Comprehensive Threat Exposure Management Platform
 Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the Report
Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the ReportAttackers don’t think in terms of isolated CVE scores. They look for the path of least resistance, chaining together multiple weaknesses across your entire attack surface to reach their goal. This is why the search for a Kenna replacement is so critical. It’s not just about finding a new tool to list vulnerabilities; it’s about adopting a platform that helps you see your organization through an attacker’s eyes. A modern threat exposure management platform gives you a complete picture of your assets, prioritizes threats based on real-world exploitability, and even lets you test your defenses to ensure they work as expected.
If you’re a Kenna Security user, you’re likely facing a big decision. The platform has been a staple for many vulnerability management teams, but recent changes mean it’s time to plan your next steps. This isn’t just about replacing a tool; it’s an opportunity to rethink your entire approach to security and adopt a more proactive strategy. The end of Kenna signals a broader shift in the industry, moving beyond simply identifying vulnerabilities to truly understanding and managing your organization’s exposure to threats. This moment gives you a unique chance to evaluate what’s working, what isn’t, and how a modern platform can better align with your security goals.
Many teams are using this transition to move from a reactive stance, where they are constantly chasing down a long list of CVEs, to a proactive one. A modern approach helps you see your assets from an attacker’s perspective, prioritize what actually matters, and validate that your security controls are working as expected. By starting your search now, you can thoughtfully choose a partner that will not only fill the gap left by Kenna but also help you build a more resilient and forward-thinking security program for the years to come. It’s a chance to get ahead of threats instead of just responding to them.
The main reason to start your search is that Cisco is officially sunsetting its Vulnerability Management platform, formerly known as Kenna. According to the official announcement, the end-of-sale date is set for March 2026, with all support ending in June 2028. While that might seem far off, migrating your vulnerability management program takes time and careful planning. Waiting until the last minute can lead to a rushed decision and a difficult transition. Starting the process now gives your team the space to properly evaluate alternatives and ensure a smooth handover without disrupting your security operations. This proactive planning is key to maintaining your security posture throughout the change.
The security landscape is shifting away from traditional, reactive vulnerability management. Today, leading organizations are adopting a more comprehensive approach called Continuous Threat Exposure Management (CTEM). Instead of just cataloging vulnerabilities, a CTEM program helps you see your organization through an attacker’s eyes. It’s a proactive cycle of discovering your entire attack surface, prioritizing threats based on real-world exploitability, validating your defenses, and mobilizing teams for remediation. This transition from Kenna isn’t just a forced tool swap; it’s your chance to move from a simple vulnerability list to a true understanding of your overall threat exposure and build a more effective, risk-informed security strategy.
With Kenna’s end-of-life confirmed, several strong platforms are ready to fill the gap. Each offers a unique approach to threat and vulnerability management, so the right choice depends on your team’s specific needs and long-term security goals. Whether you need a direct replacement or want to adopt a more comprehensive exposure management program, these are the top contenders to consider.
If you’re looking for a platform that moves beyond traditional vulnerability management, Hive Pro is a strong contender. The Uni5 Xposure Platform is built for proactive threat exposure management. It gives you a single, unified view of your cyber risks by continuously scanning your entire attack surface. What sets it apart is the focus on imminent threats, using in-house threat intelligence from HiveForce Labs to help you prioritize what actually matters. It’s a complete suite that covers everything from asset discovery and vulnerability prioritization to validating your security controls and guiding remediation. This end-to-end approach helps you shift from a reactive posture to one where you can confidently reduce your exposure before an attack happens.
Nucleus Security has positioned itself as a direct replacement for Kenna, making it a natural starting point for many teams. According to the company, “Nucleus is positioned as the primary, direct replacement for Kenna, focusing on unified exposure management and offering, in some cases, buyout options for existing contracts.” This focus on a smooth transition is a major draw, especially for organizations looking to minimize disruption. Their platform centers on unifying exposure management, aggregating data from your existing tools to provide a centralized view of risk. For teams that want a solution designed to fill the specific gap Kenna is leaving, Nucleus is definitely one to evaluate.
For organizations needing a broad and comprehensive view of their environment, Tenable One is a powerful option. It’s designed as an all-in-one platform that goes beyond traditional network vulnerabilities. As Tenable explains, “Tenable One offers a robust, comprehensive exposure management platform that covers risk assessment for assets, cloud, and applications.” This makes it a great fit if your attack surface spans on-premise infrastructure, multiple cloud environments, and web applications. The platform’s strength lies in its ability to correlate data from across these different environments to give you a holistic understanding of your exposure, helping you see connections and attack paths you might otherwise miss.
If your primary goal is to replicate and improve upon Kenna’s risk-prioritization capabilities, Qualys VMDR (Vulnerability Management, Detection, and Response) is worth a look. It’s recognized as a “viable option for similar risk-prioritization needs,” making it a solid choice for teams that valued Kenna’s approach to scoring and ranking vulnerabilities. Qualys VMDR combines asset discovery, vulnerability assessment, threat detection, and response actions into a single application. This integrated workflow helps streamline the entire lifecycle, from identifying a new asset to patching a critical vulnerability. It’s a well-established platform in the vulnerability management space, known for its accuracy and extensive coverage of different types of assets. You can find more details on Software Reviews.
Rapid7’s InsightVM is another leading alternative that excels at turning vulnerability data into clear, actionable steps. It’s frequently listed among the top alternatives, providing “effective risk prioritization and remediation actions.” InsightVM uses real-time threat intelligence and an understanding of attacker methodologies to help you focus on the vulnerabilities most likely to be exploited. It also provides clear guidance on remediation, helping your IT and security teams work together more efficiently. The platform includes features like live dashboards, goal-based tracking, and integrations with ticketing systems to help you manage your remediation projects from start to finish. For a closer look at user comparisons, you can check out reviews on G2.
When Kenna Security first came on the scene, it was a game-changer for vulnerability management. But the security landscape has evolved, and so have the tools we need to defend it. Simply identifying and prioritizing vulnerabilities isn’t enough anymore. Attackers don’t just exploit a single CVE; they chain together multiple weaknesses across your entire attack surface. Your next platform needs to think like an attacker and give you a complete picture of your exposure.
This means moving beyond traditional vulnerability management and toward a more holistic approach. You need a platform that not only finds weaknesses but also understands their business context, validates your security controls, and streamlines the entire process from detection to remediation. As you evaluate your options, look for a solution that provides a unified view of your cyber risks. The goal is to get a clear, continuous understanding of your security posture so you can focus your team’s efforts on the threats that truly matter.
Let’s be honest, vulnerability scanners are noisy. They can generate thousands of findings, and most of them aren’t urgent. A great Kenna replacement cuts through that noise by prioritizing vulnerabilities based on actual risk to your organization, not just a generic CVSS score. It should analyze multiple factors, including real-time threat intelligence, asset criticality, and evidence of active exploitation. This approach helps you focus on the small percentage of vulnerabilities that pose a genuine threat. Your platform should clearly explain why a vulnerability is a high priority, giving your team the context needed to act decisively and defend your most critical assets first.
You can’t protect what you can’t see. Your organization’s attack surface is constantly changing, with new cloud instances, IoT devices, and applications appearing all the time. A modern threat exposure management platform needs to provide total attack surface management, giving you a complete and continuously updated inventory of all your assets. This goes beyond simple network scans. It means discovering unknown assets, identifying misconfigurations, and understanding the complex relationships between different parts of your infrastructure. By seeing your organization from an attacker’s perspective, you can identify and close security gaps before they can be exploited.
Threat intelligence gives you the “so what?” behind every vulnerability. It’s the critical context that tells you which threats are being actively exploited by attackers right now. A solid Kenna alternative should seamlessly integrate this intelligence into its prioritization engine. This information shouldn’t be in a separate dashboard or a static report; it needs to be woven directly into your workflows. Look for a platform with a dedicated research team, like HiveForce Labs, that provides timely and relevant intelligence. This ensures your team is always working on fixing the vulnerabilities that attackers are actively targeting, making your remediation efforts much more effective.
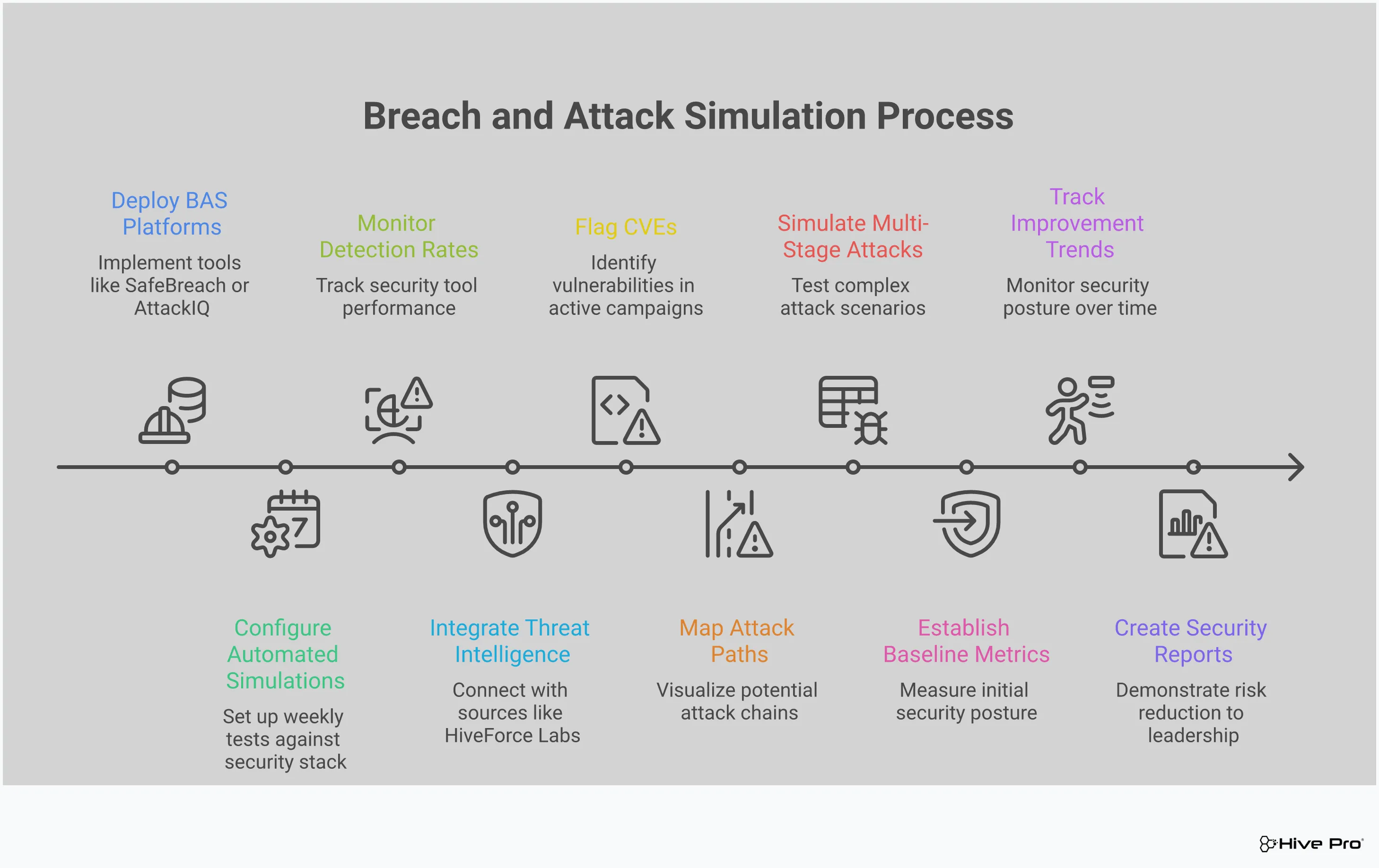
Finding a vulnerability is one thing; knowing if your security controls can actually stop an attack is another. This is where Breach and Attack Simulation (BAS) becomes essential. Instead of just assuming your firewalls and EDR are working, a platform with BAS capabilities allows you to safely simulate real-world attack scenarios. This process of adversarial exposure validation helps you measure the true effectiveness of your defenses. It identifies gaps in your security posture, like misconfigured controls or blind spots in your monitoring, so you can fix them before an actual attacker finds them. It’s a proactive way to ensure your security stack is performing as expected.
Identifying and prioritizing threats is only the first step. The real goal is to fix them. A top-tier Kenna replacement should help you close the loop by automating your remediation workflows. This means integrating with your existing tools, like ticketing systems and patch management solutions, to streamline the entire process. The platform should automatically assign remediation tasks to the correct teams, provide clear instructions, and track progress until the vulnerability is resolved. By automating these manual steps, you can reduce human error, shorten your time to remediate, and free up your security team to focus on more strategic initiatives.
Let’s be honest, staring at a list of thousands of vulnerabilities feels overwhelming. The old way of using CVSS scores alone just doesn’t cut it anymore. You can’t possibly fix everything, so how do you decide what to tackle first? This is where threat intelligence changes the game. It moves you from a reactive guessing game to a proactive, data-driven strategy. By layering real-world threat data over your vulnerability scans, you get the context you need to focus your team’s efforts on the issues that truly pose a danger to your organization. It’s about working smarter, not just harder, to reduce your actual exposure.
Instead of treating every vulnerability as a potential crisis, threat intelligence acts as a filter, showing you what attackers are doing right now. This insight allows you to see your environment through an adversary’s eyes. You can pinpoint the specific weaknesses they are most likely to target and understand the potential impact on your most critical assets. This shift in perspective is fundamental. It transforms vulnerability management from a compliance-driven, check-the-box activity into a strategic function that directly reduces business risk and strengthens your security posture against real-world attacks.
Not all vulnerabilities are created equal. A critical vulnerability on a non-essential, internal-only server is less of a fire drill than a medium-risk one on your main web application. Threat intelligence provides the real-world context to understand these differences. It helps you see why a specific risk is important by connecting it to your company’s unique assets and active threat campaigns. Instead of chasing every high CVSS score, you can focus your resources on the small percentage of vulnerabilities that attackers are actually exploiting. This is the core of effective vulnerability and threat prioritization, allowing your team to address the most urgent threats first.
Threat actors have their favorite exploits, and they use them over and over. Threat intelligence gives you a direct line of sight into what’s happening in the wild right now. It tells you which vulnerabilities have known public exploits and are being actively used in attacks. This information is critical because it separates theoretical risks from immediate threats. By focusing on actively exploited vulnerabilities, you are directly countering the methods attackers are currently using. You can find this information in regularly updated threat advisories that allow you to patch the holes most likely to be targeted, significantly reducing your attack surface before an incident occurs.
Beyond individual exploits, threat intelligence helps you understand broader attacker trends and campaigns. Are threat actors targeting a specific technology in your stack? Is your industry currently under attack by a particular ransomware group? Answering these questions helps you anticipate an attacker’s next move. This is a key part of the shift from simple vulnerability management to a more comprehensive threat exposure management strategy. It’s not just about finding individual security flaws; it’s about understanding how all the pieces connect to create pathways an attacker could follow. This holistic view is essential for securing your organization with a platform like Uni5 Xposure.
Finding a vulnerability is one thing, but knowing if it can actually be exploited in your environment is another challenge entirely. This is where Breach and Attack Simulation (BAS) comes in. Instead of just guessing whether your security controls will hold up against an attack, BAS lets you test them safely and proactively. It’s like having a dedicated red team on-demand, constantly running controlled attack scenarios to see what breaks.
A modern threat exposure management platform should offer more than just a list of vulnerabilities. It needs to provide a way to validate your defenses against real-world threats. By incorporating adversarial exposure validation, you can move beyond theoretical risk scores and see exactly how an attacker could move through your network. This gives you concrete evidence of where your security gaps are, helping you prioritize fixes that have the most impact and prove the value of your security investments to leadership.
Your security stack is made up of firewalls, endpoint detection, and other tools designed to protect you. But are they configured correctly? Are they actually working as expected? Breach and Attack Simulation tools help you answer these questions by letting you simulate real-world attack scenarios to test your security controls. This proactive approach helps you find gaps in your defenses before a real attacker does. Think of it as a continuous fire drill for your security systems, ensuring every component is ready to respond when a genuine threat appears.
Traditional vulnerability scanners are great at telling you what’s broken, but they don’t always show you what matters most. A long list of CVEs can be overwhelming and may not reflect your actual risk. BAS provides a much clearer picture by measuring not just vulnerabilities, but the potential impact of those vulnerabilities in the context of real-world attack paths. It helps you understand your true exposure by showing you which weaknesses can be chained together to lead to a breach. This context is critical for effective vulnerability and threat prioritization.
The threat landscape is always changing, with new attack techniques emerging all the time. A security control that was effective yesterday might not be tomorrow. This is why continuous validation is so important. With the evolving threat landscape, regular testing of your security controls is crucial. BAS platforms enable you to consistently run tests against the latest threats and tactics described in threat advisories. This automated and continuous approach ensures your security posture remains strong over time, adapting as new threats appear and as your own environment changes.
Moving on from Kenna means you’re not just choosing new features; you’re also evaluating new pricing structures. The final cost is important, but the model itself can have a big impact on your budget, scalability, and overall value. Understanding the different ways vendors package their solutions will help you find a platform that aligns with your financial strategy and operational needs, preventing any surprise costs down the road. Let’s break down the common pricing models you’ll encounter.
Most modern cybersecurity platforms have moved away from traditional perpetual licensing, which involves a large upfront payment for the software and separate, ongoing fees for maintenance and support. Instead, you’ll likely find subscription-based models, often delivered as a Software-as-a-Service (SaaS) solution. This approach bundles the software, support, and updates into a recurring annual or monthly fee. The big advantage here is flexibility. An all-inclusive SaaS model lets you deploy the software wherever it makes the most sense for your organization, whether that’s in your own data centers or in the cloud, without being locked into a single environment.
Two of the most common pricing structures you’ll see are asset-based and user-based. Asset-based pricing ties the cost to the number of assets you’re monitoring, like servers, endpoints, or cloud resources. This model scales directly with your attack surface, making it a predictable choice for many vulnerability management programs. On the other hand, user-based pricing is determined by how many people on your team need access to the platform. This can be cost-effective for small teams managing a large number of assets, but costs can climb quickly as your team grows. Consider which metric, assets or users, is more likely to scale in your organization to find the best fit.
The price you see on a vendor’s website is rarely the final price, especially for enterprise customers. Vendors are competing for your business, and many are offering special terms to attract former Kenna users. For example, some vendors explicitly offer preferred commercial terms to recognize the investment you already made in your previous solution. Don’t hesitate to ask potential vendors about migration discounts, multi-year contract benefits, or bundled packages. This is your opportunity to negotiate a deal that fits your budget. Always review the contract details to understand what’s included, such as support levels, training, and implementation assistance, to ensure you’re getting the full picture.
Switching platforms is a big decision, and marketing materials only tell you part of the story. To get the full picture, it’s smart to see what current users are saying about their experiences. Looking at reviews and community discussions can give you honest insights into a tool’s real-world performance, integration capabilities, and the quality of customer support you can expect. These firsthand accounts help you understand how a platform will actually function within your environment and what challenges you might face. This feedback cuts through the noise and helps you focus on what truly matters for your team’s success. Here are a few key themes that pop up when teams discuss their move from Kenna.
When you’re managing thousands of vulnerabilities, you need a tool that can keep up. Sluggish dashboards and unreliable scans can bring your entire workflow to a halt. Users often highlight performance as a key factor in their satisfaction. For example, some reviews note that certain platforms offer more robust and reliable performance in managing vulnerabilities effectively compared to others. When evaluating your options, look for feedback on how the platform handles large, complex environments. Does it process data quickly? Are the reports accurate and timely? A high-performing tool ensures your team can focus on remediation, not on waiting for pages to load.
Your vulnerability management tool doesn’t operate in a vacuum. It needs to connect seamlessly with the other security tools in your stack. This is a major point of discussion for teams moving on from Kenna. Alternatives like Nucleus and Tenable One are often praised for their extensive integration libraries, connecting with hundreds of security tools. This allows you to create a central hub for all your security data, giving you a more complete view of your total attack surface. A platform with broad integration support makes it easier to automate processes and enrich your vulnerability data, leading to smarter, faster decisions.
Migrating to a new platform is a significant project, and strong vendor support can make all the difference. You’re not just buying software; you’re building a partnership. Users often recommend looking for vendors that offer a clear, guided plan for the transition. Does the provider offer dedicated onboarding support to get your team up and running? How responsive is their customer service when issues arise? A vendor with a reputation for excellent support and comprehensive training will help you minimize disruption and ensure your team can leverage the new platform to its full potential from day one.
Moving away from a tool as embedded as Kenna Security can feel like a huge undertaking, but it’s also a great opportunity to refine your threat exposure management program. Breaking the transition down into manageable steps makes the process much smoother. A successful switch hinges on three key areas: migrating your data, connecting your tools, and adapting your team’s processes. By planning ahead, you can ensure a seamless move and avoid any last-minute disruptions to your security operations. Think of this not just as a replacement project, but as a chance to upgrade your capabilities and align your security efforts more closely with your business goals.
First things first, let’s talk about your data. You have years of valuable historical information in Kenna, from vulnerability scans to remediation tickets. The key is to start planning your migration strategy well before the official end-of-life date. Decide what data is essential to move over, such as asset inventories, open vulnerabilities, and historical risk trends. This is the perfect time to do some housekeeping. You can clean up outdated asset information and archive old data that you don’t need to access daily. A well-planned data migration ensures you start with a clean, relevant dataset in your new platform, making your vulnerability management program more efficient from day one.
Your vulnerability management platform doesn’t operate in a silo. It needs to communicate with the rest of your security ecosystem, including scanners, ticketing systems, and SIEMs. Before you choose a replacement, map out every tool that currently integrates with Kenna. Leading platforms today offer extensive integration libraries, connecting with hundreds of other security tools. When evaluating alternatives, check for pre-built connectors for your essential systems. A platform with robust integration capabilities, like the Hive Pro Uni5 Xposure Platform, will save you from complex custom development and ensure a smooth, uninterrupted flow of security data across your entire stack.
A new tool inevitably changes how your team works, and this is often for the better. Modern platforms can streamline your processes by automatically assigning remediation tasks to the right teams and providing role-specific dashboards. Involve your security operations, IT, and DevOps teams early in the evaluation process. Let them see how a new tool could simplify their day-to-day tasks. Look for a solution that helps you improve your vulnerability and threat prioritization workflows, not just replicate them. Getting your team’s input and buy-in is critical for a successful adoption and ensures everyone can make the most of the new platform’s features.
Making the switch from Kenna Security is more than just a simple tool replacement; it’s a chance to rethink and strengthen your entire vulnerability management program. Instead of looking for a one-to-one feature match, think about what a modern threat exposure management platform can do for you. This is your opportunity to move from a reactive posture, where you’re constantly chasing down vulnerabilities, to a proactive one where you can anticipate and neutralize threats before they become real problems. The right platform will give you a complete picture of your risk, from your cloud environments to your on-premise servers, and help you focus on the issues that truly matter.
As you evaluate your options, consider the long-term partnership. You’re not just buying software; you’re investing in a solution that will become a core part of your security operations. Look for a vendor that provides robust support, continuous innovation, and a clear vision for the future of cybersecurity. The goal is to find a platform that not only solves today’s challenges but also adapts to the evolving threat landscape. This strategic approach will ensure your transition is a true upgrade, setting your team up for success for years to come.
First, take a detailed inventory of your current security stack. What scanners, agents, and cloud security tools are you using? This is crucial because some Kenna alternatives are tied to a specific vendor’s scanning technology, while others are vendor-agnostic, designed to ingest data from any source. If your organization uses a mix of tools from different vendors, a vendor-agnostic platform will offer the most flexibility and prevent you from being locked into a single ecosystem. Make sure the solution you choose has robust, well-documented APIs to ensure a smooth integration with your existing tools and workflows, from ticketing systems to SIEMs.
To compare vendors objectively, build a scorecard based on the capabilities that matter most to your team. A modern platform should do more than just score vulnerabilities; it needs to provide a comprehensive view of your entire attack surface. Your framework should prioritize features like the ability to combine data from all your security tools, use real-time threat intelligence to contextualize risk, and offer clear, actionable guidance on how to fix things. Look for a solution that helps you understand how vulnerabilities connect across your assets, from a line of code to a live system, so you can address the root cause of your exposure.
A proof of concept is your chance to see how a platform performs in your unique environment with your actual data. Don’t rely on demos alone. During the PoC, a great strategy is to run the potential replacement tool in parallel with your existing Kenna instance. This allows you to directly compare the prioritization, reporting, and workflows side-by-side. Define clear success criteria before you begin. Can the platform easily ingest all your data sources? Does it help your team work more efficiently? A successful PoC should leave you feeling confident that the new solution not only meets your requirements but also empowers your team to reduce risk more effectively.
Why should I start looking for a Kenna alternative now if the support doesn’t end for a few years? While the final end-of-life date seems distant, migrating a core security platform isn’t a quick project. A thoughtful transition involves evaluating vendors, running a proof of concept with your own data, negotiating contracts, and migrating years of historical information. Starting now gives you the time to make a strategic choice without being rushed, ensuring the new platform truly fits your needs and improves your security program, rather than just being a last-minute replacement.
What is the biggest difference between what Kenna did and what a modern Threat Exposure Management platform does? Kenna was excellent at helping you prioritize a long list of known vulnerabilities. A modern Threat Exposure Management platform takes a much broader view. Instead of just looking at individual CVEs, it helps you see your organization from an attacker’s perspective by mapping your entire attack surface, integrating real-time threat intelligence, and validating that your security controls are actually working. It shifts the goal from managing a list to proactively reducing your overall exposure to real-world threats.
How does integrating threat intelligence actually change my day-to-day work? Integrating threat intelligence directly into your platform transforms your daily workflow from a guessing game into a focused mission. Instead of chasing high CVSS scores that might not be relevant, you can immediately see which vulnerabilities are being actively exploited by attackers right now. This allows your team to confidently focus its time and resources on fixing the handful of issues that pose an immediate danger, making your remediation efforts significantly more effective.
We already have firewalls and other security tools. Why do we also need Breach and Attack Simulation (BAS)? Your firewalls and other controls are your first line of defense, but you can’t just assume they are configured perfectly and working as intended. Breach and Attack Simulation acts as a quality control check for your entire security stack. It safely simulates real-world attack techniques to test your defenses, revealing misconfigurations or gaps an attacker could exploit. It provides concrete proof of whether your security investments are actually protecting you.
What’s the most important step in making sure the transition to a new platform is successful? The most critical step is to involve your team early and plan your proof of concept (PoC) carefully. Don’t just rely on a vendor’s demo. A successful PoC should use your own data to test the platform’s performance in your specific environment. This allows you to directly compare its prioritization logic, reporting, and workflows against your current setup. Getting your team’s hands-on feedback ensures the new tool will genuinely make their jobs easier and your organization more secure.