Comprehensive Threat Exposure Management Platform
 Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the Report
Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the ReportAttackers don’t just look for a single high-severity vulnerability; they look for a path of least resistance. They connect the dots between a misconfigured cloud service, an exposed credential, and an unpatched server to reach their goal. To build a strong defense, you need to see your environment through the same lens. This is the core idea behind exposure management. So, what is exposure management? It’s a proactive security approach that helps you map potential attack paths, validate your security controls, and understand how different weaknesses can be chained together by an adversary. It shifts your focus from a simple list of flaws to a holistic view of your true exposure.
Exposure management is a continuous security cycle designed to help you stay ahead of threats. Instead of just reacting to problems as they pop up, it’s about proactively finding, validating, and prioritizing security risks across your entire digital footprint. This isn’t just about servers and software; it includes everything from your cloud configurations and web applications to employee identities and connected devices. The core idea is to maintain a clear, ongoing picture of your security gaps so you can fix the ones that matter most before an attacker finds them.
This approach moves security from a series of disconnected tasks to a unified strategy. It’s the foundation of a modern Threat Exposure Management Platform, which brings all these moving parts into a single, manageable view. By truly understanding your full attack surface and how different weaknesses can be connected, you can shift from a constantly defensive posture to a more strategic one. This allows you to focus your team’s time and resources on the exposures that pose a genuine threat to your business operations, rather than getting lost in a sea of low-risk alerts. It’s about working smarter, not just harder, to reduce your overall risk.
For years, security teams have been stuck in a reactive loop, chasing down vulnerabilities as they’re announced. Exposure management changes that dynamic. Instead of just patching a long list of CVEs, this approach helps you think like an attacker. It looks for the subtle weaknesses, like misconfigurations, weak passwords, or exposed credentials, and figures out how a threat actor might connect them to create a real attack path. This shift allows your team to move from simply managing vulnerabilities to actively reducing exposure. It helps you make smarter, faster decisions and provides a clearer way to explain security risks to company leaders, focusing on potential business impact rather than just technical severity scores.
At its heart, an exposure management program is about adding context to your security data. It evaluates risks based on their potential impact on the business and the real-world likelihood of an exploit, not just a generic severity score. This process turns a noisy list of vulnerabilities into clear, business-focused insights. You can start answering questions like, “Which business unit has done the most to reduce its critical risks this quarter?” or “Is our overall organizational risk going up or down?” It connects the dots between a specific weakness, your most important company assets, and active threats, giving you a true understanding of your total attack surface.
If you’ve been in cybersecurity for a while, you’re probably very familiar with vulnerability management. It’s the foundational practice of finding and fixing known weaknesses in your systems. Exposure management doesn’t replace this; it evolves it. Think of it as the next logical step, moving your security program from a reactive, checklist-driven process to a proactive, risk-focused one. While traditional vulnerability management asks, “What is vulnerable in our environment?”, exposure management asks a more critical question: “What actually puts our business at risk?”
This shift is about adding layers of context. Instead of just seeing a long list of CVEs, you start to see the bigger picture. Exposure management connects those vulnerabilities to your most important assets, maps potential attack paths, and considers active threats in the wild. It helps you understand not just that a weakness exists, but how an attacker could realistically exploit it to cause harm. This approach allows you to prioritize your efforts based on genuine business risk, making your security program more efficient and effective. It also changes how you talk about security with leadership, moving the conversation from technical jargon to tangible business impact. By focusing on exposures, you can clearly articulate which issues pose a direct threat to revenue, reputation, or operations, which is a language every executive understands.
Traditional vulnerability management programs often feel like a never-ending cycle of scanning and patching. Your team is handed a massive list of vulnerabilities, and the pressure is on to fix everything, all at once. This approach is noisy and overwhelming. It’s great at identifying weaknesses, but it doesn’t provide a clear path for what to fix first. Without proper context, your team might spend valuable time patching a low-risk vulnerability on a non-critical asset while a more dangerous threat lurks elsewhere. This constant fire drill leads to burnout and, worse, can leave critical exposures unaddressed simply because they were buried in the noise.
Exposure management cuts through the noise by adding crucial business context to each vulnerability. It moves beyond a simple count of CVEs and helps you understand the relationships between your assets, their weaknesses, and their business value. For example, a critical vulnerability on a public-facing server that holds sensitive customer data presents a much higher risk than the same vulnerability on an isolated development machine. By providing a unified view of cyber risks, exposure management platforms help you see these connections, transforming raw vulnerability data into business-focused insights that guide your remediation efforts.
Relying solely on CVSS scores to prioritize vulnerabilities is like driving using only your rearview mirror. It tells you how bad a vulnerability could be in theory, but it doesn’t tell you what’s happening on the road ahead. Exposure management prioritizes vulnerabilities based on real-world risk, incorporating up-to-the-minute threat intelligence. It focuses on what attackers are actually doing right now. Knowing that a specific vulnerability is being actively exploited in the wild is a far more powerful signal for action than a static severity score. This intelligence, often gathered by research teams like HiveForce Labs, allows you to focus on the threats that pose an immediate danger to your organization.
A solid exposure management program isn’t a single tool; it’s a cycle built on a few core activities. Think of it as a continuous loop that keeps your security posture strong. The process has four main parts that work together, giving you a complete picture of your risk and a clear path to reducing it.
You can’t protect what you don’t know you have. The first step is creating a complete, continuously updated inventory of every digital asset, from cloud services to user accounts. Because your digital footprint is always changing, this discovery can’t be a one-time event. By pulling data from various sources, you can maintain a live map of your environment. This is the foundation for understanding your total attack surface and gives you the visibility to spot weak points before an attacker does.
Once you know your assets, the next step is to find your real risks. This goes beyond simple vulnerability scanning to include misconfigurations and policy violations. To truly understand your exposure, you need to combine technical details with business context. This helps you prioritize threats by understanding which issues pose a genuine danger to critical operations versus those that are only theoretical. This validation step ensures your team focuses its energy on the problems that matter.
This is where you connect internal security data with what’s happening in the outside world. Integrating actionable threat intelligence means gathering information on emerging threats, attacker tactics, and actively exploited vulnerabilities. This context is crucial for making smart decisions. Instead of treating all high-severity vulnerabilities the same, you can focus on the ones attackers are using right now. This proactive approach, powered by research from teams like HiveForce Labs, helps you anticipate and defend against potential attacks.
Finding and prioritizing risks is only half the battle; you also need a solid plan to fix them. The final part of the cycle is establishing clear, efficient workflows for remediation and response. This involves assigning responsibility, setting realistic timelines, and using automation to speed up the process. It also includes validating that fixes have been implemented correctly and have actually reduced your exposure. A structured process ensures that identified risks are addressed quickly, closing security gaps before they are exploited.
If your security team feels like it’s constantly playing catch-up, you’re not alone. The sheer volume of vulnerabilities and security alerts is overwhelming, and traditional approaches just can’t keep pace. This is where exposure management comes in. It’s a strategic shift away from simply counting vulnerabilities and toward understanding your actual, quantifiable risk. It helps you answer the most important questions: What are our most critical assets, are they exposed, and what threats are most likely to target them?
Adopting an exposure management mindset helps your organization in a few critical ways. First, it gives you the visibility you need to get your arms around a modern, sprawling attack surface that extends far beyond your office walls. Second, it equips you to communicate risk in a language your leadership team understands, connecting technical issues to real business impact. Finally, it provides a clear, defensible framework for meeting and exceeding compliance requirements. It’s about working smarter, not just harder, to protect what matters most.
Let’s be honest, your organization’s digital footprint is bigger and more complex than ever. With assets spread across cloud environments, remote employee devices, and interconnected third-party services, the traditional idea of a network perimeter is gone. This expansion creates countless new avenues for attack and dangerous blind spots for security teams. You can’t protect what you can’t see, and trying to manually track every asset is an impossible task.
Exposure management is designed for this reality. It provides a continuous, unified view of your entire total attack surface, discovering and mapping all your assets, whether they are on-premise or in the cloud. By understanding how everything is connected, you can identify and prioritize the most likely attack paths before an adversary does. This proactive visibility is the foundation of a strong security posture.
One of the biggest challenges for security leaders is translating technical data into meaningful business insights. Your board doesn’t want a list of 10,000 critical CVEs; they want to know how security risks could impact revenue, operations, and reputation. They need to understand the return on investment for security initiatives in terms of risk reduction.
This is where exposure management shines. It moves the conversation away from abstract severity scores and toward concrete business context. By connecting vulnerabilities to the critical assets and business processes they affect, you can clearly articulate what’s at stake. This allows you to have more productive conversations about vulnerability and threat prioritization, justify resource allocation, and demonstrate how your team’s efforts are directly reducing the company’s overall business risk.
Meeting compliance standards like GDPR, HIPAA, or PCI DSS is a non-negotiable part of doing business. However, simply checking boxes during an annual audit isn’t enough to stay secure or satisfy regulators. Auditors and governing bodies increasingly want to see evidence of a mature, continuous, and proactive security program.
An exposure management program provides exactly that. It creates a defensible, data-driven process for how your organization identifies, prioritizes, and remediates risk. This continuous cycle of discovery, validation, and remediation demonstrates due diligence and shows that you have a robust system in place to manage your security posture. Using a comprehensive exposure management platform gives you a clear audit trail and the proof you need to confidently meet governance and compliance mandates.
Think of threat intelligence as the crucial context that turns a long list of vulnerabilities into a focused, actionable plan. Without it, you’re staring at thousands of potential weaknesses with little more than a technical severity score to guide you. This often leads to a constant, reactive scramble where everything feels like a top priority. Threat intelligence changes the game by showing you your attack surface through the eyes of an actual attacker. It answers the critical questions: Who is attacking organizations like mine? What methods are they using? And which of my specific weaknesses are they most likely to target right now?
This insight is what separates modern exposure management from traditional vulnerability scanning. Instead of just knowing you have vulnerabilities, you understand your actual, measurable risk. High-quality threat intelligence, like the research from HiveForce Labs, provides the data you need to connect specific threats to your unique assets. This allows your security team to stop chasing every potential issue and instead concentrate its time, budget, and energy on fixing the problems that pose a genuine and immediate danger to your business operations. It’s the key to moving from a defensive posture to a proactive and predictive security strategy.
A high CVSS score doesn’t always mean high risk to your specific organization. Threat intelligence helps you see beyond these static scores by providing dynamic, real-world data. It tells you which vulnerabilities are trending in underground forums, which exploits are being packaged into attack kits, and which weaknesses are being targeted by threat actors who focus on your industry. This approach transforms raw vulnerability counts into business-focused insights. By enriching your asset and vulnerability data with timely threat context, you can create a vulnerability and threat prioritization model that reflects true business risk, not just technical severity. This ensures your team is always working on the most important fixes first.
Knowing a vulnerability can be exploited is one thing; knowing it is being actively exploited in the wild is another. This is often the most critical piece of information for your security team. Threat intelligence feeds provide real-time alerts on vulnerabilities with known, active exploits. A medium-severity vulnerability that attackers are successfully using to breach networks is a much more urgent problem than a critical-severity flaw with no public exploit code. A continuous threat exposure management (CTEM) program uses this intelligence to help you proactively identify and mitigate these specific threats, drastically reducing the likelihood of a successful attack and allowing you to get ahead of the next big headline.
Effective defense isn’t just about patching vulnerabilities; it’s about understanding your adversary. Threat intelligence gives you deep insights into the tactics, techniques, and procedures (TTPs) used by various threat actor groups. By learning how specific groups operate, you can better anticipate their next move. For instance, if you know a particular ransomware group targeting your sector favors exploiting unpatched VPNs, you can prioritize securing those assets. Security teams can correlate data from multiple sources to identify patterns that signal an impending attack. This understanding of attacker behavior allows you to tailor your defensive controls and response plans to counter the most likely threats you face.
Think of Breach and Attack Simulation (BAS) as a continuous, automated sparring partner for your security team. Instead of waiting for a real attack to see how your defenses hold up, BAS tools safely mimic the tactics and techniques of actual adversaries. This isn’t just about scanning for vulnerabilities; it’s about actively testing whether your security controls, processes, and configurations can withstand a real-world attack scenario. It helps you answer the critical question: “Are our defenses working as well as we think they are?”
By running these controlled attack simulations, you can see exactly where your security gaps are. Maybe a firewall rule is misconfigured, an endpoint detection tool fails to flag a specific type of malware, or a phishing email simulation reveals a need for more employee training. BAS platforms provide the evidence you need to find and fix these weaknesses before a real attacker can exploit them. This proactive approach is a core component of modern exposure management, shifting your security posture from reactive to resilient. It’s a key part of adversarial exposure validation, ensuring your security investments are delivering real value by continuously testing them against the latest threats.
You’ve invested in firewalls, endpoint protection, and other security tools, but how do you know they’re actually doing their job? BAS helps you validate the effectiveness of your entire security stack. By launching simulations that replicate known threat behaviors, you can test if your controls are properly configured to detect, alert on, and block malicious activity. This process helps you move beyond assumptions and get clear, data-driven insights into your security performance.
These simulations can reveal critical gaps, such as a SIEM that isn’t generating the right alerts or an endpoint agent that can be easily bypassed. Finding these issues through a safe simulation allows you to fine-tune your tools and processes without the pressure of a live incident. It’s about making sure your technology works for you, identifying blind spots, and improving the accuracy of your threat detection capabilities.
Patching a vulnerability is one thing; confirming the fix actually closed the security gap is another. This is where BAS becomes an essential part of the remediation lifecycle. After your team has applied a patch or implemented a compensating control, you can use a BAS tool to run a specific attack simulation that targets the vulnerability you just addressed. This provides immediate validation that the remediation was successful and the attack path is no longer viable.
This creates a powerful feedback loop for your security program. You identify a risk, apply a fix, and then immediately test that fix. This approach not only confirms that your efforts were effective but also helps you demonstrate a measurable reduction in risk to leadership. It moves your team from a state of “we think we fixed it” to “we have proven it’s fixed,” which is a much more confident place to be.
Your IT environment is never static. New assets are added, software is updated, and configurations change daily. At the same time, attackers are constantly evolving their methods. A one-time security assessment or annual penetration test simply can’t keep up. BAS addresses this challenge by providing a way to continuously assess your security posture. By running simulations automatically and on a regular basis, you get a real-time view of your defenses.
This ongoing testing ensures that a change in your environment doesn’t accidentally create a new security hole. It helps you maintain a consistent state of readiness and adapt to the ever-changing threat landscape. This continuous validation is fundamental to a successful exposure management program, helping you proactively manage risk and ensure your security posture remains strong over time.
Shifting to an exposure management program is a smart move, but it’s not always a simple transition. Like any significant change in strategy, it comes with its own set of hurdles. Most organizations run into similar challenges related to visibility, technology, and team coordination. Thinking about these potential roadblocks ahead of time is the best way to create a clear path for your team and set your program up for success from day one.
You can’t protect what you don’t know you have. This is a foundational challenge for any security program. Many companies simply don’t have a full, clear picture of all their digital systems, often missing hidden or temporary resources. Your attack surface is likely much larger than you think, sprawling across cloud environments, forgotten subdomains, and IoT devices. Without a complete and continuously updated inventory, you’re operating with blind spots. A successful exposure management program starts with a commitment to Total Attack Surface Management, ensuring you have a comprehensive view of every asset that could potentially be exposed.
Your security team probably uses a dozen different tools for scanning, detection, and response. Each one generates valuable data, but it often lives in a silo. The real challenge is connecting the dots. Without a way to unify asset and risk data across these disparate tools, you’re left with a fragmented view of your security posture. You need a platform that can aggregate data from all your sources and provide rich context. This integrated approach, offered by platforms like Uni5 Xposure, is what allows you to move from looking at isolated vulnerabilities to understanding complex attack paths and true business risk.
Exposure management isn’t just a task for the security team; it’s a company-wide effort. A major hurdle is getting IT, DevOps, and security teams out of their silos and working together toward a common goal. This requires translating technical data into something everyone can understand. Exposure management helps by transforming raw counts of vulnerabilities into business-focused insights, showing which departments have reduced their risk or how security efforts are impacting the organization’s bottom line. When you can clearly communicate risk in business terms, you’re much more likely to get the buy-in and resources needed for effective and timely remediation.
The threat landscape changes by the minute. Relying on static threat information or generic CVSS scores just doesn’t cut it anymore. As one report notes, “Using old threat information won’t work against new attackers who constantly change their methods.” Your prioritization efforts are only as good as the intelligence behind them. To stay ahead, you need to focus on the vulnerabilities that are actively being exploited in the wild. This means integrating dynamic, real-world data into your program. Access to timely Threat Advisories ensures your team is always focused on fixing the exposures that pose an immediate and genuine threat to your organization.
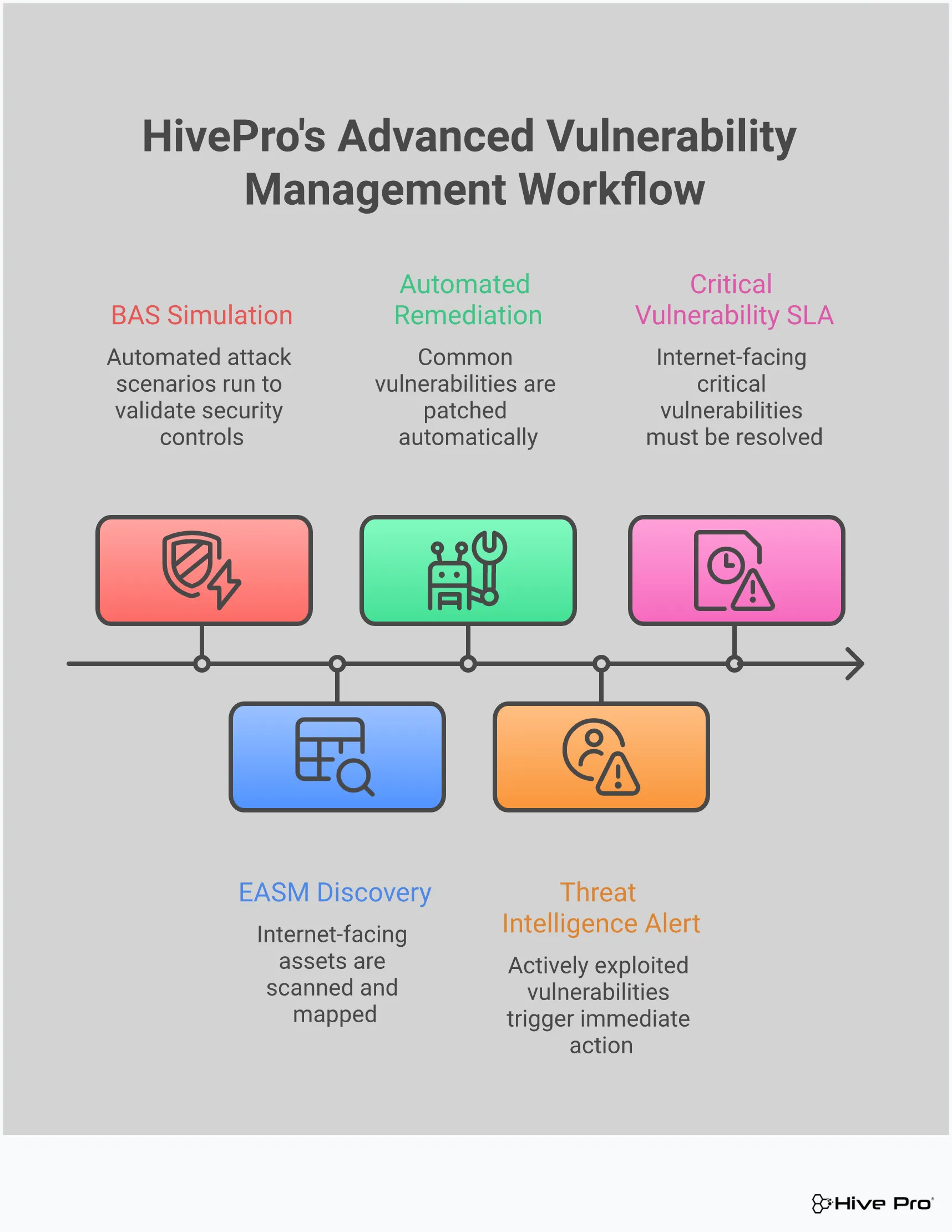
An effective exposure management program isn’t a one-time project; it’s a continuous cycle. Think of it as a strategic, repeatable process that helps you adapt to new threats and changes within your own environment. This approach moves you from simply reacting to problems to proactively reducing your risk before an attack can happen. A successful program is built on a foundation of four key processes that work together to give you a clear, actionable view of your security posture.
The cycle begins with comprehensive discovery, ensuring you see every asset you own. From there, you move to contextual assessment, where you figure out which vulnerabilities actually pose a threat. Next, you plan and execute a remediation strategy to fix the most critical issues. Finally, you continuously monitor and validate your defenses to make sure your fixes worked and that you’re prepared for the next threat. Each step feeds into the next, creating a loop that strengthens your security posture over time. This integrated approach breaks down silos and helps your teams work together more effectively, turning security from a series of disconnected tasks into a unified, strategic function. Let’s walk through each of these essential steps.
You can’t protect what you don’t know you have. The first step is to gain complete visibility by discovering and mapping every asset across your digital environment. This goes beyond just servers and laptops. It includes everything from cloud instances and applications to user accounts and code repositories. This process creates a comprehensive inventory of your total attack surface, giving you a clear picture of your organization’s digital footprint. A complete and continuously updated asset inventory is the bedrock of any strong security program, ensuring no part of your infrastructure is left unmonitored and vulnerable.
Once you have a complete map of your assets, the next step is to identify the weak spots. However, not all vulnerabilities carry the same level of risk. Instead of getting lost in a sea of CVEs with high severity scores, a modern approach focuses on context. Exposure management helps you prioritize threats by looking at how real attackers operate and which weaknesses truly matter. You’ll evaluate risks based on their potential business impact and the likelihood of exploitation, allowing your team to focus its energy on the vulnerabilities that pose a genuine threat to your organization.
Finding a critical exposure is important, but fixing it is what actually reduces risk. This is where you turn insight into action. A solid remediation strategy involves creating clear, efficient workflows to ensure vulnerabilities are addressed quickly. This means assigning ownership to the right teams, setting realistic deadlines for fixes, and tracking progress from start to finish. For many common issues, you can automate the remediation process, which frees up your security team to handle more complex threats. This focus on execution ensures that identified risks are not just logged but are actively resolved.
The security landscape is always changing, and so is your IT environment. That’s why the final process is to monitor and validate your defenses on an ongoing basis. This closes the loop and makes exposure management a true cycle. You need to continuously check for new threats and confirm that your security controls are working as intended. This is where adversarial exposure validation techniques, like breach and attack simulation, become invaluable. By safely simulating real-world attack scenarios, you can test your defenses, confirm that your remediation efforts were successful, and adapt your strategy to stay ahead of attackers.
A strong exposure management program isn’t just a set of processes; it’s powered by a stack of technologies designed to work together. These tools give you the visibility, context, and automation needed to move from a reactive to a proactive security posture. Think of it as building a security nervous system for your organization, where different components handle discovery, analysis, and response.
The goal is to create a seamless flow of information, from identifying an unknown asset on the internet to validating a fix for a critical vulnerability. The right tools eliminate manual work, correlate data from different sources, and ultimately help your team make faster, smarter decisions. The three core pillars of this technology stack are platforms for external discovery, a central solution for continuous management, and tools to automate your response. Each plays a distinct but interconnected role in helping you see and secure your entire attack surface.
You can’t protect what you don’t know you have. External Attack Surface Management (EASM) platforms are your eyes on the outside world, constantly scanning the internet to find assets connected to your organization. This includes forgotten subdomains, shadow IT in the cloud, and third-party services that could expose you to risk.
This proactive approach helps you discover your organization’s total attack surface from an attacker’s perspective. EASM platforms scan for publicly visible assets outside your company’s network, allowing you to identify vulnerabilities that could be exploited. By finding these exposed assets before an attacker does, you can close critical security gaps that might otherwise go unnoticed in traditional vulnerability scans.
If EASM tools are your scouts, then a Continuous Threat Exposure Management (CTEM) solution is your command center. CTEM is a framework for managing exposure on a large scale, moving beyond periodic reviews to a model of constant validation and improvement. It’s about creating an ongoing cycle of discovery, prioritization, validation, and remediation.
A CTEM program emphasizes continuous testing, monitoring, and improvement of your security defenses in real time. Platforms like Hive Pro’s Uni5 Xposure Platform integrate data from across your attack surface, enrich it with threat intelligence, and provide a unified view of your most critical risks. This ensures your security efforts are always aligned with the evolving threat landscape, allowing you to adapt quickly and confidently.
Discovering and prioritizing exposures is only half the battle; you also have to fix them. This is where security orchestration and automation tools become essential. These platforms connect your exposure management system to your broader IT environment to streamline and accelerate remediation.
By integrating with tools like Security Orchestration, Automation, and Response (SOAR) or IT Service Management (ITSM), you can automate simple fixes and speed up the entire process. For example, you can create automated workflows that patch a common vulnerability or create a ticket for a system administrator to investigate a more complex issue. This automation reduces the manual burden on your team, minimizes human error, and ensures that critical risks are addressed quickly and efficiently.
You can’t improve what you don’t measure, and that’s especially true in cybersecurity. A successful exposure management program isn’t just about finding vulnerabilities; it’s about demonstrating a real, sustained reduction in risk. To do that, you need to move beyond old-school metrics like the total number of patches applied. Instead, focus on tracking progress in a way that shows your team’s impact and communicates the value of your security efforts to the rest of the business. This means setting clear goals, monitoring your risk level over time, and getting faster at fixing what matters most.
To effectively measure your success, you need to establish the right Key Performance Indicators (KPIs). Instead of just counting the number of vulnerabilities you find, shift your focus to more strategic metrics that tell a story. Think about timeliness, risk exposure, and the potential financial impact of security issues. For example, you could track the percentage of critical assets covered by your scanning or the average time it takes to patch a high-risk vulnerability. These types of cybersecurity metrics provide a much clearer picture of your program’s effectiveness and help you communicate its value in business terms.
Exposure management is a continuous cycle, not a one-time project. Your ultimate goal is to steadily decrease your organization’s exposure to threats. Success is measured by how much that exposure drops over time. By collecting threat intelligence and correlating data, you can identify patterns and trends that show your defenses are improving. This isn’t just about closing individual tickets; it’s about seeing the bigger picture. Are you seeing fewer critical risks month over month? Are you better at prioritizing threats that pose a genuine danger? Tracking this downward trend in exposure is one of the most powerful ways to demonstrate the success of your program.
Knowing about a problem is only half the battle; fixing it is what counts. That’s why measuring your team’s remediation speed is so important. Key metrics like Mean Time to Detect (MTTD) and Mean Time to Resolution (MTTR) are essential here. They tell you how quickly your team can spot a threat and how long it takes to implement a fix. Tracking these numbers helps you understand the efficiency of your incident response and find any gaps in your controls or processes. As these times decrease, you have clear evidence that your vulnerability management activities are maturing and becoming more effective, all managed within a unified exposure management platform.
My team is already swamped with vulnerability alerts. How does exposure management actually help reduce the workload? That’s a common feeling, and it’s exactly the problem exposure management is designed to solve. Instead of adding more work, it helps you focus on the work that truly matters. It cuts through the noise by adding business context and real-world threat data to your alerts. This transforms a massive, overwhelming list of potential issues into a short, prioritized list of actual risks, allowing your team to stop chasing every low-risk vulnerability and concentrate its efforts on fixing the exposures that pose a genuine threat to your business.
Is this just another term for vulnerability management? Not at all. Think of exposure management as the next evolution of vulnerability management. Traditional vulnerability management is great at identifying weaknesses, asking “What is vulnerable?” Exposure management takes it a step further by asking, “What is at risk?” It connects those individual vulnerabilities to your critical assets, active threats, and potential attack paths. It’s a more strategic approach that moves beyond a simple technical checklist to give you a true understanding of your business risk.
How is using Breach and Attack Simulation (BAS) different from our yearly penetration test? A yearly penetration test is like an annual check-up; it gives you a valuable snapshot of your security at a single point in time. Breach and Attack Simulation, on the other hand, is like having a continuous fitness tracker for your security controls. It runs automated, safe attack scenarios all the time to constantly validate that your defenses are configured correctly and working as expected. This gives you immediate feedback and helps you find and fix gaps as they appear, rather than waiting a full year to discover them.
What’s the most important first step to building an exposure management program? The most critical first step is gaining complete visibility. You simply can’t protect what you don’t know you have. Before you can prioritize risks or validate controls, you need a comprehensive and continuously updated inventory of every asset across your entire digital footprint. This includes everything from your cloud environments and web applications to employee devices and user accounts. Establishing this complete view of your attack surface is the foundation everything else is built on.
How does threat intelligence change how we prioritize what to fix? Threat intelligence is the key to prioritizing with confidence. Relying only on a static severity score, like a CVSS score, tells you how bad a vulnerability could be in a perfect storm. Threat intelligence tells you what attackers are actually doing right now. Knowing that a medium-severity vulnerability is being actively exploited in the wild makes it a much higher priority than a critical-severity one with no known exploit. It allows you to focus on the clear and present dangers, not just the theoretical ones.