
CISO Guide: Building a Business Case for CTEM
A step-by-step guide for CISOs to build a board-ready business case for CTEM: ROI metrics, CFO-friendly language, and objection-handling strategies.

A step-by-step guide for CISOs to build a board-ready business case for CTEM: ROI metrics, CFO-friendly language, and objection-handling strategies.
For a detailed CISA’s KEV Catalog, download the pdf file here Summary The Known Exploited Vulnerability (KEV) catalog, maintained by CISA,...
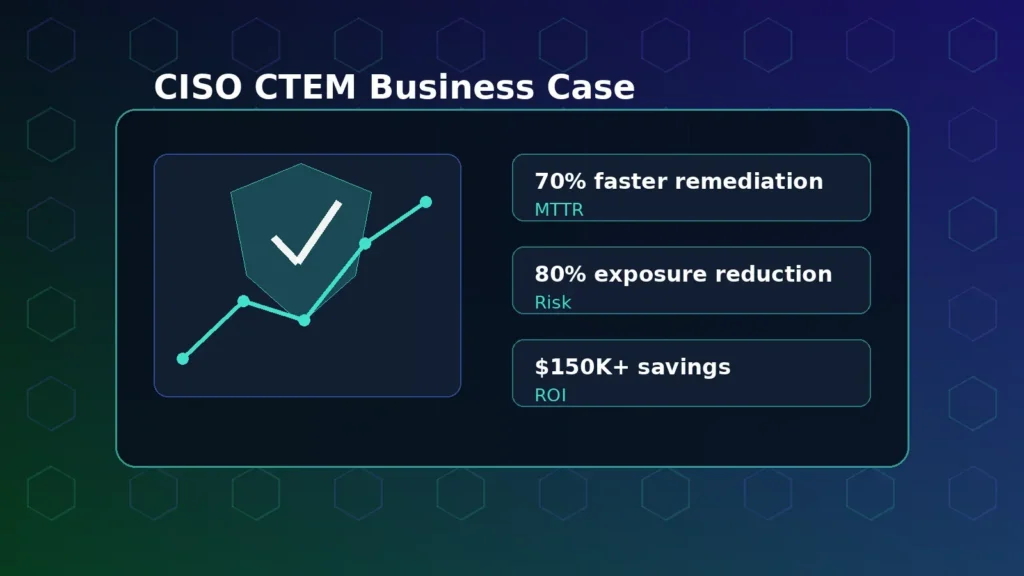
Build a board-ready CTEM business case with risk, remediation, productivity, and cost metrics CISOs can defend.
For a detailed threat digest, download the pdf file here April reshaped the cybersecurity landscape with active exploitation of 15...
Explore the top OT cybersecurity and ICS security challenges in 2026, from legacy assets to remote access, ransomware, and exposure...
Learn common cyber insurance cybersecurity requirements and how CTEM helps prove risk reduction, vulnerability management, and control readiness.
From the Trenches This is the conversation I have with VM leads every week. It usually starts at minute thirty...
Stay informed with HiveForce Labs as they provide comprehensive insights into the latest vulnerabilities, threats, and threat actor activities.
Subscribe below to receive in-depth weekly and monthly updates, along with daily and weekly advisories designed to help you proactively manage and mitigate cybersecurity risks.
Subscribe Here