Comprehensive Threat Exposure Management Platform
 Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the Report
Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the ReportYou have firewalls, endpoint detection, and countless other security controls in place, but how do you know they’ll work when an actual attack happens? Guesswork isn’t a strategy. Breach and Attack Simulation (BAS) helps answer this question by safely testing your defenses against real-world attack scenarios. The results provide concrete evidence of what is truly exploitable in your environment. This data is the key to intelligently prioritize cyber risk, allowing you to focus your remediation efforts on the weaknesses that create a direct path to your most critical assets, not just the ones with the highest theoretical scores.
If your team feels like they’re constantly playing catch-up with an endless stream of security alerts, you’re not alone. The sheer volume of potential threats can be paralyzing, making it difficult to know where to even begin. This is where cyber risk prioritization comes in. It’s not just about making a list; it’s about creating a clear, strategic plan that transforms your security posture from reactive to proactive. By focusing your energy where it truly counts, you can make meaningful progress in protecting your organization’s most valuable assets.
Many security teams are drowning in alerts. When everything is flagged as urgent, it’s nearly impossible to decide which fires to put out first. This constant state of reaction often leads to wasted effort on low-impact issues while critical vulnerabilities get missed. The problem is that traditional methods, like relying solely on technical severity scores, don’t tell the whole story. A “critical” vulnerability on a non-essential test server isn’t nearly as dangerous as a “medium” one on your primary customer database. Without business context, you’re just guessing what could actually cause harm.
Risk prioritization is your strategy for cutting through the noise. It’s the process of figuring out which risks pose the greatest threat to your organization so you can address them first. Let’s be realistic: you have limited time, a finite budget, and a team that can’t be everywhere at once. A clear approach to vulnerability and threat prioritization helps you apply those resources intelligently. Instead of just patching vulnerabilities, you can build a program focused on proactive exposure reduction. This means you’re not just reacting to threats as they appear; you’re actively strengthening your defenses against the ones most likely to cause real damage.
Moving from a reactive stance to a proactive one requires a clear, repeatable process. Effective prioritization isn’t about having a perfect crystal ball; it’s about using a structured approach to make informed decisions with the data you have. By breaking down the process into manageable steps, you can create a system that focuses your team’s energy on the threats that truly matter to your organization. This framework helps you move beyond simply patching every vulnerability and toward strategically reducing your overall exposure.
You can’t protect what you don’t know you have. The first step is to create a comprehensive inventory of all your digital assets, including hardware, software, cloud services, and data. Once you have a clear picture of your environment, you can begin scanning for security issues, misconfigurations, and other weaknesses. This process is fundamental to understanding your complete attack surface. A thorough Total Attack Surface Management strategy ensures you have full visibility, which is the bedrock of any effective security program. Without it, you’re essentially flying blind, leaving critical assets potentially exposed and unaccounted for in your defense strategy.
A vulnerability without an active threat is a potential problem, but a vulnerability with a known exploit is an immediate danger. Understanding the current threat landscape is what adds crucial context to your list of vulnerabilities. You need to know which threats are targeting your industry, what methods attackers are using, and which of your specific vulnerabilities are being actively exploited in the wild. This is where threat intelligence becomes invaluable. By consulting up-to-date threat advisories, you can connect the dots between a theoretical weakness and a real-world attack, allowing you to focus on the issues that pose a clear and present danger.
Once you have a list of vulnerabilities and context from the threat landscape, it’s time to score and rank them. To prioritize risks effectively, you need to assign a score to each one based on its potential impact and the likelihood of it being exploited. While systems like the Common Vulnerability Scoring System (CVSS) offer a standardized baseline, true prioritization goes deeper. It combines the CVSS score with asset criticality and real-time threat intelligence. This multi-faceted approach to vulnerability and threat prioritization helps you create a ranked list that reflects the actual risk to your specific business operations, not just a generic severity rating.
With a prioritized list of risks, you can develop a clear and actionable response plan. Not every vulnerability requires the same level of attention or the same remediation strategy. For your most critical risks, the goal might be immediate mitigation through patching or configuration changes. For others, you might decide to reduce the impact through compensating controls or even transfer the risk using cyber insurance. This strategic planning is essential for allocating your team’s time and budget effectively. It ensures your resources are directed toward the vulnerabilities that pose the greatest threat, maximizing the impact of your remediation efforts and preventing team burnout.
Cyber threats are not static, so your risk priorities can’t be either. The threat landscape is constantly changing as new vulnerabilities are discovered and attackers develop new techniques. A risk assessment performed last quarter might be outdated today. That’s why continuous monitoring is so important. You need an ongoing process to reassess your risks and adjust your priorities accordingly. Adopting a Continuous Threat Exposure Management (CTEM) platform helps automate this cycle of discovery, prioritization, and validation. This approach ensures your security posture adapts in real time to the evolving threat landscape, keeping you prepared for what’s next.
Once you’ve identified your vulnerabilities, the real work begins: figuring out which ones to fix first. A scattershot approach just won’t cut it. You need a consistent framework to evaluate each risk, so you can separate the minor annoyances from the major threats. A strong risk assessment doesn’t just look at a vulnerability’s technical severity score; it considers the full context of your business environment.
Think of it like a doctor triaging patients in an emergency room. They don’t just treat the person who yells the loudest; they assess vital signs, consider underlying conditions, and prioritize those in most critical need. Similarly, your risk assessment should be guided by a clear set of criteria that helps you understand both the technical details and the potential business consequences. By consistently applying these criteria, you can create a prioritized list that directs your resources where they’ll have the greatest impact, ensuring you’re tackling the risks that truly threaten your organization.
Not every vulnerability is an active threat. Many have complex requirements for exploitation or simply aren’t on attackers’ radars. That’s why the first question you should ask is, “How likely is this to be exploited?” This moves you beyond the theoretical and into the practical. Look for evidence like the existence of a public proof-of-concept exploit, chatter on dark web forums, or inclusion in common exploit kits.
A vulnerability with a high CVSS score might seem scary, but if it’s incredibly difficult to exploit, it may be a lower priority than a simpler flaw that attackers are actively using. Effective vulnerability and threat prioritization means focusing on weaknesses that present a clear and present danger, not just a potential one.
A vulnerability’s impact is directly tied to the asset it affects. A critical flaw on a non-essential internal server is a problem, but that same flaw on your primary e-commerce database is a catastrophe waiting to happen. This is where you need to connect your security data to business context. Start by identifying your most critical assets, the ones your business cannot function without.
What would be the impact if this system went down or its data was stolen? Consider financial loss, reputational damage, operational disruption, and data privacy implications. By mapping vulnerabilities to the assets they reside on, you can better understand the potential fallout of an attack. This ensures you’re protecting your most valuable resources first.
Your risk assessment shouldn’t happen in a bubble. To truly understand your exposure, you need to know what attackers are doing in the wild. Integrating threat intelligence gives you a real-time view of the threat landscape, showing you which vulnerabilities are being actively targeted in campaigns and which industries are under fire. This is where a dedicated research team like HiveForce Labs becomes invaluable.
This external context helps you see your vulnerabilities through an attacker’s eyes. For example, if a new ransomware strain is exploiting a specific flaw, any asset you have with that vulnerability immediately becomes a higher priority. Threat intelligence transforms your prioritization from a static, internal exercise into a dynamic defense informed by real-world attack data.
For many organizations, risk isn’t just about preventing a breach; it’s also about meeting legal and industry obligations. Regulations like HIPAA, PCI DSS, and GDPR carry strict requirements for protecting sensitive data. A vulnerability that exposes protected health information (PHI) or credit card data isn’t just a security risk, it’s a major compliance violation that can result in steep fines and legal action.
When assessing risk, always consider the compliance implications. Does this vulnerability put you in breach of a specific regulation? Could it cause you to fail an upcoming audit? Factoring in these requirements ensures your prioritization efforts align with your broader business obligations, protecting you from both cyberattacks and regulatory penalties.
Knowing you need to prioritize cyber risk is one thing; actually doing it is another. It’s easy to get stuck when you’re facing a mountain of vulnerabilities and a sea of alerts. If you feel like you’re constantly playing catch-up, you’re not alone. Many security teams run into the same roadblocks that turn a strategic goal into a daily struggle. From overwhelming alert volumes to disconnected teams, these challenges can make effective prioritization feel just out of reach. Let’s walk through some of the most common hurdles and, more importantly, how you can start clearing them.
Your security tools are doing their job by finding potential threats, but the constant stream of alerts can be deafening. Many organizations struggle to decide which risks to fix first simply because there are too many alerts and not enough people to handle them. The real challenge isn’t just finding risks; it’s knowing which ones pose a genuine threat to your business. When your team is stretched thin, every minute spent chasing a low-impact vulnerability is a minute not spent on a critical one. This constant pressure leads to burnout and makes it nearly impossible to move from a reactive to a proactive security posture.
How does your organization define a “critical” risk? If your security team, IT team, and business leaders all have different answers, you have a framework problem. Traditional methods for prioritizing risks, like relying solely on technical scores such as CVSS, often fail to show how a vulnerability could actually hurt the business. A vulnerability with a high technical score might affect a non-critical asset, while a medium-score vulnerability could expose sensitive customer data. Without a consistent, business-aware framework for vulnerability and threat prioritization, teams work from different playbooks, leading to confusion and misaligned efforts that leave critical assets exposed.
Cybersecurity isn’t just an IT problem; it’s a business-wide responsibility. Yet, in many companies, security, operations, and development teams operate in their own worlds. Security finds a vulnerability, IT has to patch it, and developers are focused on shipping new features. When these teams don’t communicate or share the same priorities, critical remediation work gets stuck in limbo. Each team has its own metrics for success, and “patching a server” might not be at the top of everyone’s list. This siloed approach prevents anyone from having a complete, unified view of the organization’s total attack surface, making it difficult to manage risk effectively.
Moving past these challenges starts with centralizing your approach and using smarter tools. Instead of manually sifting through alerts, you can use automation and AI to make faster, more informed decisions about your security. The first step is to create one central place to track all security findings from across your environment. From there, you can develop a risk-scoring system that considers both technical severity and business impact, giving you a clear, contextualized view of your priorities. A unified exposure management platform helps you consolidate your data, apply consistent scoring, and give every team a shared understanding of what needs to be fixed first, turning chaos into a clear action plan.
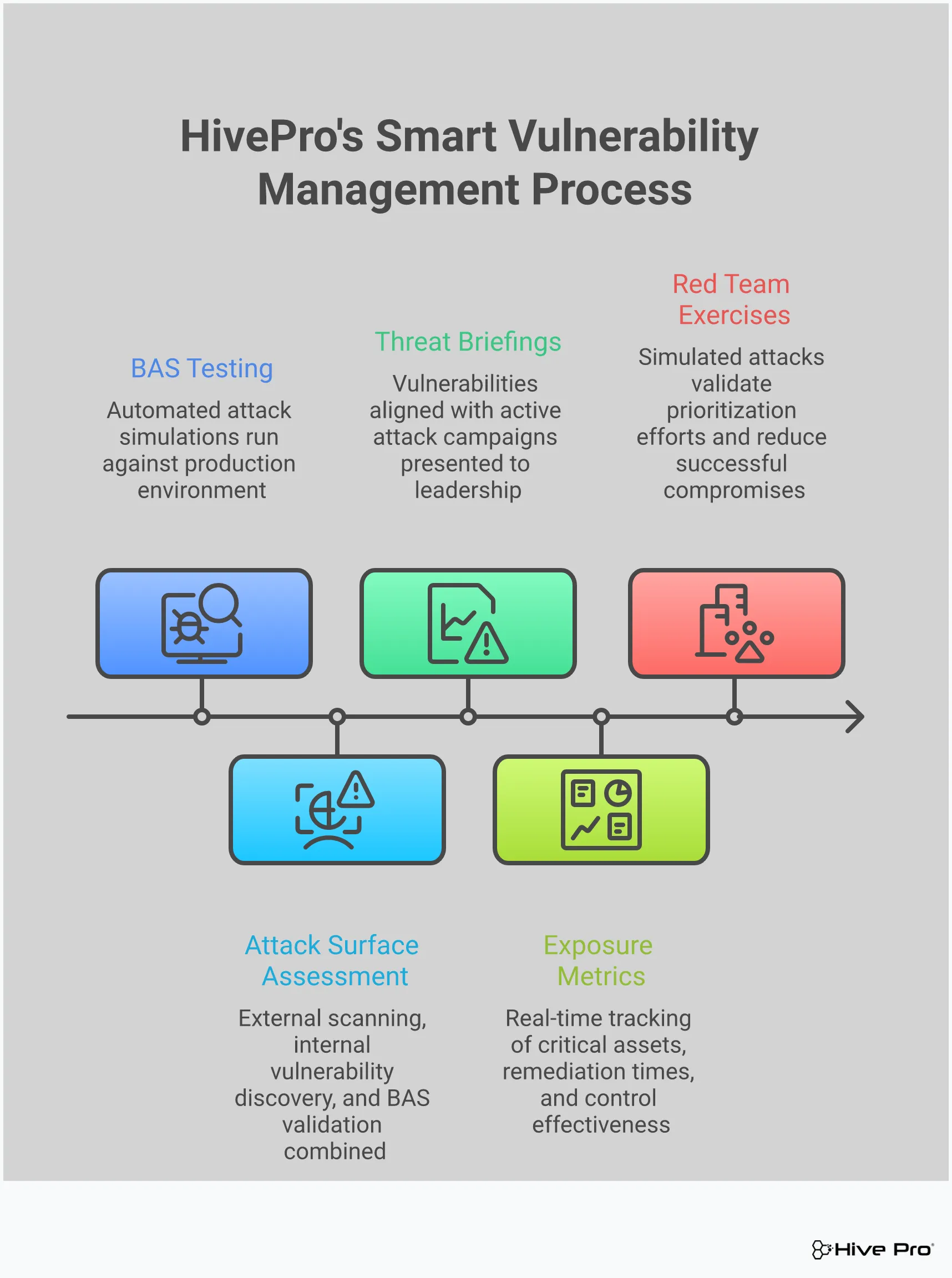
After you’ve assessed your assets and the threat landscape, you might still be left with a long list of “what ifs.” What if an attacker targets this specific server? What if our endpoint protection fails? Relying on vulnerability scores and theoretical models alone can feel like guessing. This is where Breach and Attack Simulation (BAS) comes in, shifting your strategy from passive defense to active testing. Instead of just identifying potential weaknesses, BAS tools let you safely simulate real-world attack scenarios to see how your defenses actually perform.
Think of it as a controlled sparring match against a virtual adversary. These simulations mimic the tactics, techniques, and procedures (TTPs) used by actual threat actors, giving you a clear picture of your security posture. By running these tests, you can validate your security controls, identify hidden gaps in your defenses, and understand your true exposure. This process provides concrete, evidence-based data that cuts through the noise of endless vulnerability alerts. It helps you answer the most critical question: which vulnerabilities create a direct path to my most critical assets? With that knowledge, you can prioritize remediation efforts with confidence, focusing your team’s limited time and resources on the fixes that matter most.
Every security team operates on a set of theories about how their defenses will hold up against an attack. You assume your firewalls are configured correctly and your EDR will catch suspicious activity. Breach and Attack Simulation lets you put those assumptions to the test. By running adversarial exposure validation, you can launch controlled, real-world attack scenarios against your own environment. These aren’t just theoretical exercises; they are practical tests that show you exactly how your security stack responds to specific threats. This allows you to move beyond hoping your defenses work and start proving that they do, providing clear evidence of your security effectiveness and highlighting where improvements are needed.
Vulnerability scans are great at finding known weaknesses in your assets, but they don’t always show you the full picture. An attacker’s path is rarely a straight line; it often involves chaining together multiple lower-risk vulnerabilities or exploiting a simple misconfiguration. BAS helps you see your environment through an attacker’s eyes, revealing the complex attack paths that might otherwise go unnoticed. By simulating attacks, you can pinpoint specific gaps in your security controls, whether it’s a poorly written detection rule, a disabled security feature, or a process failure in your incident response plan. This proactive approach helps you find and fix holes before a real adversary can exploit them.
One of the biggest challenges in vulnerability management is separating the signal from the noise. A vulnerability with a high CVSS score might seem urgent, but if it’s not exploitable in your environment, it’s not an immediate risk. BAS provides a more accurate measure of your organization’s actual exposure by demonstrating what is truly exploitable. This data-driven approach helps you move beyond perceived risk based on generic scores. Instead, you can base your vulnerability and threat prioritization on tangible evidence of what could impact your business. This allows you to focus on the vulnerabilities that pose a clear and present danger, ensuring your remediation efforts have the greatest possible impact.
Trying to manage vulnerabilities without good threat intelligence is like trying to find your way in the dark. You know dangers are out there, but you have no idea where they are or what they look like. Threat intelligence flips on the lights. It provides the context you need to move from a reactive, checklist-based approach to a proactive, threat-informed strategy. Instead of treating every vulnerability as an equally urgent fire to put out, you can focus your resources on the ones that pose a genuine, immediate threat to your organization.
This shift is fundamental. It allows your team to stop chasing every potential weakness and start building a defense against actual attacks. By integrating data on active exploits, attacker techniques, and trending threats, you can make smarter, faster decisions. This is the core of effective vulnerability and threat prioritization, turning an overwhelming list of CVEs into a manageable, actionable plan that directly reduces your organization’s risk. It’s about working smarter, not just harder, to stay ahead of adversaries.
Threat intelligence gives you a look inside the attacker’s playbook. It provides specific details on the tactics, techniques, and procedures (TTPs) that threat actors are using right now. This isn’t just theoretical information; it’s actionable insight into how adversaries compromise networks, move laterally, and achieve their objectives. Understanding these methods allows you to anticipate potential attacks and adjust your defenses accordingly. For example, if you know a certain ransomware group is exploiting a specific vulnerability, you can immediately check your assets and prioritize the patch. This proactive stance is a game-changer, moving you from defense to a more strategic security posture.
Not all vulnerabilities are created equal. While thousands are disclosed every year, only a small fraction are ever actively exploited in the wild. Threat intelligence helps you cut through the noise and concentrate on the vulnerabilities that attackers are actually using. By leveraging real-world data from sources like HiveForce Labs, you can prioritize patching based on evidence of active exploitation. This means your team spends its valuable time fixing the security gaps that matter most, rather than getting bogged down by low-risk vulnerabilities that are unlikely to ever be targeted. This focused approach dramatically improves your security team’s efficiency and effectiveness.
The threat landscape changes constantly. A vulnerability that was low-risk yesterday could become a primary target for attackers tomorrow. This is why real-time data is so critical. By continuously monitoring the threat landscape and correlating that information with your own environment, you can adapt your vulnerability management strategy on the fly. Timely threat advisories and digests provide the up-to-the-minute information needed to address the most pressing risks as they emerge. This dynamic approach ensures your defenses are always aligned with the current reality of the threat landscape, not based on a static snapshot from weeks or months ago.
A solid cyber risk prioritization strategy isn’t a one-and-done project; it’s a continuous program that adapts to your organization and the evolving threat landscape. Building a sustainable program means creating a repeatable, scalable process that consistently reduces your exposure over time. It involves weaving together the right technology, clear metrics, and a collaborative team culture. When these elements work in harmony, you move from constantly fighting fires to proactively managing risk with confidence. This approach ensures your efforts have a lasting impact, making your security posture stronger and more resilient for the long haul.
A sustainable program is built on a cycle of continuous improvement. You identify risks, prioritize them based on real-world data, take action, and then measure the results to refine your approach. It’s about making incremental gains that add up to a significant reduction in overall risk. This requires moving beyond ad-hoc efforts and establishing a formal framework that everyone understands and follows. By embedding prioritization into your daily operations, you create a security-aware culture where risk management is a shared responsibility, not just a task for the security team. This proactive stance is what separates mature security programs from those that are always one step behind attackers.
Your security tools shouldn’t operate in isolation. When your vulnerability scanner, asset inventory, and threat intelligence feeds are disconnected, you get a fragmented view of your risk. A sustainable program starts with a unified platform that brings all your exposure data into one place. Integrating your technology provides real-time, data-driven insights into your cyber risks, giving you a transparent view of your security landscape. Automation is the engine that drives this integration, correlating data from different sources to surface the most critical threats without manual effort. This allows your team to stop wasting time connecting the dots and start focusing on strategic remediation, using quick, quantified metrics to turn complex data into actionable steps.
You can’t improve what you don’t measure. To know if your prioritization program is working, you need to define what success looks like and track it with key metrics. These aren’t just for reports; they are vital signs for your security health. Tracking metrics like mean time to remediate (MTTR), critical vulnerability exposure, security control effectiveness, and incident response times gives you the visibility needed to anticipate threats. These data points help you quantify the likelihood and potential impact of threats, showing you where you’re making progress and where you need to adjust your focus. Consistently measuring these indicators proves the value of your program to leadership and helps secure the resources you need to keep it running effectively.
Technology and metrics are crucial, but a prioritization program is ultimately driven by people. A sustainable strategy requires breaking down silos and aligning your security, IT, and development teams around shared goals. This means investing in a comprehensive cybersecurity strategy that includes clear policy development, regular training, and open communication channels. When remediation teams understand the context behind a high-priority vulnerability, they are more likely to act quickly. By creating a culture where everyone understands their role in risk mitigation, your organization can better anticipate threats and implement effective plans. This collaborative approach turns prioritization into a continuous cycle of assessment, action, and refinement, building long-term resilience.
My team already uses CVSS scores for prioritization. Why isn’t that enough? CVSS scores are a fantastic starting point for understanding the technical severity of a vulnerability, but they don’t tell the whole story. A high CVSS score on a test server that isn’t connected to anything important is far less risky than a medium-score vulnerability on your main customer database. Effective prioritization adds two crucial layers on top of CVSS: business context, which tells you how critical the affected asset is, and threat intelligence, which tells you if attackers are actively exploiting the vulnerability in the wild.
What’s the real difference between identifying vulnerabilities and understanding my actual exposure? Identifying a vulnerability is like knowing you have an unlocked door in your house. Understanding your exposure is knowing that someone is actively walking down your street checking for unlocked doors. A vulnerability scan gives you a list of potential problems, but tools like Breach and Attack Simulation and real-time threat intelligence show you which of those problems create a direct, exploitable path to your most important assets. This shifts your focus from theoretical weaknesses to tangible, immediate threats.
Our security and IT teams are always at odds over patching. How can a better prioritization strategy help? This is a classic challenge, and it often comes down to a communication gap. A strong prioritization framework creates a shared language based on risk to the business. Instead of the security team simply saying a patch is “critical,” they can provide concrete data: “This specific vulnerability on our payment processing server is being used by a known ransomware group, and a breach could halt our revenue.” When IT and operations teams see the clear business impact, it reframes the conversation from a routine task to a shared effort in protecting the organization.
How does threat intelligence practically change our day-to-day vulnerability management? Threat intelligence transforms your team’s daily to-do list from overwhelming to manageable. Without it, your team might be looking at a report with thousands of vulnerabilities, trying to decide where to begin. With good threat intelligence, that list gets filtered down to the handful of vulnerabilities that are being actively used in real-world attacks right now. It allows your team to stop chasing every potential issue and focus their limited time and energy on fixing the security holes that present a clear and present danger.
This all sounds great, but where do I start if my program is still very reactive? The best first step is to gain complete visibility of your environment. You can’t protect what you don’t know you have, so begin by creating a comprehensive and continuously updated inventory of all your digital assets, from servers and laptops to cloud services and applications. Once you have a clear map of your attack surface, you can begin to identify which assets are most critical to your business operations. This foundational step makes every subsequent part of prioritization, from scoring to remediation, more accurate and effective.