Comprehensive Threat Exposure Management Platform
If your security team is drowning in alerts and spending more time triaging than remediating, you know the old approach to vulnerability management is broken. Chasing endless CVEs and trying to stitch together data from a dozen different tools leads to burnout and leaves critical gaps in your defenses. This is the reality many teams using legacy tools face. With its development frozen and end-of-life announced, Kenna can no longer solve these modern challenges. It’s time to stop the cycle of reactive panic-patching. You can replace Kenna (cisco vulnerability management) with Hive Pro to cut through 95% of the noise, get a single unified view of your entire attack surface, and finally focus your team’s energy on the handful of threats that truly matter.
For years, Kenna Security was a go-to for teams looking to move beyond basic CVSS scores and focus on vulnerabilities that posed a real-world threat. It helped many organizations get a handle on risk-based vulnerability management, and for that, it deserves credit. But the security landscape has changed dramatically. What was once a leading approach now struggles to keep up with the complexity of modern attack surfaces and the speed of motivated attackers.
The conversation has shifted from managing individual vulnerabilities to understanding your organization’s total threat exposure. This means looking at everything—your cloud infrastructure, application code, user identities, and all the connections in between. As you plan your security strategy for the coming years, it’s critical to assess whether your current tools can meet these new demands. With Kenna’s development halted and its end-of-life announced, now is the time to find a forward-looking partner to help you build a more proactive and resilient security program with a modern threat exposure management platform.
Kenna was revolutionary because it prioritized vulnerabilities based on active exploitation rather than just static severity scores. However, it was designed for a simpler time. Today’s IT environments are a complex mix of on-premise servers, cloud services, containerized applications, and sprawling codebases. Kenna wasn’t built to provide a unified view across this diverse and dynamic attack surface.
Furthermore, with its development frozen, it won’t receive updates for new industry standards like CVSS v4. This means its risk assessment capabilities will become less accurate over time, leaving your team to work with outdated intelligence. Simply managing known vulnerabilities is no longer enough; you need a platform that provides a complete picture of your exposure and helps you prioritize threats across your entire digital footprint.
Beyond its technical limitations, there’s a hard deadline forcing a change. Cisco has officially announced Kenna Security’s end-of-life. The last day to purchase new licenses is March 10, 2026, and all support will cease on June 30, 2028. This means no new features, no updates, and eventually, no support for a critical part of your security stack.
Waiting until the last minute to migrate puts your organization at significant risk. The process of selecting, implementing, and integrating a new platform takes time and careful planning. By starting your search now, you give your team the space to properly evaluate alternatives and ensure a smooth transition without disrupting your security operations. This isn’t just a tool swap; it’s an opportunity to upgrade your entire strategy.
When you’re weighing your options, it helps to put them side-by-side. Both Kenna Security and Hive Pro aim to help you manage vulnerabilities, but they go about it in fundamentally different ways. Kenna’s risk-based vulnerability management (RBVM) was a step forward, but the landscape has evolved. A modern strategy requires a more proactive and comprehensive approach to get ahead of threats, not just react to them.
Let’s break down how the two platforms compare across four key areas. This will give you a clear picture of how Hive Pro offers a more complete, forward-looking solution for threat exposure management that aligns with where security programs are headed.
Kenna relies on predictive models and external threat feeds to score vulnerabilities. It’s a solid approach, but it can sometimes lack the specific context of your unique environment. Hive Pro takes this a step further with its advanced Vulnerability & Threat Prioritization. What makes this so effective is the intelligence from HiveForce Labs, our in-house threat research team. This gives you a more nuanced understanding of which threats pose a real, immediate danger to your organization, helping you focus your team’s efforts where they matter most instead of just chasing high CVSS scores.
Your attack surface is more than just your known servers and applications; it’s every possible entry point for an attacker. Hive Pro’s approach to Total Attack Surface Management is built on the principle of complete visibility. Our Uni5 Xposure platform continuously scans all possible attack vectors—from cloud assets and IoT devices to your external-facing infrastructure and code repositories. This ensures you have a complete, up-to-date picture of your entire exposure. In contrast, Kenna’s focus is more narrowly centered on known vulnerabilities within discovered assets, which can leave you with critical blind spots in today’s complex and expanding IT environments.
Both platforms use threat intelligence, but how they use it differs significantly. Kenna aggregates data from various external sources to inform its risk scores. Hive Pro, however, is designed to be your central hub for security intelligence. We integrate disparate threat feeds, data from your existing security tools, and our own proprietary research into a single, unified view. This approach transforms siloed data into clear, actionable insights. Instead of just getting a risk score, you get the full context behind a threat, which helps you make faster, more informed decisions about remediation.
A cluttered or disjointed interface can slow your team down when every second counts. Hive Pro is built as a unified platform, not just another point solution. We bring compliance workflows, vulnerability management, and posture monitoring together into one intelligent and intuitive dashboard. This streamlined interface is designed to improve your team’s operational efficiency, making it easier to track progress and collaborate on remediation. While Kenna provides useful data, Hive Pro’s Uni5 Xposure Platform focuses on creating a seamless workflow that guides you from discovery to resolution without having to jump between different tools.
Switching platforms can feel like a huge undertaking, but it’s also a chance to seriously upgrade your security program. Moving on from Kenna isn’t just about finding a replacement; it’s about adopting a more modern, proactive approach to managing your threat exposure. Hive Pro is built from the ground up to help you do exactly that. It goes beyond traditional vulnerability management to give you a complete, forward-thinking framework for reducing risk across your entire organization. Let’s look at a few key areas where Hive Pro stands out and offers a clear path forward for your team.
If your team feels like they’re drowning in a sea of vulnerability alerts, you’re not alone. The sheer volume can make it impossible to know where to start. Hive Pro helps you find the signal in the noise by reducing your vulnerability workload by up to 95%. Instead of just relying on static CVSS scores, our platform uses a multi-factor vulnerability and threat prioritization engine. It analyzes exploitability, threat actor activity, and the business impact of an asset to surface the handful of issues that pose a genuine, immediate threat. This means your team can stop chasing low-risk alerts and focus their time and energy on fixing the vulnerabilities that truly matter.
For years, vulnerability management has been a reactive cycle of scan, panic, and patch. Hive Pro helps you break that cycle and shift to a proactive Continuous Threat Exposure Management (CTEM) strategy. Our Uni5 Xposure platform is designed to give you a continuous, 360-degree view of your attack surface and potential attack paths. Instead of waiting for the next critical vulnerability to be announced, you can actively identify and address weaknesses in your defenses before they can be exploited. This changes your security posture from one of constant defense to one of confident, strategic action.
How much time does your team spend toggling between different dashboards and trying to piece together data from siloed tools? Hive Pro brings all your security intelligence into one place. It integrates data from your existing scanners, asset inventories, and threat intelligence feeds to create a single, unified view of your entire threat landscape. This comprehensive perspective on your total attack surface management allows you to see connections you might have otherwise missed and make faster, more informed decisions. You get actionable insights, not just more data to sift through.
Adopting a new platform shouldn’t mean throwing out the tools you already trust. Hive Pro is built to enhance your current security stack, not replace it. It seamlessly integrates with your existing tools like Qualys, Tenable, and Rapid7, pulling in their data to enrich its analysis. This allows you to get more value from your current investments while streamlining your workflow. By automating data collection and correlation, Hive Pro frees up your team from tedious manual tasks. This allows them to concentrate on higher-value activities like threat hunting and strategic risk reduction, making your entire security operation more efficient.
Moving away from Kenna Security is an opportunity to do more than just swap out a tool; it’s a chance to fundamentally improve your security posture. Instead of staying in a reactive cycle of patching vulnerabilities, you can adopt a proactive Continuous Threat Exposure Management (CTEM) framework. This approach gives you a comprehensive, ongoing program to systematically refine your security priorities and processes.
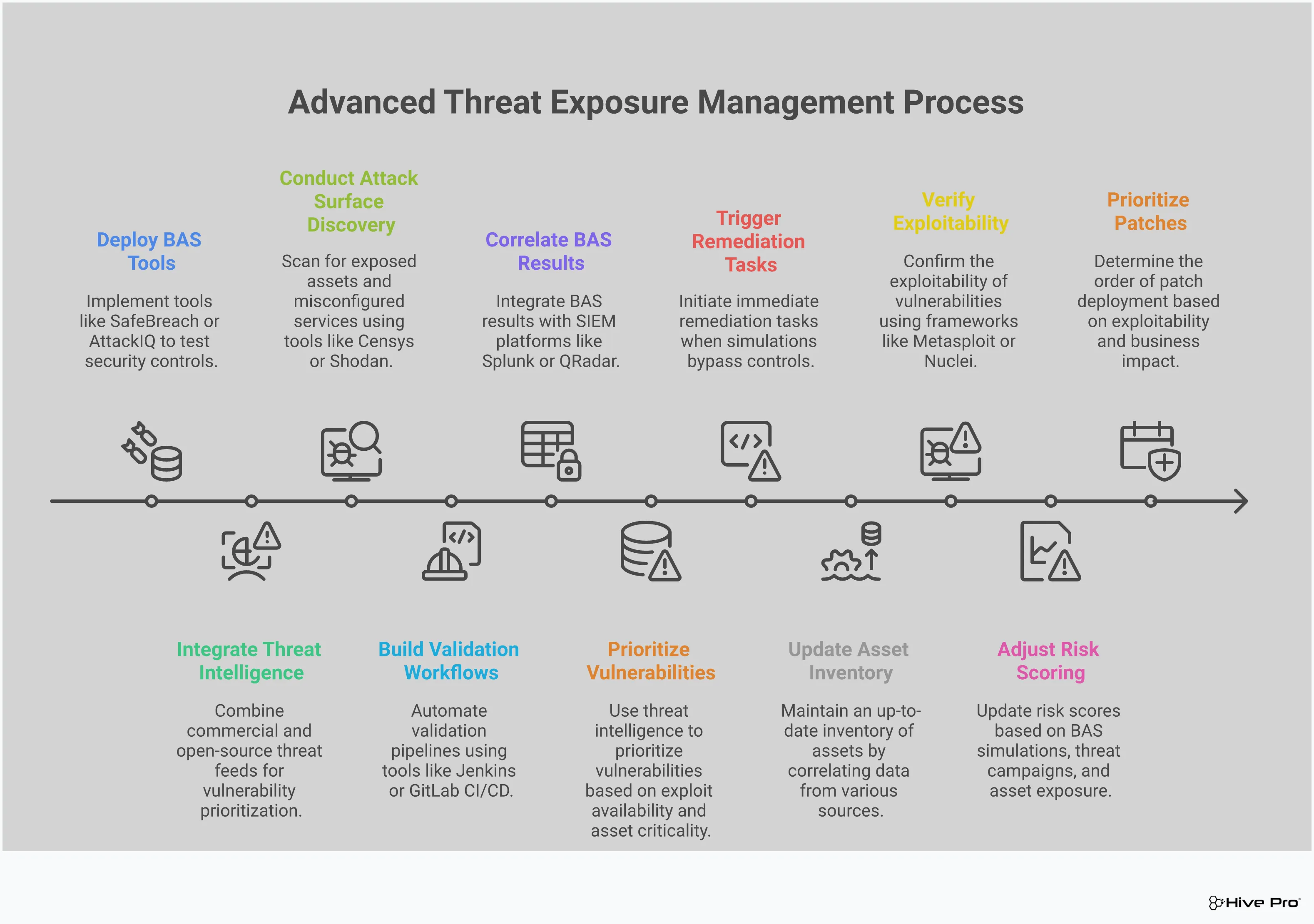
A CTEM program isn’t just about finding vulnerabilities. It’s a five-step cycle that helps you understand your true exposure and take confident action. Hive Pro’s Uni5 Xposure platform is built around this modern framework, guiding you from discovery all the way through to remediation. It helps you answer the most important questions: What are our most critical assets? Where are we exposed? And what should we fix right now? By shifting to this model, you move from simply managing a list of CVEs to actively reducing your attack surface based on real-world threats.
A successful CTEM program follows a clear, repeatable cycle. Hive Pro is one of the few platforms that supports you through all five stages defined by Gartner. It starts with Scoping, where you define the critical assets and business processes that need protection. Next is Discovery, which involves continuously identifying your assets and their associated vulnerabilities across your entire environment. Then comes Prioritization, where you use threat intelligence and business context to determine which exposures pose the greatest risk. Validation tests your security controls against simulated attacks to see if they hold up. Finally, Mobilization turns insights into action by creating and tracking remediation tasks for your IT and DevOps teams.
You can’t protect what you can’t see. A major limitation of older tools is their reliance on periodic scans, which can leave you blind to new threats that emerge between assessments. Hive Pro provides a real-time, comprehensive view of your entire digital footprint. The platform offers Total Attack Surface Management by continuously discovering everything from on-premise servers to cloud configurations and application code. It also unifies data from your existing security tools like Qualys and Tenable, giving you a single, reliable source of truth for all your assets and potential exposures. This constant monitoring ensures you always have an up-to-date picture of your risk.
One of the biggest challenges in security is the overwhelming noise from too many alerts and not enough context. It’s easy to get stuck in analysis paralysis. Hive Pro cuts through that noise by providing clear, actionable guidance. Using threat intelligence from our in-house HiveForce Labs team, the platform helps you focus on the vulnerabilities that matter most. It doesn’t just give you a prioritized list; it helps you with the final, crucial step of mobilization. The platform automates the creation of remediation tickets and helps you track their progress, ensuring that critical exposures are actually fixed and your security posture improves.
Knowing you have vulnerabilities is one thing; knowing if your security controls can actually stop an attack that exploits them is another. This is where Breach and Attack Simulation (BAS) changes the game. Instead of just reacting to a list of CVEs, you can proactively test your defenses against the same tactics and techniques real attackers use. It’s like having a dedicated red team on-demand, constantly running drills to see where your defenses hold strong and where they might buckle.
This proactive approach moves you beyond theoretical risk scores and into the practical reality of your security posture. By simulating attacks, you get clear, actionable evidence of what needs fixing. It’s not about guessing which vulnerability an attacker might use; it’s about confirming which ones they can use and whether your security stack is configured to stop them. This continuous validation loop is a core part of a modern threat exposure management program and a significant step up from the reactive patching cycles of the past.
It’s easy to assume your security tools are working as intended, but assumptions can be dangerous. Hive Pro’s platform helps you validate security controls by simulating real attacks to see if they are effective. This process lets you safely run attack scenarios against your production environment to check if your firewalls, EDR, and other defenses are properly configured to detect and block threats. Think of it as a continuous fire drill for your security stack. You get to find the gaps and misconfigurations before a real adversary does, turning your security from a checklist into a battle-tested defense system.
Not all vulnerabilities are created equal, and not all of them pose a direct threat to your organization. By simulating real-world attack paths, you can see exactly how an attacker could chain together different exposures to reach your critical assets. This context is crucial for making smart decisions. By focusing on the most critical risks and validating defenses, companies can get a much better return on their security investments. You stop wasting time on low-impact issues and instead direct your resources toward mitigating the attack paths that represent a genuine danger to your business.
The sheer volume of vulnerabilities can be overwhelming, but BAS helps you cut through the noise with precision. When you can confirm that a vulnerability is exploitable in your specific environment, it immediately jumps to the top of the list. Hive Pro can identify the top 1% of risks where a company is most likely to be attacked in less than a day. This capability allows your team to prioritize remediation efforts with confidence, knowing they are fixing the issues that matter most. You’re no longer just patching based on a CVSS score; you’re disarming active threats to your organization.
Effective vulnerability management isn’t just about finding weaknesses; it’s about understanding which ones pose a real threat. Generic threat feeds often create more noise than signal, leaving your team to sort through thousands of alerts. This is where the quality of your threat intelligence makes all the difference. Instead of just aggregating data, Hive Pro provides curated, contextual intelligence that helps you see the threats that matter most to your organization. This approach transforms your security program from a reactive cycle of patching to a proactive strategy focused on reducing genuine exposure. By connecting vulnerabilities to active exploits and attacker tactics, you can finally prioritize with confidence and direct your resources where they will have the greatest impact.
Generic threat intelligence feeds can feel like drinking from a firehose. Hive Pro’s prioritization is effective because it’s powered by intelligence from HiveForce Labs, our dedicated in-house threat and vulnerability research team. This isn’t just repackaged data from third-party sources. Our experts are constantly analyzing the threat landscape, tracking attacker campaigns, and identifying emerging exploits. This specialized focus ensures the insights you receive are timely, relevant, and actionable. It gives you a significant advantage, allowing you to base your security decisions on curated intelligence rather than just raw data, so you can stay ahead of attackers.
A long list of CVEs with high CVSS scores doesn’t tell you where to start. You need to know which of those vulnerabilities are actually being used by attackers in the wild. Hive Pro adds that crucial layer of real-world context to your data. Our platform continuously reveals your full attack surface, prioritizes exposure based on real-world threats, and proactively guides remediation. This process transforms cybersecurity from reactive guessing into confident action. By understanding the “why” behind a vulnerability’s risk, your team can make more effective decisions and communicate the urgency of a threat to the rest of the business, ensuring everyone is aligned on vulnerability and threat prioritization.
Your team doesn’t have time to chase down every single vulnerability. The key is to focus on the critical few that attackers are actively targeting. Hive Pro helps you do exactly that by identifying the top 1% of risks where your company is most likely to be attacked in less than a day. This rapid and precise identification cuts through the noise of low-risk alerts, allowing your team to concentrate its efforts on the most pressing threats. This isn’t just about working faster; it’s about working smarter. By zeroing in on the vulnerabilities that represent an imminent danger, you can significantly strengthen your security posture and make the most of your limited resources.
Making a platform change is a big decision, and the budget is always a key part of the conversation. But thinking about cost isn’t just about the license fee. It’s about understanding the total investment and, more importantly, the return you’ll get from it. Let’s break down what to expect when you consider the move from Kenna to Hive Pro, from licensing and implementation to the long-term value you’ll gain.
When you switch platforms, you’re not just buying a new tool; you’re investing in a new way of working. Hive Pro’s Uni5 Xposure platform is designed as a comprehensive Threat Exposure Management solution, which is reflected in its licensing. Instead of patching together multiple tools with separate costs, you get a unified platform that covers the entire CTEM lifecycle. This approach provides more predictable spending and eliminates the hidden costs that come with managing multiple vendors and integrations. Our goal is to give you a clear, all-in-one solution that scales with your needs, so you can focus on securing your organization, not on juggling contracts.
Let’s be direct: transitioning from a tool as embedded as Kenna requires a thoughtful plan. For teams who built their entire vulnerability program on Kenna’s foundation, moving forward means carefully migrating data, workflows, and integrations. This process involves more than just a technical setup; it’s an investment in setting your team up for success. We understand that. Our team works with you to map out a smooth transition, ensuring your historical data is handled correctly and your existing security stack is integrated seamlessly. We help you plan for these one-time costs so you can minimize disruption and start seeing value from day one.
This is where the investment truly pays off. The biggest cost in any security program is often the time your team spends chasing down false positives and wrestling with too many alerts. Juggling multiple, disconnected tools leads to serious inefficiencies and alert fatigue. Hive Pro is built to solve this. By providing a single, unified view of your threat exposure, we help you cut through 95% of vulnerability noise. This massive reduction means your team can stop wasting cycles on low-risk issues and focus their expertise on the threats that actually matter. The return on investment comes from greater efficiency, faster remediation, and a more proactive, confident security posture.
Switching your vulnerability management platform is a big move, but it doesn’t have to be a painful one. With some thoughtful planning, you can make the transition from Kenna to Hive Pro a smooth and strategic upgrade for your entire security program. Think of it less as a replacement and more as an evolution. The key is to focus on three core areas: your data, your team, and your timeline. By addressing each of these head-on, you can sidestep common roadblocks and set your team up for success from day one. Let’s walk through how to manage each piece of the puzzle.
Let’s be honest: moving years of security data can feel like a monumental task. A successful transition requires more than just a simple data dump; it’s an investment in a cleaner, more unified security posture. The good news is that this is an area where Hive Pro is built to help. Instead of wrestling with siloed information from different tools, you can bring it all together. Hive Pro’s platform is designed to integrate disparate threat intelligence feeds, scanners, and APIs into a single, clear view. This process transforms your scattered data into actionable insights, making it easier to see the full picture of your threat exposure without the usual migration headaches.
A new tool means a new way of working, and preparing your team is just as important as migrating your data. Many teams are used to juggling multiple, disconnected solutions for vulnerability management, threat intelligence, and attack simulation. Consolidating these functions into one platform creates massive efficiencies, but it also requires a shift in workflow. The goal is to move your team from managing tools to managing risk. Proactive training and clear communication are essential. By focusing on how the Uni5 Xposure platform simplifies their daily tasks and helps them focus on what matters, you can build excitement and ensure everyone is ready to hit the ground running.
With Kenna’s end-of-sale set for March 2026 and final support ending in June 2028, the clock is ticking. Now is the perfect time to map out a clear transition plan. Use this opportunity to do more than just find a replacement—use it to adopt a more proactive and comprehensive cyber risk program. Start by outlining key milestones: when will you conduct a pilot? When will you migrate historical data? When do you plan to be fully operational on Hive Pro? Thinking through these steps will help you identify where you might need support, allowing you to build a realistic timeline and ensure a seamless switch long before the deadline arrives.
Seeing a tool you rely on head for sunset can be unsettling, but it’s also the perfect opportunity to rethink your strategy and upgrade your capabilities. Moving on from Kenna doesn’t have to be a headache. By breaking the process down into clear, manageable steps, you can ensure a smooth transition that leaves your security posture stronger than before. Let’s walk through how to plan your move, evaluate your options, and build a timeline that works for your team.
The first step is to start planning your move away from Kenna Security well before the key deadlines. With the last day to renew your support contract set for June 11, 2026, now is the time to get organized. Use this transition as a chance to assess what’s working and what isn’t in your current vulnerability management program. Talk to your team about their daily frustrations and wish-list features. What manual tasks are eating up their time? Where are the visibility gaps? Defining these requirements will help you find a replacement that doesn’t just fill a gap but actively improves your workflow and gives you a more unified view of cyber risks.
This isn’t about finding a simple one-to-one replacement for Kenna. It’s your chance to adopt a more modern, proactive approach. Consider moving to a comprehensive threat exposure management platform like Hive Pro to get a more complete picture of your security risks. Look for a partner that offers a true Continuous Threat Exposure Management (CTEM) framework, not just another vulnerability scanner. Schedule demos with your top contenders and come prepared with questions specific to your environment and goals. Don’t be afraid to ask for a pilot program or proof of concept. Seeing how a platform handles your actual data is the best way to validate its effectiveness and ensure it’s the right fit for your team.
With Kenna’s end-of-life on the horizon, it’s crucial to map out your transition. Keep these official dates from Cisco in mind:
Work backward from these deadlines to build your migration roadmap. Your timeline should include key milestones for vendor evaluation, final selection, procurement, data migration, and team training. Breaking the project into smaller phases will keep you on track and prevent a last-minute scramble. A well-planned timeline ensures you have your new solution fully implemented and optimized long before your Kenna support runs out.
My Kenna contract isn’t up for a while. Why should I start looking for a replacement now? While the final end-of-life date seems far away, waiting to migrate puts your security program at a disadvantage. The process of evaluating, purchasing, and implementing a new platform takes time. Starting now gives you the space to make a strategic decision and upgrade your entire approach, rather than being forced into a rushed replacement later. It’s an opportunity to move from a tool that will no longer be updated to a modern platform that evolves with the threat landscape.
Isn’t Hive Pro just another risk-based vulnerability management tool? Not at all. While Kenna helped popularize risk-based vulnerability management (RBVM), the security field has moved toward a more comprehensive strategy. Hive Pro is built for Continuous Threat Exposure Management (CTEM), which is a proactive framework for continuously seeing and reducing your entire attack surface. Instead of just reacting to a prioritized list of vulnerabilities, you get a unified program that helps you understand how attackers could target your critical assets and guides you in closing those gaps before they can be exploited.
How does Breach and Attack Simulation (BAS) help my team more than a simple risk score? A risk score tells you a vulnerability is theoretically dangerous, but BAS tells you if it’s actually a threat in your specific environment. It safely simulates real-world attack techniques to test if your security controls would detect and block an attempt to exploit a vulnerability. This gives you concrete proof of where your defenses are strong and where they need work, allowing you to prioritize fixes based on what can be exploited, not just what a score says.
My team is already overwhelmed with alerts. How does Hive Pro help with that? We understand that alert fatigue is a huge problem. Hive Pro is designed to reduce your vulnerability workload by up to 95%. It does this by combining asset context, exploitability data, and intelligence from our in-house HiveForce Labs research team. This multi-factor approach filters out the low-risk noise and surfaces the small percentage of vulnerabilities that pose a genuine, immediate threat, so your team can stop chasing ghosts and focus on fixing what truly matters.
What makes the threat intelligence from HiveForce Labs different from other sources? Many platforms simply aggregate data from third-party threat feeds, which can add to the noise. HiveForce Labs is our dedicated, in-house research team that actively analyzes the threat landscape, tracks attacker campaigns, and identifies emerging exploits. This means the intelligence powering Hive Pro is curated and contextual, not just a raw data dump. You get actionable insights tailored to current threats, which helps you make faster, more confident decisions.