Comprehensive Threat Exposure Management Platform
 Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the Report
Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the ReportFor a detailed threat digest, download the PDF file here
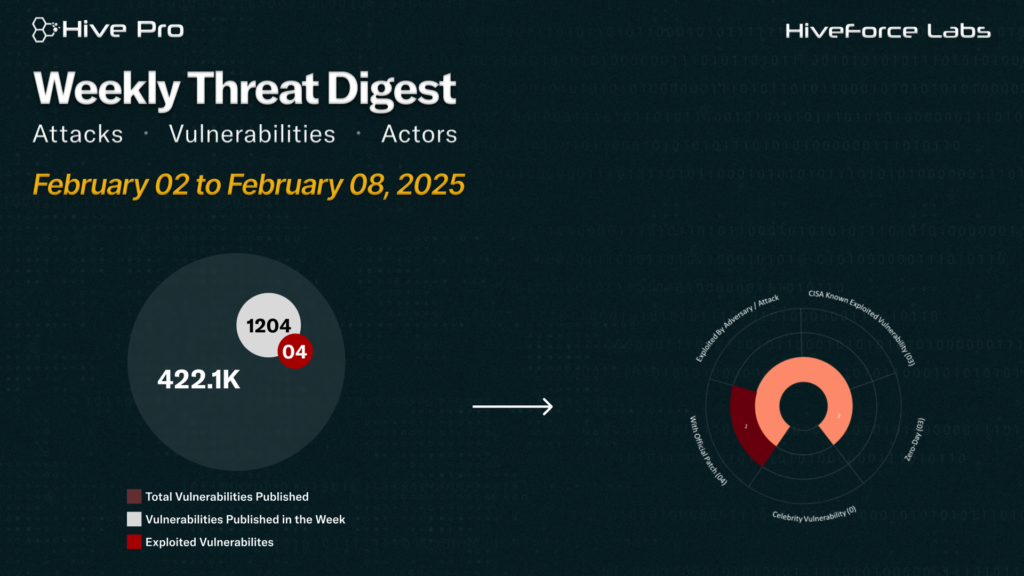
HiveForce Labs has reported a sharp rise in cybersecurity threats, highlighting the increasing complexity and frequency of global cyber incidents. Over the past week, eleven major attacks were detected, four critical vulnerabilities were publicly disclosed, and five active threat actor groups were monitored, signaling a concerning escalation in malicious activity.
CVE-2026-25253 is a high-risk remote code execution vulnerability in the open-source AI agent OpenClaw (Clawdbot/Moltbot). This “1-click” attack can leak authentication tokens and hijack WebSocket connections, giving attackers the ability to execute arbitrary commands on the victim’s local machine.
In a separate attack, the Chinese state-sponsored APT group Lotus Blossom launched a sophisticated supply chain attack, compromising Notepad++ infrastructure to deploy a previously unknown backdoor, Chrysalis. Additionally, threat actors targeted the Open VSX Registry in a supply chain attack, hijacking a legitimate developer account (oorzc) to distribute GlassWorm malware via malicious updates. These updates were embedded in four trusted VS Code extensions, impacting over 22,000 users.
Finally, APT28‘s Operation Neusploit signals a renewed wave of cyber-espionage activity across Central and Eastern Europe. These underscore the need for disciplined security updates and sustained monitoring in response to rapidly evolving attack methodologies.
Subscribe to receive our weekly threat digests and alerts directly in your inbox.