Comprehensive Threat Exposure Management Platform
For a detailed threat digest, download the PDF file here
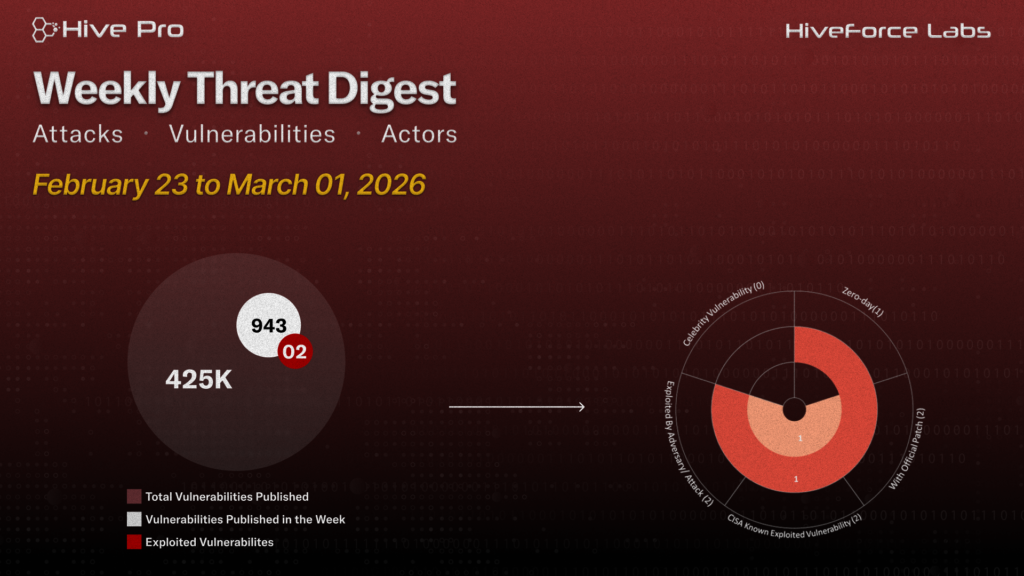
HiveForce Labs has recently made significant advancements in identifying cybersecurity threats. Over the past week, seven major attacks were detected, two critical vulnerabilities were actively exploited, and three threat actors were closely monitored, reflecting an alarming escalation in malicious activities.
CVE-2026-20127 is being actively exploited to achieve unauthenticated control-plane takeover of Cisco SD-WAN environments, enabling persistent network compromise and root access when chained with additional flaws. SANDWORM_MODE npm worm demonstrated self-propagating supply chain compromise by harvesting developer secrets, hijacking CI/CD pipelines, and poisoning AI-assisted workflows.
Meanwhile, MuddyWater’s Operation Olalampo leveraged macro-based spear-phishing to deploy multiple malware families across the MENA region, utilizing diversified C2 infrastructure and suspected AI-assisted development to enable sustained espionage and strategic intrusion operations. Mercenary Akula (UAC-0050) targeted a European financial institution supporting Ukraine through spoofed judicial-domain spear-phishing, deploying RMS via a multi-layered archive chain to establish persistent, stealthy access for likely intelligence collection or financial theft. These rising threats pose significant and immediate dangers to users worldwide.
Subscribe to receive our weekly threat digests and alerts directly in your inbox.