Comprehensive Threat Exposure Management Platform
Your security team is talented, but they aren’t miracle workers. With a persistent skills shortage and ever-tightening budgets, asking them to patch every single vulnerability is not just unrealistic; it’s inefficient. Chasing low-risk issues wastes valuable time and leads to burnout, all while critical threats slip through the cracks. A risk-based vulnerability management tool acts as a force multiplier for your team. By automating the analysis and prioritization process, it eliminates the guesswork and points your team directly to the most urgent fixes. This allows your existing staff to operate more effectively, drastically reducing your mean time to remediation (MTTR) and demonstrating a clear return on investment by focusing resources on what truly reduces organizational risk.
Let’s be honest: the traditional “scan and patch” cycle is broken. Security teams are drowning in a sea of vulnerabilities, with little guidance on where to start. This is where a risk-based vulnerability management (RBVM) tool changes the game. At its core, RBVM is a strategic approach that helps you identify, prioritize, and fix vulnerabilities based on the actual risk they pose to your organization. Instead of treating every vulnerability as equally urgent, an RBVM platform helps you focus your time and resources on the threats that truly matter.
Think of it as a smart filter for your security efforts. It moves you away from an endless to-do list and toward a targeted, proactive strategy. By considering factors beyond a simple severity score, like whether a vulnerability is being actively exploited in the wild and how critical the affected asset is to your business, you can make informed decisions. This approach ensures your security efforts are directly aligned with protecting your most important assets and reducing your overall threat exposure. A strong vulnerability management program goes beyond just patching weaknesses; it connects your security actions to real business risks, making your entire posture more resilient.
Traditional vulnerability management often feels like a numbers game. You run a scan, get a massive report of every single issue, and then try to tackle the list, usually starting with the “criticals.” The problem is, this approach lacks context. It treats a critical vulnerability on a non-essential internal server the same as one on your primary, customer-facing application. RBVM, on the other hand, prioritizes vulnerabilities based on their risk level, considering both the potential impact and the likelihood of an attack. This means you can confidently focus on the small percentage of vulnerabilities that pose the most danger, making your security efforts far more efficient and effective.
An effective RBVM platform is more than just a scanner. It’s a comprehensive system designed to manage the entire vulnerability lifecycle. The core components work together to provide a clear, actionable view of your security posture. It starts with complete visibility across your entire attack surface, from on-premise servers to cloud assets. From there, it continuously identifies weaknesses and enriches that data with threat intelligence and business context. This allows for intelligent vulnerability and threat prioritization that points your team to the most critical fixes. Finally, it provides remediation guidance and integrates with your existing workflows to streamline the patching process, helping you close security gaps faster.
At its core, a risk-based vulnerability management (RBVM) tool follows a logical, three-step process to turn a mountain of vulnerability data into a manageable, prioritized list of actions. Instead of just telling you what’s broken, these platforms help you understand what’s broken, what’s likely to be attacked, and what you need to fix first. This strategic approach moves your team away from a constant fire drill and toward a more proactive security posture. It’s about working smarter, not just harder, by focusing your team’s valuable time and resources on the threats that truly matter to your organization. Let’s break down how these tools make that happen.
Everything starts with visibility. You can’t protect what you don’t know you have. RBVM tools begin by continuously scanning your entire environment to create a comprehensive inventory of all your assets and their associated vulnerabilities. This goes beyond simple network scans, covering everything from cloud infrastructure and applications to endpoints and operational technology. This foundational step gives you a clear, up-to-date picture of your total attack surface. By automating the discovery process, these tools ensure you have a complete and accurate understanding of your security posture, which is the essential first step before you can begin to prioritize and remediate.
Once vulnerabilities are identified, the real work begins. Instead of just relying on a generic CVSS score, an RBVM tool analyzes each vulnerability through the lens of risk. It asks critical questions: Is this vulnerability actively being exploited in the wild? How critical is the affected asset to our business operations? What would be the impact if it were compromised? By layering this context on top of the vulnerability data, the tool generates a risk score that reflects the true threat to your organization. This allows your team to focus on the most impactful issues first, optimizing your resources and ensuring you’re tackling the problems that pose the greatest danger.
To make accurate risk assessments, RBVM platforms integrate real-time threat intelligence from multiple sources. This is the secret sauce that makes the prioritization so effective. By pulling in data on active exploits, attacker tactics, and trending threats, the tool provides crucial context that a static vulnerability database can’t offer. This intelligence helps you understand which vulnerabilities are just theoretical risks and which are being used by attackers right now. With a platform that includes in-house research, like HiveForce Labs, you get curated intelligence that helps you make faster, more informed decisions about where to direct your remediation efforts.
When you start evaluating RBVM tools, you’ll find that they aren’t all built the same. The right platform moves beyond simple scanning and scoring to become a central part of your security operations. It should give you the clarity to focus on what truly matters and the tools to act decisively. A strong RBVM solution doesn’t just add more data to the pile; it provides actionable intelligence that helps your team work smarter, not harder. As you compare your options, look for these four key features. They are the difference between a tool that just identifies problems and a platform that actually helps you solve them, strengthening your security posture with every action you take.
For years, the Common Vulnerability Scoring System (CVSS) has been the standard for rating vulnerability severity. While it’s a useful baseline, relying on it alone is like driving with an outdated map. A CVSS score doesn’t account for whether a vulnerability is actively being exploited in the wild or if it’s relevant to your specific environment. A top-tier RBVM tool provides smarter vulnerability and threat prioritization by layering real-time threat intelligence on top of traditional scores. It answers the critical question: “Is anyone actually using this vulnerability to attack companies like mine right now?” This approach helps you cut through the noise of thousands of “critical” alerts to focus on the handful of threats that pose an immediate danger.
A vulnerability’s risk level is not absolute; it’s relative to the asset it affects. A flaw on a developer’s test machine is a nuisance, but that same flaw on your customer-facing payment server is a crisis. This is where asset and business context becomes essential. A powerful RBVM tool doesn’t just find vulnerabilities; it maps them to your complete inventory of assets. It should integrate with your CMDB or use its own discovery methods to provide total attack surface management. By understanding which assets are mission-critical, internet-facing, or handle sensitive data, you can prioritize fixes based on true business impact, ensuring your most valuable resources are protected first.
Finding vulnerabilities is only half the battle. The real goal is to fix them, and quickly. The best RBVM platforms bridge the gap between security and IT operations by streamlining the remediation process. Look for features like automated ticket generation for systems like Jira or ServiceNow, which assigns remediation tasks directly to the right teams. The tool should also provide clear, actionable guidance on how to patch the vulnerability, including links to patches and configuration advice. This automation and guidance drastically reduces the time from detection to resolution, helping you move from a months-long process to a matter of days or even hours.
How do you know if your vulnerability management program is actually working? You need to measure it. An effective RBVM tool provides intuitive dashboards and customizable reports that let you track key metrics over time. You should be able to monitor things like your overall risk score, mean time to remediate (MTTR), and the number of critical vulnerabilities patched per month. These analytics aren’t just for your team; they are crucial for communicating the value of your security efforts to leadership. Clear reporting helps you demonstrate risk reduction, justify your budget, and show how your team’s work directly supports the organization’s business objectives.
It’s one thing to understand the theory behind risk-based vulnerability management, but it’s another to see how it works day-to-day. A true RBVM platform isn’t just another scanner; it’s a central hub that transforms how your team approaches security. It connects the dots between a vulnerability, the asset it affects, and the real-world threats targeting it. Let’s look at how a platform like Hive Pro’s Uni5 Xposure puts these principles into practice to help you move from simply finding weaknesses to proactively reducing your threat exposure. This shift is what separates a legacy vulnerability management program from a modern, risk-aligned strategy.
Risk-based vulnerability management is a strategic approach that helps you identify, prioritize, and remediate vulnerabilities based on the actual risk they pose to your organization. Instead of getting lost in a sea of “critical” CVEs, you can focus on what matters most. The Uni5 Xposure platform is built on this foundation. It moves your team beyond the endless cycle of scan-and-patch by providing the context needed to make smart decisions. It helps you answer the most important questions: Which vulnerabilities are most likely to be exploited? Which assets are most critical to our business? And what’s the fastest way to fix the biggest risks? This is how you transition from a reactive stance to a proactive one.
A strong vulnerability management program does more than just patch weaknesses; it ensures your security efforts align with business goals. To do that, you need a single, unified view of your entire attack surface. An RBVM platform pulls data from all your assets, whether they are on-prem, in the cloud, or part of your operational technology. By seeing everything in one place, you can understand the business context of each vulnerability. This total attack surface management allows you to allocate resources more effectively, reduce the likelihood of a breach, and build a stronger overall security posture that protects what’s most valuable to your organization.
Not all vulnerabilities are created equal. Many will never be exploited, so why treat them all with the same urgency? Integrating real-time threat intelligence is crucial for cutting through the noise. This is where in-house research from teams like HiveForce Labs becomes a game-changer. This intelligence provides critical context on which vulnerabilities are being actively used in attacks, which malware families are targeting them, and what the latest threat actor tactics are. By layering this data over your vulnerability scan results, you can confidently focus your team’s time and energy on the handful of threats that pose an immediate danger, rather than wasting cycles on low-risk issues.
A long list of vulnerabilities is just noise until you know which ones actually pose a threat to your organization. This is where threat intelligence comes in. It cuts through the clutter by providing a real-world view of the threat landscape, showing you exactly what attackers are targeting and how. Instead of chasing down every single vulnerability, you can concentrate your efforts on the ones that are actively being exploited in the wild. This shift from a theoretical to a practical view of risk is what makes a risk-based approach so effective. It allows your team to stop wasting cycles on low-risk issues and focus on closing the gaps that attackers are most likely to find and use against you.
To effectively prioritize, you need to move beyond static vulnerability data. Integrating real-time threat intelligence feeds into your vulnerability management strategy is a game-changer. These feeds provide up-to-the-minute information on new exploits, attacker tactics, and trending threats. This allows you to see which vulnerabilities have become sudden, high-priority risks because attackers have started targeting them. With this information, you can quickly pivot your remediation efforts to address the most immediate dangers. A dedicated threat intelligence team like HiveForce Labs provides this crucial, timely data, ensuring your team isn’t working with outdated information and can respond to threats as they emerge.
Knowing a vulnerability exists is one thing; knowing it’s being actively exploited is another. An RBVM platform helps you make this critical distinction. It highlights vulnerabilities that have known exploits and are being used in current attack campaigns. This is a huge step up from traditional scanning, which often leaves teams overwhelmed by a sheer volume of findings. By focusing on the vulnerabilities that pose a clear and present danger, you can allocate your security resources more efficiently. This approach ensures you’re fixing the most critical problems first and significantly reducing your exposure to the threats that matter most right now.
Threat intelligence is powerful, but it’s even more effective when combined with the unique context of your own environment. A critical vulnerability on an isolated test server doesn’t carry the same weight as a medium-risk one on your main, customer-facing application. True vulnerability and threat prioritization requires layering threat data with asset context. This means understanding what the asset is, what it does, its business value, and how it’s connected to other systems. This comprehensive view allows you to make smarter, more accurate decisions about which vulnerabilities to tackle first, based on their potential business impact.
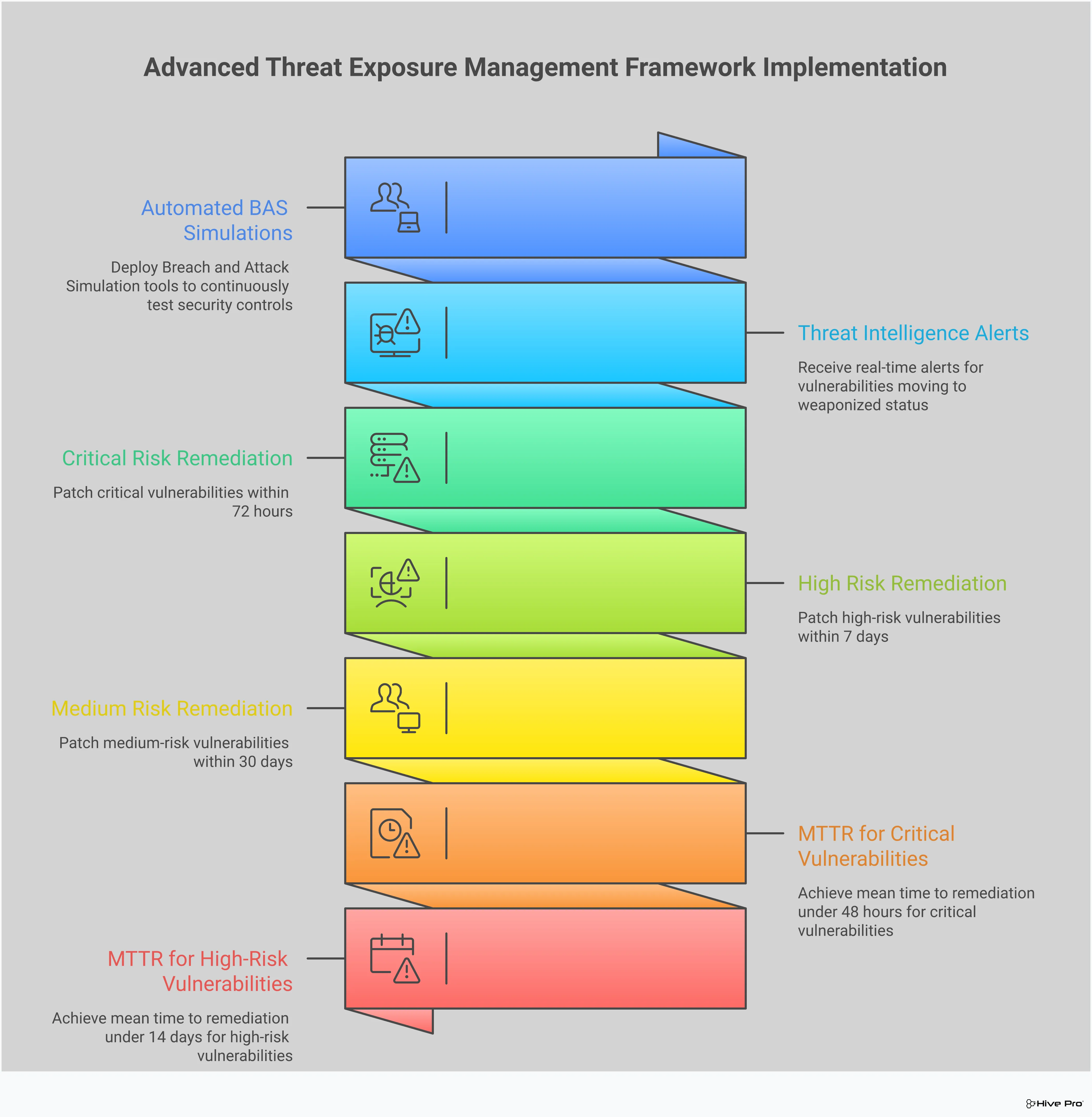
Finding vulnerabilities is only half the battle. The real question is, can an attacker actually exploit them to get through your defenses? This is where Breach and Attack Simulation (BAS) comes in, shifting your security program from a reactive checklist to a proactive, evidence-based strategy. Instead of just assuming your security tools are working as intended, BAS lets you safely and continuously test them against the same tactics and techniques real attackers use. It’s a critical component of modern Adversarial Exposure Validation, helping you find and fix security gaps before they can be exploited.
You’ve invested in firewalls, endpoint detection, and other security controls, but how do you know they’re configured correctly and doing their job? BAS tools answer this question by continuously validating your security stack. They run automated, simulated attacks that mimic real-world threats to see if your controls detect and block them as expected. This proactive approach ensures your security measures are not just present, but effective. It moves you beyond compliance-based checks and gives you real-world proof that your defenses are aligned with the evolving threat landscape, helping you get the most out of your security investments.
Generic tests can only get you so far. The real strength of BAS is its ability to test your defenses against the actual attack techniques used by cybercriminals right now. By using up-to-the-minute threat intelligence from research teams like HiveForce Labs, BAS platforms can simulate the latest ransomware campaigns or phishing tactics. This isn’t a theoretical exercise; it’s a practical drill that shows you exactly how your systems would hold up against a genuine threat. This process reveals specific weaknesses in your defenses and provides clear insights on how to strengthen them before an attacker finds them first.
You can’t improve what you don’t measure. BAS tools provide the metrics and analytics you need to track your security posture over time. After running simulations, the platform generates clear reports that show which attacks were blocked and which succeeded. This allows you to measure your progress in reducing exposure and demonstrate the effectiveness of your security program to leadership. By continuously assessing your controls and tracking performance, you can make informed, data-driven decisions about where to focus your resources. It creates a feedback loop that helps you systematically harden your defenses and improve your overall security maturity.
Switching to a risk-based approach is a major step forward for any security program, but let’s be real, adopting any new tool comes with its own set of hurdles. It’s not just about flipping a switch. You might run into roadblocks with budget, team bandwidth, or getting the new platform to play nicely with your existing security stack.
The good news is that these challenges are common, and they are completely solvable. By anticipating them, you can create a smoother transition and start seeing the benefits of a smarter vulnerability management program much faster. Let’s walk through some of the most frequent obstacles and how you can clear them.
Getting buy-in for a new security tool often feels like an uphill battle. In fact, one report found that 56% of organizations see budget constraints as a top barrier to improving their vulnerability management. The key is to frame the investment around value, not just cost. Instead of focusing on features, build a business case that highlights the return on investment. Show how an RBVM tool reduces the risk of a costly breach and makes your current team more efficient. By automating prioritization and providing clear remediation steps, the right platform allows your team to do more with the resources they already have, turning a perceived expense into a strategic investment in your company’s security and stability.
With a persistent cybersecurity skills shortage, many teams are already stretched thin. The idea of implementing and learning a complex new system can feel daunting. Organizations constantly struggle to find the right balance between speed and accuracy, and a tool with a steep learning curve only makes that harder. This is where choosing an intuitive RBVM platform makes all the difference. Look for a solution that offers intelligent automation and clear, actionable guidance. A platform that simplifies workflows empowers your existing team to act decisively and effectively. It helps bridge the skills gap by making expert-level analysis accessible, allowing your team to focus on fixing what matters instead of getting lost in the data.
Your security tools should work together, not create more data silos. A common pitfall is failing to get a complete inventory of all your assets, which makes it nearly impossible to match vulnerabilities and understand your true risk. If your new RBVM tool doesn’t integrate smoothly with your existing scanners, asset management databases, and ticketing systems, you’ll be stuck with an incomplete and inaccurate picture of your attack surface. The solution is to prioritize a platform built for integration. A tool that provides a unified view of cyber risks in a single place eliminates these blind spots, ensuring you can effectively track and manage vulnerabilities from discovery to remediation without anything falling through the cracks.
Picking the right Risk-Based Vulnerability Management (RBVM) tool is more than just comparing feature lists. It’s about finding a platform that fits your team’s unique workflow, scales with your infrastructure, and ultimately makes your security program more effective. A tool that looks great in a demo but doesn’t integrate with your existing stack or align with your team’s goals will only create more friction.
To make the right choice, you need to look at the bigger picture. Think about how the tool will support your team, connect with your other security investments, and deliver a clear return on investment. By focusing on three key areas, you can find a solution that not only identifies risks but also empowers your team to fix them faster and more efficiently. Let’s walk through how to evaluate your options and select a platform that truly meets your needs.
Before you even look at a demo, start with an internal conversation. What are the biggest challenges in your current vulnerability management process? Where are the communication breakdowns? A successful RBVM program requires collaboration between IT, security, and leadership teams, so the tool you choose must serve all of them. Your security analysts need granular threat data, your IT team needs clear remediation guidance, and your CISO needs high-level reports that connect security efforts to business risk.
Map out your ideal workflow. Who needs to see what information, and when? The right tool should provide a single source of truth that everyone can rely on, breaking down silos instead of creating new ones. Look for a platform that offers customizable dashboards and reporting for different stakeholders, ensuring everyone gets the insights they need without information overload.
Your security program is an ecosystem of tools, and a new RBVM platform needs to be a team player. A tool that doesn’t integrate with your existing SIEM, ticketing systems, and patch management solutions will create manual work and slow down your response times. Make a list of your must-have integrations and ask potential vendors how they connect with your current technology stack.
Your infrastructure is also constantly evolving. Modern environments are a complex mix of on-prem servers, cloud instances, containers, and serverless functions. An effective RBVM tool must provide visibility across this entire landscape. As one report notes, vulnerability management software must assess risks across all these environments to be truly effective. Ensure the tool you choose can scale to cover your complete and future attack surface, giving you a unified view of risk no matter where your assets live.
When evaluating cost, think beyond the license fee. Consider the total cost of ownership, which includes implementation, training, and the internal resources required to manage the platform. With budget constraints and a persistent cybersecurity skills gap being major barriers for many teams, the last thing you need is a tool that’s too complex or resource-intensive to use effectively.
The real value of an RBVM tool is its return on investment (ROI). How much time will it save your team by automating prioritization and reporting? By focusing on the most critical threats, you can drastically reduce your Mean Time to Remediation (MTTR) and lower your overall risk exposure. A platform that provides clear, actionable guidance helps your existing staff operate more efficiently, turning your security program from a cost center into a strategic business enabler.
Making the switch to a risk-based approach is more than just a software update; it’s a strategic move that fundamentally changes how your security team operates for the better. Instead of chasing an endless list of vulnerabilities, you can start making calculated decisions that directly reduce your organization’s real-world risk. This shift brings some significant wins that you’ll see almost immediately, from optimizing your team’s effort to getting ahead of threats before they can cause damage.
If your team feels like they’re constantly playing catch-up, you’re not alone. The sheer volume of vulnerabilities discovered every day is overwhelming, and trying to patch everything is an impossible task. A risk-based approach helps you cut through the noise. It’s a strategic method that helps you identify, prioritize, and remediate vulnerabilities based on the actual risk they pose to your business. By focusing on the critical few instead of the trivial many, you can direct your team’s limited time and energy to the fixes that will have the greatest impact on your security posture. This means less wasted effort on low-risk issues and more effective, targeted work that truly protects your most important assets.
Mean Time to Remediation (MTTR) is a critical metric that measures the average time it takes to fix a vulnerability after it’s been discovered. A long MTTR is a wide-open invitation for attackers. Traditional vulnerability management often gets bogged down in debates over what to fix first, creating huge backlogs and slowing everything down. RBVM changes the game by providing clear, data-driven priorities. It helps your teams fix security problems much quicker, moving from discovery to resolution in a fraction of the time. When your remediation team receives a ticket that already has risk context and clear guidance, they can act immediately, shrinking that window of opportunity for attackers and strengthening your defenses.
For too long, security has been a reactive discipline, responding to fires after they’ve already started. A risk-based approach allows you to finally get ahead. RBVM is inherently proactive; it helps you get ahead of threats rather than just reacting after an attack is underway. By combining vulnerability data with real-time threat intelligence and the business context of your assets, you can see your organization through an attacker’s eyes. This allows you to identify and fix the weaknesses that are most likely to be exploited. This strategic shift transforms your team from digital firefighters into forward-thinking defenders who are always one step ahead, working toward proactive exposure reduction.
We already use CVSS scores to prioritize. Isn’t that enough? Think of CVSS scores as a starting point, not the finish line. A high CVSS score tells you a vulnerability is theoretically severe, but it doesn’t tell you if anyone is actually using it in an attack or if it affects a critical business system. A risk-based approach adds that essential context. It layers real-time threat intelligence and your own business priorities on top of the CVSS score, so you can distinguish between a “critical” vulnerability on a test server and one on your main payment application that attackers are actively exploiting right now.
My team is already overwhelmed. Will implementing an RBVM tool just add more work? It’s actually the opposite. The goal of an RBVM platform is to reduce your team’s workload by eliminating the noise. Instead of handing them a report with thousands of vulnerabilities to investigate, the tool does the heavy lifting of analysis and prioritization for them. It points them directly to the small percentage of issues that pose a genuine, immediate threat. This allows your team to stop wasting time on low-risk findings and focus their energy where it will have the most impact, making them more efficient and effective.
How does Breach and Attack Simulation (BAS) relate to vulnerability management? Vulnerability management tells you where the cracks are in your walls. Breach and Attack Simulation tests if an attacker could actually get through those cracks and bypass your security guards. A BAS platform safely simulates real-world attack techniques to validate that your security controls, like your firewall or endpoint protection, are configured correctly and working as intended. It’s the proactive step that answers the question, “Even with this vulnerability, are our defenses strong enough to stop an attack?”
Does an RBVM platform replace my existing vulnerability scanner? Not at all. An RBVM platform works with your existing scanners to make their data more powerful. Your scanners are great at identifying vulnerabilities, but they often stop there. The RBVM platform ingests that raw data and enriches it with threat intelligence and business context to create a prioritized, actionable list. It acts as the brain of your operation, taking the information from your scanners and turning it into a strategic remediation plan.
How can I justify the cost of an RBVM tool to my leadership? Frame the conversation around efficiency and risk reduction, not just features. Explain that the tool makes your current team more productive by automating the manual analysis that bogs them down, allowing them to fix more critical issues faster. You can also highlight the return on investment by showing how focusing on the most likely threats directly reduces the risk of a costly data breach. It’s about shifting security from a cost center to a strategic function that protects the business’s most valuable assets.