Comprehensive Threat Exposure Management Platform
Security leaders do not need another framework for the sake of paperwork. They need a practical way to decide which cybersecurity frameworks help the business govern risk, harden defenses, and validate whether controls can withstand real attack behavior. This guide compares NIST CSF, CIS Controls, and MITRE ATT&CK so you can see where each framework fits, where it falls short, and how to combine them inside a modern exposure management program.
Ready to move from framework alignment to measurable exposure reduction? Explore Hive Pro Uni5 Xposure to see how unified CTEM helps teams prioritize and validate what matters most.
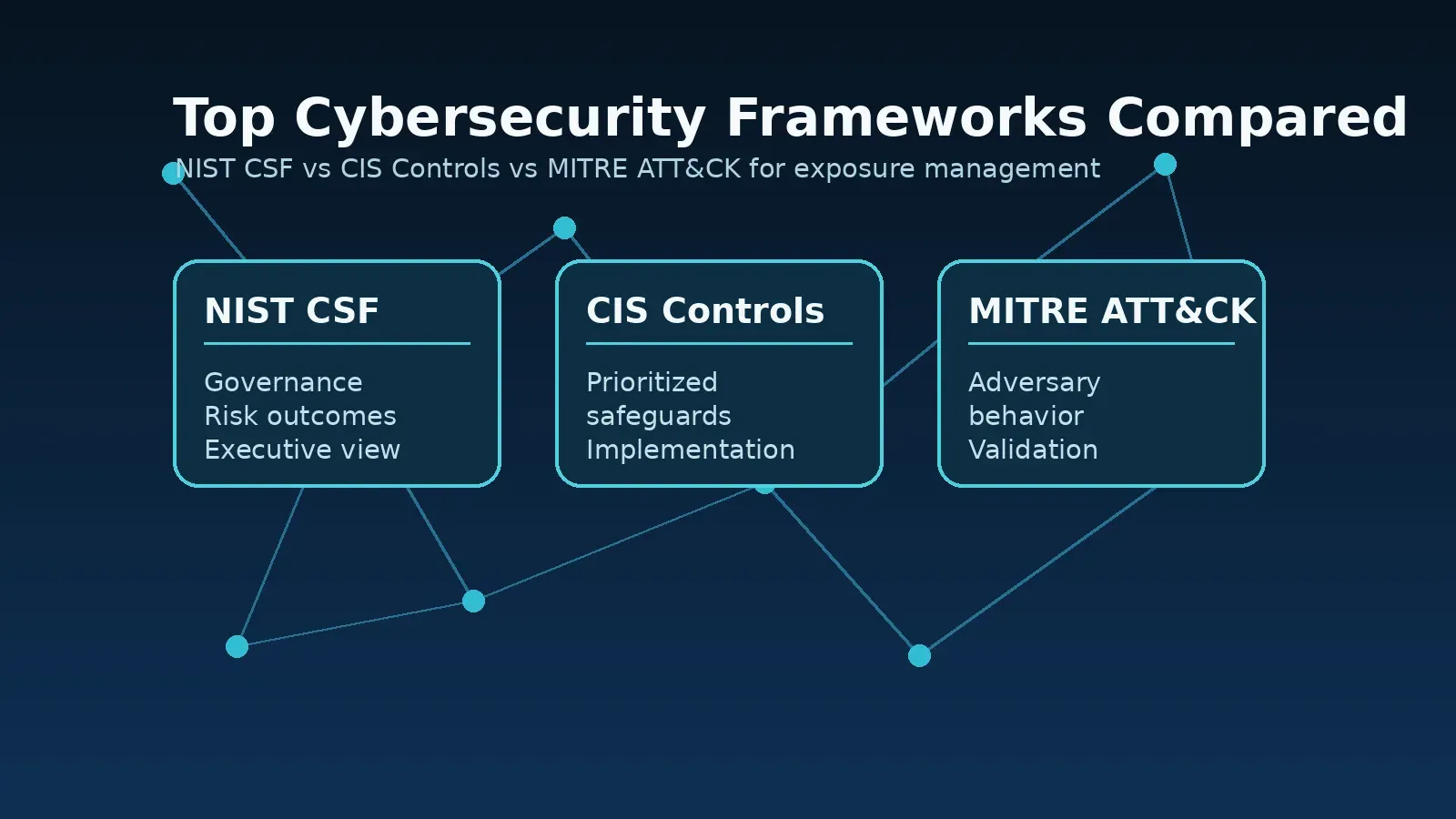
The short answer: NIST CSF is best for governance and enterprise risk communication, CIS Controls is best for prioritized technical safeguards, and MITRE ATT&CK is best for understanding adversary behavior and validating defenses. The strongest programs use all three. NIST defines the risk outcomes the business cares about, CIS translates those outcomes into safeguards, and MITRE ATT&CK tests whether those safeguards work against real techniques.
| Framework | Best Use | Primary Audience | Strength | Limitation |
|---|---|---|---|---|
| NIST Cybersecurity Framework | Risk governance, executive reporting, program maturity | CISOs, risk leaders, boards, compliance teams | Creates a shared language for cybersecurity risk | Does not prescribe exactly which technical controls to deploy |
| CIS Controls | Prioritized safeguards and implementation planning | Security operations, infrastructure, IT, audit teams | Gives teams a concrete control baseline | Needs business context to avoid checklist-driven security |
| MITRE ATT&CK | Adversary emulation, threat hunting, detection engineering, validation | SOC, red teams, blue teams, CTI, detection teams | Maps defenses to real-world attacker tactics and techniques | Can be too technical without a governance layer |
For a CISO, the decision is less about choosing one winner and more about sequencing the work. Start with NIST to define outcomes and governance priorities. Use CIS Controls to build a practical defensive baseline. Use MITRE ATT&CK to test those controls against the attacker techniques most relevant to your environment.
The NIST Cybersecurity Framework, often called NIST CSF, is a risk management framework designed to help organizations understand, assess, prioritize, and communicate cybersecurity risk. NIST CSF 2.0 is built around six core functions: Govern, Identify, Protect, Detect, Respond, and Recover. That structure makes it useful for translating technical security work into board-level risk language.
NIST is especially valuable when a security program needs alignment across leadership, compliance, audit, and operations. It helps answer questions such as: What are our most important cyber risks? Which capabilities are mature? Which functions need investment? How do we explain progress to executives without drowning them in vulnerability counts?
The limitation is that NIST CSF is outcome-oriented, not implementation-prescriptive. It tells you what outcomes matter, but it does not give your team a step-by-step control build sheet. That is why NIST often works best when paired with CIS Controls and a validation framework such as MITRE ATT&CK.
The CIS Critical Security Controls are a prioritized set of safeguards designed to defend against common cyber attacks. CIS Controls are practical by design. They help teams move from broad risk objectives into specific security actions such as inventory management, vulnerability management, secure configuration, account control, logging, malware defense, and data protection.
CIS is useful because it forces focus. Security teams rarely fail because they lack possible work. They fail because everything looks urgent. CIS Controls provide a defensible sequence for improving baseline security, especially when teams need measurable progress across endpoints, networks, cloud environments, applications, and identities.
The risk with CIS is that teams can treat it as a checklist. A safeguard may be implemented, but still not reduce the most relevant business risk. For example, patching all critical CVEs by CVSS score may look good on a control dashboard, but it may not address which vulnerabilities are actually exploited, exposed, or connected to critical assets. That is where threat intelligence for exposure management becomes essential.
MITRE ATT&CK is a globally accessible knowledge base of adversary tactics, techniques, and procedures based on real-world observations. Instead of starting with controls or governance categories, ATT&CK starts with how attackers behave. It organizes techniques across the attack lifecycle, from initial access and execution to persistence, privilege escalation, lateral movement, command and control, exfiltration, and impact.
For exposure management, MITRE ATT&CK is powerful because it helps teams ask a harder question: which attacker techniques can succeed in our environment right now? That question changes vulnerability management from a static list of findings into an adversary-informed program.
MITRE ATT&CK is not a full governance framework. It does not replace NIST, and it does not replace a control baseline. Instead, it makes both more relevant by showing whether your controls and priorities match the techniques attackers actually use. Hive Pro has covered this connection in more depth in its guide to the MITRE ATT&CK framework for exposure management.
If you are comparing NIST, CIS, and MITRE ATT&CK, choose based on the problem you need to solve. Each framework answers a different question.
That distinction matters because many cybersecurity programs confuse activity with risk reduction. A vulnerability team can close thousands of tickets and still leave the most exploitable attack path untouched. A compliance team can map dozens of controls and still miss a technique used by an active threat group. A SOC can tune detections without knowing whether the underlying exposure has been remediated.
Want to connect frameworks, threat intelligence, validation, and remediation in one operating model? See how a CTEM platform operationalizes all five Gartner CTEM stages.
Continuous Threat Exposure Management, or CTEM, gives security teams a practical way to move beyond periodic assessments and reactive vulnerability queues. In a CTEM program, frameworks are not static documents. They become inputs into a continuous cycle of scoping, discovery, prioritization, validation, and mobilization.
NIST helps define governance, business context, and risk outcomes. CIS helps define the safeguards and operational controls needed to reduce exposure. MITRE ATT&CK helps validate whether those safeguards can resist attacker behavior. Together, they form a useful operating model:
This is where framework comparison becomes operational. The goal is not to prove that a control exists. The goal is to prove that the organization is reducing exploitable exposure across the assets and attack paths that matter most.
No single framework does everything. NIST gives structure, CIS gives controls, and MITRE gives adversary context. Using one without the others can create blind spots. NIST without technical controls can stay too abstract. CIS without risk context can become checkbox security. MITRE without governance can become a technical exercise that is hard to explain to leadership.
Severity scores are useful, but they are not enough. A high-severity vulnerability on a low-value, well-isolated asset may be less urgent than a lower-severity exposure on an internet-facing system connected to a critical business process. Modern programs need risk scoring that accounts for exploitability, asset criticality, compensating controls, and attacker activity. For more on this issue, read Hive Pro’s guide on going beyond CVSS for critical CVE vulnerability analysis.
Control mapping is not the same as control effectiveness. A spreadsheet can show that endpoint protection, logging, access management, and patching are in place. It cannot prove that an attacker technique would fail. MITRE ATT&CK mapped validation, BAS, purple teaming, and attack path analysis help close that gap.
Compliance is important, but compliance alone does not guarantee resilience. The best programs use compliance requirements as one input into exposure management. That approach helps teams prove control coverage while also showing which exposures create real business risk. Hive Pro discusses this connection in its CTEM compliance guide for SOC 2, ISO 27001, and PCI-DSS.
The best cybersecurity framework depends on your current maturity and business objective.
For most mature security teams, the answer is not NIST vs CIS vs MITRE. The answer is NIST plus CIS plus MITRE, connected by exposure data, threat intelligence, validation, and workflow automation. That combination helps CISOs move from fragmented security activity to a defensible risk reduction program.
Hive Pro Uni5 Xposure is built for security teams that need to turn framework alignment into action. The platform unifies exposure data, scanner findings, threat intelligence, AI-powered prioritization, validation, and remediation workflows so teams can focus on the exposures most likely to create business impact.
Instead of treating NIST, CIS, and MITRE as separate documents, Uni5 Xposure helps teams connect them inside a CTEM operating model. Security leaders can align work to governance outcomes, identify control gaps, enrich findings with real threat intelligence, validate exposures through BAS and attack path analysis, and mobilize remediation across the tools teams already use.
If your team is ready to make frameworks operational, request a closer look at Hive Pro Uni5 Xposure and see how continuous exposure management turns guidance into measurable risk reduction.
The top cybersecurity frameworks include the NIST Cybersecurity Framework, CIS Controls, and MITRE ATT&CK. NIST is best for risk governance, CIS is best for prioritized safeguards, and MITRE ATT&CK is best for adversary-informed validation and detection planning.
NIST is not better than CIS Controls. It serves a different purpose. NIST helps organizations govern and communicate cybersecurity risk, while CIS Controls helps teams implement prioritized safeguards. Many organizations use NIST for strategy and CIS for control execution.
MITRE ATT&CK is a framework and knowledge base of adversary tactics, techniques, and procedures. It is most useful for threat-informed defense, detection engineering, red team exercises, purple team exercises, BAS planning, and exposure validation.
Usually not. One framework may support a specific need, but mature programs combine multiple frameworks. NIST supports governance, CIS supports control implementation, and MITRE ATT&CK supports validation against real attacker behavior.
Cybersecurity frameworks support CTEM by giving teams structure, controls, and adversary context. NIST helps define risk outcomes, CIS helps prioritize safeguards, and MITRE ATT&CK helps validate whether controls reduce exposure to real attack techniques.
Cybersecurity frameworks are most valuable when they help teams make better decisions. NIST CSF helps leaders govern risk. CIS Controls helps teams implement the right safeguards. MITRE ATT&CK helps defenders validate security against real-world attacker behavior. When combined through CTEM, these frameworks become more than reference material. They become a practical system for reducing exposure, proving progress, and focusing security work on the risks that matter most.