Comprehensive Threat Exposure Management Platform
 Critical Threat Research : The Iranian Cyber War Intensifies! Download the Report
Critical Threat Research : The Iranian Cyber War Intensifies! Download the ReportFor years, security has been an inside-out job. We scan our own systems, find our own flaws, and create our own to-do lists. But what if we flipped the script and looked at our organization from the outside-in? This is the core idea behind Threat Exposure Management. It’s a continuous process that helps you see your digital footprint exactly as an attacker would, identifying the paths they could take to breach your defenses. Instead of just knowing you have vulnerabilities, you’ll understand which ones are truly exploitable and how they connect to your most critical assets. This is what makes threat exposure management for enterprises so powerful: it moves you from theory to reality.
Think of Threat Exposure Management (TEM) as a continuous process for seeing your organization through an attacker’s eyes. It’s a strategic approach that helps you find, understand, and fix security weaknesses before they can be exploited. For years, security teams have been stuck in a reactive cycle, chasing down endless lists of vulnerabilities generated by scanners. TEM changes that. Instead of just identifying potential flaws, it focuses on the actual attack paths a real adversary could take to breach your systems. This shifts your security posture from being reactive—patching after an incident—to being proactive and predictive.
The core idea is to move beyond simply knowing you have vulnerabilities. TEM answers the more critical questions: Which of these vulnerabilities actually matter? How could they be chained together in an attack? And what is our real-world exposure to the threats that are active right now? By connecting the dots between assets, vulnerabilities, and active threats, you can get a clear picture of your risk and prioritize what to fix first. A comprehensive Threat Exposure Management Platform provides this unified view, helping you focus your resources on the gaps that pose the most immediate danger to your business. It’s about working smarter, not just harder, to reduce your attack surface and confidently answer the question, “Are we secure?”
A strong TEM program is built on several key pillars that work together. It starts with complete Attack Surface Discovery, which means identifying and mapping every single asset connected to your organization, from servers and cloud instances to applications and user devices. Next, Threat Intelligence provides crucial context, highlighting which vulnerabilities are being actively exploited by attackers in the wild. This is combined with Vulnerability Context to understand how a specific weakness could impact your unique environment. Finally, all this information feeds into Risk-Based Prioritization, a system that helps you focus on fixing the most critical exposures first, rather than getting lost in a sea of low-risk alerts.
Threat Exposure Management isn’t a one-time project; it’s a continuous, cyclical process often called Continuous Threat Exposure Management (CTEM). This lifecycle has five main phases that repeat to keep your defenses sharp. It begins with Scoping, where you define what parts of your digital environment you need to protect. The Discovery phase follows, where you continuously scan your total attack surface for assets and potential exposures. In the Prioritization phase, you analyze the discovered vulnerabilities against threat intelligence to determine which ones pose the greatest risk. Next is Validation, where you test if these high-risk exposures are truly exploitable. Finally, the Mobilization phase involves communicating these findings to the right teams so they can take action and remediate the issues.
Security teams are often caught in a cycle of reacting to endless alerts, trying to patch everything at once. This approach is not only exhausting but also ineffective. Threat Exposure Management (TEM) offers a way to break this cycle by shifting from a reactive stance to a proactive one. Instead of just chasing vulnerabilities, TEM helps you understand your entire digital environment from an attacker’s perspective. This allows you to focus your resources on the exposures that truly matter, preventing breaches before they can happen and building a more resilient security posture. It’s about working smarter, not just harder, to protect your organization’s most critical assets.
Traditional security methods often have teams running in circles. You spend countless hours scanning for vulnerabilities and generating massive reports, but much of that effort is wasted on issues that pose little to no real threat. This reactive approach doesn’t account for context. Knowing a weakness exists isn’t enough; you need to know if an attacker can actually use it to cause harm. Without that insight, your team ends up treating every vulnerability with the same level of urgency, leading to burnout and leaving critical exposures unaddressed. This is where effective vulnerability and threat prioritization becomes a game-changer, helping you cut through the noise and focus on what attackers are actively targeting.
Threat Exposure Management is the strategic shift your security program needs. It moves beyond the narrow focus of traditional vulnerability management, which often operates in a silo. Instead, TEM provides a holistic view of your entire attack surface, evaluating risk from a broader, organizational perspective. It’s a smarter way to manage cybersecurity because it helps you find, understand, and fix security problems before attackers can exploit them. This proactive, continuous program identifies, prioritizes, validates, and remediates security exposures across your entire digital footprint. By adopting a TEM framework, you can gain a complete picture of your total attack surface and make confident, risk-informed decisions.
A strong Threat Exposure Management strategy is a continuous cycle that helps you stay ahead of threats by seeing your environment from an attacker’s perspective. It’s a framework built on a few core pillars that work together to reduce your overall risk. By focusing on these key elements, you can move from a reactive, checklist-based approach to a proactive security posture that truly protects your organization. Let’s walk through the foundational components that make a TEM program successful.
First things first: you can’t protect what you don’t know you have. The initial step is getting a complete and continuous view of your entire attack surface. This means identifying every asset that could be a potential entry point for an attacker—from servers and laptops to cloud instances and shadow IT. This isn’t about running a scan once a quarter; it’s about creating a living map of your digital footprint. A comprehensive approach to total attack surface management gives you the foundational visibility needed to understand where you might be exposed at any given moment.
With a map of your attack surface, the next step is to understand the actual risk. A long list of CVEs is just noise without context. Instead of only looking at a vulnerability’s severity score, a strong TEM program asks more important questions: Is this vulnerability actually exploitable in our environment? What critical systems could an attacker access through it? This is where you add vulnerability context. By layering in threat intelligence and business impact, you can prioritize the issues that pose a genuine threat, focusing your team’s efforts where they matter most.
Your attack surface is not static. New assets are deployed and configurations change daily, so a one-and-done approach to security doesn’t work. A mature TEM program involves continuous monitoring to catch new exposures as they appear. But it doesn’t stop there. You also need to validate that your security controls are working as expected and that your remediation efforts were effective. This is where you perform adversarial exposure validation to test your defenses against real-world attack scenarios and ensure your security posture is genuinely improving.
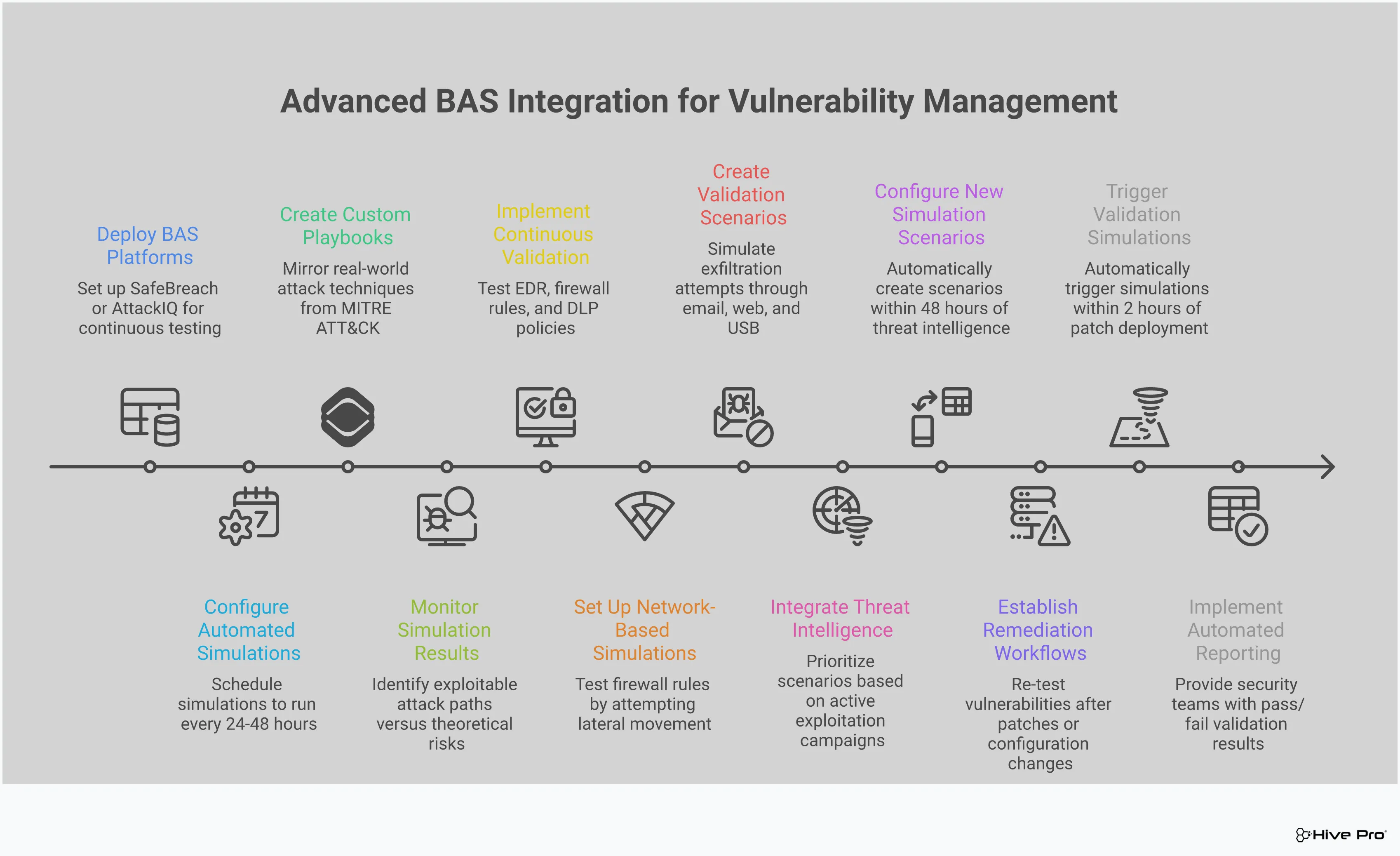
Think of vulnerability management as identifying all the unlocked doors and windows in your house. Breach and Attack Simulation (BAS) is the next logical step: it actually tries to open them. BAS platforms safely and continuously simulate real-world attack techniques to see if your security controls—like your firewall, EDR, and security policies—are actually working as expected. Instead of just knowing you have a vulnerability, you’ll know if it’s truly exploitable in your environment. This moves your security posture from a theoretical state to one that’s been battle-tested, giving you a clear picture of your actual risk.
One of the biggest challenges in security is knowing if your defenses will hold up against a real attack. BAS allows you to stop guessing. By continuously testing your security controls in real-time, you can proactively find weaknesses before an attacker does. This approach helps you stay ahead of potential threats by simulating real-world attack scenarios against your live environment. It’s like having a persistent, automated red team that’s always on, checking your defenses against the latest threats and tactics. This constant validation ensures your security tools are configured correctly and performing effectively day in and day out, giving you confidence in your security investments.
You’ve identified a critical vulnerability, your team has deployed the patch, and the ticket is closed. But how do you know the fix actually worked and didn’t open up another issue? BAS helps you validate your remediation efforts effectively. After you apply a patch or change a configuration, you can run a simulation that specifically targets that vulnerability to confirm it’s no longer exploitable. This validation phase ensures that the security measures you’ve implemented are not just present, but are truly effective in mitigating the risk. It closes the loop on your vulnerability management process, providing concrete proof that your hard work has paid off and your organization is safer.
Traditional vulnerability scans are essential, but they often produce a long list of CVEs without much context, leaving you to figure out what to fix first. BAS goes beyond these scans by providing a comprehensive view of your entire attack surface. It evaluates risk from a broader organizational perspective, transforming raw counts of vulnerabilities into actionable insights that focus on business impact. Instead of just seeing a vulnerability, you see the entire attack path an adversary could take to exploit it. This helps you understand which exposures pose the greatest risk to your critical assets, allowing you to focus your resources where they matter most.
A constant stream of vulnerability alerts can feel overwhelming. With thousands of new CVEs published every year, it’s impossible to patch everything at once. This is where threat intelligence becomes your most valuable asset. Instead of trying to boil the ocean, you can use real-world data to pinpoint which threats actually pose a danger to your organization. A strong TEM program integrates threat intelligence at its core, transforming your security strategy from a reactive checklist to a proactive, focused defense.
This approach allows you to see your environment through an attacker’s eyes. You start to understand which vulnerabilities are being actively exploited in the wild, which ones are part of a popular ransomware campaign, and which ones are just theoretical. By layering this context over your vulnerability data, you can cut through the noise and direct your team’s efforts to the fixes that matter most. This intelligence-led approach is fundamental to reducing your true exposure and building a more resilient security posture. It’s about working smarter, not just harder, to stay ahead of emerging threats.
Not all vulnerabilities are created equal. A critical CVSS score is important, but it doesn’t tell the whole story. The real question is: are attackers actually using this vulnerability to break into systems like yours? This is where active threat data comes in. By integrating intelligence from sources like HiveForce Labs into your TEM program, you can see which vulnerabilities are trending among threat actors and which have known public exploits. This allows you to elevate the priority of a medium-risk vulnerability that’s being widely exploited over a critical one that’s only a theoretical risk. This continuous assessment helps you create a dynamic, risk-based to-do list.
Knowing which vulnerability an attacker might use is one thing; knowing how they’ll use it is another. Threat intelligence gives you crucial insight into the tactics, techniques, and procedures (TTPs) that attackers favor. For example, you might learn that a specific threat group often exploits a certain type of vulnerability to gain initial access, then uses a common misconfiguration to move laterally across the network. This context helps you think beyond a single patch. You can use this knowledge to strengthen related security controls, hunt for signs of specific attacker behaviors, and better prepare your incident response team. Understanding the attacker’s playbook helps you build a more comprehensive and effective defense.
Your team has limited time, budget, and energy. A threat-informed TEM program ensures these resources are spent where they’ll have the greatest impact. Instead of chasing down every vulnerability that pops up on a scan, you can prioritize your remediation efforts on the exposures that are actively being targeted by adversaries. This data-driven approach stops the endless cycle of reactive patching and allows you to make strategic decisions that measurably reduce your organization’s risk. It provides a clear, defensible rationale for your security roadmap, making it easier to communicate priorities to leadership and demonstrate the value of your security investments.
Moving to a Threat Exposure Management (TEM) model isn’t just about adopting new tools; it’s about fundamentally changing your security posture for the better. Instead of constantly reacting to threats, you can get ahead of them. This shift brings tangible benefits that strengthen your defenses, streamline your operations, and better protect your organization. By focusing on what attackers see and how they operate, you can make smarter, more impactful security decisions.
The core advantage of TEM is its proactive nature. Traditional security often feels like a game of catch-up, where you’re patching vulnerabilities after they’ve become a problem. TEM flips the script by helping you find and fix security weaknesses before an attacker can exploit them. It does this by continuously mapping your entire attack surface and correlating it with active threat intelligence and known vulnerabilities. This holistic view allows you to see your organization through an attacker’s eyes, identify the most likely paths they would take, and close those doors before they’re ever tested. It’s about moving from defense to offense in your security strategy.
Security teams are often flooded with thousands of vulnerability alerts, making it impossible to address everything. TEM helps you cut through the noise by transforming raw data into clear, business-focused insights. Instead of just seeing a long list of CVEs, you get a prioritized view of which exposures pose the greatest risk to your critical assets. This allows you to focus your team’s limited time and resources on the fixes that matter most. With effective vulnerability and threat prioritization, you can stop wasting cycles on low-risk issues and direct your efforts toward reducing your organization’s most significant exposures, demonstrating clear progress to leadership.
While TEM aims to prevent breaches, it also prepares you to handle them more effectively when they do occur. A key part of TEM involves continuously testing your security controls against real-world attack scenarios. This adversarial exposure validation acts like a fire drill for your security team, allowing them to practice their response in a controlled environment. By running these simulations, your team can identify gaps in your defenses, refine their playbooks, and build the muscle memory needed to react quickly and decisively during a real incident. This preparation ensures that when an attack happens, your response is swift, coordinated, and effective.
Shifting to a Threat Exposure Management program is a smart move, but it’s not always a straight path. Like any significant change in strategy, it comes with a few common hurdles. Understanding these potential roadblocks ahead of time is the best way to prepare for them. When you know what to expect, you can build a plan that addresses these issues from the start, making your transition to a proactive security posture much smoother. Let’s walk through some of the most frequent challenges teams face and how you can think about solving them.
Your security team is likely swimming in threat data. From vulnerability scanners, threat feeds, and security tools, the sheer amount of information can be overwhelming. The challenge isn’t a lack of data; it’s figuring out what actually matters. This information deluge often leads to “analysis paralysis,” where your team spends so much time sifting through alerts that they struggle to take decisive action. The key is to cut through the noise. Instead of trying to fix everything, a successful TEM program uses real-world threat intelligence to focus on the vulnerabilities that pose a genuine, immediate risk to your organization, which is a core part of effective vulnerability and threat prioritization.
You can’t protect what you can’t see. Modern IT environments are sprawling and complex, with assets spread across on-premise data centers, multiple cloud providers, and remote employee devices. This expansion makes it incredibly difficult to maintain a complete and accurate inventory of your entire attack surface. As noted by industry analysts, this limited visibility is a major roadblock for security teams. Without a comprehensive view, you’re left with dangerous blind spots where threats can hide. A foundational step in any TEM program is to implement tools and processes for total attack surface management, ensuring you have continuous discovery and mapping of all your digital assets.
It’s no secret that there’s a significant shortage of skilled cybersecurity professionals. This talent gap makes it tough for many organizations to build and maintain an effective TEM program. You might not have enough people, or your current team may be stretched thin just handling day-to-day security operations. This is where the right platform can act as a force multiplier for your team. A unified solution like the Uni5 Xposure Platform automates many of the manual, time-consuming tasks involved in TEM. This frees up your security experts to focus on strategic initiatives and high-impact remediation efforts, allowing you to achieve more with the resources you have.
Implementing a Threat Exposure Management (TEM) program is a great first step, but how do you know if it’s actually working? Success isn’t just about being busy; it’s about making a measurable impact on your organization’s security posture. Tracking the right metrics helps you demonstrate the value of your efforts, justify your security investments, and continuously refine your strategy. It’s how you shift from simply managing vulnerabilities to actively reducing risk. By focusing on a few key areas, you can get a clear picture of your program’s effectiveness and show how your team is making the company safer.
You can’t protect what you can’t see. The first measure of success is understanding how much of your environment your TEM program is actually checking. A comprehensive program should cover your entire attack surface, from on-premise servers to cloud assets and employee devices. Once you have a handle on coverage, you can focus on speed. Key metrics like Mean Time to Detect (MTTD) and Mean Time to Remediate (MTTR) are essential. In simple terms, these tell you how fast you find new weaknesses and how quickly you fix them. Lowering these times is a clear indicator that your processes are becoming more efficient and your security posture is improving.
Speed is important, but so is effectiveness. How do you know if your defenses will hold up during a real attack? This is where you can use simulations to test your controls and response plans. Running controlled, fake attacks helps you validate whether a weakness could actually be exploited and if your current defense plans would work as expected. It’s also critical to have clearly defined triggers for your response plan. For example, what specific event or signal initiates a plan to block access to a critical system? Having these answers ready ensures your team can act decisively and effectively when a genuine threat appears, rather than scrambling to figure out the next steps.
Ultimately, the goal of any TEM program is to reduce risk. This means moving beyond simply counting closed vulnerabilities. Instead, focus on whether you are reducing the number of high-risk problems and lowering the overall risk score for your company. Effective exposure management translates raw vulnerability data into meaningful business insights. You should be able to track which business units have successfully reduced their most critical exposures and how the organization’s overall risk is trending over time. This approach provides a clear, C-suite-friendly view of your program’s impact and helps you prioritize the threats that truly matter.
A strong Threat Exposure Management program doesn’t appear overnight. It’s built on a solid foundation of the right technology, collaborative teams, and a smart, structured plan. Trying to do everything at once is a recipe for frustration. Instead, focus on putting these core building blocks in place. This approach will help you create a sustainable program that delivers real risk reduction without overwhelming your teams. By focusing on these key areas, you can move from a reactive security posture to a proactive one, confidently answering the question, “How secure are we?”
To get a handle on your threat exposure, you need the right toolkit. This means choosing technology that helps with core TEM tasks, like vulnerability scanners, threat intelligence platforms, and attack surface management tools. The goal is a single, unified view of your risk. A comprehensive platform like the Hive Pro Uni5 Xposure Platform gives you a constant, real-time view of your entire attack surface. Instead of juggling disconnected tools, you can consolidate your efforts and focus on what truly matters: finding and fixing your most critical exposures before they can be exploited.
Technology alone won’t solve your exposure problems. A successful TEM program requires a culture of shared responsibility. Security, IT, and application teams need to cooperate closely to manage and fix exposures effectively. Fixing a security issue often involves teams beyond just the security department, and there are usually multiple ways to solve a problem. Open communication and clear processes ensure that when a critical vulnerability is found, everyone knows their role and can act quickly. This collaborative approach speeds up remediation and builds a stronger security posture.
Rolling out a TEM program can feel like a huge undertaking, but a phased approach makes it manageable. Gartner suggests a five-step cycle as a clear roadmap. Start by defining your scope, then discover assets and assess their risks. From there, you can prioritize the threats that matter most to your business. Next, validate that these exposures are exploitable and test your security response. Finally, mobilize the right teams for remediation. This isn’t a one-time project; it’s a continuous loop. Regularly identifying and testing vulnerabilities lets you effectively respond to threats and consistently reduce your risk.
How is Threat Exposure Management (TEM) really different from the vulnerability management we already do? Think of it as a shift in perspective. Traditional vulnerability management gives you a long to-do list of potential weaknesses, often based on a technical severity score. TEM asks a more important question: which of these weaknesses could an attacker actually use to harm our business? It moves beyond a simple list of CVEs by adding crucial context, like active threat intelligence and an understanding of your unique attack surface. This helps you see your organization from an attacker’s point of view so you can focus on fixing the pathways they are most likely to take.
My team is already swamped with alerts. Won’t a TEM program just add more noise? Actually, the goal of a strong TEM program is the exact opposite. It’s designed to cut through the noise, not add to it. Instead of treating every alert with the same level of urgency, TEM uses real-world threat intelligence to help you prioritize. It filters out the low-risk, theoretical vulnerabilities and shines a spotlight on the ones that are actively being exploited in the wild. This allows your team to stop chasing down every minor issue and focus their limited time and energy on the exposures that pose a genuine threat to your organization.
What’s the relationship between Breach and Attack Simulation (BAS) and threat intelligence? They work together to give you a complete and realistic picture of your risk. Threat intelligence tells you what attackers are doing—the specific vulnerabilities they’re targeting and the techniques they’re using. Breach and Attack Simulation then takes that information and safely tests it against your environment to see if those attack methods would actually work. In short, threat intelligence provides the “what,” and BAS provides the “what if,” helping you validate whether a theoretical threat is a practical danger for you.
What’s the most important first step to get started with TEM? The foundational first step is always visibility. You simply can’t protect what you don’t know you have. Before you can prioritize threats or validate controls, you need a complete and continuous inventory of your entire attack surface. This means identifying every asset, from servers in your data center to cloud instances and employee devices. Gaining this comprehensive view is the essential starting point that makes all other aspects of a successful TEM program possible.
How can I justify the shift to a TEM program to my leadership? Focus on two key business outcomes: smarter resource allocation and measurable risk reduction. Explain that TEM stops the cycle of spending time and money fixing low-impact issues. Instead, it directs your team’s efforts to the threats that could actually disrupt the business. You can frame it as moving security from a reactive cost center to a proactive function that provides a clear, defensible strategy for protecting the company’s most critical assets against the most likely attacks.