Comprehensive Threat Exposure Management Platform
 Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the Report
Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the ReportFor a detailed threat digest, download the PDF file here
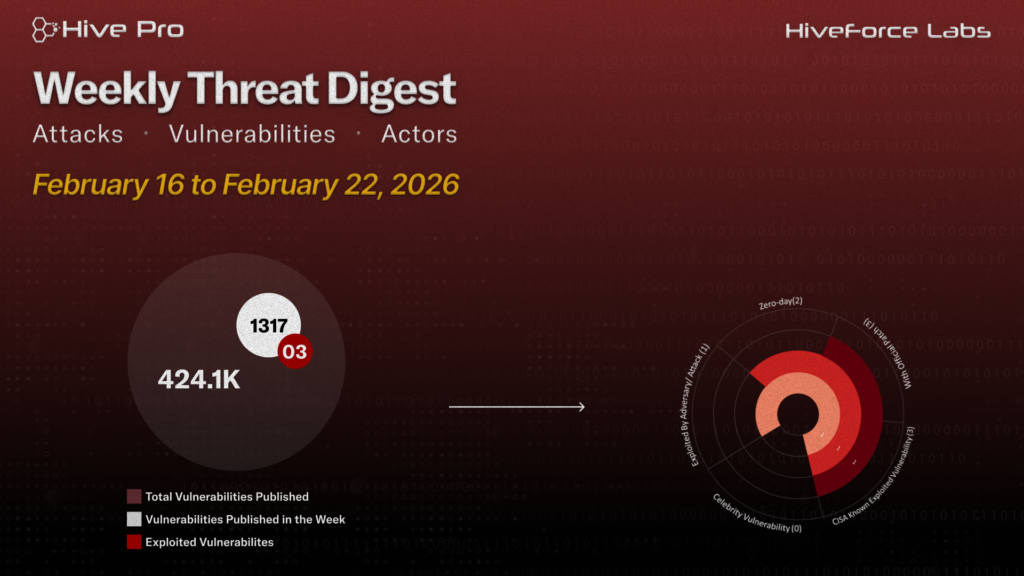
HiveForce Labs has recently made significant advancements in identifying cybersecurity threats. Over the past week, thirteen major attacks were detected, three critical vulnerabilities were actively exploited, and two threat actors were closely monitored, reflecting an alarming escalation in malicious activities.
CVE-2026-1731 is being actively exploited to achieve unauthenticated RCE against BeyondTrust appliances, posing a critical risk of full remote compromise to exposed, unpatched systems. CVE-2026-2441 is an actively exploited use-after-free flaw in the Chromium CSS engine, allowing drive-by remote code execution via a malicious webpage, immediate browser updates are critical to mitigate risk.
Meanwhile, A ClickFix campaign is deploying Matanbuchus 3.0 to deliver AstarionRAT, enabling stealthy initial access with encrypted C2, credential theft, and proxy capabilities, reinforcing the growing commercialization and sophistication of MaaS-driven intrusions. UNC6201 exploited CVE-2026-22769 to gain unauthenticated root access to infrastructure appliances, deploying advanced backdoors and maintaining long-term stealthy persistence aligned with PRC intelligence objectives. These rising threats pose significant and immediate dangers to users worldwide.
Subscribe to receive our weekly threat digests and alerts directly in your inbox.