Comprehensive Threat Exposure Management Platform
You wouldn’t set sail across the ocean without checking the weather forecast. Meteorologists gather data on temperature, wind, and pressure systems to predict an incoming storm, giving you time to prepare. Predictive threat intelligence applies the same logic to cybersecurity. It collects and analyzes a massive volume of data—from your own network logs to activity on the dark web—to forecast where, when, and how attackers might strike next. This isn’t about gazing into a crystal ball; it’s a methodical, data-driven process. The goal of predictive threat intelligence for organizations is to give you that forecast, turning abstract risks into a clear warning so you can strengthen your defenses before the storm hits.
Predictive threat intelligence is all about getting ahead of cyber threats. Instead of just reacting to attacks as they happen, this approach uses advanced analysis to anticipate and prepare for potential threats before they ever hit your network. It’s a strategic shift that moves your security program from a defensive crouch to a forward-leaning stance, allowing you to act first.
Most security tools are built to respond after an attack is already underway. That’s a bit like having a great plan for what to do once your house is on fire. Predictive threat intelligence flips the script. It aims to stop attacks before they even begin by forecasting what attackers are likely to do next. By analyzing historical attack data, current threat trends, and typical attacker behaviors, you can build a picture of future risks. This proactive approach helps you put up the right defenses in the right places, significantly reducing the chance of a breach and minimizing the potential fallout. It’s the core of a modern threat exposure management strategy.
So, how does this forecasting actually work? The heavy lifting is done by artificial intelligence (AI) and machine learning (ML). These technologies are incredibly good at sifting through enormous amounts of data—like network telemetry and user behavior—to spot subtle patterns and anomalies that would be impossible for a human to catch. Think of it as a super-powered security analyst that never sleeps. By recognizing repeated attack patterns and identifying new adversary techniques as they emerge, AI and ML can make informed predictions about future threats. This is the kind of advanced analysis that powers the insights from security research teams like HiveForce Labs, turning raw data into actionable, forward-looking intelligence.
Predictive threat intelligence isn’t about gazing into a crystal ball; it’s a methodical process that turns massive amounts of data into a forecast of potential cyberattacks. Think of it like weather forecasting for cybersecurity. Meteorologists gather data on temperature, pressure, and wind patterns to predict a storm. Similarly, predictive intelligence platforms collect and analyze data from countless sources to forecast where, when, and how attackers might strike next. This process works by looking at past attack information, current threat trends, and the typical behaviors of cybercriminals.
By connecting these dots, it moves your security strategy from a reactive mode—cleaning up after an attack—to a proactive one where you can prepare your defenses for threats that are on the horizon. It’s about understanding an attacker’s intent and plans before they can execute them. This foresight allows you to focus your resources on the threats that pose the most significant risk to your organization, rather than trying to defend against everything all at once. It’s a fundamental shift that helps you get ahead of attackers by anticipating their next move.
The strength of any prediction lies in the quality of its data. Predictive threat intelligence starts by collecting a huge volume of information from a wide array of sources. This isn’t just about pulling in one or two threat feeds; it’s about creating a comprehensive picture of the threat landscape. Your organization’s own security logs and network traffic provide an internal view, while external sources add crucial context. This includes threat intelligence feeds that share known bad IP addresses, public information from news and security research, and even monitoring the deep and dark web where attackers often plan their campaigns. The goal is to cast a wide net and pull in as much relevant data as possible to feed the analytical engine.
Once all this data is collected, the real work begins. It’s impossible for a human team to manually sift through terabytes of information and find meaningful connections. This is where AI and machine learning become essential. These technologies analyze all the incoming data to establish a baseline of what “normal” looks like for your systems and users. From there, the AI can spot anomalies—like a sudden spike in failed login attempts from an unusual location or a large data transfer at 3 a.m.—that could signal a potential threat. It’s trained to recognize the subtle patterns and tactics that attackers use, connecting seemingly unrelated events to reveal an emerging attack campaign.
This is where data analysis turns into actionable foresight. After identifying patterns and anomalies, the system uses historical data and real-time activity to forecast likely attack scenarios. Instead of just telling you what’s happening now, it predicts what attackers are likely to do next. This level of insight helps you with vulnerability and threat prioritization by showing you your specific risk based on the current threat landscape. For example, the platform might predict that a new strain of ransomware is likely to target your industry within the next quarter. This allows you to move from simply patching known issues to proactively strengthening the specific defenses needed to stop that forecasted attack before it ever happens.
Shifting from a reactive to a proactive security strategy is no longer a luxury—it’s a necessity. Instead of waiting for alerts to tell you you’ve been breached, you can anticipate an attacker’s next move. Predictive threat intelligence uses data modeling and machine learning to forecast potential attacks, giving your team the foresight to act before an incident occurs. This approach fundamentally changes how you manage risk, allowing you to build a more resilient and prepared security posture. By understanding what’s coming, you can allocate resources more effectively and focus on the threats that pose the greatest danger to your organization.
The core value of predictive threat intelligence is its ability to help you see around the corner. Instead of just responding to attacks as they happen, this approach allows you to prepare for them in advance. By analyzing vast datasets for patterns and indicators of malicious activity, predictive models can guess where and how cyberattacks are likely to occur. This means you can anticipate attacks before they happen, moving your security program from a defensive stance to an offensive one. It’s about getting ahead of the threat actor’s timeline, giving you the critical time needed to reinforce defenses where they’re needed most.
Predictive intelligence directly strengthens your overall security posture by making it much harder for cyberattacks to succeed. When you can foresee likely attack vectors, you can proactively close security gaps, update configurations, and educate employees on emerging threats. This preemptive action significantly reduces your attack surface and overall risk profile. This forward-looking strategy is a cornerstone of modern exposure management, where the goal is to continuously identify and mitigate risks before they can be exploited. By focusing on prevention rather than reaction, you build a more robust and resilient defense against an ever-changing threat landscape.
The financial argument for predictive threat intelligence is compelling. It’s almost always cheaper to prevent an attack than to recover from one. The costs of a breach—including downtime, data recovery, regulatory fines, and reputational damage—can be astronomical. Predictive analytics helps you avoid these costs by stopping attacks before they can cause harm. Organizations that use predictive tools can often detect attacks faster than those relying on traditional methods alone. This speed not only minimizes potential damage but also frees up your security team to focus on strategic initiatives instead of constant firefighting, delivering a clear return on investment.
Traditional vulnerability management often feels like a never-ending game of whack-a-mole. A scan runs, a long list of vulnerabilities appears, and your team scrambles to patch them before the next scan reveals even more. It’s a reactive cycle that leaves security teams feeling overwhelmed and constantly behind. Predictive threat intelligence breaks this cycle by fundamentally changing how you approach vulnerabilities. Instead of just reacting to a list of known weaknesses, you can start anticipating which ones attackers are most likely to target.
This shift is about adding a layer of foresight to your security strategy. By analyzing vast datasets and identifying patterns, predictive intelligence helps you understand the probability of an exploit, not just its possibility. It allows you to see your environment through the eyes of an attacker, focusing on the pathways they’re most likely to take. This transforms vulnerability management from a compliance-driven, box-ticking exercise into a proactive, threat-informed defense that actively reduces your organization’s exposure to real-world attacks. It’s about working smarter, not just harder, to protect what matters most.
For years, the standard advice was to patch everything as quickly as possible. But with thousands of new vulnerabilities discovered annually, that’s simply not sustainable. Predictive threat intelligence offers a better way forward. It uses AI to help you anticipate and stop cyberattacks before they happen, moving your team from a reactive to a proactive stance. Instead of waiting for a vulnerability to be exploited, you can use predictive insights to identify which weaknesses are on attackers’ radars right now. This allows you to get ahead of the threat, fortifying your defenses against the attacks that are most likely to come your way, rather than just chasing down every single alert.
Not all vulnerabilities pose the same level of risk. A critical vulnerability on a non-essential internal server is far less concerning than a medium-risk one on your primary, customer-facing application. Predictive intelligence helps you cut through the noise by adding crucial context to your vulnerability data. It helps you focus your security efforts and resources on the most probable and impactful threats. By correlating vulnerability data with real-time threat actor activity, exploitability trends, and asset criticality, you can move beyond basic CVSS scores. This enables a truly risk-based approach to vulnerability and threat prioritization, ensuring your team spends its valuable time fixing the issues that actually reduce your organization’s exposure.
Predictive intelligence is powerful, but it’s most effective when it’s part of a larger, continuous process. This is where a Continuous Threat Exposure Management (CTEM) program comes in. A CTEM framework integrates predictive insights into a seamless cycle of asset discovery, prioritization, validation, and remediation. A platform like Hive Pro’s Uni5 Xposure brings these elements together, using predictive intelligence as a core engine to provide a unified view of risk. It combines asset discovery, AI-driven prioritization, breach and attack simulation, and threat intelligence to give you a complete picture of your exposure. This integration turns predictive insights into confident, decisive action, transforming your security program from a series of disconnected tasks into a cohesive and proactive defense strategy.
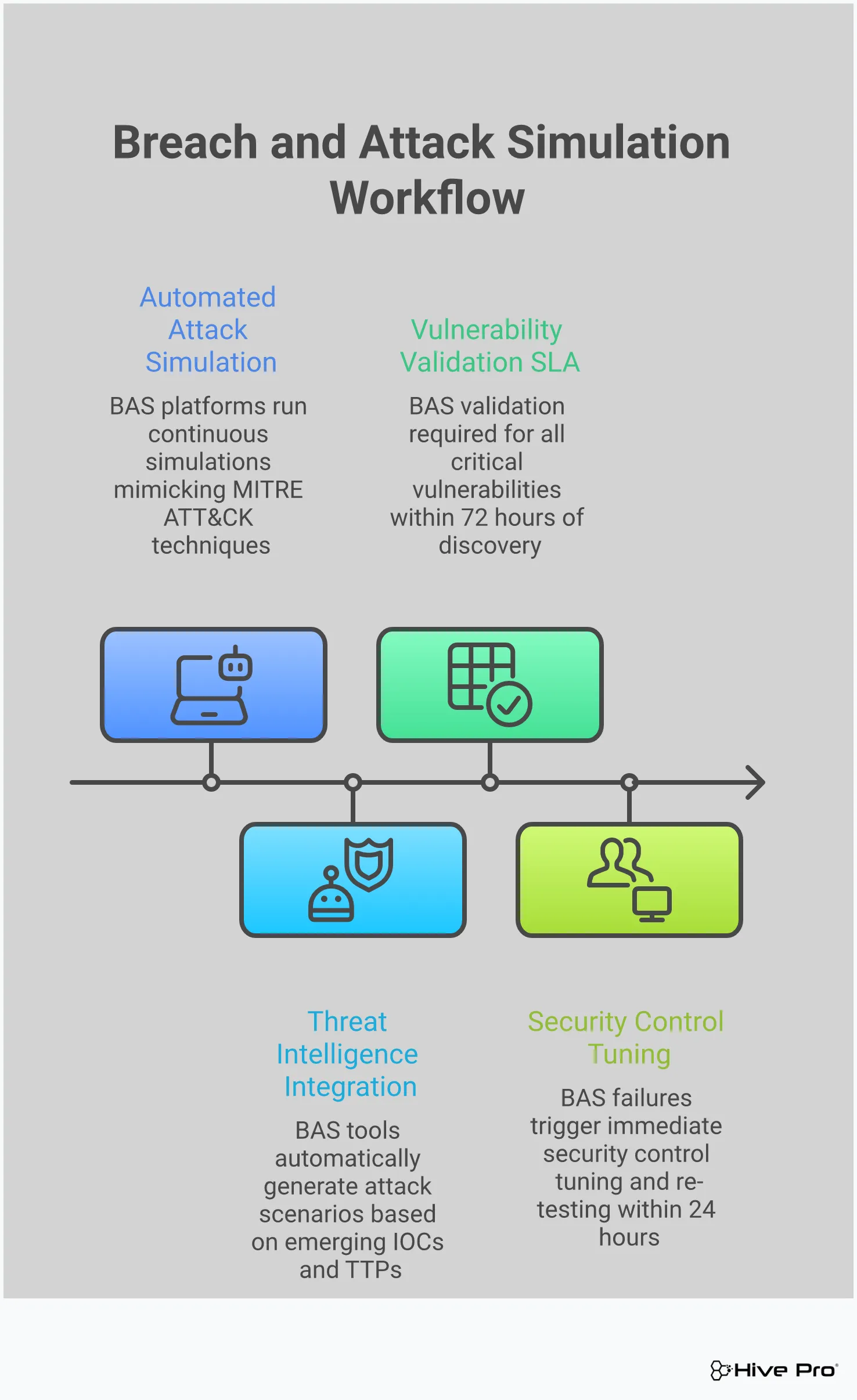
Predictive intelligence gives you a powerful heads-up about what attackers might do next. But a prediction is just a well-informed guess until you test it. This is where Breach and Attack Simulation (BAS) comes in. Think of it as moving from theory to practice. While predictive intelligence tells you which threats are on the horizon, BAS lets you safely launch simulated versions of those threats against your own systems to see how they hold up.
Instead of waiting for a real attack to find your weak spots, you can proactively pressure-test your defenses in a controlled environment. This approach helps you answer critical questions: Are our security controls configured correctly? Would we detect this type of activity? How would our team respond? By running these drills, you can find and fix security gaps before an attacker gets the chance to exploit them. This is a core part of a modern Adversarial Exposure Validation strategy, turning abstract threat data into concrete actions that make your organization safer.
Waiting for an incident to discover a vulnerability is a high-stakes game. A much better approach is to run regular fire drills for your security posture. BAS platforms allow you to do just that by continuously running simulated attacks that mimic the latest real-world adversary techniques. These aren’t disruptive, theoretical exercises; they are safe, automated tests that check if your security tools—from firewalls to endpoint detection—are working as expected. This proactive testing helps you spot misconfigurations, gaps in coverage, and process weaknesses before they become a real problem. It’s about finding the holes in your armor yourself, rather than letting an attacker find them for you.
Your predictive intelligence platform might flag a new ransomware strain or a specific phishing technique that’s gaining traction. That’s valuable information, but how do you know if your organization is actually protected against it? BAS provides the answer by letting you validate those predictions. You can take the intelligence about a specific threat and immediately run a simulation that mimics its behavior. This gives you clear, evidence-based proof of whether your defenses would succeed or fail. This process transforms a general threat warning into specific, actionable insight about your own environment, all managed within a comprehensive threat exposure management platform.
Security isn’t a one-time setup; it’s an ongoing process of adaptation. BAS is a key driver of that process. When a simulation identifies a weakness, your team can implement a fix. But the cycle doesn’t end there. You can then re-run the simulation to confirm the fix works and hasn’t introduced any new issues. This creates a powerful feedback loop: predict a threat, test your defense against it, remediate any gaps, and validate the solution. By repeating this cycle, you steadily strengthen your security posture over time. It ensures your defenses evolve right alongside the threat landscape, building a more resilient and prepared organization.
Think of threat intelligence as the context that turns a long list of vulnerabilities into a clear, actionable to-do list. Without it, you’re staring at thousands of potential weaknesses with little insight into which ones pose a genuine, immediate threat to your organization. Threat intelligence answers the most important question for any security team: “Of all the things we could fix, what do we need to fix right now?” It provides the real-world data on attacker activity, trending exploits, and emerging campaigns that you need to make smart, risk-based decisions.
This is where exposure management truly shines. By integrating threat intelligence from sources like HiveForce Labs, you can shift from a reactive cycle of endless patching to a proactive strategy focused on reducing your most significant exposures. It’s about understanding not just that a vulnerability exists, but how likely it is to be exploited by a real adversary. This intelligence-driven approach allows you to focus your team’s limited time and resources on the threats that actually matter, effectively shrinking your attack surface and strengthening your defenses against active campaigns.
Not all vulnerabilities are created equal. A critical vulnerability with a high CVSS score might seem like a top priority, but if no threat actor is actively exploiting it, is it truly your biggest risk? On the other hand, a medium-severity flaw that has become the go-to tool for a ransomware group is a ticking time bomb. Threat intelligence feeds cut through this noise by highlighting which vulnerabilities are being used in the wild right now.
This allows you to prioritize based on real, observed attacker behavior rather than theoretical risk scores. A platform that provides total asset exposure visibility uses this intelligence to connect the dots between a trending threat and the specific assets in your environment that are susceptible. This way, you can immediately pinpoint and address the weaknesses that attackers are most likely to target next.
Beyond individual exploits, threat intelligence gives you a bird’s-eye view of the entire threat landscape. It helps you understand the specific tactics, techniques, and procedures (TTPs) that adversaries are using to target organizations in your industry or region. Are attackers favoring a particular type of phishing attack? Is a new malware strain gaining traction? This situational awareness is crucial for making informed, strategic decisions about your security posture.
By staying current with relevant threat advisories, you can anticipate an attacker’s next move instead of just reacting to it. This context helps you understand your organization’s unique risk profile and adjust your defenses accordingly. It’s about knowing what’s coming over the horizon so you can prepare your defenses before the storm hits.
Ultimately, intelligence is only valuable if it leads to action. Threat intelligence transforms your remediation efforts from a guessing game into a precise, data-driven process. When you know which vulnerabilities are being actively exploited and how, you can prioritize patching and mitigation efforts with confidence. This ensures your team is spending its time on fixes that deliver the greatest impact on your security posture.
This approach makes the entire process of vulnerability and threat prioritization more efficient and effective. Instead of working through a backlog based on generic severity ratings, your team can focus on closing the exact security gaps that attackers are leveraging today. This not only reduces your immediate risk but also helps you build a more resilient and proactive security program over the long term.
While every organization can gain from a more proactive security approach, some industries face unique pressures that make predictive threat intelligence especially valuable. The sheer volume of threats, combined with strict regulatory requirements and the high value of their data, puts certain sectors squarely in the crosshairs of attackers. For these industries, moving from a reactive to a predictive model isn’t just an improvement—it’s a necessity for survival and resilience.
Predictive intelligence helps these high-stakes industries not only fend off attacks but also meet compliance demands and protect their most critical assets. By anticipating where attackers will strike next, security teams can allocate resources more effectively, patch the most critical vulnerabilities first, and build a more robust defense. Let’s look at a few sectors where this proactive shift is making the biggest impact.
Financial institutions and healthcare organizations are prime targets for cybercriminals because of the sensitive data they manage. For banks, it’s financial assets and customer information; for hospitals, it’s protected health information (PHI). A breach in either sector can lead to massive financial loss, regulatory fines, and a severe loss of public trust. Predictive threat intelligence allows these organizations to get ahead of sophisticated attacks. For example, one major financial institution utilized threat intelligence to successfully detect and shut down a phishing campaign before it could impact customers. Similarly, healthcare providers can use predictive insights to protect patient data and ensure the continuity of care, which is critical for patient safety.
The stakes are incredibly high for government agencies and critical infrastructure sectors like energy, water, and transportation. A successful attack can disrupt essential services and threaten national security. These organizations face threats from nation-state actors and sophisticated cybercriminal groups. Predictive threat intelligence is becoming essential for powering a preemptive defense strategy, allowing them to anticipate and counter threats before they can cause widespread damage. Furthermore, these sectors are often bound by strict compliance and reporting regulations. Implementing comprehensive threat intelligence solutions is not just a best practice but a requirement for mitigating risks and protecting the sensitive data that keeps public services running safely and securely.
Tech and telecom companies operate in a landscape of constant innovation and rapid change, which also means their attack surfaces are continually expanding. They manage vast networks and a treasure trove of intellectual property and customer data, making them attractive targets. For these industries, leveraging artificial intelligence is key. AI’s ability to learn from vast datasets, identify subtle patterns, and predict potential threats is transforming how these organizations defend their digital assets. By integrating predictive intelligence, tech and telecom companies can automate their responses, protect their infrastructure from advanced threats, and secure the digital future for their customers.
Adopting predictive threat intelligence is a game-changer, but it’s not as simple as flipping a switch. Like any powerful new capability, it comes with its own set of hurdles. Getting ahead of these challenges is the key to making your implementation a success. Most teams run into issues with integrating disparate data sources, equipping their people with the right skills, and managing the sheer volume of new information. Let’s walk through how to tackle each of these common roadblocks so you can get the most out of your predictive tools from day one.
Your security data probably lives in a dozen different places—SIEMs, endpoint protection platforms, cloud services, and network scanners. Predictive intelligence needs to pull from all these sources to be effective, but they often don’t speak the same language. The first step is to standardize your data formats so your systems can communicate. A platform that provides a unified view of cyber risks can break down these data silos. This is especially important in hybrid environments where you’re managing on-premise servers, multiple cloud instances, and a remote workforce. Your tools need the flexibility to cover this entire, complex landscape without leaving blind spots.
New technology requires new skills, and it’s easy to underestimate the human side of implementation. Your security team needs to understand how AI-powered systems work so they can trust the insights and act on them confidently. This isn’t just about technical training; it’s about building new workflows and habits. You can support your team by providing clear documentation, hands-on practice exercises, and playbooks for responding to different types of predicted threats. When your analysts understand the ‘why’ behind an alert, they can make faster, smarter decisions. Investing in your team’s skills ensures your new tools don’t just sit on a digital shelf.
The goal of predictive intelligence is clarity, but sometimes the flood of new data can have the opposite effect, leading to analysis paralysis. When your team is overwhelmed with alerts, it’s hard to know where to focus. The solution isn’t more data—it’s better-prioritized data. Use smart filters and intuitive dashboards to surface the most critical threats that pose an immediate danger to your organization. A system that excels at vulnerability and threat prioritization will cut through the noise for you. This allows your team to stop chasing down every minor alert and concentrate their efforts on the vulnerabilities that attackers are most likely to exploit.
Putting predictive threat intelligence into practice is more than just flipping a switch on a new tool. It’s about building a strategic capability that helps your security program mature. By focusing on a few key areas, you can create a system that not only anticipates threats but also gives your team the clear, actionable guidance they need to prevent them. It starts with quality data, thrives on teamwork, and proves its value through clear, measurable results. When these pieces come together, you shift from simply reacting to threats to proactively managing your threat exposure.
The accuracy of your predictions depends entirely on the quality and breadth of your data. Think of it as building a comprehensive library of threat information. You need to gather intelligence from a wide range of sources, both inside and outside your organization. This includes your own security logs, endpoint data, and network traffic, combined with external feeds like public threat reports, dark web monitoring, and industry-specific advisories. The goal is to create a rich, diverse dataset. This allows your platform to connect the dots and identify patterns that would otherwise go unnoticed, giving you a much clearer picture of potential attacks heading your way.
Predictive intelligence is most effective when it’s a shared resource, not a siloed function. Your security operations, vulnerability management, and IT teams all have a stake in the game, and they need to be on the same page. When everyone works from a single, unified view of potential threats, communication improves and response becomes more coordinated. Encourage your teams to share information and insights freely. This collaborative approach ensures that when a credible threat is predicted, the right people have the context they need to act quickly and decisively, strengthening your overall security posture and breaking down the barriers that can slow down remediation.
To understand if your predictive strategy is working, you need to define what success looks like. Move beyond simple counts and focus on metrics that demonstrate real risk reduction. Track key performance indicators (KPIs) like your early detection rate, the reduction in attacker dwell time, or a decrease in the number of impacted assets after an incident. You can also measure how many threats were neutralized before they could cause harm. Tracking these quantifiable metrics does more than just prove the value of your investment; it provides the feedback you need to continuously refine your approach, making your predictions even more accurate over time.
Selecting the right predictive threat intelligence platform is about more than just buying new software; it’s about finding a partner that can help you turn data into decisive action. With so many options available, it’s easy to get lost in feature lists and marketing promises. The key is to focus on platforms that not only provide accurate predictions but also fit into your existing security ecosystem and can grow with you over time.
A great platform should give you a clear, unified view of your cyber risks without adding unnecessary complexity. It needs to do the heavy lifting of collecting and analyzing vast amounts of data so your team can focus on what they do best: protecting your organization. Think of it as hiring a new, incredibly smart analyst for your team—one who works 24/7 to find threats before they find you. Let’s walk through the essential features and considerations to keep in mind during your search.
The foundation of any effective predictive threat intelligence platform is its ability to gather and process data. Look for a solution that offers comprehensive data collection, giving you complete visibility across your entire attack surface. This means it should handle everything from asset discovery to providing detailed patch intelligence. A platform like Uni5 Xposure uses AI-driven insights to deliver risk-oriented analysis, helping you prioritize which vulnerabilities to fix first based on real-world threats. This ensures your team isn’t just busy, but productive, focusing on the issues that pose the greatest risk to your organization.
A new tool shouldn’t force you to rebuild your security stack from the ground up. The right platform will integrate smoothly with the security tools and workflows you already use, enhancing your current setup without causing major disruptions. It should act as a central hub, pulling in data from your existing systems to enrich its analysis. Equally important is scalability. Your organization is going to grow, and your security platform needs to be able to keep up. Choose a solution designed to handle an increasing number of assets and data streams, ensuring it can support your vulnerability and threat prioritization needs for years to come.
How is predictive threat intelligence different from the standard threat feeds we already use? Think of standard threat feeds as a rearview mirror—they tell you about known bad actors and attacks that have already happened. It’s valuable information, but it’s reactive. Predictive threat intelligence is like your GPS, analyzing current conditions and historical data to show you the most likely route an attacker will take to get to you. It moves beyond a simple list of known threats to forecast future attack scenarios, giving you a chance to prepare your defenses before an attack is even launched.
My team is already overwhelmed with alerts. Won’t this just add to the noise? That’s a fair concern, but a good predictive intelligence platform should do the exact opposite. Its main job is to cut through the noise, not add to it. Instead of just flagging every potential issue, it uses context to prioritize what actually matters. By correlating vulnerability data with active threat actor behavior, it helps you focus on the handful of critical exposures that pose a genuine, immediate risk, allowing your team to ignore the low-risk alerts that can wait.
How does this help me deal with my existing backlog of thousands of vulnerabilities? That massive backlog is exactly where predictive intelligence makes the biggest impact. It provides the context needed to stop treating all vulnerabilities equally. Instead of just working from the top of a list sorted by CVSS score, you can use predictive insights to identify which vulnerabilities in your backlog are most likely to be targeted by attackers soon. This allows you to strategically address the 1% of issues that cause 99% of the risk, making your remediation efforts far more efficient and effective.
How can I be sure the predictions are accurate and not just guesses? This is where validation comes into play. A prediction is a strong starting point, but you need to test it against your reality. This is often done using Breach and Attack Simulation (BAS). You can take a prediction—for instance, that a certain attack technique is on the rise—and run a safe, simulated version of that attack against your own defenses. This gives you concrete proof of whether you’re protected or not, turning an intelligent guess into an evidence-based action plan.
What’s the first practical step to get started with predictive intelligence? The best first step is to get a clear picture of your data foundation. You can’t predict threats if you don’t have good visibility into your own environment. Start by identifying your key data sources—like security logs, network traffic, and asset inventories—and think about how you could bring them together. A platform that can unify this information is essential, as it creates the comprehensive view needed for the AI and machine learning models to make accurate forecasts.