Comprehensive Threat Exposure Management Platform
 Critical Threat Research : The Iranian Cyber War Intensifies! Download the Report
Critical Threat Research : The Iranian Cyber War Intensifies! Download the ReportHow do you know if your security controls will actually stop an attack? You can have the best firewalls and endpoint protection on the market, but misconfigurations or undiscovered assets can render them useless. This is the fundamental question that traditional vulnerability management can’t answer. It can tell you where the weaknesses are, but not which ones are truly exploitable in your specific environment. An exposure management cybersecurity platform provides the answer by safely mimicking real-world attack techniques to continuously test your defenses. This validation gives you concrete proof of risk, allowing you to fix the most critical weaknesses first.
Exposure management is a continuous cycle of identifying, assessing, and reducing the risk from all your company’s exposed assets. Think of it as a complete security check-up that never stops. It goes beyond just finding vulnerabilities; it’s about understanding your entire attack surface—from your networks and applications to your cloud infrastructure and data—and figuring out which weaknesses are most likely to be exploited by an attacker. This approach helps you see your organization through an attacker’s eyes, allowing you to find and fix the most critical security gaps before they can cause real damage.
The goal is to move from a state of constantly reacting to threats to proactively managing your security posture. Instead of drowning in a sea of alerts and vulnerability reports, you get a clear, prioritized list of what actually needs your attention. This means your security team can focus its time and resources on the issues that pose a genuine threat to your business. By adopting an exposure management mindset, you’re not just patching holes; you’re building a more resilient and defensible security program that can adapt to a constantly changing threat landscape.
For years, security teams have been stuck in a reactive loop: scan for vulnerabilities, get a massive list, try to patch everything, and hope for the best. A proactive security approach flips this model on its head. It assumes that system compromises are not a matter of if, but when, and shifts the focus to continuous risk assessment and mitigation. Instead of waiting for an attack to happen, you’re constantly searching for potential entry points and weaknesses, just like an attacker would.
This shift means you’re always one step ahead. You’re not just responding to alerts; you’re actively reducing your attack surface and validating that your security controls work as expected. This allows you to manage your threat exposure before it becomes a full-blown incident, saving your team from the stress of firefighting and your company from the costs of a breach.
Traditional vulnerability management was built for a simpler time. Today’s IT environments are dynamic and complex, with cloud services, containers, and other assets spinning up and down in minutes. Standard security scans often miss these fast-changing components, leaving dangerous blind spots in your defenses. The result is often an overwhelming list of vulnerabilities with little context, making it nearly impossible to know where to start.
Exposure management addresses these shortcomings by providing a unified view of your total attack surface. It doesn’t just count vulnerabilities; it contextualizes them based on asset criticality, potential business impact, and active threats. This helps you see the full picture of your risk, including the short-lived assets that traditional tools miss, so you can prevent attacks before they happen.
How do you know if your security controls will actually stop an attack? Breach and Attack Simulation (BAS) gives you the answer. BAS tools safely mimic real-world attack techniques to continuously test your defenses. By combining these simulated attacks with external scanning, you can see exactly where your security might fail and which vulnerabilities are truly exploitable in your environment.
This is a game-changer for prioritization. Instead of guessing which CVEs are the most dangerous, you get concrete proof. Adversarial exposure validation helps you move beyond theoretical risk to understand your actual exposure. It shows you the potential attack paths an adversary could take, allowing you to fix the most critical weaknesses first and confirm that your security investments are paying off.
Not all vulnerabilities are created equal. A critical vulnerability that no one is exploiting is far less of a priority than a medium-risk one that’s part of an active ransomware campaign. This is where threat intelligence comes in. By integrating up-to-the-minute data on attacker tactics, techniques, and procedures (TTPs), you can make smarter decisions about risk assessment and mitigation.
High-quality threat intelligence from research teams like HiveForce Labs provides the context needed to focus on what matters now. It helps you understand which vulnerabilities are being targeted in the wild, allowing you to prioritize patches and defensive actions based on real-world threats. This ensures your team isn’t wasting time on low-risk issues and is instead concentrating its efforts on stopping the attacks that are most likely to hit you.
If your security team feels like they’re constantly playing catch-up, you’re not alone. The old way of managing security—running periodic scans and tackling an endless list of vulnerabilities—simply doesn’t work anymore. Modern IT environments are too complex and change too quickly. This is where an exposure management platform comes in. It shifts your entire security approach from being reactive to proactive.
Instead of just identifying weaknesses, a threat exposure management platform helps you see your organization through an attacker’s eyes. It connects the dots between a vulnerability on a server, a misconfigured cloud service, and a critical business application. This gives you a clear, unified view of your actual risk. By understanding which exposures are most likely to be exploited and what their business impact would be, you can stop guessing and start making confident, data-driven decisions to protect what matters most. This approach doesn’t just make you more secure; it makes your security operations more efficient and effective.
Every organization has security blind spots—unmanaged assets, shadow IT, or misconfigured cloud services that traditional scanners miss. These gaps represent unknown and unmanaged risks. An exposure management program is designed to shine a light on these dark corners. It’s about identifying, assessing, and mitigating the risk from all your exposed resources, including networks, applications, and data.
Without this comprehensive view, you’re essentially leaving doors open for attackers. A single forgotten server or an overlooked API can become the entry point for a major breach. The real cost of these blind spots isn’t just the potential financial loss from an incident; it’s the operational chaos, reputational damage, and erosion of customer trust. A proactive approach helps you continuously map your entire attack surface so you can close these gaps before they can be exploited.
A long list of CVEs isn’t a risk management strategy; it’s a recipe for burnout. The reality is that most vulnerabilities will never be exploited. The key is knowing which ones will. Just finding vulnerabilities isn’t enough. You need to understand which ones are truly exploitable in your specific environment and how they could impact your business operations.
This is the fundamental difference between vulnerability management and exposure management. Instead of just counting vulnerabilities, an exposure management platform provides the context you need to prioritize what actually matters. It combines vulnerability data with threat intelligence and an understanding of your asset criticality. This allows your team to focus its limited time and resources on fixing the handful of issues that pose a genuine, immediate threat to your organization.
Today’s IT environments are in constant motion. Cloud instances are spun up and down in minutes, developers deploy new applications daily, and employees connect from anywhere. Traditional security tools that rely on scheduled scans can’t keep pace with this rate of change, often missing temporary assets and leaving them completely unprotected.
An exposure management platform is built for this dynamic reality. It provides continuous discovery and monitoring, ensuring that as your environment changes, your security posture adapts with it. This proactive approach helps you find new digital assets and weak spots as they appear, not weeks or months later during a quarterly scan. By having a real-time understanding of your organization’s cyber risk, you can make much smarter decisions about where to invest your security budget and resources for the biggest impact.
When you start looking at exposure management platforms, you’ll quickly realize they aren’t all built the same. The right platform moves beyond simple scanning and reporting to give you a clear, actionable path to reducing risk. It should connect the dots between a potential weakness and a real-world threat, helping your team focus its energy where it counts. To make sure you’re choosing a solution that will actually strengthen your security posture, there are a few core capabilities that are non-negotiable. These features work together to create a complete, continuous cycle of discovery, prioritization, validation, and remediation.
You can’t protect what you can’t see. This might sound like a cliché, but it’s the foundation of any solid security program. A top-tier exposure management platform must begin by providing a comprehensive and continuous view of your entire attack surface. This goes beyond your known servers and applications to include cloud environments, IoT devices, external-facing infrastructure, and shadow IT. The goal is to eliminate blind spots by continuously monitoring your full attack surface for any new or changed assets. This complete visibility is not just a security best practice; it’s also essential for maintaining compliance with regulations like GDPR and HIPAA, which require you to know where your data is and how it’s being protected.
If your team is spending its days chasing down every single vulnerability flagged by a scanner, you’re fighting a losing battle. The sheer volume is overwhelming. A modern exposure management platform cuts through the noise by prioritizing vulnerabilities based on actual risk to your business. Instead of relying solely on a generic CVSS score, it should analyze multiple factors: Is the vulnerability actively being exploited in the wild? Do you have compensating controls in place? How critical is the affected asset to your operations? This context-aware approach allows you to prioritize exposure and focus your limited resources on fixing the flaws that attackers are most likely to target first.
Prioritization is only as good as the data that fuels it. That’s why a critical feature is the integration of continuous, high-fidelity threat intelligence. The platform should be constantly updated with information on the latest exploits, attacker tactics, and active campaigns. This ensures that your risk assessments are based on the current threat landscape, not on outdated information. Look for platforms that have a dedicated research team or leverage in-house intelligence to provide unique insights. This allows the system to dynamically adjust risk scores as new threats emerge, giving you a proactive edge and helping you anticipate an attacker’s next move before it happens.
How do you know if a critical vulnerability is truly exploitable in your specific environment? You test it. Breach and Attack Simulation (BAS) is a key feature that separates leading platforms from the rest. BAS capabilities safely mimic real-world attack techniques to test whether your existing security controls—like firewalls, WAFs, and EDR solutions—would actually stop an attack. This process of adversarial exposure validation provides concrete proof of exploitability. It answers the crucial question, “Are we really vulnerable to this?” The results help you validate which exposures pose an immediate threat and confirm that your security investments are working as intended.
Finding and prioritizing threats is only half the job. An effective exposure management platform must also help you fix them efficiently. Look for features that automate and streamline remediation workflows. This includes automatically generating tickets in systems like Jira or ServiceNow, assigning tasks to the right teams, and providing clear, step-by-step guidance for patching or mitigation. By integrating directly with your IT and DevOps tools, the platform can streamline the processes involved in remediation, significantly reducing the time it takes to close a critical exposure. This closes the loop on the management lifecycle and fosters better collaboration between security and operations teams.
Choosing the right exposure management platform can feel overwhelming, but it really comes down to understanding your organization’s specific needs and security posture. The market is filled with excellent tools, each with a slightly different approach to helping you get ahead of threats. Some platforms excel at giving you a complete, unified picture of your entire attack surface, from on-premise servers to cloud assets. Others specialize in niche areas, like validating your existing security controls or mapping out potential attack paths within your internal network.
As you explore your options, think about what matters most to your team. Are you struggling with tool sprawl and need a single source of truth? Or is your biggest challenge securing a complex cloud environment? Maybe you need to prove to leadership that your security investments are actually working. The platforms we’re about to look at represent the best of these different philosophies. From continuous validation and attack simulation to deep cloud visibility, these are the solutions that are truly pushing the boundaries of what it means to manage cyber exposure proactively. We’ll break down what makes each one stand out so you can find the perfect fit for your security program.
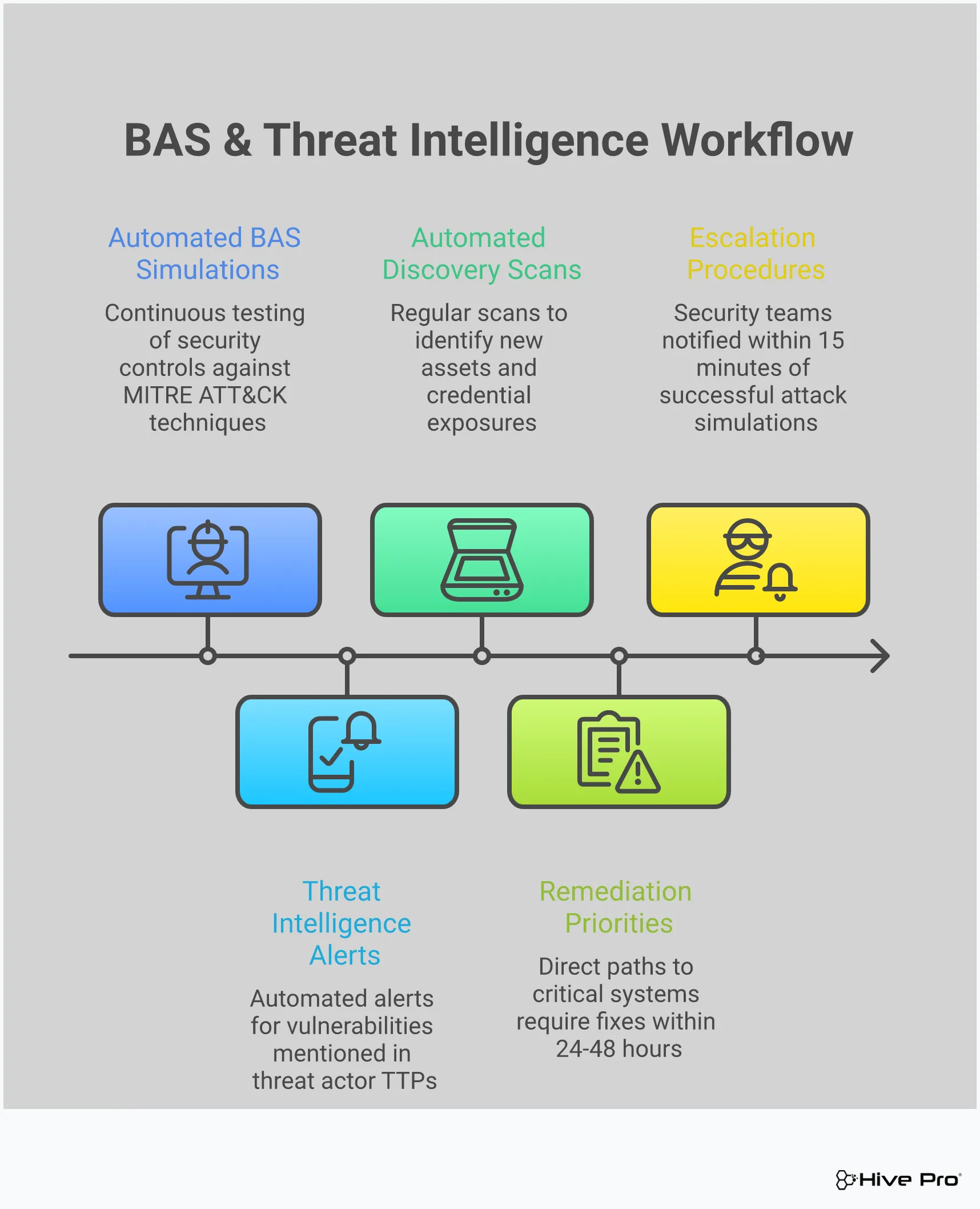
Hive Pro’s approach is all about creating a continuous, cyclical security process. The Uni5 Xposure Platform is designed to break the reactive, project-based habits of traditional vulnerability management. Instead of periodic scans and frantic patching, it fosters an ongoing loop of asset discovery, risk assessment, prioritization, and remediation. This unified platform ensures that exposure management becomes an integrated part of your daily operations, not just a task you perform once a quarter. By bringing everything into one place, Hive Pro helps you see the complete picture of your risk and focus your team’s efforts on the threats that pose a genuine danger to your business, turning security into a proactive, continuous cycle.
The Strobes Security Platform is built for comprehensive coverage, giving you visibility across your applications, cloud, infrastructure, and external-facing systems. Its real strength lies in how it prioritizes risk. Instead of just flagging every CVE, Strobes focuses on actual exploit activity and the potential business impact of a breach, so your team isn’t chasing down low-risk vulnerabilities. It also helps you validate these risks through methods like red teaming. For teams looking to streamline their response, Strobes makes it easier to resolve issues by tracking ownership and integrating directly with the tools your developers already use, like Jira, closing the loop between discovery and remediation.
XM Cyber takes an inside-out approach, focusing on how an attacker might move laterally within your network once they get past the perimeter. It’s particularly strong in analyzing internal systems and identities to map out potential attack paths. The platform uses advanced models to simulate how a threat actor could chain together different vulnerabilities, misconfigurations, and credential weaknesses to reach your critical assets. This method is incredibly effective for demonstrating real-world risk to stakeholders. By showing you the exact paths an attacker could take, XM Cyber helps you cut off those routes and fix the most critical choke points in your environment before they can be exploited.
If you’ve ever wondered whether your expensive security tools are configured correctly and actually working, Cymulate is the platform for you. It specializes in continuous security validation, essentially acting as an automated sparring partner for your defenses. Cymulate runs attack simulations to test the effectiveness of your controls, from firewalls and web application firewalls (WAFs) to endpoint protection. It provides concrete proof of risk by showing you exactly where and how your defenses failed a simulation. This gives you clear, actionable evidence to fine-tune your configurations, close gaps, and ensure your security stack is performing as expected when a real attack happens.
For organizations that are all-in on the cloud, Wiz provides deep visibility into the unique risks of public cloud environments. It excels at identifying complex issues like toxic combinations of misconfigurations, network exposure, secrets, and identity vulnerabilities that create attack paths. Wiz scans your entire cloud environment without agents, assessing risks that arise from cloud settings and the relationships between different resources. While it doesn’t actively test these configurations with attack simulations, it provides a comprehensive graph-based view of your cloud risk posture. This helps cloud security teams quickly identify and fix the most critical issues in their AWS, Azure, or GCP environments.
For organizations already invested in the Palo Alto Networks ecosystem, Cortex Xpanse offers a powerful way to manage external attack surface risks. The platform aggregates security information from various Palo Alto tools and external data sources to give you a unified view of your internet-facing assets and associated risks. It analyzes this data based on observed activity to identify potential exposures. While Cortex Xpanse provides extensive visibility and analysis, it’s important to note that it doesn’t actively test or simulate attacks against these risks. Its strength lies in consolidating data and providing insights for teams that rely heavily on the Palo Alto security stack.
Choosing an exposure management platform isn’t like picking a new laptop. Pricing is rarely listed on a website, and a demo can feel more like a sales pitch than a real look under the hood. The key is to move past the sticker price and focus on the value a platform delivers to your specific security program. What works for a massive global enterprise might be overkill for a mid-sized company, and vice-versa.
The right choice depends on your company’s setup, how your teams work together, and where your current security efforts usually get stuck. Are you drowning in alerts with no clear path to remediation? Or are you struggling to even see all your assets? Different platforms solve different core problems. As you compare your options, think less about which one has the longest feature list and more about which one directly addresses your team’s biggest headaches. This approach will help you find a partner, not just a product.
The first step in narrowing your options is deciding whether you need an enterprise-grade or a mid-market solution. Enterprise platforms are built for large, complex environments with dedicated security teams. They often offer deep customization, extensive reporting for compliance, and the ability to handle hundreds of thousands of assets. Mid-market solutions tend to be more streamlined, focusing on ease of use and faster time-to-value for teams that wear multiple hats.
Of course, this distinction comes with a price difference. For a medium-sized company, exposure management software can cost around a few hundred thousand dollars per year, while larger companies might pay more. Don’t let a big name or a massive feature set sway you if your team doesn’t have the resources to manage it. The goal is to find a tool that fits your operational reality.
True value comes from the features you’ll actually use. When you’re in a demo, it’s helpful to evaluate platforms on a few core capabilities: coverage, prioritization, proof, and workflow. Does the platform discover all your assets, from cloud to on-prem? How accurately does it prioritize vulnerabilities based on real-world threat intelligence? Can it prove a vulnerability is truly exploitable? And most importantly, how easily does it fit into your team’s existing workflow?
A platform that creates more work than it saves isn’t a good investment, no matter the cost. Look for tools that clarify who is responsible for fixing what so that nothing falls through the cracks. A platform with strong workflow automation can turn security findings into actionable tickets for the right teams, saving countless hours of manual coordination.
An exposure management platform should be the central hub of your security ecosystem, not another isolated silo. The tool should easily connect with your existing security systems, from scanners and endpoint detection tools to ticketing and patch management systems. Strong API support and pre-built integrations are non-negotiable, as they ensure all your security tools can work together seamlessly.
Think about your future needs, too. Will the platform scale as your company grows and your attack surface expands? Modern platforms often use AI to gather findings from different tools, group them intelligently, and route them to the correct teams. This automation is critical for managing a growing number of assets and alerts without overwhelming your team. A platform that can’t grow with you will quickly become a liability.
Investing in a new security platform always comes down to one question: Is it worth it? When we talk about the return on an exposure management platform, the answer isn’t just about preventing costly breaches. It’s about transforming how your security program operates. You’ll see tangible returns in the form of genuine security improvements, streamlined team operations, and a clear, measurable reduction in your overall risk. It’s about shifting security from a reactive cost center to a proactive, strategic part of the business. By focusing on what actually matters, you not only strengthen your defenses but also optimize the resources you already have. Let’s look at how this plays out in three key areas.
Traditional vulnerability scanners can generate a lot of noise, leaving you with a massive list of issues but no clear path forward. An exposure management platform changes the game by showing you what’s truly a threat. As one expert put it, “Just finding vulnerabilities isn’t enough. You need to know which ones are actually exploitable and how they impact your business.” This context is everything. Instead of chasing down every low-level CVE, your team can focus on fixing the critical exposures that attackers are actively targeting. This allows you to validate your security controls and measure progress in terms of actual risk reduction, not just patched vulnerabilities.
How much time does your team spend manually correlating data, chasing down asset owners, and debating who should fix what? An exposure management platform brings all that information into one place and automates the workflow. By clarifying who is responsible for fixing what, you ensure nothing falls through the cracks. This streamlined process has a huge impact; some companies have seen a 60% reduction in the time it takes to fix security issues. With a platform like Hive Pro Uni5 Xposure, you can automate remediation guidance and ticketing, freeing up your team to focus on strategic security work instead of administrative headaches.
Your environment is constantly changing, and so is the threat landscape. An exposure management platform gives you a continuous, up-to-date view of your risk. These tools help you find new digital assets and weak spots quickly, and most importantly, they help you prioritize which problems are most dangerous based on how likely they are to be exploited. This means you can track your risk reduction over time with clear metrics and reports. You can finally answer the tough questions from leadership with confidence, showing them exactly how security investments are making the organization safer and more resilient.
Picking a new security platform can feel overwhelming. With so many options on the market, it’s easy to get lost in feature comparisons and sales demos, each promising to be the ultimate solution. The key is to step back from the noise and focus on what your organization truly needs. The best exposure management platform isn’t the one with the longest feature list or the flashiest dashboard; it’s the one that fits seamlessly into your environment, supports your team’s current processes, and is ready to grow with you. It should feel like a natural extension of your team, not another complex tool that requires constant hand-holding.
Instead of jumping straight into product evaluations, start with an internal assessment. A clear understanding of your security maturity, integration needs, and future goals will give you a practical framework for making the right choice. Think of it as creating a blueprint for your ideal solution before you even look at what’s available. This approach helps you define your non-negotiables and nice-to-haves, allowing you to confidently select a platform that will become a cornerstone of your security program. The goal is to find a partner in risk reduction, not just another tool that gathers dust. A great platform should provide a unified view of cyber risks and help you focus on what matters most.
Before you can find the right solution, you need a clear picture of where your security program stands today. Are your teams stuck in a reactive cycle, constantly fighting fires? Or do you have proactive processes in place for identifying and managing vulnerabilities? Being honest about your current capabilities is the first step. Understanding your organization’s cyber risk posture helps you make informed decisions about where to invest your resources and what kind of support you need from a new platform. A team just starting to build a formal program will need different features—like guided workflows and clear reporting—than a mature team looking to optimize advanced threat hunting and automation.
A new platform should break down silos, not create new ones. Your exposure management solution will become the hub of your security operations, so it needs to play well with the tools you already use. For a platform to be effective, it must easily connect with your existing security systems—from threat detection and patch management to your ticketing and reporting tools—so everything works together. Before you schedule any demos, make a list of your essential integrations. This simple step ensures your new platform will streamline your workflows and provide a single source of truth for your entire team, saving you from the headache of manual data correlation and context switching between different applications.
The platform you choose today needs to meet your needs tomorrow. As your company expands, so will your attack surface. You’ll be adding new cloud environments, applications, and devices, and your exposure management tool has to keep up. The right platform needs to handle a growing amount of data and new digital assets without slowing down. Think about your company’s growth trajectory and the evolving threat landscape. Investing in a scalable solution not only safeguards your current assets but also prepares your organization for future challenges and ensures your security program can adapt and grow without needing a complete overhaul in a few years.
Choosing the right exposure management platform is a significant decision, and with so many options on the market, it’s easy to get lost in feature lists and marketing promises. To help you cut through the noise, I’ve put together a practical checklist. Think of these as the non-negotiables—the core capabilities a platform must have to truly help you move from a reactive to a proactive security posture. Use these points to guide your demos and discussions, ensuring you pick a partner that delivers real results.
You can’t protect what you can’t see. This might sound like a cliché, but in today’s sprawling digital estates, it’s the absolute truth. Your first checkpoint should be confirming the platform’s ability to see everything. A top-tier solution must scan all your digital assets, “whether they are in the cloud, on your own servers, or temporary software containers.” Ask potential vendors how they handle dynamic assets like cloud instances and containers. If a platform can’t provide a complete, continuously updated inventory of your entire attack surface, you’ll always be working with blind spots.
A long list of vulnerabilities is just noise. What your team needs is a clear, actionable signal. The right platform moves beyond simple CVSS scores and helps you focus on what matters most. As one expert puts it, “The tool should be able to tell you which problems are most urgent based on how dangerous they are and how likely they are to be exploited.” This requires a sophisticated approach that layers business context over threat intelligence. Look for a platform that can prioritize exposure by showing you which vulnerabilities are actively being targeted by threat actors and have a direct path to your critical assets.
Don’t just take the platform’s word for it—make it prove the risk is real. Many tools can show you potential problems, but the best ones validate them. “Platforms that only show you problems don’t solve these issues. The best platforms assess risks, prove they are real before you act.” This is where capabilities like Breach and Attack Simulation (BAS) come in. By safely simulating real-world attack paths, the platform can confirm whether a vulnerability is truly exploitable in your environment. This proof eliminates false positives and gives your team the confidence to act decisively, focusing their limited time on genuine threats.
A powerful tool that’s difficult to use will quickly become shelfware. The ultimate goal is to “simplify and speed up ‘exposure management,’ which means reducing a company’s risk to cyber threats.” Pay close attention to the user interface during demos. Is it intuitive? Can your team easily build reports and dashboards that make sense for different stakeholders? Evaluate how well the platform integrates with your existing ecosystem, such as ticketing systems and SIEMs. A solution that streamlines remediation workflows and fosters collaboration between security and IT teams is one that will actually get used and deliver value.
Rolling out any new security platform is a big undertaking, and an exposure management solution is no different. It represents a fundamental shift in how your organization approaches security—moving from putting out fires to preventing them. While the long-term benefits are huge, it’s smart to anticipate a few common hurdles along the way. Getting ahead of these challenges will make the transition smoother for everyone involved and ensure you get the most value from your investment right from the start.
It’s a familiar story: you’re excited to implement a new proactive security program, but then a zero-day vulnerability drops, and everyone is pulled into emergency meetings. Suddenly, your strategic project is on the back burner. The key to avoiding this is to frame the implementation not as just another project, but as the solution to this chaotic cycle. A proactive cybersecurity exposure management program can improve your understanding of your organization’s risk posture, helping you make smarter decisions about where to invest time and resources. By connecting the platform’s implementation to clear business goals, like protecting critical assets or ensuring uptime, you can secure the executive buy-in needed to keep it a top priority, even when the next “emergency” hits.
Once the initial implementation is complete, the real work begins: continuous remediation. It’s easy for teams to lose steam when faced with a seemingly endless list of vulnerabilities. This isn’t a task for one person or even one team. To keep the momentum going, you need to build a culture of shared responsibility. As experts at Bitsight suggest, it’s wise to “create a cyber exposure response team” that includes members from security, IT operations, and development. This cross-functional group can meet regularly to review progress, tackle roadblocks, and celebrate wins. By making remediation a collaborative effort with clear owners, you turn it from a daunting chore into a manageable, ongoing process.
Your security team is already busy. The last thing they need is another tool that creates more alerts and administrative work. It’s crucial to position your exposure management platform as a tool that reduces their workload, not adds to it. The right platform achieves this by automating discovery, correlating threat intelligence, and prioritizing the handful of vulnerabilities that pose a genuine risk. This focus frees your team from chasing down low-impact issues. Furthermore, by continuously monitoring your environment, an exposure management platform helps ensure you meet compliance with industry regulations like GDPR and HIPAA, streamlining audit preparation and reducing manual effort.
When a critical vulnerability is found on a server, who is responsible for patching it? Is it the security team, the IT infrastructure team, or the DevOps team that deployed the application? Ambiguity leads to inaction. Before you even go live with the platform, you need to define clear roles and responsibilities for the entire remediation lifecycle. To get the most value from your program, you should tie exposure management to specific business objectives, which helps everyone understand why their role is critical. Create a simple RACI (Responsible, Accountable, Consulted, Informed) chart for different types of vulnerabilities and establish clear Service Level Agreements (SLAs) for remediation. This ensures that when the platform flags a critical risk, everyone knows exactly who needs to act and by when.
Adopting a new platform is more than just a technical switch. To truly get ahead of threats, you need to build solid processes and get your team on board. Think of it as laying the foundation for a stronger, more proactive security posture. A successful implementation isn’t just about flipping a switch; it’s about creating a sustainable program that evolves with your organization. Here’s how to set yourself up for success from day one.
First things first, connect your exposure management program to clear business goals. Are you trying to reduce the risk of a specific type of data breach? Or maybe you need to improve compliance with industry regulations? Defining these objectives helps you measure success and get buy-in from leadership. Exposure management isn’t a one-time project; it’s a continuous cycle. You should aim to create an ongoing loop of asset discovery, risk assessment, and remediation. A unified platform like Uni5 Xposure can help you maintain this constant rhythm, ensuring you’re always adapting to new threats and changes in your environment.
Cybersecurity is a team sport, and managing exposure is definitely not a job for one person or even just the security team. Bring together a cross-functional response team with members from IT, DevOps, and even business units. When everyone understands their role, remediation happens faster and more effectively. This also means making security a shared responsibility across the company. Regular training on cybersecurity best practices is key. When you empower everyone to spot suspicious activity and handle data securely, you strengthen your defenses from the inside out and build a more resilient security culture.
Your exposure management platform is the engine, but you need a process to keep it running smoothly. This means establishing a cycle of continuous monitoring and improvement. By constantly scanning for new vulnerabilities and ensuring your security controls are working as expected, you can maintain compliance and adapt to the threat landscape. This ongoing process does more than just protect your assets; it deepens your understanding of your organization’s overall cyber risk posture. Using a solution that provides continuous vulnerability and threat prioritization ensures your team is always focused on what matters most, making steady, measurable progress in reducing risk.
Isn’t exposure management just a new name for vulnerability management? Not at all. Think of it this way: traditional vulnerability management gives you a long list of problems, like all the unlocked windows in a building. Exposure management shows you which of those unlocked windows an actual burglar would use to get to the valuables. It connects the dots between a technical flaw, real-world threats, and your most critical assets to give you a prioritized, risk-based view instead of just an overwhelming to-do list.
My team is already swamped with alerts. Won’t this just add more noise? Actually, the goal is the exact opposite. A good exposure management platform is designed to cut through the noise, not add to it. By combining threat intelligence with an understanding of your specific environment, it helps you focus on the handful of vulnerabilities that pose a genuine, immediate threat. It helps your team stop chasing down thousands of low-risk alerts and instead directs their energy toward fixing the few critical issues that could actually lead to a breach.
How is Breach and Attack Simulation (BAS) different from a regular penetration test? A penetration test is like hiring a team to try and break into your office once a year. It’s a valuable, point-in-time assessment. Breach and Attack Simulation, on the other hand, is like having an automated security guard who is constantly and safely testing all your doors and windows, 24/7. BAS continuously runs safe, simulated attacks to validate that your security controls are working as expected, giving you a real-time picture of your defenses rather than an annual snapshot.
Do I have to rip and replace my current security tools to implement an exposure management platform? Definitely not. A strong exposure management platform should act as the central hub that integrates with the tools you already have. It’s designed to pull in data from your existing vulnerability scanners, endpoint agents, and cloud security tools to create a single, unified view of your risk. The platform enhances your current investments by adding the crucial layers of prioritization and context that are often missing.
What’s the single most important thing to look for when choosing a platform? Look for a platform that can provide proof. Many tools can show you a long list of potential problems, but the best ones can validate which of those problems are truly exploitable in your environment. Features like Breach and Attack Simulation provide concrete evidence of risk, which eliminates guesswork and helps you justify remediation efforts. A platform that can prove a threat is real is one that will help you make confident, data-driven security decisions.