Comprehensive Threat Exposure Management Platform
 Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the Report
Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the ReportFor a detailed threat digest, download the PDF file here
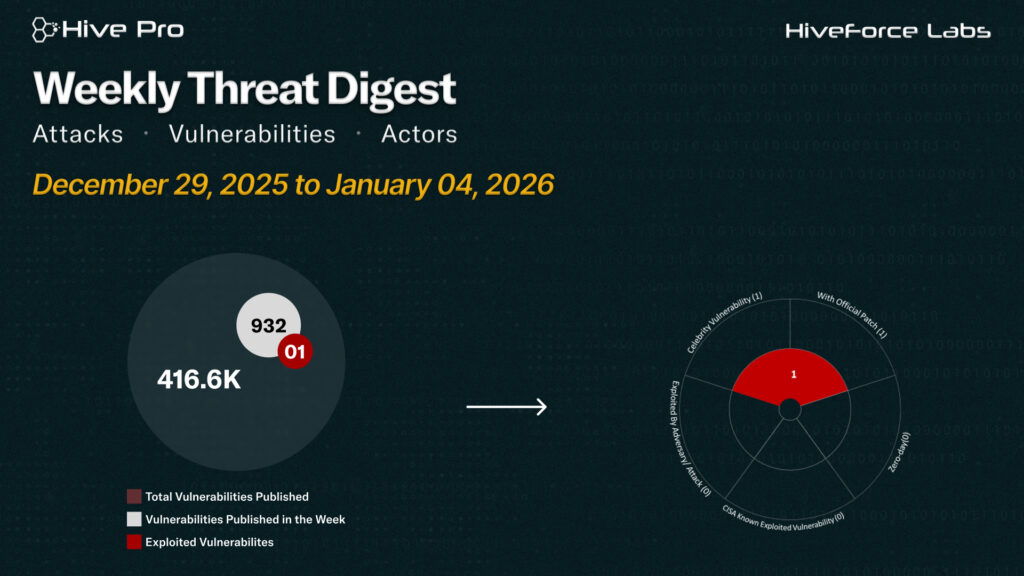
HiveForce Labs has recently made significant advancements in identifying cybersecurity threats. Over the past week, four major attacks were detected, one critical celebrity vulnerability was actively exploited, and two threat actor were closely monitored, reflecting an alarming escalation in malicious activities.
GlassWorm has emerged as a self-propagating malware campaign abusing VS Code extensions to target developers. It hides malicious code using invisible Unicode characters and primarily affects macOS systems. The malware steals credentials and cryptocurrency wallets, with C2 traffic routed through the Solana blockchain. This campaign underscores growing risks to developer environments.
Meanwhile, China-aligned APT activity remains persistent and adaptive. Silver Fox exploited tax-season lures to deploy ValleyRAT via fake Indian tax notices, targeting enterprise and healthcare sectors. Evasive Panda sustained a multi-year AitM campaign delivering MgBot through DNS poisoning and fake updates. Additionally, the critical LangGrinch (CVE-2025-68664) flaw in LangChain exposes AI applications to data theft and potential RCE. These rising threats pose significant and immediate dangers to users worldwide.
Subscribe to receive our weekly threat digests and alerts directly in your inbox.