Comprehensive Threat Exposure Management Platform
 Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the Report
Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the ReportFor a detailed threat digest, download the PDF file here
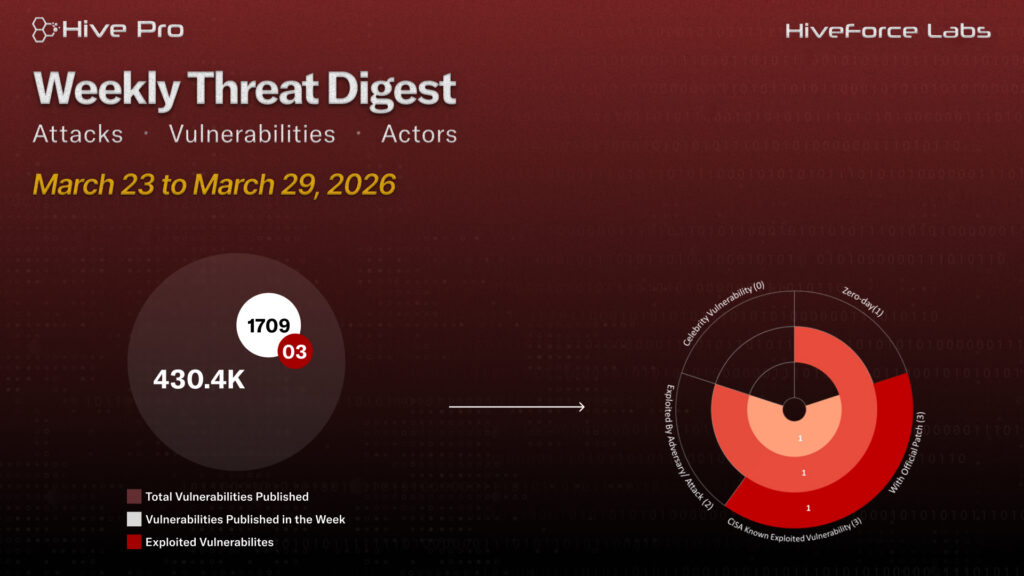
HiveForce Labs has recently made significant advancements in identifying cybersecurity threats. Over the past week, eleven major attacks were detected, three critical vulnerabilities were actively exploited, and four threat actors were closely monitored, reflecting an alarming escalation in malicious activities.
CVE-2026-33017 Critical unauthenticated RCE in Langflow, the open-source AI agent and RAG pipeline framework. A single HTTP POST with a JSON payload grants full server privileges, no auth, no chaining required. TeamPCP Automated supply chain threat group compromising tools like Trivy and LiteLLM to steal credentials and inject malicious code across GitHub, PyPI, npm, and container registries via CI/CD pipelines.
Meanwhile, MuddyWater Iranian MOIS-linked APT active since 2017, targeting critical sectors via spear-phishing and multi-language malware. Recent campaigns deploy Dindoor, Fakeset backdoors with cloud exfiltration and Telegram C2, showing AI-assisted development. MOIS Telegram C2 Campaign Iranian state actors target dissidents, journalists, and critical sectors globally via social engineering delivering multi-stage malware for surveillance, data theft, and hack-and-leak operations. These rising threats pose significant and immediate dangers to users worldwide.
Subscribe to receive our weekly threat digests and alerts directly in your inbox.