Comprehensive Threat Exposure Management Platform
To effectively defend your organization, you need to think like an attacker. Attackers don’t care about a vulnerability’s CVSS score; they care about whether they can exploit it to reach a valuable target. Traditional security often misses this crucial context, leaving you to guess which of the thousands of alerts are part of a viable attack chain. This is the problem that Continuous Threat Exposure Management was designed to solve. If you’re asking what is CTEM, think of it as a framework for adopting an adversarial mindset. It’s a continuous cycle of discovering, prioritizing, and validating your exposures to confirm which ones are truly dangerous, allowing you to disrupt attack paths before they can be exploited.
Hive Pro also tracks Gartner’s shift from threat to exposure management so security teams can connect CTEM fundamentals to the analyst guidance shaping modern exposure programs.
For deeper context across Hive Pro’s CTEM resource cluster, see 5 CTEM stages, best CTEM tools, CTEM vendors, and threat intelligence for exposure management.
If you feel like you’re constantly playing catch-up with security threats, you’re not alone. Traditional approaches often leave security teams reacting to endless vulnerability alerts without a clear sense of what to fix first. Continuous Threat Exposure Management, or CTEM, is a strategic framework designed to change that. It’s a proactive, cyclical approach that helps you consistently see and manage your organization’s security risks from an attacker’s perspective.
Instead of relying on periodic scans that quickly become outdated, a CTEM program provides an ongoing process for managing your entire attack surface. It’s about creating a sustainable security rhythm that aligns with your business goals. This framework consists of five core stages: scoping, discovery, prioritization, validation, and mobilization. By following these stages, you can move from a reactive state of fixing problems to a proactive posture of preventing them, ensuring your team’s efforts are always focused on the threats that pose a genuine risk to your organization.
At its heart, CTEM is about answering one critical question: “What vulnerabilities in my environment are most likely to be exploited by an attacker right now?” It’s a structured framework for continuously identifying, prioritizing, validating, and fixing the security gaps that put your business at risk. The goal is to cut through the noise of countless low-risk alerts and focus your resources on what truly matters. A solid Threat Exposure Management Platform gives you a unified view of these risks, helping you make informed decisions based on real-world threat intelligence rather than just technical severity scores. This continuous loop ensures your security posture improves over time.
Traditional security often involves running vulnerability scans, getting a massive report, and then trying to figure out where to start. This approach is reactive and often disconnected from how attackers actually operate. CTEM flips the script by focusing on real, exploitable attack paths across your entire digital footprint, from on-premise systems to cloud environments. It shifts security from a compliance-driven chore to a proactive, strategic function. Instead of just finding weaknesses, CTEM programs validate them to confirm they are exploitable. This focus on vulnerability and threat prioritization helps you understand your true exposure and guides your team to fix the most critical issues first.
A successful Continuous Threat Exposure Management (CTEM) program isn’t a random collection of security tasks. It’s a structured, cyclical process that brings order to the chaos of managing cyber risk. Think of it as a repeatable framework that helps your team move from constantly fighting fires to proactively reducing your attack surface. By breaking the process down into five distinct stages, you can create a clear, consistent, and effective approach to security that aligns with your business goals. Each stage builds on the last, creating a continuous loop of discovery, prioritization, validation, and remediation that strengthens your security posture over time.
Before you can protect your assets, you need to know what you’re protecting and why it matters. The scoping stage is all about defining the boundaries of your CTEM program and aligning it with what’s most important to your business. This means going beyond a simple asset inventory. You’ll decide which business units, applications, cloud accounts, and user groups are in scope. The goal is to focus your resources where they can have the biggest impact. By clearly defining your total attack surface management strategy from the start, you ensure that your security efforts are directly tied to protecting critical operations and sensitive data, rather than trying to boil the ocean.
Once you know your scope, it’s time to find the weaknesses. The discovery stage involves a continuous and comprehensive search for any potential exposure an attacker could exploit. This is much broader than a traditional vulnerability scan. You’re looking for everything: unpatched software, cloud misconfigurations, weak credentials, exposed APIs, and other security gaps across your entire environment. The key here is “continuous.” Threats and environments change constantly, so discovery can’t be a once-a-quarter activity. It needs to be an ongoing process that provides a real-time, unified view of all your potential security risks in one place.
Most security teams are drowning in a sea of “critical” alerts. The prioritization stage helps you find the real threats in all that noise. Instead of relying solely on generic CVSS scores, a CTEM approach adds crucial context. It asks questions like: Is this vulnerability being actively exploited in the wild? Does it affect a business-critical system? Is there a known exploit kit for it? By combining vulnerability data with real-world threat intelligence, you can focus on the handful of exposures that pose a genuine, immediate risk to your organization. This approach to vulnerability and threat prioritization allows your team to direct its energy toward fixing what truly matters first.
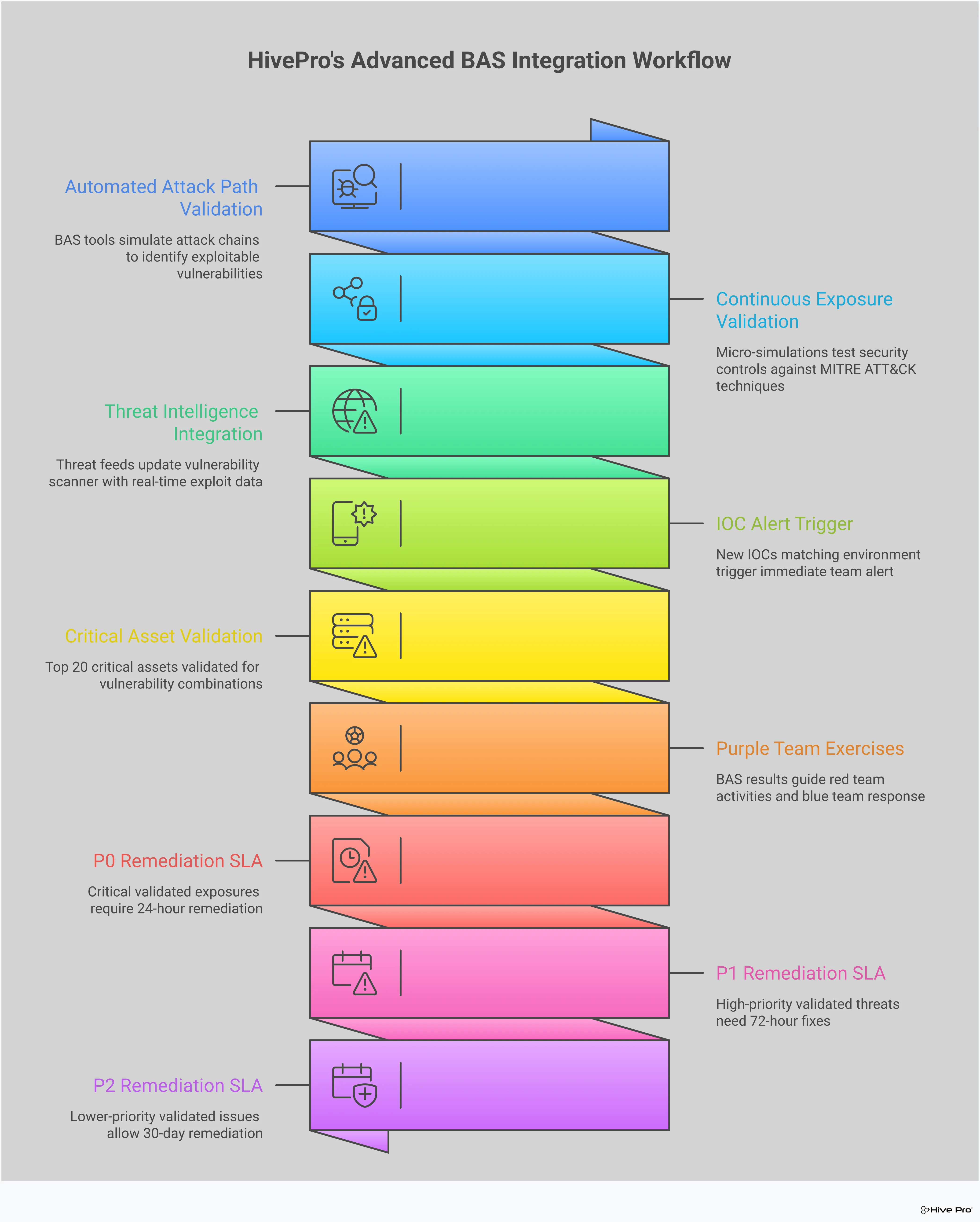
Just because a vulnerability exists doesn’t automatically mean it’s exploitable in your specific environment. The validation stage is where you test your exposures to see if they represent a real-world danger. Using techniques like Breach and Attack Simulation (BAS), you can safely simulate attacker tactics to see if your security controls would hold up. This process of adversarial exposure validation helps you confirm which vulnerabilities are truly dangerous and which are mitigated by other defenses. It provides concrete proof of risk, which is incredibly useful for getting buy-in from other teams and justifying the need for remediation. It’s about moving from theoretical risk to confirmed exposure.
Finding and validating threats is only half the battle; you also have to fix them. The mobilization stage is all about streamlining your remediation efforts to close exposures quickly and efficiently. This means breaking down the silos between security, IT, and DevOps teams. A strong CTEM program integrates with ticketing systems and provides clear, actionable guidance on how to fix problems. It makes it easier for teams to collaborate, get approvals, and track remediation progress from start to finish. The goal is to create a smooth, fast workflow that ensures the critical insights you’ve gained lead to a tangible reduction in your organization’s overall risk.
If you’ve been working in cybersecurity for a while, you’re familiar with the rhythm of traditional vulnerability management: scan, patch, repeat. It’s a model that has served us for years, but it’s starting to show its age. As our digital footprints expand with cloud services, IoT devices, and remote work, the old way of doing things just can’t keep up. The sheer volume of alerts is overwhelming, and it’s nearly impossible to know which ones pose a genuine threat.
This is where Continuous Threat Exposure Management (CTEM) changes the game. While it shares the goal of reducing risk, its methodology is fundamentally different. CTEM isn’t just an update to vulnerability management; it’s a complete strategic shift. It moves beyond periodic scans and narrow definitions of risk to provide a more holistic, proactive, and continuous way to secure your organization. Let’s break down the key distinctions.
Traditional vulnerability management often operates on a fixed schedule, running scans monthly, quarterly, or maybe annually. The problem is that your attack surface doesn’t wait for a scheduled scan to change. New assets pop up, configurations drift, and fresh threats emerge daily. A snapshot from last month is already out of date.
CTEM, by contrast, is a continuous process, not a one-time check. It constantly monitors your environment, adapting as new systems are added or threats change. This gives you a live, real-time view of your entire attack surface, so you always know what you need to protect. Instead of working with old data, your team can make decisions based on what’s happening right now.
Another key difference is what each approach looks for. Traditional programs are hyper-focused on CVEs, or common vulnerabilities and exposures, found in software. While important, CVEs are only one piece of the puzzle. Attackers are creative and will exploit any weakness they can find, not just a known software flaw.
CTEM broadens the definition of risk to include any kind of exposure that could put your organization in jeopardy. This includes everything from misconfigured cloud services and leaked credentials to weak security controls and even phishing risks. It provides a unified view of all potential attack paths, giving you a much more complete picture of your actual security posture. This holistic approach helps you see connections that a siloed, CVE-focused program would miss.
The constant cycle of patching can feel like a never-ending game of whack-a-mole. Traditional vulnerability management often leaves security teams in a reactive state, scrambling to fix every issue that pops up. This leads to burnout and a situation where the most critical risks can get lost in the noise.
CTEM shifts cybersecurity from a reactive approach to a proactive one. Instead of trying to fix every small issue, you can prioritize exposures based on which ones attackers are most likely to use. By understanding the attacker’s perspective and validating which exposures are truly exploitable, you can focus your resources on fixing the problems that matter most. This allows you to get ahead of potential attacks and strengthen your defenses before they are ever tested.
If your security program feels like a constant game of catch-up, you’re not alone. Traditional approaches struggle to keep pace with today’s dynamic IT environments and sophisticated threats. This is where a Continuous Threat Exposure Management (CTEM) program becomes essential. It’s not just another tool; it’s a strategic shift that helps you get ahead of attackers by continuously assessing and improving your security posture. By moving from periodic scans to a constant cycle of discovery and validation, you can finally focus your team’s efforts on the risks that truly matter to your business.
Your digital environment is always in motion. New cloud services are spun up, user accounts are created, and applications are updated daily. These constant changes create a shifting attack surface where new exposures can appear at any moment. Occasional vulnerability scans simply can’t keep up, leaving you with blind spots an attacker could easily exploit. A CTEM program provides a continuous, real-time view of your risks. Since most cyberattacks leverage known vulnerabilities, CTEM helps you cut through the noise, understand the latest threat advisories, and fix the problems that pose a genuine danger before they can be used against you.
As your organization grows, so does its attack surface. More devices, cloud assets, and applications mean more potential entry points for attackers. The challenge isn’t just finding individual vulnerabilities; it’s understanding how they connect to create viable attack paths. CTEM helps you map these connections, showing you exactly how an attacker could chain together seemingly low-risk exposures to reach your critical assets. This proactive approach helps you manage your total attack surface by understanding the why and how behind your security gaps, allowing you to fix the root causes instead of just patching individual symptoms.
Security teams are often stretched thin, buried under a mountain of alerts and vulnerabilities. It’s impossible to fix everything, so how do you decide what to tackle first? CTEM answers that question by providing context. It helps you prioritize remediation based on which exposures are most likely to be exploited and would cause the most damage. This focus allows your team to stop wasting time on low-impact issues and concentrate on what’s most critical. By shifting from a reactive to a proactive stance, the Uni5 Xposure platform helps you use your resources more effectively, reduce overall risk, and clearly communicate your security posture to leadership.
Adopting a CTEM program is more than just a strategic shift; it delivers practical, measurable results that can transform your security operations. Moving beyond traditional, reactive methods allows your team to become more efficient, your defenses to become more resilient, and your organization to become more secure. Let’s look at the tangible benefits you can expect when you put CTEM into practice.
One of the biggest challenges in security is the sheer volume of alerts and vulnerabilities. A CTEM framework helps you cut through that noise. Instead of trying to patch every single potential weakness, you can concentrate your efforts on the exposures that attackers are most likely to exploit. This risk-based approach means your team spends its time on fixes that genuinely reduce your organization’s risk profile. By getting a clear, unified view of your most critical threats, you can make smarter decisions and move from a constant state of reaction to a proactive security stance. This is where effective vulnerability and threat prioritization becomes a game-changer.
Security isn’t a one-time fix; it’s an ongoing process of improvement. CTEM embeds this idea into your daily operations. By continuously scanning your environment and validating your defenses, you iteratively strengthen your security posture against emerging threats. Think of it like a fitness routine for your security program. Regularly testing your controls through methods like adversarial exposure validation prepares your team for real-world incidents. When a genuine threat appears, your team can respond faster and more effectively because they’ve already practiced their defense plans, turning potential chaos into a coordinated and confident response.
When your security team is focused on the most significant threats, you naturally optimize your resources. You stop wasting valuable time and budget on low-priority issues and direct your investments where they will have the greatest impact. This improved efficiency also helps prevent costly security breaches and the associated reputational damage. Furthermore, a well-structured CTEM program simplifies compliance and audits. You can clearly demonstrate to regulators and stakeholders that you have a continuous, documented process for identifying, prioritizing, and remediating exposures across your entire attack surface, making it easier to meet industry standards and regulations.
A CTEM program is powerful, but it runs on data. To get the most out of it, you need to feed it high-quality, relevant threat intelligence. This is what transforms your program from a simple data collection exercise into a smart, proactive defense system. Think of threat intelligence as the brain behind the brawn of your security tools. It provides the crucial context needed to understand which threats are just noise and which ones pose a genuine, immediate risk to your organization. Without it, you’re operating with a blind spot, potentially wasting time on low-risk issues while a major threat goes unnoticed.
By integrating real-world threat data, you can move beyond theoretical risks and focus on what attackers are actually doing in the wild. This intelligence sharpens every stage of the CTEM cycle, from discovery to mobilization. It helps you see your environment through an attacker’s eyes, validate your defenses against real-world tactics, and direct your limited resources to the fixes that will have the greatest impact on your security posture. It’s the key to making your security efforts more efficient, effective, and forward-thinking, turning reactive guessing into confident, data-driven action.
Not all vulnerabilities are created equal. A high CVSS score doesn’t automatically mean a vulnerability is your biggest problem. Without context, you’re just chasing numbers. Threat intelligence provides that missing context by telling you which vulnerabilities are being actively exploited by threat actors. This allows you to see weaknesses in relation to real-world attack trends, helping you understand which issues are most important to fix first. Instead of working through an endless backlog, your team can use vulnerability and threat prioritization to focus on the exposures that present a clear and present danger, making your remediation efforts much more strategic.
Knowing you have a vulnerability is one thing; knowing if your security controls can actually stop an attacker from exploiting it is another. This is where Breach and Attack Simulation (BAS) comes in. Fueled by threat intelligence, BAS tools safely simulate real-world attack techniques to test your defenses. This process of adversarial exposure validation helps you identify gaps in your security coverage before a real attacker does. It’s a form of continuous testing that shows you exactly how your defenses hold up against the latest threats, allowing you to optimize your controls and improve your security posture over time.
Ultimately, the goal is to reduce risk as efficiently as possible. Threat intelligence helps you do just that by pinpointing the most critical threats and the most effective ways to address them. By using techniques like attack path analysis, you can identify the key points where a single fix can disrupt multiple potential threats. This helps you move away from a one-by-one patching cycle and toward a more strategic approach. By focusing your remediation efforts on the exposures that are actively being targeted, you can make the biggest impact with your available resources and confidently reduce your total attack surface.
Adopting a CTEM program is a significant step forward for any security team, but it’s not without its hurdles. Like any major operational shift, it requires careful planning and a clear understanding of the potential roadblocks. The good news is that these challenges are well-understood, and with the right approach, you can manage them effectively. Let’s walk through some of the most common issues teams face and, more importantly, how to solve them.
Let’s be real: security teams are almost always stretched thin. Finding the right balance between automated tools and the human expertise needed to interpret their findings is a constant struggle. This gets even harder when you’re dealing with a dozen different security tools that don’t talk to each other. Stitching together data from separate systems to get a single, unified view of risk is a massive time-sink and a source of major frustration. The solution is to find a platform that offers a unified view of cyber risks in one place. This consolidation reduces the complexity of integrations and frees up your team to focus on what they do best: reducing exposure, not wrestling with software.
A successful CTEM program requires constant coordination across multiple departments, including Security, IT, Cloud, and application owners. When ownership isn’t clear, remediation slows down and critical exposures can fall through the cracks. The key is to establish clear roles and responsibilities from the start. Even more, CTEM works best when it stops being seen as just a “security project” and becomes a business priority. You can achieve this by communicating risk in terms the business understands. When leadership sees how vulnerability and threat prioritization directly protects revenue and operations, it becomes much easier to get the cross-functional buy-in you need.
It’s easy to think that buying a new tool will solve all your problems, but CTEM is not a single piece of software. It’s a structured program that changes how you approach cyber risk. Relying on a patchwork of tools without a cohesive strategy won’t get you the results you need. Instead, focus on building a program that addresses your entire attack surface. From there, you have to define what success looks like. If you can’t demonstrate measurable exposure reduction over time, you aren’t really doing CTEM. Establish clear metrics from day one, like a decrease in critical vulnerabilities or a faster mean time to remediation, to track your progress and prove the value of your efforts.
Implementing a CTEM program is a huge step forward, but how do you know it’s actually making a difference? You can’t just set it and forget it. Measuring your success is key to demonstrating value, securing budget, and continuously refining your strategy. It’s about shifting from “we think we’re more secure” to “we know we’ve reduced risk by X%.” The right metrics give you that confidence and provide a clear roadmap for improvement.
To get a clear picture of your program’s effectiveness, you need to track the right key performance indicators (KPIs). These aren’t just vanity metrics; they are the vital signs for your organization’s security health. Think of them as the core numbers that tell you if your efforts are paying off. You can start by tracking metrics like the overall reduction in critical exposures, the percentage of your attack surface you have visibility over, and the mean time it takes to discover new threats. A comprehensive threat exposure management platform will dashboard these for you, helping you monitor your progress and communicate the effectiveness of your CTEM strategies.
Beyond just identifying risks, a successful CTEM program is measured by how quickly and effectively you respond to them. This is where time-based metrics become your best friend. A crucial one is Remediation Latency, which answers the question: How long does it take us to fix a high-risk exposure after we find it? Tracking this, along with your Mean Time to Remediate (MTTR) and vulnerability remediation rate, shows how efficient your response process is. You can also measure the success of your security control validation efforts to see how well your defenses hold up against simulated attacks. These metrics provide clear insights that help you find gaps, optimize your defenses, and get better over time.
How is CTEM really different from the vulnerability management I already do? The biggest difference is the shift from a reactive checklist to a proactive strategy. Traditional vulnerability management often focuses on scanning for a long list of known software flaws (CVEs) and then trying to patch them. CTEM broadens that view to include any exposure an attacker could use, like cloud misconfigurations or weak credentials, and then prioritizes them based on real-world attack paths. It’s less about fixing every single flaw and more about continuously securing the routes an attacker would most likely take to your critical assets.
What’s the first step my team can take to start adopting CTEM? Before you even think about tools, start with the scoping stage. The most practical first step is to sit down with business leaders and clearly define what assets are most critical to your organization’s operations. Instead of trying to protect everything equally, identify your “crown jewels” and the systems that support them. This initial focus gives you a clear boundary for your program and ensures your security efforts are immediately aligned with protecting what matters most to the business.
How does Breach and Attack Simulation (BAS) help with CTEM? Breach and Attack Simulation is the engine behind the validation stage of CTEM. While discovery tools find potential weaknesses, BAS is what confirms if those weaknesses are actually exploitable in your specific environment. It safely runs simulated attacks based on real-world threat intelligence to test if your security controls work as expected. This gives you concrete proof of risk, helping you move from a long list of theoretical problems to a short, actionable list of confirmed exposures.
My team is already overwhelmed. Does CTEM add more work or make things easier? While there’s an initial learning curve, the goal of a CTEM program is to make your team’s work more focused and effective, not just add more tasks. By using threat intelligence to prioritize what to fix, CTEM helps you filter out the noise of low-risk alerts that consume so much time. Instead of chasing hundreds of “critical” vulnerabilities, your team can concentrate on the handful that pose a genuine, immediate threat. This focus ultimately reduces wasted effort and prevents burnout.
How do I prove to my boss that a CTEM program is worth the investment? You can demonstrate its value by focusing on measurable risk reduction. Instead of just reporting on the number of patches applied, track metrics that leadership understands. Show a clear downward trend in the number of high-risk, exploitable exposures over time. Highlight improvements in your team’s response time for critical threats. By connecting your security activities to tangible outcomes like a smaller attack surface and a stronger defense, you can clearly show how the program is making the organization safer.