Comprehensive Threat Exposure Management Platform
 Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the Report
Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the ReportA high CVSS score doesn’t always equal high business risk. A critical vulnerability on a non-essential, isolated asset might be less of a priority than a medium-level one on your primary payment server. To truly manage risk, you have to connect technical data to business context. This means factoring in asset criticality, real-time threat intelligence, and the potential financial impact of a breach. A powerful vulnerability prioritization tool for enterprises does exactly that. It translates a mountain of technical alerts into a clear, actionable list that reflects what matters most to your organization, helping you protect your crown jewels and justify your team’s efforts to leadership.
If your security team feels like they’re constantly playing catch-up, you’re not alone. The sheer volume of vulnerability alerts is overwhelming, and the old method of chasing every single one is simply not sustainable. This is where vulnerability prioritization tools come in. Think of them as a smart filter for your security alerts. Instead of just showing you a long list of potential weaknesses, these tools analyze, contextualize, and rank them so you can focus your time and resources on the threats that pose a genuine risk to your organization.
These tools are a core component of a modern Threat Exposure Management program. They help you move beyond just finding vulnerabilities and toward actively reducing your attack surface. By combining data about your specific assets with real-time threat intelligence, a prioritization tool helps you answer the most important question: “What do we need to fix right now?” This shift allows your team to work more efficiently, make data-driven decisions, and stay ahead of attackers who are actively looking for the easiest way in. It’s about working smarter, not just harder, to protect your business from real-world threats. It transforms vulnerability management from a compliance checkbox into a strategic security function.
Every day, new vulnerabilities are discovered, adding to an already massive backlog. Trying to patch everything is like trying to empty the ocean with a bucket. Vulnerability prioritization is the process of ranking these weaknesses based on a variety of risk factors, including their exploitability, the importance of the affected asset, and current threat intelligence. A good tool automates this process, cutting through the noise of thousands of low-risk alerts to highlight the critical few that demand immediate attention. This allows your team to stop chasing ghosts and concentrate on the vulnerabilities that attackers are most likely to use against you.
For years, many security teams have operated in a reactive mode, scrambling to patch whatever the latest scanner report flagged as “critical.” An effective vulnerability prioritization strategy changes that dynamic. It requires a contextual approach that considers your unique infrastructure, business operations, and the specific threats you face. By automating the initial identification and evaluation, these tools free up your security analysts to focus on more strategic initiatives. This transforms your security posture from a constant state of reaction to a proactive, intelligence-driven operation where you can confidently address the most significant risks first.
When you start comparing vulnerability prioritization tools, you’ll notice they aren’t all built the same. The right platform does more than just scan and list vulnerabilities; it gives you the context and capabilities to act decisively. A great tool should feel like an extension of your team, automating the tedious work and providing clear, actionable insights. To cut through the noise, focus on a few core features that separate the truly effective platforms from the basic scanners. These capabilities are what will ultimately help you shift from a reactive cycle of patching to a proactive security posture.
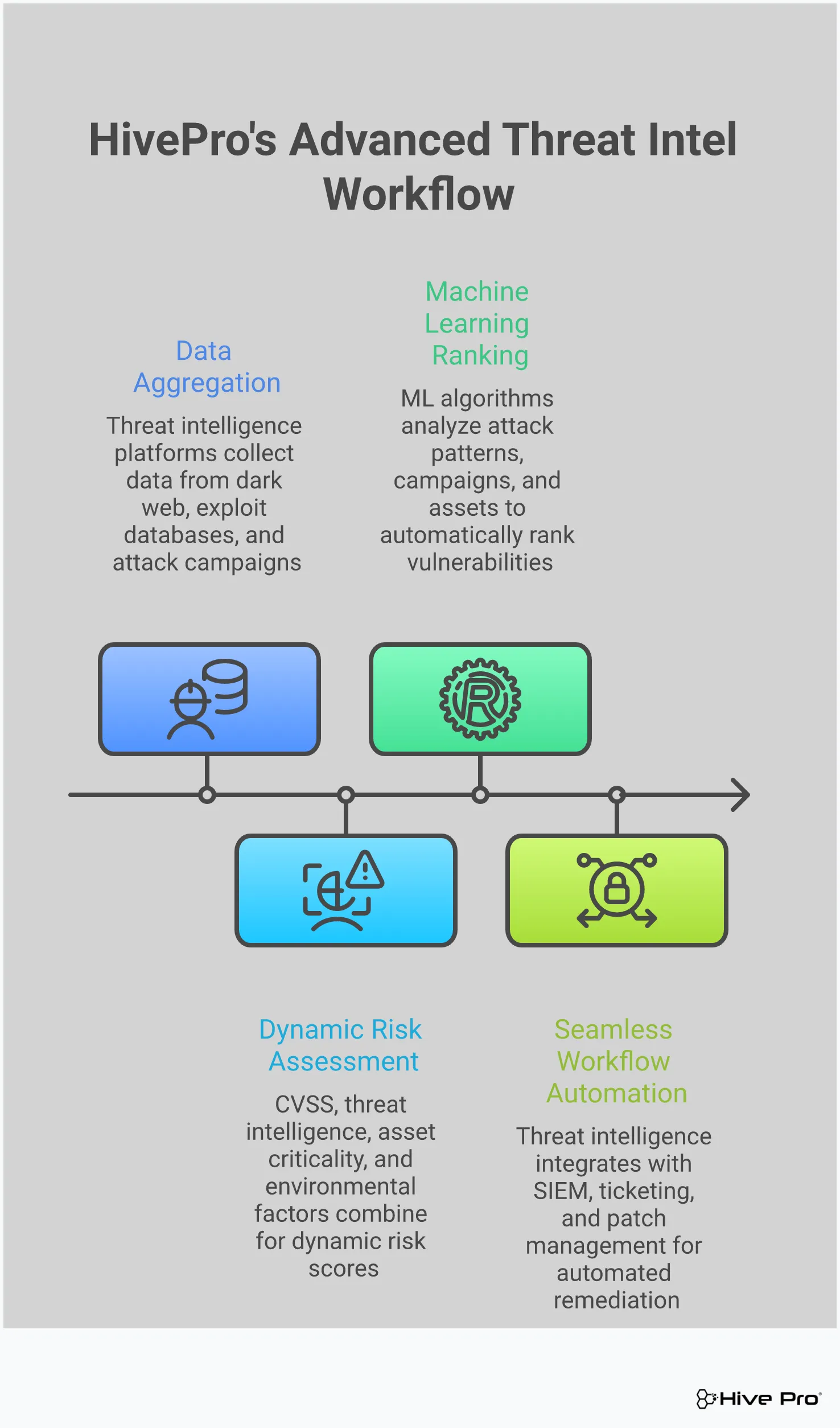
Static vulnerability data becomes stale almost instantly. To make smart decisions, you need a tool that taps into real-time threat intelligence. This means getting up-to-the-minute information on which vulnerabilities are being actively exploited by attackers in the wild. Knowing a flaw has a known exploit or is being used in active campaigns helps you explain to leadership why a particular fix is urgent. It’s the difference between saying, “This has a high score,” and, “Threat actors are using this to break into companies like ours right now.” This context, often powered by dedicated research teams like HiveForce Labs, is critical for focusing your team’s limited resources on the threats that pose an immediate danger.
The Common Vulnerability Scoring System (CVSS) is a good starting point, but it can’t be your only metric. A high CVSS score doesn’t always equal high business risk. A critical vulnerability on a non-essential, isolated asset might be less of a priority than a medium-level one on your primary payment server. Look for a tool that provides a more nuanced approach to vulnerability and threat prioritization. This means factoring in business context, asset criticality, and the potential financial impact of a breach. The best tools combine CVSS data with threat intelligence and business impact to create a true risk score that reflects what matters most to your organization.
If your team is spending its days manually correlating data, creating spreadsheets, and emailing tickets, you’re falling behind. Automation is essential for any modern security program. A strong prioritization tool should automate the entire workflow, from ingesting scan data and scoring vulnerabilities to creating remediation tickets in your team’s preferred system. This frees up your security analysts from repetitive, low-value tasks and allows them to focus on strategic initiatives like threat hunting and security architecture. Automation ensures consistency, reduces human error, and allows your program to scale effectively as your organization grows, keeping your team focused and efficient.
Your vulnerability prioritization tool shouldn’t be an isolated island. It needs to integrate smoothly with the other security and IT tools you already use. This means having robust APIs and pre-built connectors for your vulnerability scanners, asset management databases, SIEMs, and ticketing systems like Jira or ServiceNow. A well-integrated tool creates a unified workflow where information flows seamlessly from detection to remediation. This Uni5 Xposure platform approach saves countless hours of manual data entry and ensures that everyone, from the security team to IT operations, is working from the same source of truth.
Prioritization tells you where to focus, but how do you know your fixes are actually working? This is where Breach and Attack Simulation (BAS) comes in. This feature allows you to safely simulate real-world attack techniques to validate your security controls and test whether a vulnerability is truly exploitable in your environment. Instead of just assuming a patch fixed the problem, you can prove it. BAS helps you perform adversarial exposure validation to find and close exploitable attack paths before an actual attacker does. It’s the ultimate reality check for your security posture, providing concrete evidence that your defenses are holding strong.
With so many tools on the market, finding the right fit can feel overwhelming. Each platform has its own strengths, so the best choice really depends on your team’s specific needs, existing tech stack, and overall security goals. To help you get started, here’s a look at five leading vulnerability prioritization tools that security teams rely on to cut through the noise and focus on what matters most.
The Hive Pro Uni5 Xposure Platform offers a complete Threat Exposure Management solution by unifying your internal and external attack surfaces. It gives you a single, real-time view of all your assets, whether they’re in the cloud or on-premises. The platform uses agentless scanners for broad coverage and pulls in threat intelligence from our in-house HiveForce Labs to deliver accurate, risk-based prioritization. This approach helps you move beyond guesswork and proactively manage threats. Users on Gartner Peer Insights highlight its ability to quickly identify and prioritize vulnerabilities based on an organization’s unique threat context.
Tenable.io is a cloud-based vulnerability management platform designed to provide continuous visibility across your entire environment. It’s known for its advanced analytics that help you prioritize vulnerabilities based on your organization’s specific risk profile. A key strength of Tenable.io is its ability to integrate with a wide range of security tools, which allows you to centralize your vulnerability data and get a more complete picture of your exposure. This makes it a flexible option for teams looking to build on their existing security stack while improving their prioritization process.
Qualys VMDR, which stands for Vulnerability Management, Detection, and Response, combines these three critical functions into a single, unified platform. It provides real-time visibility into vulnerabilities across your IT landscape and uses machine learning to help prioritize them according to risk. One of the standout features of Qualys VMDR is its ability to automate the patching process. This helps your team not only identify what’s most important but also remediate those vulnerabilities quickly and efficiently, closing the gap between detection and response.
Rapid7 InsightVM provides live vulnerability management and endpoint analytics, giving you a real-time view of your risk. The platform takes a risk-based approach, helping your team concentrate on the vulnerabilities that pose the most significant threat to your critical assets. InsightVM also integrates with other security tools to create a more connected and effective remediation workflow. It’s a solid choice for organizations that need to see changes in their environment as they happen and want clear guidance on where to direct their remediation efforts for the biggest impact.
CrowdStrike Falcon Spotlight is a vulnerability management tool that is built directly into the well-known CrowdStrike Falcon platform. This tight integration means it provides real-time, scan-free visibility into vulnerabilities across all your endpoints. Falcon Spotlight prioritizes vulnerabilities using threat intelligence and other risk factors, helping you quickly spot and fix the most pressing issues. Because it leverages the existing Falcon agent, it’s an efficient option for organizations already using CrowdStrike for endpoint protection, as it eliminates the need to deploy another agent.
Think of threat intelligence as the cheat sheet for your vulnerability management program. Without it, you’re staring at a massive list of vulnerabilities, trying to guess which ones matter most. With it, you get the context needed to see which threats are real, active, and aimed at organizations just like yours. This is how you move from a purely theoretical risk model, often based on CVSS scores alone, to a practical, evidence-based approach.
Effective vulnerability and threat prioritization isn’t just about finding flaws; it’s about understanding the adversary. Threat intelligence tells you what attackers are exploiting right now, what tools they’re using, and who they’re targeting. This insight cuts through the noise, allowing your team to focus its limited time and resources on fixing the vulnerabilities that pose a clear and present danger to your business. It transforms your to-do list from a mountain of maybes into a targeted list of must-dos, backed by real-world data.
The most direct way threat intelligence sharpens your focus is by showing you what’s happening in the wild. A vulnerability might have a critical CVSS score, but if no one is actually exploiting it, is it truly your top priority? Threat intelligence platforms pull in data from global sources, including information on known exploited vulnerabilities, to give you a clear picture of the current threat landscape. This allows you to immediately flag vulnerabilities that are part of active attack campaigns.
Instead of guessing, you can act on concrete evidence. When you see that a specific vulnerability is being used to deploy ransomware or steal data, it naturally jumps to the top of your remediation list. This real-time visibility helps you explain the urgency to stakeholders and ensures your team is always working on the most impactful fixes first.
Great threat intelligence doesn’t just tell you what’s happening now; it helps you anticipate what’s coming next. Security researchers and threat actors are in a constant race. When a new vulnerability is disclosed, the clock starts ticking. Intelligence from sources like HiveForce Labs can track the entire weaponization lifecycle, from the initial discovery to the release of a proof-of-concept exploit and its adoption by threat groups.
This predictive insight allows you to get ahead of the curve. By monitoring chatter and tracking the development of exploit code, you can prioritize patching a vulnerability before it becomes a widespread problem. This proactive stance is key to reducing your window of exposure and preventing incidents before they can even start.
Not all threats are relevant to all organizations. A threat actor group that specializes in attacking financial institutions probably isn’t your biggest concern if you’re in the healthcare sector. This is where contextual threat intelligence becomes so valuable. It helps you filter out the noise by focusing on the adversaries, campaigns, and tactics that are known to target your specific industry.
By understanding the threats most relevant to your business, you can tailor your prioritization strategy accordingly. For example, a retail company might prioritize vulnerabilities in point-of-sale systems, while a government agency might focus on those targeted by state-sponsored actors. This level of specificity makes your vulnerability management efforts far more efficient and effective.
Ultimately, cybersecurity is about managing business risk. Threat intelligence helps you translate technical vulnerabilities into potential financial impact, a language that everyone in the organization, especially the C-suite, can understand. By knowing who the attackers are and what their motives are (e.g., financial gain, espionage, disruption), you can better assess the potential cost of a successful exploit.
This context helps you build a stronger business case for your remediation efforts. Instead of just saying, “We need to patch this critical vulnerability,” you can say, “We need to patch this vulnerability because it’s being exploited by a ransomware group that could cost us millions in downtime and recovery.” This approach connects your team’s work directly to the bottom line, demonstrating the clear value of your security program.
Vulnerability prioritization is a huge step forward, but it’s still based on predictions. You’re using threat intelligence and asset data to make an educated guess about what an attacker might do. What if you could test that guess? That’s where Breach and Attack Simulation (BAS) comes in. Instead of just identifying a potential weakness, BAS tools actively try to exploit it in a safe, controlled environment. This gives you concrete proof of your exposure and helps you move from theory to certainty.
Think of it this way: a vulnerability scan tells you a window is unlocked, but a BAS platform actually tries to open it. This approach is critical because not every vulnerability is exploitable in every environment. Your specific security controls, network segmentation, and system configurations might render a high-CVSS vulnerability completely harmless. BAS cuts through the noise by showing you which vulnerabilities create a tangible risk to your organization. By simulating real-world attack techniques, BAS validates your security controls and provides a clear, actionable map of how an adversary could breach your defenses. It’s the most effective way to answer the question, “Are we actually vulnerable to this?”
You’ve done the hard work of sifting through thousands of vulnerabilities and have a prioritized list. But how confident are you in that list? BAS lets you validate your vulnerability prioritization by running simulated attacks against your environment. These simulations mimic the tactics, techniques, and procedures (TTPs) used by actual threat actors. By seeing which of your prioritized vulnerabilities are truly exploitable in a real-world scenario, you can confirm you’re focusing your team’s limited time and resources on the issues that pose the most immediate danger. It’s the difference between knowing a door is unlocked and knowing someone can actually walk through it and access your critical assets.
Patching a vulnerability is one thing; confirming the fix is effective is another. Too often, teams deploy a patch and simply assume the risk is gone. BAS provides a crucial feedback loop by allowing you to test your remediation efforts. After you’ve applied a fix, you can run another simulation to verify that the vulnerability is no longer exploitable. This process confirms that the patch was deployed correctly and didn’t inadvertently open up another attack vector. It’s a practical way to measure the effectiveness of your security measures and ensure your hard work is actually reducing risk, not just checking a box on a compliance report.
Attackers rarely exploit a single vulnerability in isolation. They chain them together, moving laterally across your network to reach high-value assets. A standalone vulnerability scanner might miss this bigger picture. BAS tools excel at identifying these potential attack paths. By simulating multi-stage attacks, they can show you exactly how an adversary could pivot from one compromised system to another. Proactively discovering these paths gives you the chance to address the weak links in the chain before a real attacker can exploit them. This significantly improves your overall security posture by hardening your defenses against sophisticated, real-world attack campaigns, not just single-point failures.
Your attack surface and the threat landscape are constantly changing. New assets come online, software configurations change, and attackers develop new techniques every day. Because of this, security validation can’t be a one-time event. Integrating BAS into your security program allows for the continuous assessment of your exposure. Regular, automated simulations ensure you can keep pace with evolving threats and internal changes. This ongoing process of adversarial exposure validation helps you maintain a clear and current understanding of your security gaps, ensuring your defenses remain effective over time and that you’re never caught off guard by a new or re-emergent threat.
Once you’ve shortlisted tools based on features, it’s time to get practical about cost and implementation. How a tool is priced and deployed directly impacts your budget, your team’s workload, and your ability to scale. It’s about finding a solution that fits your infrastructure and grows with you, saving you from major headaches down the road. Let’s break down the key factors to consider.
Most vulnerability prioritization tools use a subscription model, often with tiered pricing based on the number of assets, features, or support level. This flexibility lets you find a plan that fits your budget and operational needs. To choose the right one, think about your company’s specific requirements. Consider the size of your network, how much automation you need, and any compliance rules you follow. This helps you avoid paying for features you won’t use while getting everything you need to secure your environment.
Deciding between a cloud-based (SaaS) or an on-premises solution is a critical step. Cloud tools are generally easier to set up and maintain, scaling effortlessly as you grow. Many cloud service providers even integrate security controls to simplify risk management. On the other hand, an on-premises tool gives you more direct control over your data, which might be necessary for strict compliance or data sovereignty rules. You’ll need to weigh the ease of a cloud solution against your organization’s need for control.
Your organization is always changing, and your security tools need to keep up. As your company expands, so does your attack surface, so scalability is non-negotiable. Your chosen tool must be able to scan every part of your network, from physical servers and virtual machines to cloud services and containers. It should handle a growing number of devices without slowing down. A truly scalable platform for total attack surface management ensures your security posture remains strong as you add new assets and technologies.
Choosing a vulnerability prioritization tool is a great first step, but the tool is only as effective as the strategy behind it. The best approach isn’t a one-size-fits-all solution you can pull off a shelf. It’s a tailored strategy that reflects your organization’s unique risk appetite, business goals, and regulatory landscape. It’s about moving beyond a simple checklist and building a dynamic process that adapts to your environment.
A successful prioritization program is built on a foundation of clear communication, intelligent automation, and a deep understanding of what matters most to your business. By focusing on these core principles, you can create a system that not only identifies the most critical threats but also empowers your teams to address them efficiently.
A vulnerability’s technical severity score doesn’t tell the whole story. To truly understand risk, you have to consider the business context. A critical vulnerability on a developer’s test machine simply doesn’t carry the same weight as a medium-level one on your customer-facing payment server. This is why asset criticality is so important. Your prioritization tool should help you identify your most valuable assets, or “crown jewels,” and weigh vulnerabilities on them more heavily. This process involves ranking vulnerabilities based on factors like exploitability, asset importance, and potential business impact, giving you a unified view of cyber risks that aligns with what your organization values most.
With thousands of vulnerabilities to sift through, automation is your best friend. Automating parts of your vulnerability management process can expedite identification, evaluation, and remediation, freeing up your team to focus on more strategic work. You can automate ticket creation, assign tasks, and even trigger rescans to verify fixes. However, automation shouldn’t completely replace human expertise. You still need skilled analysts to review edge cases, validate automated findings, and make the final call on complex remediation plans. The goal is to use automation to handle the noise so your experts can focus on the signals that truly matter.
Vulnerability management is a team sport. It requires seamless collaboration between security, IT operations, and development teams. A siloed approach where the security team simply throws a report over the wall to IT is doomed to fail. Your prioritization strategy must foster a shared sense of ownership. This means using tools and processes that provide a single source of truth, with clear dashboards and reporting that everyone can understand. When teams can see the same data and track remediation progress together, it breaks down communication barriers and ensures everyone is working toward the same goal: reducing organizational risk.
For many organizations, especially those in finance, healthcare, or government, meeting regulatory compliance is non-negotiable. Frameworks like PCI DSS, HIPAA, and GDPR come with strict requirements for managing vulnerabilities. A strong prioritization approach incorporates these mandates directly into the workflow. Your tool should help you map vulnerabilities to specific compliance controls, making it easy to identify and prioritize the fixes needed to stay compliant. This not only helps you pass audits and avoid fines but also builds a foundation of trust with your customers by demonstrating a commitment to protecting their data.
Choosing the right vulnerability prioritization tool is a major step, but the work doesn’t stop once you’ve signed the contract. Getting a new platform up and running comes with its own set of challenges, and a smooth implementation is critical to seeing a real return on your investment. If your team finds the tool clunky or disconnected from their daily work, it will quickly become shelfware. The goal is to embed this new capability into your security program, not just add another dashboard that gets ignored.
Being aware of these common hurdles ahead of time can make the entire process smoother for you and your team. Think about your current ecosystem. How will this new tool talk to your existing scanners, ticketing systems, and SIEM? A lack of seamless integration can create more manual work, defeating the purpose of getting a new tool in the first place. Then there’s the human element. Your team needs the time and training to understand not just which buttons to click, but how to interpret the data and take action. Without proper resource allocation, even the most powerful platform will fall short. From technical integrations to tracking down rogue assets and managing complex environments, let’s look at what to watch for and how to prepare for a successful rollout.
Your new vulnerability prioritization tool can’t operate in a silo. It needs to connect with the security and IT tools you already use every day. The key is to find a platform that offers robust APIs and pre-built integrations to create a unified workflow. This allows you to pull vulnerability data from your various scanners, push prioritized tickets to your ITSM platform, and send alerts to your SIEM without manual copy-pasting. A well-integrated system lets you manage vulnerabilities from a single place, which reduces the complexity of coordinating security efforts across different technologies. Before you commit, map out your existing stack and verify that the new tool can connect to your critical systems.
A new tool is only as effective as the team using it. Beyond the subscription cost, you need to budget for implementation and training. Your team needs dedicated time to learn the platform and understand how it changes their existing workflows for the better. This isn’t just about a one-hour webinar; it’s about building confidence and competence. Effective vulnerability management is a non-negotiable requirement, and that means investing in your people. Ensure your team understands the “why” behind the new tool and how it helps them focus on the threats that matter most. This buy-in is crucial for adoption and for embedding proactive security practices into your company culture.
You can’t protect what you don’t know you have. Shadow IT, from unsanctioned cloud instances to forgotten developer servers, creates dangerous blind spots in your security coverage. Traditional vulnerability management often falls short because it only scans known assets. A modern approach requires a tool with strong attack surface management capabilities to continuously discover and inventory all connected assets, whether they’re on-prem, in the cloud, or part of your supply chain. Cyber threat actors are experts at finding these unmanaged entry points. Your prioritization tool must be able to find them first, bring them under management, and assess their exposure before an attacker does.
For large enterprises with separate business units or MSSPs serving multiple clients, managing vulnerabilities at scale is a huge challenge. Each environment can have a unique tech stack, risk tolerance, and compliance requirements. Trying to apply a one-size-fits-all approach is inefficient and often ineffective. Look for a platform designed for these complex scenarios, ideally one that offers multi-tenancy or a centralized dashboard with clear segmentation. This allows you to manage security policies, view risk levels, and generate reports for each environment separately while maintaining a single, unified view of your entire operation. This capability is essential for providing consistent service and demonstrating value to different stakeholders.
Choosing the right vulnerability prioritization tool can feel overwhelming, and a few common misconceptions can send you down the wrong path. Believing these myths can lead to selecting a tool that doesn’t fit your needs, creating more noise than clarity for your team. Let’s clear up some of the most persistent myths so you can focus on what truly matters: finding a solution that helps you manage real-world risk effectively and protect your organization from actual threats.
It’s easy to fall into the trap of chasing high CVSS scores. While the scoring system is a useful starting point, it only tells part of the story. A high score reflects technical severity but doesn’t account for whether attackers are actually exploiting it in the wild. This creates a disconnect between your team’s efforts and your actual risk exposure. Relying solely on CVSS can cause you to waste valuable time on theoretical threats while a lower-scored, but actively exploited, vulnerability gets ignored. Modern vulnerability prioritization methods must go beyond static scores to incorporate real-time threat intelligence.
Your digital environment is anything but static. New assets come online, software is updated, and configurations change daily, while attackers constantly discover new exploits. Thinking of security as a one-time checklist is a critical mistake. Effective vulnerability management is a continuous cycle of discovery, prioritization, and remediation. Your tools must support this ongoing effort. A tool that only provides periodic snapshots of your security posture will always leave you a step behind. You need a solution built for continuous assessment to keep up with your evolving attack surface.
Automation is a powerful ally, helping teams handle the sheer volume of alerts and data. However, it isn’t a silver bullet. Automated scanners are excellent at identifying potential vulnerabilities, but they lack the context and critical thinking of a skilled security professional. An expert is still needed to interpret scan results, understand business impact, and make strategic decisions about remediation. The goal isn’t to replace your team but to empower them. The best tools handle repetitive tasks, freeing up your experts to focus on the high-impact analysis that helps overcome common challenges in securing your organization.
Selecting the right vulnerability prioritization tool is more than just a technical purchase; it’s a strategic decision that shapes your entire security posture. The best tool for your organization will fit seamlessly into your existing workflows, provide clear and actionable insights, and ultimately make your team more effective at reducing real-world risk. To find that perfect fit, you need a structured evaluation process that looks beyond feature lists and marketing claims. It’s about asking the right questions and testing how a platform performs in your specific environment.
Before you even look at a demo, start by defining what success looks like for your team. What key performance indicators (KPIs) matter most? Think about metrics like mean time to remediate (MTTR), the number of critical vulnerabilities patched per quarter, or the reduction in exploitable attack paths. Consider who needs to see this data. Your security team needs granular details, while your CISO and other executives need high-level dashboards that connect security efforts to business risk. A solid vulnerability prioritization tool should offer customizable reporting that speaks to every stakeholder, from the analyst in the trenches to the board member in the meeting.
A proof of concept is your chance to test-drive a tool in your own environment. Don’t rely on canned demos. Instead, set up a PoC that mirrors your daily reality. Involve the team members who will use the tool every day and give them specific scenarios to test. Can they easily integrate it with your existing scanner and ticketing system? How intuitive is the workflow for assigning and tracking remediation tasks? A successful PoC should prove that the tool not only identifies and prioritizes vulnerabilities effectively but also reduces friction for your team. This hands-on experience is the best way to confirm if a tool’s promises hold up under pressure.
Justifying a new security tool often comes down to return on investment (ROI). Success isn’t just about finding more vulnerabilities; it’s about fixing the right ones faster and more efficiently. Calculate the potential ROI by estimating the time your team will save through automation and improved focus. Think about how a tool’s contextual insights can prevent a costly breach. An effective platform provides a unified view of cyber risks that considers your unique infrastructure and the current threat landscape. This allows you to demonstrate a clear reduction in business risk, which is a powerful way to measure the tool’s true value.
When you choose a tool, you’re also choosing a partner. Look for a vendor that is invested in your success. How responsive and helpful is their support team during the PoC? Do they have a clear product roadmap that aligns with future security trends? Check out their community forums, user groups, and threat intelligence reports, like Hive Pro’s threat advisories, to gauge their expertise and commitment to their customers. A strong vendor relationship ensures you’ll have the support you need to adapt to new threats and get the most out of your investment for years to come.
Why isn’t just patching everything with a high CVSS score good enough? Relying only on CVSS scores is like reading just the headline of a news story. It gives you a general idea of severity but misses all the crucial context. A high-scoring vulnerability might not have a known exploit or could be on an isolated, non-critical asset. A good prioritization tool adds the missing details, like real-time threat intelligence showing which flaws are being actively attacked, and business context to tell you if the vulnerability is on a system that truly matters. This helps you focus on genuine business risk, not just technical severity.
How is a vulnerability prioritization tool different from the scanner I already have? Think of your scanner as the tool that finds all the potential problems; it generates a long list of every possible weakness it can detect. A vulnerability prioritization tool takes that raw list and makes it intelligent. It enriches the scanner’s data with threat intelligence and your own business context to rank and score the vulnerabilities. Its job is to cut through the noise and tell you which handful of issues on that massive list pose a clear and present danger to your organization.
How does Breach and Attack Simulation (BAS) help with vulnerability management? Breach and Attack Simulation acts as a reality check for your vulnerability management program. While prioritization helps you make an educated guess about your biggest risks, BAS lets you safely test those guesses. It simulates real-world attack methods to confirm if a prioritized vulnerability is truly exploitable in your specific environment. This helps you validate that your security controls are working as expected and ensures your team is fixing problems that create actual, provable risk.
My team is already swamped. How does a prioritization tool reduce their workload instead of adding to it? A good tool should feel like adding a new, highly efficient analyst to your team, not another task to the list. It automates the time-consuming, manual work of sifting through thousands of alerts, correlating data from different sources, and trying to figure out what to fix first. By handling that initial analysis, the tool frees up your team to focus their skills on strategic remediation and threat hunting, making their efforts more targeted and effective.
What’s the most important thing to consider besides technical features when choosing a tool? Beyond any specific feature, the most critical factor is how well the tool aligns with your organization’s business context. A platform can have all the bells and whistles, but if it can’t help you protect your most critical assets, it isn’t the right fit. The best approach involves identifying your “crown jewels” first and then finding a tool that helps you prioritize the threats that directly endanger them. This ensures your security efforts are always tied to protecting what matters most to your business.