues individually, but it won’t show you how they can be combined into a dangerous attack path. BAS excels at connecting these dots. By simulating multi-stage attacks, it can reveal hidden routes to your critical systems that you would otherwise miss. This helps you understand the full context of a vulnerability, not just its CVSS score. Seeing your total attack surface from an attacker’s perspective allows you to prioritize the vulnerabilities that open up the most critical pathways.
How do you prove your security posture is improving? With BAS, you can move beyond counting patches and start measuring real performance. By running simulations on a consistent schedule, you can track key metrics over time. Are your detection and prevention capabilities getting stronger? Is your team responding to threats faster? This data provides tangible proof of your security program’s effectiveness. It helps you demonstrate ROI on security investments and communicate your progress to leadership in clear, business-friendly terms. This continuous measurement is a core principle of a modern threat exposure management platform, helping you build a more resilient and proactive security program.
Selecting a risk-based vulnerability management platform is a big decision. The right tool can transform your security program from a reactive scramble into a proactive, focused operation. But with so many options available, how do you find the perfect fit? It’s not about finding the platform with the longest feature list; it’s about finding the one that aligns with your team’s specific goals, environment, and workflows.
Think of this process as building a partnership. You need a platform that not only provides powerful technology but also integrates smoothly into your existing ecosystem and supports your team’s day-to-day efforts. By taking a structured approach to your evaluation, you can move beyond the marketing hype and choose a solution that delivers real, measurable value. Let’s walk through the key steps to ensure you make a confident and informed choice.
Before you even look at a demo, the first step is to look inward. What does risk actually mean for your organization? A risk-based approach is effective because it’s tailored to your unique business objectives and IT environment. Start by outlining what you need the platform to do. Are you focused on meeting specific compliance standards? Do you need to secure a complex cloud environment or protect legacy on-premise systems?
Create a clear list of requirements. Differentiate between “must-haves,” like the ability to scan your total attack surface, and “nice-to-haves,” like a specific type of dashboard visualization. Consider your team’s size and skill set. A platform that requires a dedicated expert to manage might not be the right fit for a smaller team. This initial homework will give you a clear scorecard to evaluate potential vendors against.
Your vulnerability management platform shouldn’t live on an island. To be truly effective, it needs to connect seamlessly with the tools your team already uses every day. A modern platform should act as a central hub, ingesting data from all your different scanners and security solutions to give you a single, unified view of risk. Without strong integrations, your team will be stuck manually exporting data and trying to connect the dots between different systems, which defeats the purpose of a streamlined process.
Look for a platform that offers robust, out-of-the-box integrations with your asset management systems, SIEM, SOAR, and ticketing tools like Jira or ServiceNow. This ensures that when a critical vulnerability is prioritized, you can automatically create a ticket and assign it to the right team for remediation. This level of vulnerability and threat prioritization is what turns insight into action.
The best technology in the world won’t help if your team can’t or won’t use it. A successful rollout goes beyond the initial technical setup. You need to plan for how the platform will be integrated into your existing security policies and workflows. Before signing a contract, ask potential vendors about their onboarding process, training resources, and ongoing customer support. A strong partner will work with you to ensure your team feels confident using the tool from day one.
It’s also a good time to establish clear internal policies. Define service-level agreements (SLAs) for how quickly different types of vulnerabilities must be addressed once they are identified by the platform. Getting buy-in from IT and development teams early on is crucial for creating a collaborative and effective remediation process.
A proof of concept (POC) is your chance to test-drive a platform in your own environment with your own data. This is the single best way to validate a vendor’s claims and see if the tool can deliver on its promises. Don’t just run through a generic demo checklist. Instead, define specific success criteria based on the needs you identified earlier. For example, your goal might be to see if the platform can accurately identify your top 10 most critical assets and the vulnerabilities that pose the greatest risk to them.
During the POC, focus on how the platform helps your team address true business risk, not just chase high CVSS scores. Can it show you which vulnerabilities are actively being exploited in the wild? Can it simulate attacks to validate your security controls? An effective POC will prove that the platform can help you focus your team’s valuable time and resources on the threats that truly matter, making your entire adversarial exposure validation process more efficient.
My team is already overwhelmed with ‘critical’ vulnerabilities from our scanners. How does a risk-based approach actually help reduce our workload? This is the exact problem a risk-based approach is designed to solve. Instead of giving you a longer to-do list, it acts as a powerful filter. It takes that massive pile of “critical” alerts and enriches them with real-world context, like which vulnerabilities are actually being exploited by attackers and which ones exist on your most important business systems. This process often reveals that only a small fraction of those thousands of critical alerts pose a genuine, immediate threat. Your team can then focus its energy on that much smaller, manageable list, knowing they are fixing the problems that truly matter.
Is Breach and Attack Simulation (BAS) really necessary if we’re already patching vulnerabilities? Yes, because patching and simulating solve two different, but related, problems. Patching closes a known vulnerability, which is essential. However, BAS validates that your entire security posture is effective. It answers the question, “Even with this vulnerability, could our existing security tools have stopped the attack?” It also helps you confirm that a patch was successful by running a simulation after the fix is applied to prove the attack path is truly closed. Think of it as quality control for your security efforts.
How does this approach help me communicate risk to leadership who may not understand technical details like CVSS scores? A risk-based approach is perfect for translating technical findings into business impact. Instead of presenting a report full of CVE numbers and CVSS scores, you can provide a clear, prioritized list based on actual business risk. You can say things like, “This vulnerability on our payment processing server is being actively targeted by a known threat group, and a breach could directly impact revenue.” This shifts the conversation from abstract technical ratings to concrete business outcomes, which is exactly what leadership needs to hear to understand the importance of your team’s work.
This sounds complicated to set up. How do we transition from a traditional approach without disrupting our current workflow? A good platform makes this transition smoother than you might think. You don’t have to rip and replace your existing tools. Instead, a modern platform integrates with the vulnerability scanners you already use. It ingests that data and then adds the crucial layers of threat intelligence and business context on top. Your team can start by focusing on the newly prioritized list within the platform, gradually incorporating its insights into your existing ticketing and patching workflows. The goal is to make your current process smarter, not to create a brand new one from scratch.
Where does the threat intelligence in these platforms come from, and how do I know it’s reliable? Effective platforms gather threat intelligence from a wide variety of trusted sources. This typically includes public feeds like CISA’s KEV catalog, data from commercial intelligence providers, and findings from their own internal security research teams. The key to reliability is data correlation. The platform doesn’t just rely on a single source; it cross-references information to confirm that a vulnerability is not just theoretically exploitable, but is actively being used in real-world attacks. This ensures the intelligence is timely, accurate, and actionable.