Every CISO knows the frustration: you understand the exposure risk facing your organization, you know that a Continuous Threat Exposure Management program would fundamentally change your security posture, and yet, when budget season arrives, CTEM is one of the first line items questioned.
Ready to build a board-ready business case for CTEM? Explore Hive Pro Uni5 Xposure and request a demo to see how CTEM investment pays for itself.
The problem is not the technology. It is the translation. CISOs who successfully secure CTEM funding do not just present threat data; they present a business case. They speak CFO fluently. They quantify risk in dollars, not CVE counts. And they frame CTEM not as a security purchase, but as a business resilience investment.
This guide gives you the framework, metrics, and language to do exactly that. Whether you are presenting to a CFO, a board audit committee, or a skeptical CEO, here is how to build a business case for CTEM that wins approval.
Why CISOs Struggle to Win CTEM Budget Approval
CISOs struggle to win CTEM budget because cybersecurity value is invisible: success means incidents that never happen, not outcomes a CFO can measure. CTEM compounds this by asking for a continuous program investment rather than a one-time tool purchase, which sounds open-ended to financial leadership evaluating competing priorities.
Cybersecurity investments are inherently difficult to justify because their value lies in what does not happen. Unlike a new sales tool or manufacturing upgrade, a CTEM program’s success is measured by incidents avoided, exposure windows closed, and breaches that never occur. This invisibility creates a fundamental challenge when competing for budget against initiatives with clearer, faster returns.
CTEM faces an additional layer of complexity: it is a program, not a point solution. You are asking leadership to invest in a continuous, evolving practice rather than a one-time technology purchase. Without a structured business case, that ask sounds expensive and open-ended, exactly the kind of proposal that stalls in committee.
The good news: CISOs who approach this strategically consistently secure CTEM funding. The key is shifting from a security-centric argument to a business risk argument.
What Does Reactive Security Actually Cost Your Organization?
Reactive security carries three compounding costs that most organizations underestimate: escalating breach costs, silent budget drain from tool sprawl, and productivity losses from remediation inefficiency. Establishing these baseline costs before presenting CTEM pricing reframes the entire conversation from “new spend” to “better allocation of existing spend.”
Before presenting what CTEM costs, establish what reactive security already costs, and what it will cost when the next breach hits.
Breach Costs Are Accelerating
The IBM Cost of a Data Breach Report consistently shows average breach costs exceeding $4 million globally, with critical infrastructure sectors (financial services, healthcare, government) seeing costs well above that threshold. For enterprises, costs routinely reach $8 to $15 million when you factor in forensic investigation, legal liability, regulatory fines, remediation, and reputational damage. These are not hypothetical numbers; they represent a quantifiable financial risk that belongs in your business case.
Tool Sprawl Is Draining Budget Silently
Most enterprise security teams manage 10 or more security tools. According to Hive Pro platform data aggregated from enterprise customer deployments (Hive Pro Customer Outcomes Report, 2024), organizations consolidating onto a unified CTEM platform have reported saving an average of $150,000 or more annually from eliminating redundant tool licenses and reducing the FTE hours spent reconciling disparate findings. That is budget your organization may be hemorrhaging today, before a single breach occurs.
Remediation Inefficiency Has a Hidden Price Tag
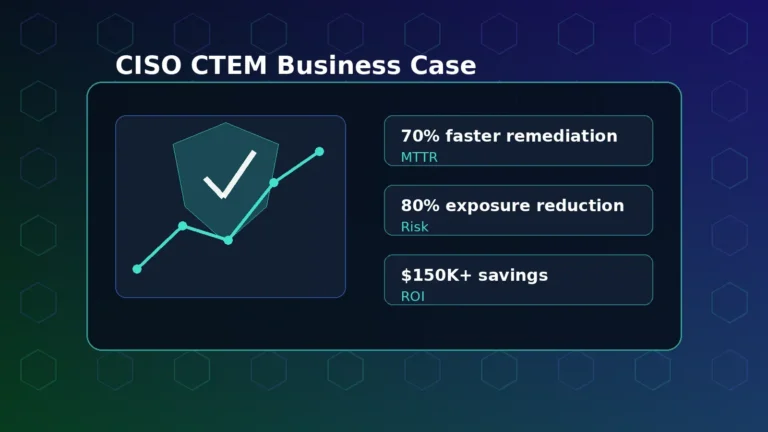
For finance leaders, remediation inefficiency looks like a staffing and operational cost problem. For the business, it is a compounding financial liability: every additional day a critical vulnerability remains unpatched extends the window of exposure and raises the expected cost of a breach. When vulnerability management teams work from fragmented, uncontextualized data, they patch the wrong things first, or worse, they are overwhelmed and patch nothing systematically. This operational failure translates directly into financial exposure: prolonged attack surfaces, costly incident response, and analyst hours spent on manual triage rather than strategic work. Organizations implementing CTEM programs have reduced remediation time by up to 70% (from three weeks to three days on average), per Hive Pro customer outcome data. The inverse of that efficiency is what reactive security costs in analyst hours, prolonged exposure windows, and downstream incident response.
Quantifying these existing costs before presenting CTEM’s price tag reframes the entire conversation: you are not asking for more budget; you are proposing to spend existing budget more effectively while reducing total risk exposure.
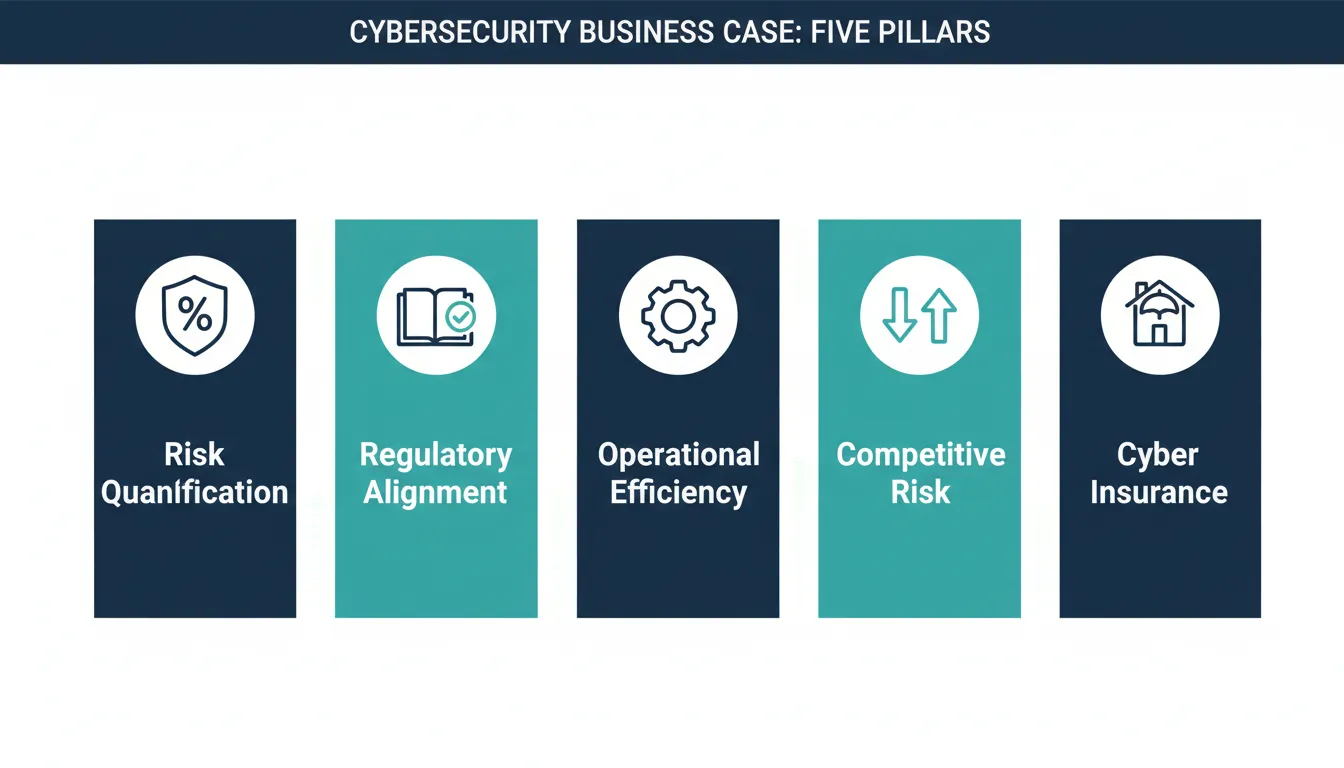
What Are the Five Pillars of a Compelling CTEM Business Case?
A compelling CTEM business case rests on five pillars: financial risk quantification, regulatory compliance alignment, operational efficiency gains, competitive and reputational risk, and cyber insurance impact. Together, these pillars give financial leadership multiple independent reasons to approve CTEM investment, reducing reliance on any single argument.
1. Risk Quantification in Financial Terms
Boards and CFOs think in probability-weighted financial outcomes, not vulnerability counts. Instead of presenting the number of critical CVEs in your environment, present the annualized loss expectancy (ALE) from your top three exposure scenarios. Use frameworks like FAIR (Factor Analysis of Information Risk) to translate technical exposure into dollar-denominated risk.
For example: “Our analysis shows that our current exposure to ransomware via unpatched network vulnerabilities carries an annualized loss expectancy of $3.2 million. A CTEM program reduces that exposure by 80%, which represents $2.6 million in avoided risk per year against a program cost of $X.” This framing converts security talk into investment logic that financial leadership can evaluate on its own terms.
2. Regulatory and Compliance Alignment
CTEM programs directly support compliance mandates that already have board-level attention: SEC cybersecurity disclosure rules, DORA (Digital Operational Resilience Act) for financial institutions, NIST CSF 2.0 Govern function, and PCI DSS v4.0 requirements. Mapping your CTEM program to specific compliance requirements converts a discretionary security investment into a compliance necessity, which is a fundamentally different budget conversation.
This is particularly effective when your organization faces an upcoming audit cycle or operates in a regulated industry. Tie CTEM directly to reducing audit findings and demonstrating proactive compliance posture.
3. Operational Efficiency Gains
One of CTEM’s most underutilized business case components is the productivity argument. Organizations that implement unified vulnerability and threat prioritization platforms eliminate the analyst time spent context-switching between multiple consoles, correlating redundant findings, and manually triaging thousands of alerts. This recovered capacity has real dollar value that finance teams understand.
Hive Pro customers have reported an average of 5x improvement in security team productivity after deploying Uni5 Xposure, based on the Hive Pro Customer Outcomes Report (2024). Translate that into FTE hours recovered, and the math often shows CTEM paying for itself through operational efficiency alone, before the breach prevention value is counted.
4. Competitive and Reputational Risk
Boards increasingly understand that a major breach does not just cost money; it costs customers, partnerships, and market position. Enterprise procurement now includes security questionnaires as standard practice. Organizations demonstrating mature CTEM programs win RFPs that competitors with reactive security postures lose.
Frame CTEM as a customer trust and revenue enablement investment: “Our largest enterprise accounts are asking about our CTEM program in procurement reviews. This is not just about security. It is about maintaining the ability to close enterprise deals.”
5. Cyber Insurance and Total Cost of Risk
Cyber insurers are scrutinizing organizations’ vulnerability management practices more rigorously than ever. Premiums are rising, coverage limits are narrowing, and exclusions are expanding for organizations that cannot demonstrate proactive exposure management. A mature CTEM program is increasingly the differentiator between favorable insurance terms and uninsurable risk.
Get a quote from your broker on premium impact of implementing continuous threat exposure management. The annual premium savings alone may cover a significant portion of CTEM program costs, giving you a quick-win ROI argument that resonates with CFOs focused on total cost of risk.
How Do You Quantify CTEM ROI for Financial Leadership?
CTEM ROI is quantified across four categories: avoided breach costs (using probability-weighted breach scenarios), tool consolidation savings (license and FTE overhead eliminated), analyst productivity recovery (hours freed from manual triage), and remediation velocity improvement (exposure-days eliminated per quarter). A three-year model combining all four typically shows payback within 12 to 18 months.
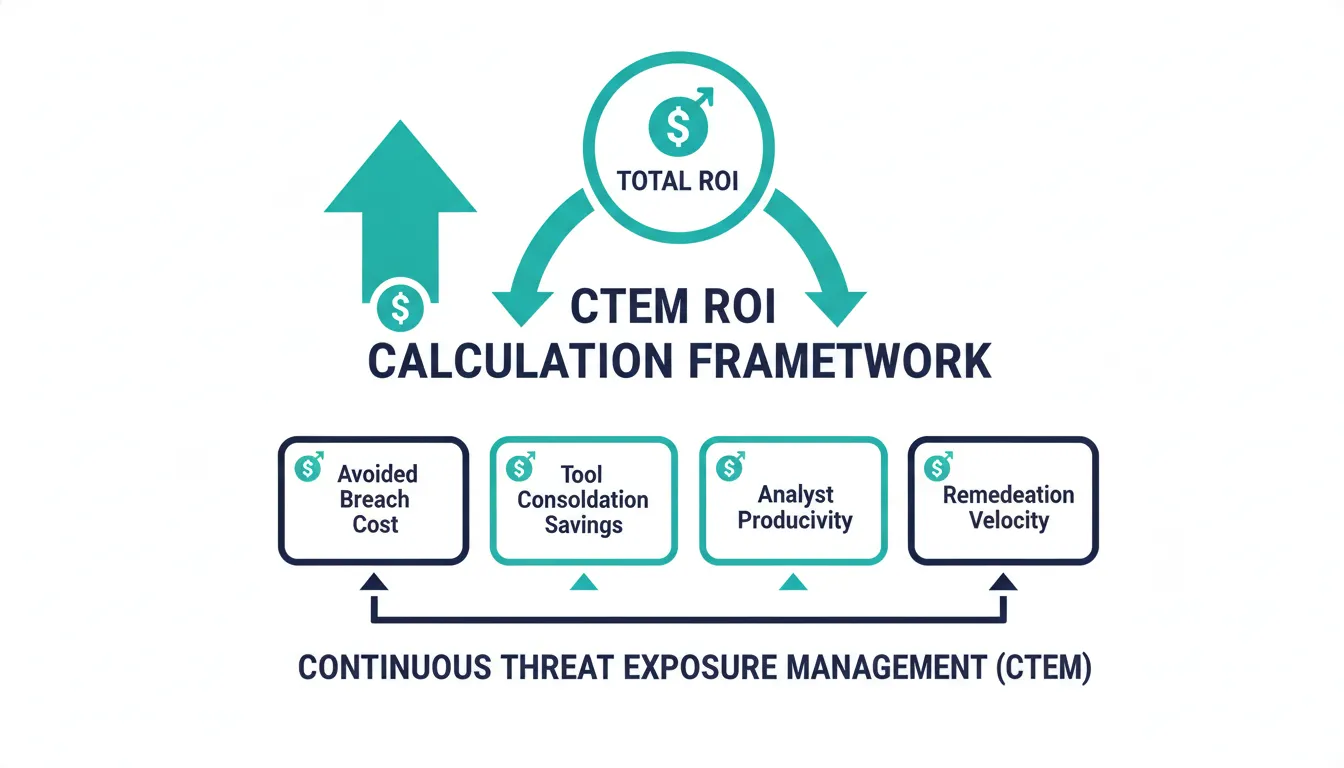
Avoided Breach Cost
Use Gartner’s finding that organizations implementing CTEM programs will be three times less likely to suffer breaches by 2026 compared to those relying on traditional vulnerability management. If your current annualized breach probability is 15% and your expected breach cost is $5 million, CTEM reduces that probability to approximately 5%, representing $500,000 in avoided risk per year. This is the headline number most boards respond to most strongly.
Tool Consolidation Savings
Audit your current security tool stack. Identify redundant capabilities that a unified CTEM platform would replace. Organizations moving to a platform like Uni5 Xposure, which includes native scanners for code, containers, cloud, web applications, network, and mobile, plus 50 or more integrations, typically eliminate three to five point solutions. Calculate the license costs, training overhead, and integration maintenance costs eliminated to build the consolidation savings line item.
Analyst Productivity Recovery
Estimate the hours your vulnerability management team currently spends on manual triage, tool context-switching, and remediation coordination. Apply a fully-loaded cost per FTE hour. If CTEM reduces manual analyst work by 70%, multiply those recovered hours by your FTE cost. For a 5-person VM team at $120,000 fully loaded per analyst, a 70% productivity improvement represents $420,000 in recovered analyst value annually, a compelling standalone ROI argument.
Remediation Velocity Impact
Every day a critical vulnerability sits unpatched is a day of exposure. If CTEM reduces your mean time to remediate (MTTR) from 21 days to 6 days, quantify the exposure window reduction in terms of days-at-risk across your vulnerability backlog. For organizations with hundreds of critical vulnerabilities, this can represent tens of thousands of exposure-days eliminated per quarter, each representing real financial risk reduction.
How Do You Build a CTEM Business Case Step by Step?
Building a CTEM business case follows five steps: baseline your current security state and costs, model your top three to five threat scenarios, define full program scope and costs, build a three-year pro forma combining all ROI categories, and tailor the framing for your specific audience. Each step builds on the previous, so skipping baseline documentation undermines the ROI model that follows.
Step 1: Baseline Your Current State
Before you can show improvement, document where you are today. Capture metrics like: current MTTR for critical vulnerabilities, number of security tools in your stack, annual security tool spend, analyst FTE hours spent on manual triage, and recent security incidents and their costs. This baseline is your “before” picture and the foundation for your ROI calculation.
Step 2: Model Your Top Threat Scenarios
Identify the three to five threat scenarios most relevant to your industry and attack surface. Use your existing threat intelligence (or threat intelligence from HiveForce Labs if you are evaluating Hive Pro) to map your exposure to each scenario. Estimate the financial impact if each scenario materialized and the probability under your current security posture.
Step 3: Define CTEM Program Scope and Costs
A complete CTEM business case requires a clear program definition. What are you proposing to implement? What are the all-in costs, including platform licensing, implementation, training, and ongoing management? What timeline are you committing to for full deployment and measurable outcomes? Ambiguity at this stage is a budget killer; precision builds credibility.
Step 4: Build Your Three-Year Pro Forma
Present a three-year financial model showing CTEM program costs alongside quantified benefits: avoided breach costs, tool consolidation savings, productivity gains, and insurance premium reduction. Include a payback period calculation. Most organizations find CTEM pays back within 12 to 18 months when all benefit categories are included, a timeline that typically satisfies CFO hurdle rates.
Step 5: Frame for Your Audience
Tailor your presentation to the room. For the CFO: lead with cost reduction and avoided loss. For the board: lead with risk governance and regulatory alignment. For the CEO: lead with competitive advantage and customer trust. For the audit committee: lead with compliance evidence and control effectiveness. The same data, a different frame. The most effective CISO communicators prepare audience-specific versions of their business case.
How Do You Handle Common Board Objections to CTEM Investment?
The three most common board objections to CTEM investment are: “We already have VM tools,” “How do we know this will reduce risk?”, and “What is the alternative?” Each objection has a data-backed response that reframes the objection as evidence for CTEM, not against it. Preparing these responses in advance signals financial fluency and reduces the risk of a budget stall.
“We already have vulnerability management tools.”
Legacy VM tools identify vulnerabilities; they do not prioritize them intelligently, validate exploitability, or operationalize remediation. Show the gap between the vulnerabilities your current tools find and the ones that are actually exploitable and targeted by threat actors in your industry. Then show what a CTEM-informed prioritization would look like: instead of 10,000 vulnerabilities competing for attention, a focused list of 50 that actually pose imminent risk. The issue is not detection; it is intelligent prioritization.
“How do we know this will actually reduce our risk?”
Point to third-party validation: Gartner’s research on CTEM effectiveness, your industry peers’ outcomes, and platform-specific customer data. Hive Pro customers have achieved 80% reduction in threat exposure and 70% reduction in remediation time per Hive Pro customer outcome reporting. Ask your CTEM vendor to provide customer references who will speak directly to their outcomes. Third-party validation shifts the conversation from vendor claims to peer-verified results.
“This is expensive. What is our alternative?”
Your alternative is maintaining the status quo, and the status quo has a price tag. Present the annual cost of your current tool stack, the estimated cost of the breaches you are statistically likely to experience without CTEM, and the rising cost of cyber insurance for organizations without mature exposure management programs. Make the cost of inaction explicit and financial. Inaction is not free; it is a choice to absorb risk.
How Hive Pro Uni5 Xposure Strengthens Your Business Case
Hive Pro Uni5 Xposure strengthens your CTEM business case by providing a unified platform that operationalizes all five Gartner CTEM stages, delivering measurable outcomes including 80% reduction in threat exposure and 70% faster remediation, the exact metrics boards and CFOs need to approve and sustain a CTEM investment.
For CISOs evaluating CTEM platforms to support their business case, Hive Pro’s Uni5 Xposure platform offers a differentiated value proposition that addresses common board concerns directly.
Uni5 Xposure is the only platform that operationalizes all five stages of Gartner’s CTEM framework, including Scope, Discover, Prioritize, Validate, and Mobilize, in a single unified platform. That unified architecture directly supports the tool consolidation savings argument: instead of five separate platforms performing each stage independently, one platform does all five. The financial case for consolidation writes itself.
The platform’s Unictor AI engine moves prioritization beyond CVSS scores to context-aware risk assessment using real-world threat intelligence from HiveForce Labs, Hive Pro’s in-house research team tracking 230,000 or more vulnerabilities and 250 or more threat actors. This intelligence-driven prioritization is the mechanism behind the 70% reduction in remediation time and 80% reduction in threat exposure that customers achieve per Hive Pro outcome data. Those are outcomes you can cite in your business case alongside third-party Gartner projections.
Hive Pro also offers a comprehensive CTEM resource library including executive guides, case studies, and ROI frameworks designed specifically to help CISOs make the business case for CTEM investment. If you are building your case now, the Hive Pro CISO whitepaper on CTEM is a useful source of validated metrics and frameworks.
The CISO Who Wins Budget Thinks Like a CFO
The CISO who wins CTEM budget is the one who translates security risk into business risk, presenting a quantified three-year financial model with clear ROI, regulatory alignment, and competitive advantage. Treat CTEM as a business resilience investment and you stop competing for budget against other security tools.
The most effective business cases for CTEM share a common thread: the CISOs who built them stopped thinking like security practitioners presenting to a finance audience, and started thinking like business leaders presenting a risk management investment.
When you quantify current exposure costs, demonstrate ROI across multiple benefit categories, align your program to compliance and competitive priorities, and present a clear three-year financial model, CTEM stops being a discretionary security line item and becomes an obvious business investment.
The cyber threat landscape is not waiting for your next budget cycle. Gartner projects that by 2026, organizations with mature CTEM programs will be three times less likely to suffer breaches than their reactive counterparts. The organizations that build their business case now and secure investment now will be the ones building competitive advantage from their security posture rather than recovering from their next incident.
Ready to build your CTEM business case? Explore Hive Pro Uni5 Xposure and request a demo to see how the platform supports every component of your investment case.
Frequently Asked Questions: Building a Business Case for CTEM
What is a CTEM business case and why do CISOs need one?
A CTEM business case is a structured financial and strategic argument for investing in a Continuous Threat Exposure Management program. CISOs need one because security investments compete with non-security priorities for budget, and financial leadership evaluates proposals based on ROI, risk reduction, and compliance value rather than technical vulnerability metrics alone.
How do you quantify CTEM ROI for a CFO presentation?
CTEM ROI is quantified across four categories: avoided breach costs (using probability-weighted loss models like FAIR), tool consolidation savings (eliminated licenses and integration overhead), analyst productivity recovery (hours freed from manual triage), and remediation velocity improvement (exposure-days eliminated). A three-year financial model combining all four typically shows payback within 12 to 18 months.
What compliance frameworks does CTEM support?
CTEM programs directly support SEC cybersecurity disclosure requirements, DORA (Digital Operational Resilience Act) for financial institutions, NIST CSF 2.0’s Govern and Identify functions, and PCI DSS v4.0 vulnerability management requirements. Mapping CTEM to existing compliance obligations converts a discretionary investment into a compliance necessity.
How long does it take for CTEM to show ROI?
Most organizations achieve CTEM payback within 12 to 18 months when all benefit categories are counted: tool consolidation savings, analyst productivity gains, insurance premium reduction, and avoided breach costs. Tool consolidation and productivity gains often materialize within the first six months of full deployment, providing early financial validation before breach prevention ROI compounds.
How does CTEM differ from traditional vulnerability management?
Traditional vulnerability management identifies and inventories vulnerabilities. CTEM extends that to continuous exposure prioritization, exploitability validation, remediation operationalization, and threat actor context. The result is a shift from managing a list of thousands of vulnerabilities to maintaining a dynamic, prioritized view of the 50 to 100 exposures that actually pose imminent risk given your specific threat landscape.
Does a mature CTEM program affect cyber insurance premiums?
Yes. Cyber insurers increasingly require evidence of proactive exposure management as a condition of coverage and favorable premium terms. Organizations that can demonstrate CTEM maturity, including continuous discovery, risk-based prioritization, and documented remediation velocity, are better positioned to negotiate lower premiums, higher coverage limits, and fewer exclusions than organizations relying on reactive vulnerability management alone.
 Critical Threat Research : The Iranian Cyber War Intensifies!
Critical Threat Research : The Iranian Cyber War Intensifies!