Comprehensive Threat Exposure Management Platform
For a detailed threat digest, download the PDF file here
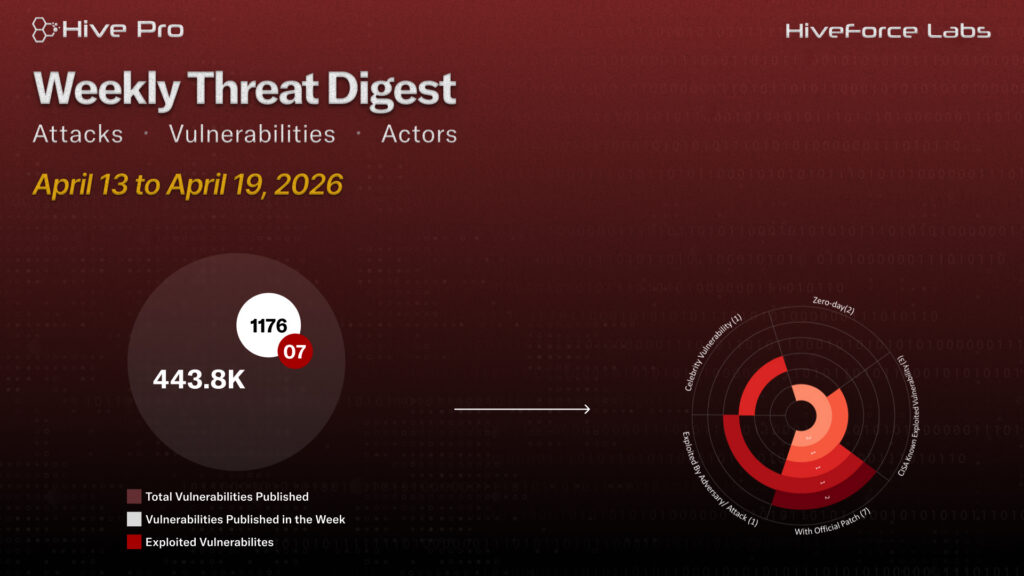
HiveForce Labs has recently made significant advancements in identifying cybersecurity threats. Over the past week, four major attacks were detected, seven critical vulnerabilities were actively exploited, and two threat actors were closely monitored, reflecting an alarming escalation in malicious activities.
CVE-2026-34621 Adobe Acrobat/Reader Critical prototype pollution flaw in the JavaScript engine, exploited via crafted PDFs to trigger privileged APIs like util.readFileIntoStream() for local file access, with data exfiltrated via RSS.addFeed() to attacker-controlled servers. Handala Hack Team Iran-affiliated threat group launched a destructive campaign against GCC critical infrastructure, allegedly wiping 6 PB of data and exfiltrating 149 TB of classified documents via compromised VPN credentials, infostealer-harvested accounts, and targeted phishing.
Meanwhile, Storm-2755 Payroll Heist Financially motivated group leveraging CVE-2025-27152 in Axios and AiTM phishing via fake Microsoft 365 login pages to capture session tokens, bypass MFA, and reroute salary payments through Workday HR systems. PHANTOMPULSE Multi-stage social engineering campaign weaponizing Obsidian community plugins to deliver the PHANTOMPULL loader and PHANTOMPULSE RAT, using LinkedIn and Telegram lures with Ethereum blockchain as a dead-drop C2 resolver. These rising threats pose significant and immediate dangers to users worldwide.
Subscribe to receive our weekly threat digests and alerts directly in your inbox.