Comprehensive Threat Exposure Management Platform
Your scanners find thousands of vulnerabilities every cycle. Your team triages, assigns, and patches what they can. But weeks later, the same critical CVEs still sit open, SLAs blow past their deadlines, and the backlog keeps growing. The problem is rarely a lack of detection. It is a broken remediation process.
Vulnerability remediation is the most operationally demanding phase of any security program, and it is where most organizations struggle. This guide covers the complete vulnerability remediation process from initial triage through verification, including practical SLA frameworks, compensating controls for what you cannot patch, and how orchestration platforms cut mean time to remediate (MTTR) by eliminating the manual handoffs that slow everything down.
See how Uni5 Xposure automates the full remediation lifecycle. Book a demo.
Vulnerability remediation is the process of identifying, prioritizing, and permanently fixing security weaknesses in your systems, applications, and infrastructure before attackers exploit them. It is the action phase of vulnerability management, where findings from vulnerability management tools and assessments get converted into actual fixes that reduce your organization’s risk.
Remediation goes beyond simply running a patch. It encompasses the full lifecycle: triaging findings to separate real risks from noise, assigning ownership to the right teams, applying the appropriate fix (whether that is a patch, configuration change, or compensating control), verifying the fix worked, and tracking everything against defined service-level agreements.
In 2024, a record 40,009 CVEs were published. AI cybersecurity tools help teams cut through this volume by automating triage and prioritizing threats based on real-world exploit intelligence. Yet the mean time to remediate critical vulnerabilities still sits around 97 days, according to industry benchmarks. That three-month gap between discovery and resolution is where breaches happen. A structured vulnerability remediation process is what closes that gap.
These three terms get used interchangeably, but they mean different things:
Understanding these distinctions matters because not every vulnerability can be patched immediately. Legacy systems, operational constraints, and change control windows often require mitigation as a bridge until remediation is possible.
Effective security vulnerability remediation follows a structured, repeatable workflow. Each step feeds the next, creating a closed loop that reduces risk systematically rather than reactively. Here is the process from start to finish.
Remediation starts before anyone writes a ticket. Automated vulnerability scanners (network, application, container, cloud) continuously identify weaknesses across your total attack surface. But raw scan output is noisy. A single scan cycle can produce thousands of findings, many of which are duplicates, false positives, or informational.
Triage is the first filter. During triage, your team:
Without effective triage, teams waste cycles chasing false positives while genuine threats sit unaddressed.
Not all vulnerabilities demand the same urgency. A critical CVE on an internet-facing production database is a fundamentally different risk than the same CVE on an isolated test server.
Risk-based vulnerability and threat prioritization goes beyond raw CVSS scores by layering in:
This context-driven approach is what separates mature remediation programs from those drowning in alert fatigue. When your team focuses on the top 3% of vulnerabilities that represent genuine, immediate risk, the workload becomes manageable and the impact measurable.
Once priorities are set, each vulnerability needs a clear owner with a clear deadline. This is where many remediation programs break down. The security team identifies the issue, but the fix often falls to IT operations, DevOps, application teams, or infrastructure engineers who have their own priorities and backlogs.
Effective assignment requires:
Manual assignment through spreadsheets or email chains is the single largest contributor to remediation delays. Every manual handoff adds days.
With ownership assigned and deadlines set, the remediation team executes the fix. The appropriate action depends on the vulnerability type and operational constraints:
Patching is the most direct fix for software vulnerabilities. Apply the vendor-issued update, test for regressions, and deploy to production. For critical vulnerabilities on high-value assets, this should happen within hours, not weeks.
Configuration changes address misconfigurations: tightening permissions, disabling unnecessary services, rotating exposed credentials, or updating security group rules in cloud environments.
Code fixes apply to application-layer vulnerabilities found through SAST/DAST scanning. The development team patches the vulnerable code, runs regression tests, and deploys through the CI/CD pipeline.
Compensating controls serve as a bridge when immediate remediation is not possible. Common examples include:
Compensating controls are not a substitute for remediation. They reduce risk temporarily while the permanent fix is scheduled and executed.
A remediation ticket marked “complete” means nothing until you verify the fix actually worked. Verification closes the loop and proves risk reduction.
The verification process includes:
Organizations that skip verification often discover that patches were applied incorrectly, were rolled back during a maintenance window, or simply did not address the root cause. Without verification, your remediation metrics are unreliable.
Remediation is not a project; it is a continuous cycle. Every completed fix generates data that should feed back into the process:
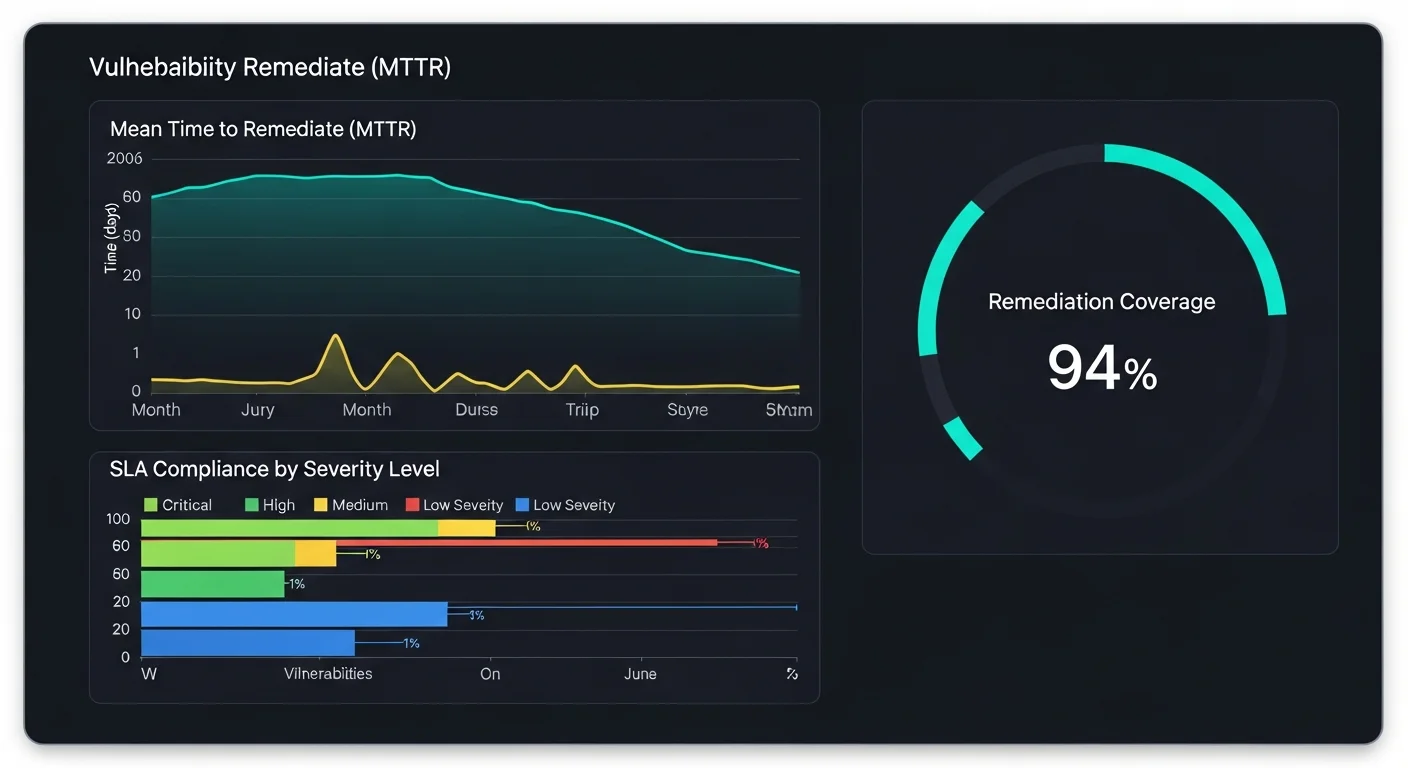
This data powers executive reporting, audit readiness, and continuous process improvement. Security leaders who can show a declining MTTR and increasing SLA compliance are proving measurable risk reduction, which is the language leadership understands.
Service-level agreements create accountability. Without defined timelines, remediation operates on a “best effort” basis, which in practice means critical vulnerabilities sit unresolved for months.
Here is a practical SLA framework based on industry benchmarks and regulatory guidance from CISA:
| Severity | Target SLA | Rationale |
|---|---|---|
| Critical (CVSS 9.0-10.0) | 24-72 hours | Actively exploited or trivially exploitable. CISA recommends 15 days max. |
| High (CVSS 7.0-8.9) | 30 days | Significant risk but may require change control. |
| Medium (CVSS 4.0-6.9) | 60 days | Moderate risk; batch remediation is acceptable. |
| Low (CVSS 0.1-3.9) | 90 days | Minimal immediate risk; address during routine maintenance. |
These timelines are starting points. Adjust them based on asset criticality, regulatory requirements (PCI DSS, HIPAA, SOX), and your organization’s risk appetite. The key principle: define the SLA, measure against it, and escalate when it is breached.
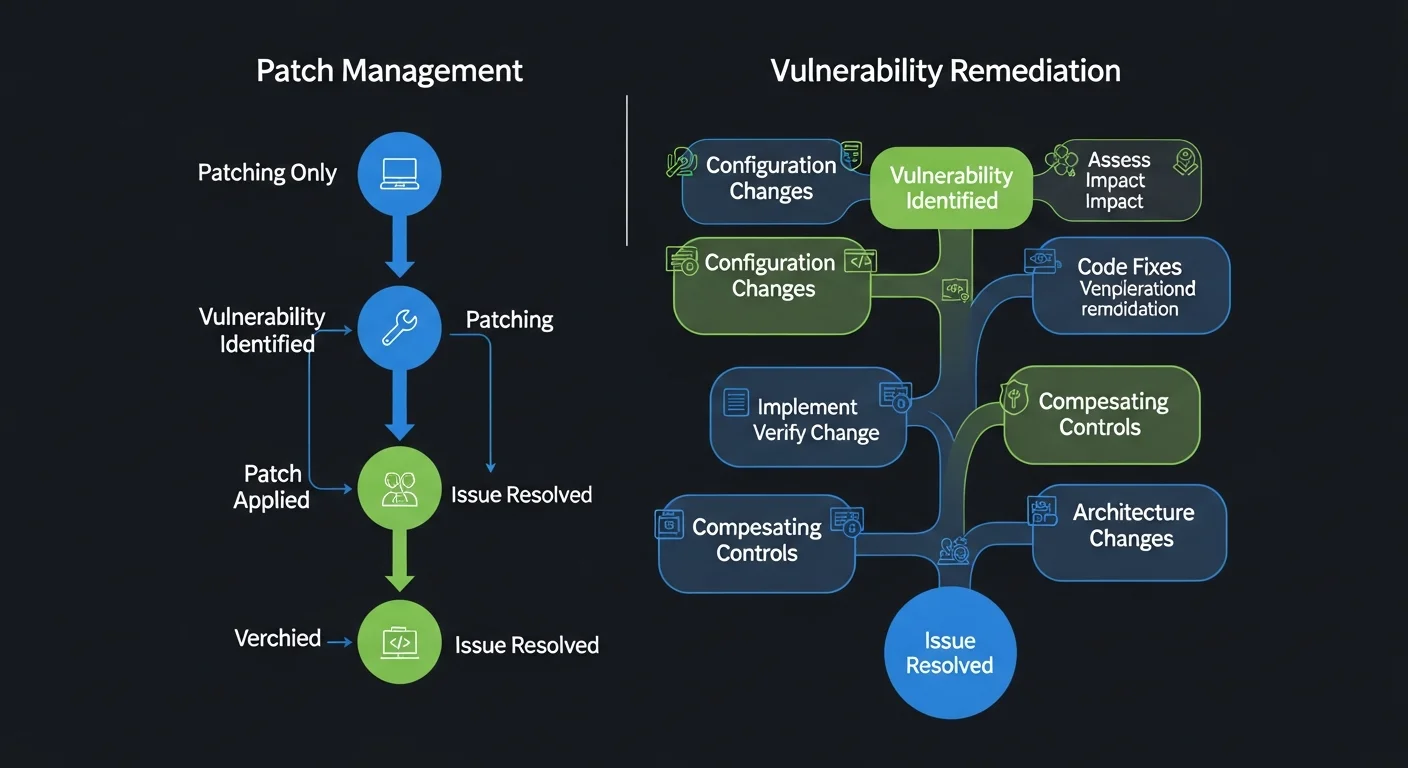
Patch management and vulnerability remediation are related but not synonymous. Confusing the two creates blind spots.
Patch management is a subset of remediation focused specifically on deploying software updates. It covers patch identification, testing, scheduling, deployment, and verification. Patch management tools automate the distribution of vendor updates across endpoints, servers, and applications.
Vulnerability remediation is the broader discipline. It includes patching but also encompasses configuration hardening, code fixes, compensating controls, architecture changes, and risk acceptance decisions. A vulnerability caused by a misconfigured cloud storage bucket cannot be “patched,” it must be reconfigured. A zero-day with no available patch requires compensating controls, not a patch management workflow.
Organizations that equate remediation with patching inevitably miss entire categories of risk: misconfigurations, design flaws, insecure defaults, and vulnerabilities in legacy systems where patches are no longer available.
The biggest bottleneck in vulnerability remediation is not detection or prioritization. It is the gap between “we know about this vulnerability” and “someone is actively working on fixing it.” Manual processes fill that gap with delays: emails that go unread, tickets that route to the wrong team, escalations that happen too late.
Automated remediation orchestration eliminates these friction points by connecting your vulnerability data directly to your operational workflows.
Here is what that looks like in practice with a platform like Hive Pro’s Uni5 Xposure:
This end-to-end orchestration is what transforms remediation from a manual, error-prone process into a systematic operation. Organizations using automated orchestration typically see MTTR reductions of 60-80% on critical vulnerabilities because the handoff delays that inflate manual remediation simply disappear.
Building on the process framework above, here are the practices that separate high-performing remediation programs from those constantly fighting their backlog:
Maintain a complete, current asset inventory. You cannot remediate what you do not know exists. Ensure your asset discovery and attack surface management covers every endpoint, cloud workload, container, and shadow IT asset in your environment.
Prioritize by actual risk, not CVSS alone. Combine severity scores with exploitability data (EPSS), asset criticality, and real-time threat intelligence. A platform that provides context-aware prioritization makes this practical at scale.
Automate everything that does not require human judgment. Ticket creation, assignment routing, SLA tracking, escalation, and verification scanning should all run automatically. Reserve human expertise for exception handling and strategic decisions.
Establish clear ownership for every vulnerability. Every finding needs a named owner and a deadline. Unassigned vulnerabilities do not get fixed.
Document compensating controls with expiration dates. When you apply a temporary mitigation instead of a permanent fix, document it and set a review date. Compensating controls that become permanent are technical debt in disguise.
Validate every fix before closing the ticket. Rescan, test, and confirm. A closed ticket without verification is a false sense of security.
Report on outcomes, not activities. Leadership does not care how many tickets you closed. They care about MTTR reduction, SLA compliance, and overall risk posture improvement.
Ready to cut your MTTR and close your remediation gap? Book a demo of Uni5 Xposure.
What is vulnerability remediation?
Vulnerability remediation is the process of fixing security weaknesses in your systems, applications, and infrastructure to prevent exploitation. It includes the full lifecycle: triage, prioritization, assignment, applying fixes (patches, configuration changes, or compensating controls), verification, and continuous tracking against defined SLAs.
What is the difference between vulnerability remediation and patch management?
Patch management is one component of vulnerability remediation. It focuses specifically on deploying software updates to fix known vulnerabilities. Vulnerability remediation is the broader practice that also includes configuration hardening, code fixes, compensating controls, and risk acceptance decisions for weaknesses that cannot be patched.
How should organizations prioritize vulnerabilities for remediation?
Prioritize based on actual risk, not just CVSS scores. Factor in whether the vulnerability is being actively exploited (check the CISA KEV catalog), the criticality of the affected asset, available threat intelligence, and the potential business impact. This context-driven approach focuses your team on the vulnerabilities that matter most.
What are compensating controls in vulnerability remediation?
Compensating controls are temporary security measures applied when immediate remediation is not possible. Examples include network segmentation, WAF rules, enhanced monitoring, and access restrictions. They reduce risk while the permanent fix is scheduled, but they are not a long-term substitute for actual remediation.
How long should it take to remediate a critical vulnerability?
Industry best practice recommends remediating critical vulnerabilities within 24-72 hours. CISA recommends a maximum of 15 calendar days for vulnerabilities on its Known Exploited Vulnerabilities list. The actual timeline should be defined in your organization’s SLA framework and adjusted based on asset criticality and operational constraints.
How does automated orchestration reduce remediation time?
Automated orchestration eliminates the manual handoffs that create delays: ticket creation, team assignment, SLA tracking, and verification scanning all happen automatically. By connecting vulnerability data directly to ITSM platforms like Jira and ServiceNow, orchestration platforms cut the gap between detection and active remediation, typically reducing MTTR by 60-80% on critical findings.