Comprehensive Threat Exposure Management Platform
To beat an attacker, you have to think like one. An adversary doesn’t care about your compliance reports or internal severity ratings. They care about one thing: finding an exploitable path to your critical assets. So why are we still prioritizing based on theoretical scores? A modern security strategy requires seeing your organization from the outside in. Threat intelligence gives you the attacker’s playbook, showing you which vulnerabilities they favor and the techniques they use. Breach and Attack Simulation (BAS) then lets you run those plays against your own defenses. This shift in perspective is the foundation of a strong CTEM cybersecurity program, transforming your defense from a passive checklist into an active, intelligent hunt for real-world risk.
For deeper context across Hive Pro’s CTEM resource cluster, see CTEM cybersecurity program, 5 stages of continuous threat exposure management, and CTEM platform.
Continuous Threat Exposure Management, or CTEM, is a strategic cybersecurity program designed to keep you one step ahead of attackers. Instead of treating security as a series of one-off tasks, CTEM is a continuous, five-stage cycle: scoping, discovery, prioritization, validation, and mobilization. Think of it as a proactive loop that helps you consistently see your organization from an attacker’s point of view. This approach allows you to find, prioritize, and fix the security gaps that pose a real threat to your business before they can be exploited. It’s about moving beyond just managing vulnerabilities and starting to manage your actual exposure to threats.
For too long, security teams have been stuck in a reactive cycle. You run a scan, get a massive list of vulnerabilities, and then spend your time putting out fires as they pop up. This constant state of defense leads to alert fatigue and burnout, and it doesn’t always make you safer. A successful CTEM program helps you break that cycle. It provides the framework to shift from reacting to incidents to proactively hunting for weaknesses. By focusing your team’s efforts on the exposures that matter most, you can reduce the noise and concentrate on fixes that have a real impact, transforming your security posture from defensive to strategic.
Traditional vulnerability management was a necessary first step, but it often misses the bigger picture. It can generate overwhelming lists of vulnerabilities, ranked by generic scores that lack business context. A “critical” vulnerability on a test server isn’t nearly as urgent as a “medium” one on your primary database. More importantly, these traditional methods often fail to show you how an attacker could connect different weaknesses to create an attack path to your critical assets. CTEM addresses this by focusing on exploitable pathways, aligning your security efforts with business risk. It helps you answer the most important question: not just “what are my vulnerabilities?” but “which ones can an attacker actually use against me?” This is where true vulnerability and threat prioritization comes into play.
If you’ve been in cybersecurity for a while, you know the drill: run a scan, get a massive report of vulnerabilities, and then try to figure out what to fix first. It’s a cycle that often feels more reactive than strategic. Continuous Threat Exposure Management (CTEM) isn’t just another industry buzzword; it’s a fundamental shift away from that old model. Instead of just managing vulnerabilities, a CTEM program focuses on managing exposure.
Traditional approaches often operate in silos. Your vulnerability management team runs their scans, your asset management team keeps their inventory, and your threat intel team watches for new exploits. CTEM brings these functions together. It creates a unified, continuous loop of identifying your attack surface, discovering exposures, prioritizing them based on real-world threats, and validating your defenses. It’s about moving from a checklist mentality to a proactive security posture that’s aligned with your actual business risk. This approach helps you answer the most important question: what are the most likely ways an attacker could breach our defenses and how do we stop them?
Traditional vulnerability management often relies on point-in-time scans, maybe running them quarterly or monthly. The problem is that your attack surface is anything but static. New assets pop up, code gets deployed, and configurations change daily. A scan from last Tuesday is already outdated. These periodic checks leave dangerous blind spots that attackers are more than happy to exploit. They aren’t waiting for your next scheduled scan to make their move.
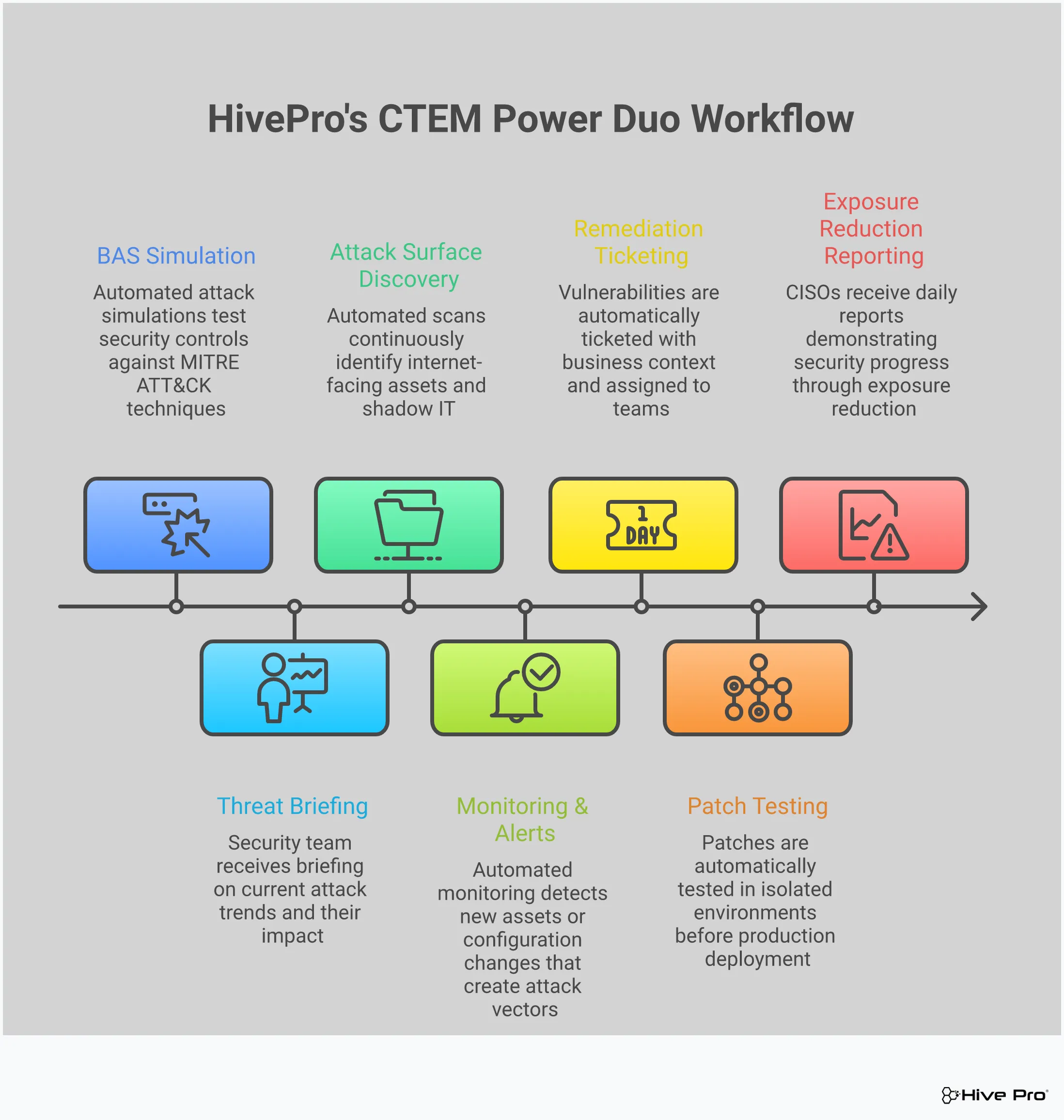
CTEM replaces this outdated snapshot approach with continuous monitoring. It’s about having a live, always-on view of your entire environment. By continuously scanning your total attack surface, you can spot new assets and exposures the moment they appear. This allows you to identify, prioritize, and remediate security gaps in near real-time, closing windows of opportunity for attackers. It’s a proactive cycle that keeps pace with your dynamic environment, ensuring you’re always working with the most current information.
The traditional security model is often a waiting game. You set up your defenses, monitor for alerts, and react when something bad happens. This puts your team in a constant state of defense, waiting for the next incident to pull them into firefighting mode. It’s an exhausting and inefficient way to operate, and it means the attacker always makes the first move.
A CTEM program flips the script by encouraging you to hunt for threats proactively. Instead of asking, “Are we compromised?” you start asking, “How could we be compromised?” This mindset shift turns your security team into hunters who actively search for exploitable attack paths and weak points. By using up-to-date threat advisories and intelligence, you can simulate potential attacks and find weaknesses before a real adversary does. This approach helps you build a stronger, more resilient security posture over time, creating a clear plan that everyone from leadership to the technical teams can get behind.
For years, prioritization has been driven by CVSS scores. While helpful, a high score doesn’t always translate to high risk for your specific organization. This often leads to security teams chasing down thousands of “critical” vulnerabilities, many of which pose little actual threat. The result is a massive, unmanageable backlog and a team that’s burning out trying to fix everything at once.
CTEM changes the game by focusing on real-world risk. It connects insights from your attack surface, the flaws in your assets, and active threat intelligence to create a unified view of your true business risk. An effective vulnerability and threat prioritization strategy considers which vulnerabilities are actively being exploited in the wild and which ones exist on attack paths leading to your most critical assets. This allows your team to work smarter, not harder, by focusing their limited time and resources on the exposures that truly matter.
A Continuous Threat Exposure Management (CTEM) program provides a structured, five-stage framework to help your security team get ahead of threats. Instead of constantly reacting to incidents, you can proactively identify and fix the security gaps that matter most to your business. Think of it as a continuous cycle that aligns your security efforts with your most critical functions, ensuring you’re always protecting what’s most valuable. This approach moves beyond periodic scans and simple checklists, creating a dynamic process that adapts to your ever-changing attack surface. As new assets come online and threats evolve, your security strategy evolves with them.
By following these five stages, you can systematically reduce your exposure, streamline remediation, and make more informed security decisions based on real-world risk. A unified platform like Uni5 Xposure can bring all five stages together, giving you a single, clear view of your security posture from discovery to remediation. This structured approach not only makes your security operations more efficient but also helps you communicate risk more effectively to leadership. When you can show exactly what you’re protecting, what threats you’ve validated, and how you’ve fixed the gaps, you can demonstrate measurable improvements over time and build a stronger case for your security investments.
Before you can protect your assets, you need to know what they are and which ones are most important. The scoping stage is all about defining the boundaries of your CTEM program. This means identifying your critical business systems, applications, cloud accounts, and user groups that are essential to your operations. It’s about asking, “What can we not afford to have compromised?” A well-defined scope ensures your team focuses its energy on the parts of your business that carry the most risk. This isn’t just a technical inventory; it’s a business-centric view of your total attack surface management that guides the rest of your security strategy and prevents your team from getting lost in a sea of low-impact alerts.
Once you know what you need to protect, the discovery stage is where you continuously search for weaknesses across that defined scope. This goes far beyond traditional vulnerability scanning. It involves actively identifying a wide range of exposures, including unpatched software, cloud misconfigurations, weak credentials, and overly permissive user access. The goal is to maintain a real-time, comprehensive inventory of every potential entry point an attacker could use. Because your environment is constantly changing with new assets and users, discovery can’t be a one-time event. It must be a continuous process that keeps pace with your organization, ensuring you always have an up-to-date view of your potential security gaps.
Discovery will likely uncover thousands of potential vulnerabilities, and you can’t fix them all at once. The prioritization stage is where you cut through the noise. Instead of relying solely on technical severity scores like CVSS, a CTEM program enriches this data with real-world context. This includes threat intelligence on which vulnerabilities are being actively exploited in the wild, the criticality of the affected asset to your business, and the effectiveness of existing security controls. This approach to vulnerability and threat prioritization helps your team focus on the handful of issues that pose a genuine, immediate threat to your organization, allowing you to allocate your resources for maximum impact.
Just because a vulnerability exists doesn’t automatically mean it’s exploitable in your environment. The validation stage is about confirming which prioritized threats are real and actionable. This is where you test your defenses to see if an attacker could actually leverage a specific weakness to breach your systems. Techniques like Breach and Attack Simulation (BAS) are used to safely simulate attack paths and test the effectiveness of your security controls. This process of adversarial exposure validation provides concrete proof of risk, helping you eliminate false positives and build a strong business case for remediation. It answers the critical question: “Are we truly vulnerable, or do we have compensating controls in place?”
The final stage, mobilization, is all about taking action. Once a vulnerability has been discovered, prioritized, and validated, it’s time to fix it. This stage involves creating clear, actionable remediation plans and coordinating efforts across different teams, including security, IT, and DevOps. A successful mobilization phase relies on streamlined workflows and clear communication to ensure everyone understands their role and the urgency of the task. This isn’t just about patching; it could also involve changing configurations or implementing new security controls. This stage closes the loop, and the entire cycle begins again, creating a continuous process of improvement that strengthens your security posture over time.
A CTEM program is powerful on its own, but it becomes truly strategic when you fuel it with threat intelligence. Think of threat intelligence as the lens that brings your security landscape into sharp focus. Instead of looking at a massive list of potential exposures, you can see which ones are being actively targeted by attackers right now. This intelligence transforms your CTEM strategy from a simple inventory of weaknesses into a proactive defense plan that anticipates real-world threats. It’s the difference between knowing you have unlocked doors and knowing which one an intruder is about to use. By integrating real-time data on attacker behaviors, you can prioritize with precision and allocate your resources where they will have the greatest impact, moving from a reactive posture to one of confident action.
A vulnerability score tells you how severe an issue could be, but it doesn’t tell the whole story. Threat intelligence adds the missing real-world context. It answers critical questions: Is this vulnerability being used by threat actors targeting my industry? Is it part of a new ransomware campaign? This information, often curated by research teams like HiveForce Labs, turns abstract data into a clear narrative about your risk. When you can explain that a medium-severity vulnerability is a favorite tool for a specific threat group, you create a security plan that everyone, from leadership to your technical teams, can understand and support.
Your security team faces thousands of alerts, making it impossible to fix everything at once. Threat intelligence helps you cut through the noise by pinpointing which vulnerabilities are not just theoretically exploitable, but are actively being used in attacks. This is a game-changer for prioritization. Instead of just chasing high CVSS scores, you can focus on the exposures that present a clear and present danger. This proactive stance lets you concentrate on the attack paths that adversaries are actually using, aligning your security efforts with tangible business risk and protecting your most critical assets first.
When you combine insights about your attack surface with intelligence on active threats, you get a clear view of your true business risk. This allows your team to work smarter, not harder. Threat intelligence directs your remediation efforts to the most critical issues, ensuring your team’s time is spent on fixes with the greatest security impact. An effective vulnerability and threat prioritization process means you’re not just patching vulnerabilities; you’re systematically dismantling the most likely routes an attacker would take to compromise your organization.
After you’ve identified and prioritized your exposures, it’s time for a reality check. This is where the validation stage of CTEM comes in, and Breach and Attack Simulation (BAS) is its star player. Think of it this way: you can have all the best security tools on paper, but how do you know they’re configured correctly and will actually stop an attack? BAS answers that question by safely simulating real-world attack scenarios to see how your defenses hold up.
Instead of waiting for a real incident to find the gaps, BAS lets you proactively test your security controls in a controlled environment. It’s the difference between hoping your firewall will block a specific threat and knowing it will. By running these simulations, you move beyond theoretical security and get tangible proof of your resilience. This validation is what transforms exposure management from a simple reporting exercise into a program that actively improves your security posture. Hive Pro’s approach to adversarial exposure validation integrates this testing directly into the CTEM lifecycle, ensuring your defenses are always battle-tested.
Your security stack is made up of many layers, from firewalls and email gateways to endpoint detection and response (EDR) tools. Each one is supposed to do a specific job, but misconfigurations or gaps between tools can leave you exposed. BAS acts like a dedicated testing team, running automated attacks that mimic the techniques used by actual adversaries.
These simulations can test whether your systems will detect and block known malware, if your network segmentation is preventing lateral movement, or if your EDR can stop a ransomware attack in its tracks. The goal isn’t to break things; it’s to find weaknesses before a real attacker does. This gives you clear, actionable evidence of which controls are working as expected and which ones need attention, allowing you to fine-tune your defenses based on performance, not assumptions.
Patching a vulnerability or reconfiguring a security tool is only half the battle. The critical next step is to confirm that the fix actually worked and closed the exposure. This is where many teams fall short, often assuming a “patched” status means the risk is gone. A robust exposure management program requires continuous validation to ensure remediation efforts are successful.
This is another key role for BAS. After your team has implemented a fix, you can re-run the relevant attack simulation to verify that the defensive gap is truly closed. This creates a crucial feedback loop, confirming that your team’s hard work has paid off and tangibly reduced risk. Without this step, you could be operating with a false sense of security, believing you’ve addressed a problem that an attacker could still easily exploit.
Your IT environment is constantly changing. New assets come online, software is updated, and configurations are tweaked. A security assessment from last quarter might be completely irrelevant today. Because CTEM is a continuous process, your validation efforts need to be continuous, too. BAS provides this ongoing insight by allowing you to run simulations regularly.
By integrating BAS into your routine security operations, you get a real-time view of your security posture as it evolves. This allows you to quickly spot new weaknesses that appear due to environmental changes or adapt to new threats as they emerge. This continuous validation, a core component of a unified CTEM platform, ensures that your security program keeps pace with both your organization and the threat landscape, helping you maintain a consistently strong defensive posture.
Adopting a CTEM program is about fundamentally changing how your security team operates for the better. By shifting from a reactive, checklist-driven approach to a proactive, risk-informed strategy, you can achieve tangible results that strengthen your security posture and support your business goals. The core benefits boil down to speed, efficiency, and clarity, transforming how you manage and reduce threat exposure across your organization.
A CTEM program creates a clear, consistent security plan that everyone from leadership to your technical teams can get behind. Instead of different departments working from separate data sets, CTEM unifies your view of risk. This shared understanding eliminates confusion and streamlines communication, allowing your teams to move directly from identification to remediation. When everyone agrees on what needs to be fixed and why, you can significantly shorten the time it takes to close critical security gaps and continuously strengthen your defenses against emerging threats.
Your security team is busy. A CTEM program helps them make the most of their time by focusing their efforts where they’ll have the greatest impact. It connects the dots between your attack surface, known flaws, and active threat intelligence to create a unified view of your true business risk. This means your team can stop chasing down every single low-risk alert and instead concentrate on the vulnerabilities that attackers are actually exploiting. This targeted approach to vulnerability and threat prioritization reduces alert fatigue and ensures your most valuable resources are dedicated to mitigating the most significant threats.
CTEM provides a constant, real-time view of your organization’s security health, replacing periodic snapshots with a continuous feed of actionable information. This clarity empowers security leaders to make smarter, data-driven decisions that align with business objectives. With a comprehensive understanding of your exposure, you can justify security investments, communicate risk effectively to the board, and report on your program’s progress with confidence. A platform that offers a unified view of cyber risks helps you move from guessing to knowing, ensuring your security strategy is always on the right track.
Making the switch to a Continuous Threat Exposure Management (CTEM) program can feel like a huge undertaking. It’s a different way of thinking about security, moving from periodic check-ins to a constant, proactive cycle. It’s natural to have questions and concerns about what this change means for your team, your budget, and your existing security tools. Many teams worry about the heavy lifting involved, the potential for disruption, and whether they have the resources to pull it off.
The good news is that these challenges are not roadblocks; they’re just hurdles you can clear with the right approach. Adopting CTEM doesn’t mean you have to tear down everything you’ve built. Instead, it’s about enhancing your current security program to be more strategic and effective. A platform like Uni5 Xposure is designed to integrate with your environment, not overhaul it. By understanding the common misconceptions, planning for resource allocation, and creating a solid game plan, you can make a smooth transition. Let’s walk through some of the most common concerns and how you can address them head-on.
One of the biggest myths holding teams back is the idea that you have to discard your entire security program to start with CTEM. That’s simply not true. CTEM is designed to build upon and refine what you already do, making your efforts more focused and impactful. It’s also not just another “security thing” for the IT team to handle alone. True exposure management is a shared responsibility that involves everyone, because a security gap in one department can affect the entire organization. Finally, CTEM isn’t about adding more work; it’s about helping your team work smarter by directing their attention to the vulnerabilities that pose a genuine threat.
The word “continuous” can sound intimidating, often sparking concerns about needing more staff and more tools. While CTEM does require ongoing monitoring, it doesn’t have to be a resource drain. The key is to start with a manageable scope. You don’t need to cover your entire attack surface on day one. Begin with a critical business unit or a specific set of assets to demonstrate value and build momentum. A modern CTEM platform should also integrate smoothly with your existing security stack, pulling data from your current tools to create a unified view of risk. This integration prevents you from adding complexity and instead streamlines your operations, making continuous management an achievable goal.
A successful CTEM implementation starts with clear communication and a strategic plan. Frame the program as a business enabler that aligns security operations with your company’s goals, not just another technical requirement. This helps secure buy-in from leadership and other departments. Your plan should focus on moving your team from a reactive to a proactive posture, which reduces alert fatigue and allows your team to concentrate on fixing the exposures that matter most. Start small, celebrate early wins, and gradually expand the program. This methodical approach builds confidence and demonstrates the value of CTEM across the organization, creating a stronger, more resilient security culture.
Transitioning to a Continuous Threat Exposure Management program is a strategic move that pays off in stronger security and a more efficient team. But getting started requires a solid plan. It involves picking the right tools, getting your team aligned, and knowing how you’ll measure success along the way. Here’s how to approach each of these steps to build a CTEM program that lasts.
Choosing the right platform is the first step in building your CTEM program. Look for a solution that offers more than just scanning. A strong CTEM platform provides continuous validation to confirm if your security controls are actually working against real-world attack scenarios. It should also automate the heavy lifting, like tracking threats and guiding remediation, to free up your team’s time. The goal is to get a single, unified view of your cyber risks. A platform like Uni5 Xposure brings together attack surface scanning, vulnerability prioritization, and remediation workflows in one place, saving you from juggling multiple tools and spreadsheets.
A new program is only as good as the team that runs it. To get everyone on board with CTEM, focus on how it makes their jobs easier. CTEM helps your team work smarter, not harder, by connecting insights from your attack surface, vulnerabilities, and threat intelligence into one clear picture of business risk. This approach works well even in decentralized organizations because you can apply the same focused security lens to different business units. Start by demonstrating how a unified platform breaks down silos between security and IT teams, creating a shared understanding of what needs to be fixed first and why.
To show that your CTEM program is working, you need to track the right metrics. The biggest win is the shift from a reactive to a proactive security stance. Instead of just counting patched vulnerabilities, measure the reduction in your overall threat exposure. Key performance indicators (KPIs) could include a lower mean time to remediate (MTTR) for critical risks, a decrease in exploitable vulnerabilities, and improved security posture scores over time. A successful program creates a clear security plan that everyone from your technical teams to the C-suite can understand and support, proving its value and justifying continued investment.
Isn’t CTEM just another buzzword for vulnerability management? That’s a fair question, but CTEM is a genuine shift in strategy. Traditional vulnerability management often gives you a massive, static list of problems ranked by technical scores, leaving your team to figure out what actually matters. CTEM is a continuous cycle that focuses on your actual exposure. It connects your vulnerabilities to real-world threat intelligence and your business context, helping you see the complete attack paths an adversary could use. It’s less about checking off a list and more about proactively managing your true business risk.
My team is already swamped. How can we adopt CTEM without getting overwhelmed? This is a common concern, and the key is to remember that CTEM is about working smarter, not harder. It actually helps reduce the noise. Instead of trying to fix thousands of “critical” vulnerabilities, a CTEM program uses threat intelligence and business context to pinpoint the handful of exposures that pose a real, immediate threat. You don’t have to cover your entire attack surface on day one. Start with a well-defined scope, like your most critical business applications, and show value there first. This focus makes the workload manageable and directs your team’s energy where it will have the most impact.
What’s the difference between validating a threat and just patching it? Patching a vulnerability is the fix, but validation is the proof that the fix worked and that your defenses are configured correctly. Just because a patch is applied doesn’t mean an attacker can’t find another way in. The validation stage, often using Breach and Attack Simulation (BAS), safely tests your security controls against real-world attack techniques. It answers the question, “Can an attacker actually exploit this weakness in my environment?” This step confirms your security posture is truly stronger and helps you avoid a false sense of security.
How does threat intelligence actually change our day-to-day work in a CTEM program? Threat intelligence transforms your team’s daily to-do list from a theoretical exercise into a targeted action plan. Without it, you’re often prioritizing based on generic severity scores. With it, you can see which specific vulnerabilities are being actively exploited by attackers in the wild, especially those targeting your industry. This allows your team to immediately focus on the clear and present dangers, rather than spending weeks working through a backlog of issues that pose little actual risk. It turns down the volume on alerts and turns up the focus on what matters now.
What’s the most important first step to building a CTEM program? The most critical first step is scoping. Before you start scanning and discovering, you need to define what you are protecting and why it’s important to the business. This means identifying your most critical assets, data, and systems. By starting with a clear, business-focused scope, you ensure that your entire security program is aligned with protecting what is most valuable to your organization. This foundational step prevents your team from getting lost in low-priority alerts and guides every other stage of the CTEM cycle.