Comprehensive Threat Exposure Management Platform
 Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the Report
Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the ReportMost security teams are great at finding problems. The real challenge is figuring out which problems to solve first. When everything is a priority, nothing is. This is a common frustration that leaves teams feeling overworked and unsure if their efforts are making a real difference. A more strategic method is required to align security work with business protection. This brings us to the question, what is CTEM? Continuous Threat Exposure Management is a framework that helps you prioritize security efforts based on actual risk. It combines vulnerability data with real-world threat intelligence and business context, so you can focus on fixing the exposures that could cause the most damage to your organization. It’s about making smarter, data-driven decisions.
If you feel like your team is constantly playing catch-up with security threats, you’re not alone. Traditional approaches often leave teams reacting to alerts and patching vulnerabilities only after they’ve become a problem. This is where Continuous Threat Exposure Management, or CTEM, comes in. It’s a strategic shift in how we approach cybersecurity, moving from a defensive crouch to a proactive stance. Instead of just managing individual vulnerabilities, CTEM provides a comprehensive, ongoing program to understand and reduce your organization’s entire threat exposure. It’s about seeing your security posture through an attacker’s eyes and fixing the most critical issues before they can be exploited. This approach helps you align security efforts with business goals, ensuring you’re protecting what matters most.
At its core, Continuous Threat Exposure Management is a proactive, five-stage framework designed to continuously identify, evaluate, and remediate security risks across all your digital and physical assets. Think of it as a planned, ongoing way to find, check, rank, and fix security weaknesses across your entire IT environment. It’s a new way to handle cybersecurity that helps companies regularly check their risks, see where they are exposed, and decide which security problems to fix first. By implementing a CTEM platform, you can bring all this information together, giving you a unified view of your risk landscape instead of trying to piece it together from dozens of different tools.
The biggest change CTEM brings is the move from reactive to proactive security. For years, many security teams have been stuck in a cycle of scanning, finding thousands of vulnerabilities, and then struggling to figure out which ones to patch first. Instead of just reacting to security problems after they pop up, CTEM helps organizations actively reduce risks by understanding real threats and what matters most to the business. It’s a continuous loop that constantly looks for and addresses security exposures, moving organizations from a state of reaction to one of proactive resilience. This allows you to focus your team’s valuable time and resources on the threats that pose a genuine danger, guided by a clear strategy for vulnerability and threat prioritization.
For years, vulnerability management has been the bedrock of many security programs. The cycle is familiar: run a scan, get a long list of vulnerabilities ranked by a CVSS score, and hand that list over to IT to patch. While this approach was a solid starting point, it’s no longer enough to keep up with today’s complex IT environments and sophisticated attackers. The digital landscape has expanded far beyond traditional servers and endpoints, and security teams are drowning in alerts with little context to guide them.
This is where Continuous Threat Exposure Management (CTEM) marks a fundamental shift. It’s not just a new name for the same old process; it’s a strategic evolution that moves security from a reactive, checklist-based function to a proactive, business-aligned operation. Instead of just finding vulnerabilities, CTEM focuses on understanding and reducing actual exposure. It answers the critical questions that traditional methods often miss: What are our most critical assets? How could an attacker reach them? And which threats should we fix right now to have the biggest impact on our security posture? This change in perspective helps teams break free from the endless cycle of scanning and patching to focus on what truly matters.
Traditional vulnerability management programs are often laser-focused on finding known software vulnerabilities—the CVEs that pop up on servers, laptops, and applications. While important, this view is dangerously narrow. Attackers don’t limit themselves to software flaws, and neither should your defenses. A CTEM program broadens the aperture to cover your total attack surface.
This means looking at all the potential weaknesses an attacker could exploit. CTEM assesses exposures across your entire IT ecosystem, including cloud misconfigurations, weak or exposed credentials in identity systems, and vulnerabilities in operational technology (OT) and IoT devices. It’s about seeing your organization through an attacker’s eyes, identifying not just single vulnerabilities but the interconnected pathways they could use to reach your most critical assets.
Many organizations still operate on a schedule of quarterly or monthly vulnerability scans. The problem with this model is that it creates significant blind spots. A new, critical vulnerability could be discovered the day after your scan, leaving you exposed for weeks or months without even knowing it. In a dynamic cloud environment where assets are constantly being created and decommissioned, periodic scans become outdated almost as soon as they’re finished.
CTEM replaces this static, point-in-time snapshot with a continuous, automated loop of discovery and assessment. It’s designed to provide a real-time view of your exposure as your environment changes. This continuous approach ensures you can identify and address new risks as they emerge, not just when the next scan is scheduled. By using a unified platform, you can maintain constant visibility and actively reduce your risk instead of just documenting it after the fact.
One of the biggest challenges in traditional vulnerability management is the overwhelming volume of alerts. When everything is labeled “critical,” it’s hard to know where to start. Most programs rely heavily on the Common Vulnerability Scoring System (CVSS), but a high CVSS score doesn’t always translate to high business risk. A “critical” vulnerability on a non-essential, isolated test server is far less urgent than a “medium” one on your primary payment database.
CTEM revolutionizes vulnerability and threat prioritization by adding crucial context. It combines vulnerability data with real-world threat intelligence and an understanding of your business. It focuses on how a security problem could actually impact your operations by asking key questions: Is this vulnerability being actively exploited by threat actors? Is it located on a business-critical asset? Does it lie on a known attack path? This intelligence-driven approach helps you cut through the noise and direct your team’s efforts to the few exposures that pose a genuine threat.
A successful CTEM program follows a continuous, five-stage cycle. Think of it not as a linear checklist, but as a loop that constantly refines your security posture. Each stage builds on the last, creating a system that helps you move from simply managing vulnerabilities to proactively reducing your overall threat exposure. This framework gives your team a repeatable process for identifying, prioritizing, and fixing the security gaps that matter most.
Before you can protect your assets, you need to know what you’re protecting. Scoping is the foundational step where you identify your most critical systems and data. You can’t defend everything with the same level of intensity, so this stage is all about focus. By defining which parts of your digital footprint are most vital to your business operations, you ensure your security efforts are concentrated where they can have the greatest impact. This isn’t just about servers and endpoints; it includes cloud services, applications, and all the digital assets that are essential for your organization to function. A clear scope prevents your team from getting overwhelmed and sets the stage for a more manageable and effective attack surface management strategy.
Once you’ve defined your scope, the next step is discovery. This is where you continuously scan your critical systems to find every potential risk, vulnerability, and misconfiguration. The key word here is continuously. Your environment is always changing—new assets are added, and new threats emerge daily. A one-time scan is just a snapshot, but a continuous discovery process ensures you have an up-to-date inventory of your exposures. This stage goes beyond just finding known software vulnerabilities; it’s about uncovering the full range of weaknesses across your entire scoped environment, from insecure configurations in the cloud to overlooked shadow IT assets. This comprehensive view is essential for understanding your true security posture.
Discovery will likely uncover thousands of vulnerabilities, and your team can’t fix them all at once. Prioritization is how you decide what to tackle first. Instead of relying solely on generic CVSS scores, a CTEM approach uses real-world threat intelligence to assess which vulnerabilities pose the most immediate danger. This means focusing on issues that are actively being exploited by attackers in the wild. By combining threat data with the business context you established during the scoping phase, you can create a vulnerability & threat prioritization queue that directs your team’s efforts toward the risks that truly matter. This intelligence-driven approach helps you fix the most impactful problems first.
Just because a vulnerability exists doesn’t automatically mean it’s exploitable in your specific environment. The validation stage is about confirming which exposures present a genuine, practical risk. This is often done through techniques like Breach and Attack Simulation (BAS), which safely simulates attacker methods to see if your security controls hold up. Validation helps answer critical questions: Can an attacker actually leverage this weakness? Are our existing defenses working as expected? By performing adversarial exposure validation, you can confirm which vulnerabilities are truly urgent and avoid wasting valuable time and resources fixing issues that pose little to no real-world threat to your organization.
The final stage, mobilization, is where insight turns into action. This is about connecting the validated, high-priority vulnerabilities to your operational teams and processes to ensure they get fixed. It’s not enough to just send a report; mobilization involves creating clear lines of accountability, integrating with ticketing and workflow systems, and tracking remediation progress from start to finish. This stage closes the loop on the CTEM cycle by ensuring that identified risks are not just known but are actively being addressed. A strong mobilization process makes remediation more efficient and confirms that your security efforts are leading to a tangible reduction in risk across your entire exposure management platform.
If your CTEM program is the engine driving your proactive security, then threat intelligence is the high-octane fuel that makes it run. Without it, you’re just staring at a massive list of potential vulnerabilities, with no real way to know which ones pose an immediate danger. It’s the difference between knowing a window in your house is unlocked and knowing a burglar is on your street, actively checking for unlocked windows. One is a fact; the other is a threat that demands immediate action.
Threat intelligence provides the real-world context you need to make smart, timely decisions. It helps you see your organization through an attacker’s eyes, revealing which of your exposures are the most attractive targets. By integrating live data on what attackers are doing right now, you can move beyond a simple checklist of vulnerabilities. Instead, you can build a dynamic, risk-informed strategy that focuses your team’s limited time and resources on the issues that truly matter. This is how you shift from a reactive cycle of patching and praying to a confident, proactive security posture.
A strong CTEM strategy relies on a constant stream of high-quality, real-world threat data. This isn’t just about pulling in public CVE information. It’s about integrating intelligence from multiple sources to get a complete picture of the threat landscape. This includes insights from dedicated security research teams, malware analysis, dark web monitoring, and global honeypot networks. This live feed of information gives you a direct view into current attacker tactics, techniques, and procedures. By understanding which vulnerabilities are being weaponized and how, you can anticipate an attacker’s next move instead of just reacting to it. This is where a dedicated intelligence team like HiveForce Labs becomes invaluable, providing the curated data needed to power your security decisions.
Security teams are often overwhelmed by the sheer volume of vulnerabilities. It’s impossible to patch everything, and frankly, you don’t need to. Many vulnerabilities are theoretical or too complex for most attackers to exploit. Threat intelligence helps you cut through that noise by highlighting the specific exposures that are being actively exploited in the wild. This allows you to focus on the clear and present dangers to your organization. Instead of working through an endless backlog, your team can prioritize the handful of vulnerabilities that have known exploits and are being used in current attack campaigns. This targeted approach, often detailed in threat advisories, ensures your remediation efforts have the greatest possible impact on reducing your actual risk.
The ultimate goal is to connect external threat data with your internal business context. It’s not enough to know a vulnerability is being exploited; you need to know if it affects your most critical assets. A mature CTEM program helps you map active threats to your specific environment, showing you the potential attack paths to your crown jewels. This is what true vulnerability and threat prioritization looks like. By understanding which combination of exposures creates a direct line to your sensitive data or critical systems, you can prioritize remediation based on genuine business risk, not just a technical severity score. This intelligence-driven approach ensures you’re always working on the right things at the right time.
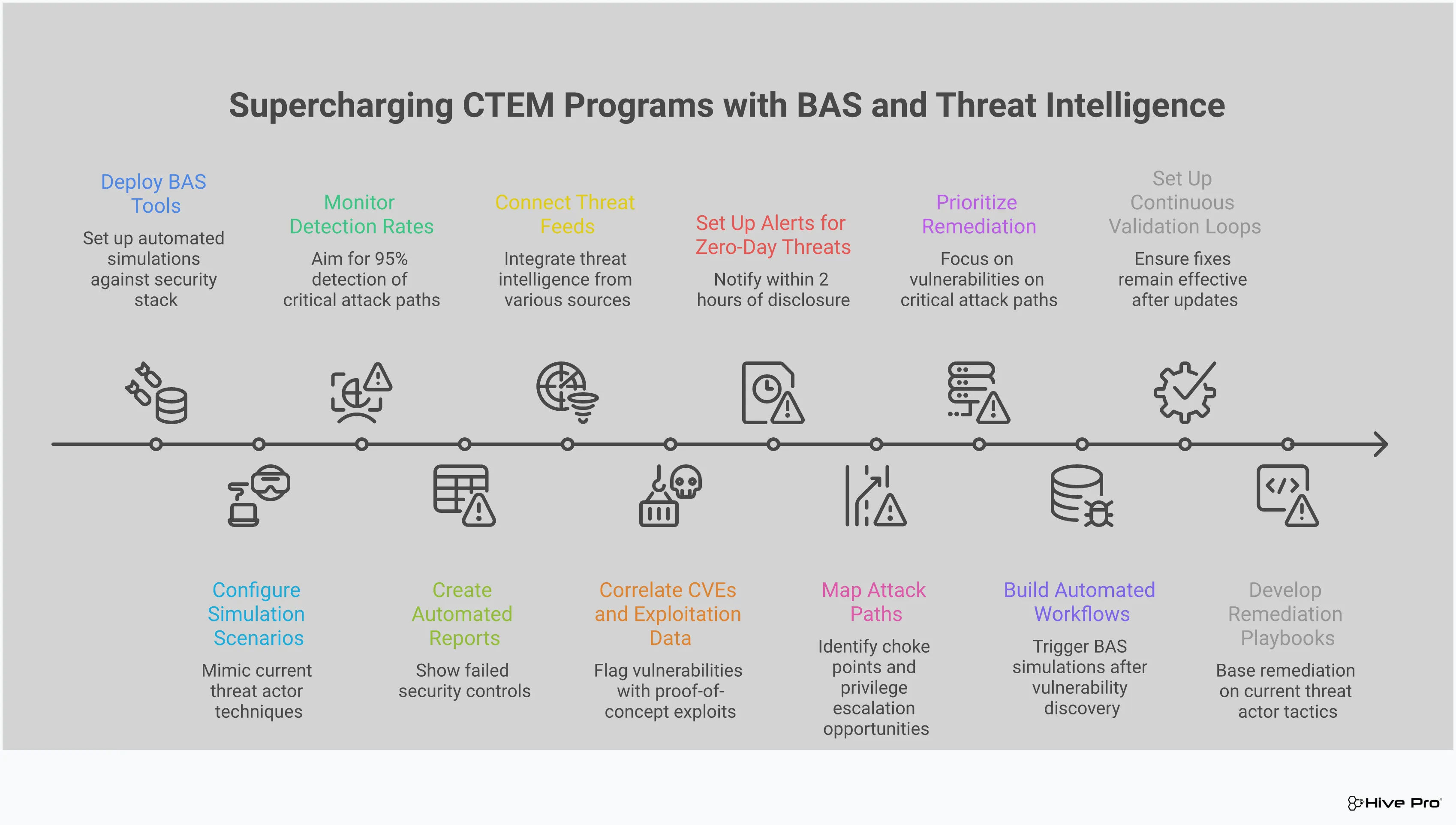
After you’ve scoped your attack surface, discovered your assets, and prioritized your vulnerabilities, it’s time to validate your findings. This is where Breach and Attack Simulation (BAS) becomes a game-changer within the CTEM framework. Think of it as a sparring partner for your security infrastructure. Instead of just assuming your security controls will work during a real attack, BAS lets you safely and continuously test them against the latest threats and attack techniques.
This proactive testing answers critical questions: Is that firewall rule configured correctly? Will our EDR solution actually detect and block this specific type of malware? By simulating real-world attack scenarios in a controlled way, BAS moves you from a theoretical understanding of your security posture to a practical, evidence-based one. It helps you find and fix the gaps in your defenses before an attacker can exploit them. This makes it an essential part of a mature threat exposure management program, transforming your security validation from a periodic, manual exercise into an automated, continuous process. It’s about replacing assumptions with certainty and ensuring your security investments are delivering the protection you expect.
Your security stack is made up of many layers, from firewalls and web application firewalls (WAFs) to endpoint detection and response (EDR) tools. But how do you know they’re all working together as intended? BAS provides the answer by running automated, simulated attacks that mimic the behavior of real adversaries. This process of adversarial exposure validation tests whether your security tools will actually detect, alert, and block malicious activity. It’s like running a fire drill; you get to see how your team and tools respond under pressure without the danger of a real fire. This gives you concrete proof of your security effectiveness and highlights misconfigurations or gaps that need immediate attention.
Finding a vulnerability is one thing; fixing it effectively is another. Sometimes, a patch can have unintended consequences or a new firewall rule might not fully block the intended threat. BAS allows you to test your remediation plans in a safe environment before pushing them to production. You can run a simulation to confirm a vulnerability, apply your proposed fix in a test environment, and then run the same simulation again. If the attack is now blocked, you can deploy the fix with confidence, knowing it works as expected. This “measure twice, cut once” approach saves time, reduces risk, and ensures your remediation efforts are truly effective.
Your IT environment is constantly changing. New assets are added, software is updated, and configurations are modified. At the same time, attackers are always developing new techniques. A one-time security assessment quickly becomes outdated. Integrating BAS into your CTEM program allows you to continuously check for exposure. By running simulations on an ongoing basis, you can ensure that your security controls remain effective as your environment evolves and new threats emerge. This continuous validation loop is fundamental to proactive cybersecurity, helping you maintain a strong security posture over time with a platform like Uni5 Xposure.
Adopting a CTEM program isn’t just about adding another tool to your security stack; it’s about fundamentally changing how you approach cybersecurity. Instead of constantly playing defense, you get to be strategic and proactive. This shift brings some major advantages that can make a real difference for your team and your entire organization. From reducing risk to making your team’s work more impactful, let’s walk through the key benefits you can expect.
The biggest win with CTEM is getting ahead of the game. You’re no longer just reacting to threats as they appear; you’re actively finding and fixing security gaps before attackers can exploit them. This proactive stance means you stop attacks before they even start. By continuously scanning your environment and understanding your exposures from an attacker’s perspective, you can address the most critical weaknesses first. This approach helps you build a more resilient security posture and significantly lowers the chances of a successful breach, letting your team move from firefighting to strategic defense.
If you’re tired of staring at endless lists of theoretical vulnerabilities, CTEM can bring some much-needed clarity. It gives you a continuous, real-time view of your security landscape, but with a crucial filter: it shows you the exposures that attackers are most likely to use. Instead of a noisy report filled with low-priority items, you get a focused view of your true attack surface. This allows you to see your organization as an attacker would, helping you understand which pathways are most vulnerable and where to direct your attention for the biggest impact.
Your security team’s time is one of your most valuable assets. A CTEM program helps you make the most of it by automating discovery and focusing efforts on what matters. By using threat intelligence to prioritize vulnerabilities, you can cut through the noise and guide your team to fix the most critical risks first. This means less time spent on manual analysis and chasing down low-impact issues. Instead, your team can dedicate their expertise to addressing the exposures that pose a genuine threat to your business, making their work more efficient and effective.
CTEM helps bridge the gap between security operations and business objectives. When you can clearly identify and prioritize threats based on their potential business impact, your response becomes much more strategic. This focus allows you to show leadership exactly how your team’s efforts are reducing risk to critical operations. By concentrating on the most significant exposures, you not only improve your overall security but also strengthen your ability to respond quickly and effectively when a real threat emerges. It’s about making smarter, data-driven decisions that protect the entire organization.
Shifting to a Continuous Threat Exposure Management (CTEM) program is a game-changer, but let’s be real—it’s not as simple as flipping a switch. Like any significant strategic change, it comes with a few hurdles. The good news is that these challenges are well-understood, and with a bit of foresight, you can plan for them instead of being caught off guard.
Thinking through these potential roadblocks ahead of time is the best way to ensure a smooth transition. From getting the right budget to breaking down internal silos, addressing these issues head-on will set your CTEM program up for success from day one. It’s about moving forward with a clear-eyed view of what it takes to build a truly proactive security posture. The goal isn’t just to adopt a new framework but to embed it into your organization’s culture for the long haul.
Getting the green light for funding is often the first challenge. It’s important to frame the conversation correctly: CTEM is a strategic program, not just a single product. You’ll likely use many different tools to cover the five stages of the CTEM cycle. The key is to budget for a platform that can unify these processes and provide a single source of truth. When you’re making the case, focus on the value of proactive risk reduction and operational efficiency. A platform that consolidates your view of the entire attack surface and automates prioritization doesn’t just reduce risk; it saves your team countless hours, delivering a clear return on investment.
Most security teams are already dealing with a sprawling toolkit of scanners, agents, and monitoring solutions. The challenge isn’t a lack of data; it’s the overwhelming noise and the difficulty of connecting the dots. A successful CTEM program hinges on your ability to pull all this information together. To move beyond generic severity scores, you need to automate the analysis of contextual factors like threat intelligence and business criticality. This requires a central platform that can ingest data from your existing tools, de-duplicate findings, and enrich them with real-world context from sources like HiveForce Labs. The goal is to create a single, prioritized list of exposures that tells you exactly what to fix first.
Cybersecurity is a team sport, but many organizations still operate in silos. Security finds vulnerabilities, IT manages the infrastructure, and DevOps writes the code. CTEM requires these teams to work in lockstep, which can be a major cultural shift. The key to overcoming this is to establish a shared framework and a common language. A CTEM platform acts as a bridge, providing a unified view of risk that everyone can understand. When remediation steps are clear, assigned to the right owner, and tracked in one place, collaboration becomes a natural part of the workflow instead of a constant struggle.
It’s no secret that there’s a significant shortage of skilled cybersecurity workers. This can make implementing a comprehensive program like CTEM feel intimidating, especially for teams that are already stretched thin. But you don’t necessarily need a bigger team—you need a more efficient one. The right technology, like a unified threat exposure management platform, can act as a force multiplier by automating the manual, time-consuming tasks that bog down your analysts. By automatically correlating vulnerabilities with active threats and providing clear remediation guidance, it allows your team to focus its limited time and expertise on the exposures that pose a genuine threat to your business.
Shifting to a CTEM model is a strategic move that requires careful planning and execution. It’s not just about buying a new tool; it’s about evolving your security processes and culture. Here’s how you can set your team up for success.
Adopting CTEM is a process, not a one-time project. Instead of trying to overhaul everything at once, plan a phased rollout. Start by identifying the weakest links in your current security posture or the business units with the most critical assets. By focusing on a specific area first, you can demonstrate quick wins, learn valuable lessons, and build momentum for a broader implementation. This approach allows your team to adapt gradually and ensures you’re addressing the most significant risks from the get-go. As you expand, you can build a comprehensive view of your total attack surface and mature your program over time.
A successful CTEM program can’t operate in a silo. It requires active collaboration between your security, IT operations, and development teams. Involve key people from these departments early in the planning process to ensure the program aligns with their workflows and overall business objectives. When everyone shares the same data and understands the priorities, you can eliminate friction and speed up remediation. A unified platform that provides a single, consistent view of threat exposure is essential for getting everyone on the same page and fostering a culture where security is a shared responsibility.
The right technology is the backbone of your CTEM program, bringing all five stages together in a cohesive workflow. Look for a platform that can integrate with your existing security tools to avoid creating more data silos. Your goal should be a single source of truth that supports the entire lifecycle, from discovery to remediation. The Uni5 Xposure Platform is built to provide this unified view, helping you manage your entire program from one place. It connects asset discovery, vulnerability prioritization, control validation, and remediation guidance to give your team a clear path forward.
To show that your CTEM program is working, you need to track the right metrics. Key performance indicators (KPIs) help you measure effectiveness and communicate the value of your efforts to leadership. Start by tracking metrics like Mean Time to Detect (MTTD), Mean Time to Remediate (MTTR), and the percentage of critical vulnerabilities patched within your service-level agreements (SLAs). These data points provide clear evidence of risk reduction and help you make informed decisions about where to focus your resources. Tracking your progress helps justify your security investments and demonstrates how your team is strengthening the organization’s security posture.
Is CTEM just another buzzword for vulnerability management? Not at all. While it builds on some of the same principles, CTEM is a strategic evolution. Traditional vulnerability management often focuses narrowly on finding and patching known software flaws. CTEM broadens that view to your entire attack surface, including things like cloud misconfigurations and weak credentials. It’s a continuous program that prioritizes what to fix based on real-world threats and business impact, not just a technical severity score.
My team is already swamped. Will implementing CTEM just add more work? It’s a valid concern, but the goal of CTEM is actually to make your team more efficient. By automating discovery and using threat intelligence to prioritize, it cuts through the noise of thousands of low-risk alerts. This allows your team to stop chasing down every minor vulnerability and focus their limited time and energy on the few exposures that pose a genuine, immediate threat to your organization.
How is the prioritization in CTEM really different from just using CVSS scores? A high CVSS score tells you a vulnerability is technically severe, but it doesn’t tell you if it’s a real risk to your business. CTEM adds two crucial layers of context. First, it incorporates threat intelligence to see if attackers are actually exploiting that vulnerability in the wild. Second, it considers business context to know if the vulnerability exists on a critical asset. This combination helps you focus on fixing a “medium” vulnerability on your payment server before a “critical” one on a non-essential test machine.
Do I need to get rid of all my current security tools to adopt a CTEM program? Definitely not. A strong CTEM program doesn’t require you to rip and replace your existing tools. Instead, the right platform will integrate with the scanners and agents you already have. It acts as a central hub, pulling in data from all your different sources to create a single, unified view of your risk. This actually makes your current tools more valuable by putting their findings into a broader, more actionable context.
What’s the first practical step my team can take to start moving towards a CTEM model? The best place to start is with the first stage: scoping. Before you scan anything, sit down with business leaders and identify your most critical assets and processes. What systems absolutely cannot go down? Where is your most sensitive data stored? By defining what matters most to the business first, you create a focused scope that ensures all your subsequent security efforts are aimed at protecting your most valuable assets.