Comprehensive Threat Exposure Management Platform
For a detailed threat digest, download the pdf file here
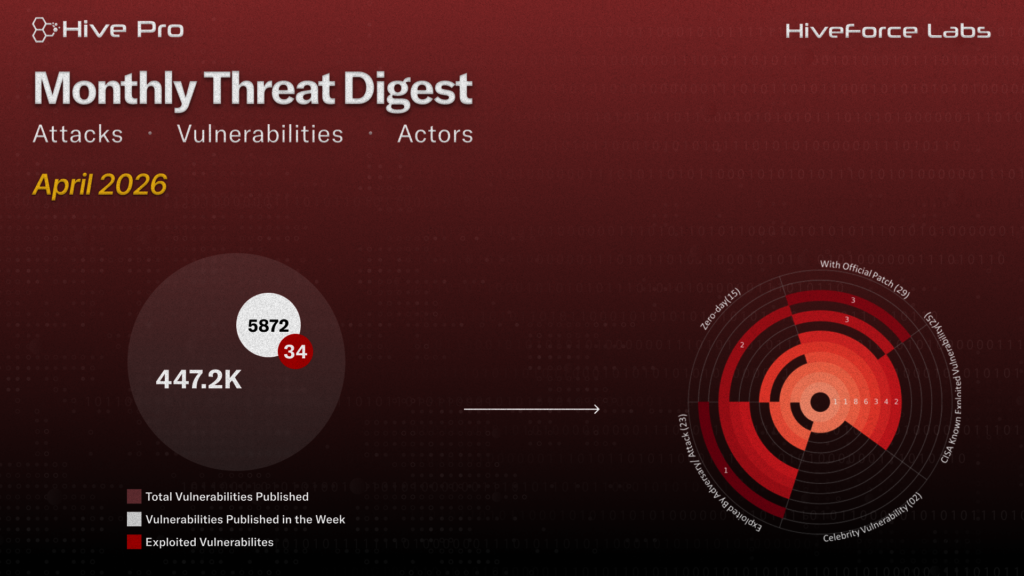
April reshaped the cybersecurity landscape with active exploitation of 15 zero-days. Google pushed out emergency patches for CVE-2026-5281, a Chrome zero-day already under active exploitation, stemming from a use-after-free flaw in the WebGPU-based Dawn component. The vulnerability allows attackers to manipulate memory and execute arbitrary code, making immediate patching non-negotiable.
Meanwhile, Handala Hack Team Iran-affiliated threat group launched a destructive campaign against GCC critical infrastructure, allegedly wiping 6 PB of data and exfiltrating 149 TB of classified documents via compromised VPN credentials, infostealer-harvested accounts, and targeted phishing.
Scattered LAPSUS$ Hunters (SLH) are scaling cloud-focused data theft and extortion by exploiting trusted SaaS integrations, moving laterally across platforms, and pressuring victims through data leaks, DDoS attacks, and targeted harassment, often blurring attribution as impersonators mimic well-known cybercrime brands.
Finally, the rebranded VECT 2.0 ransomware group is rapidly expanding its RaaS ecosystem with a purpose-built C++ framework designed for efficiency and impact. Alongside this, Operation TrustTrap is leveraging a vast phishing infrastructure of over 16,800 domains, cleverly mimicking government services across multiple countries by manipulating subdomains and trusted naming patterns to evade detection. With these increasing risks, strengthening defensive measures is more critical than ever in today’s digital landscape.
Subscribe to receive our weekly threat digests and alerts directly in your inbox.