Comprehensive Threat Exposure Management Platform
 Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the Report
Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the ReportAttackers don’t care about your massive backlog of “critical” vulnerabilities. They look for the path of least resistance—the one exploitable weakness that gives them a foothold into your network. If your vulnerability management program isn’t thinking like an attacker, you’re always one step behind. Relying on static severity scores alone leaves you blind to the real-world tactics threat actors are using right now. To learn how to prioritize vulnerabilities effectively, you must see your environment through their eyes. This means leveraging active threat intelligence and simulating attack paths to find the flaws that are not just severe, but actively exploitable. This guide will show you how.
If your security team is trying to fix every single vulnerability, you’re fighting a losing battle. The sheer volume of flaws discovered by scanners is overwhelming, and the truth is, not all of them pose a real threat to your organization. This is where vulnerability prioritization comes in. It’s the process of systematically identifying which vulnerabilities to fix first based on a range of factors, not just a generic severity score. Think of it as a triage system for your digital environment.
Effective vulnerability and threat prioritization moves you from a state of constant reaction to one of strategic action. Instead of just looking at a vulnerability’s CVSS score, this approach considers its real-world context. Is it actively being exploited by attackers? Does it exist on a business-critical asset? Could it be part of a larger attack chain? Answering these questions helps you focus your limited time and resources on the issues that present the most significant risk to your business. It’s about working smarter, not just harder, to meaningfully reduce your threat exposure.
For years, the standard approach to vulnerability management was simple: scan, find, and try to fix everything, usually starting with the “criticals.” This reactive model creates a never-ending backlog that security and IT teams can’t possibly clear. The result? Talented professionals spend their days chasing down low-risk issues while truly dangerous vulnerabilities get lost in the noise. It’s like trying to patch hundreds of tiny cracks in a dam while ignoring the one that’s about to burst.
This approach is not only inefficient but also dangerous. Attackers thrive on this chaos. They don’t need to invent complex, new exploits when they know most organizations haven’t patched well-known vulnerabilities that are easy to leverage. When your team is overwhelmed by volume, they can’t focus on the threats that attackers are actively using. This constant state of reaction leads to team burnout and leaves your most critical assets exposed.
A modern, effective vulnerability management program shifts the focus from the volume of vulnerabilities to the value of remediation. The goal isn’t to patch the most vulnerabilities; it’s to reduce the most risk. This requires understanding that a “medium” severity vulnerability on your company’s crown-jewel database is far more important than a “critical” one on an isolated development server. It’s all about context.
By focusing on value, you empower your team to make intelligent decisions. This means concentrating remediation efforts on weaknesses that are actively exploited, protect your most critical assets, and could cause the most damage to your business operations. This risk-based approach ensures your security resources are used wisely, addressing the threats that truly matter. It transforms your program from a simple box-checking exercise into a strategic function that directly protects the business and its total attack surface.
Deciding which vulnerability to fix first can feel like a high-stakes game of whack-a-mole. When you’re staring at a list of thousands of potential weaknesses, where do you even begin? The key is to move beyond a single metric and adopt a multi-faceted approach. Effective prioritization isn’t about the sheer number of vulnerabilities you close; it’s about closing the right ones. This means looking at a combination of factors to build a clear, contextual picture of your actual risk. By layering these different lenses, you can focus your team’s valuable time and resources on the threats that truly matter to your organization.
Severity scores are often the first data point teams look at, and for good reason. The Common Vulnerability Scoring System (CVSS) gives you a standardized numerical score indicating how severe a vulnerability could be. It’s a helpful starting point for sorting a massive list. However, relying on CVSS alone can be misleading. A vulnerability with a 9.8 “critical” score might exist on an isolated, non-essential test server, posing little real-world danger to your business. Conversely, a “medium” vulnerability on a critical, internet-facing system could be a much bigger problem. These scores are a crucial piece of the puzzle, but they lack the context of your specific environment.
This is where you answer the question, “If this asset was compromised, how bad would it be?” Not all assets are created equal. A vulnerability on your primary e-commerce database is infinitely more critical than one on a developer’s sandboxed laptop. To prioritize effectively, you must understand which systems are essential for your company’s operations. Consider the potential business impact of an exploit: Would it cause a service outage, lead to significant financial loss, or result in a compliance failure? Mapping vulnerabilities to your most critical assets helps you see which weaknesses pose a direct threat to your bottom line and business continuity.
A vulnerability is just a potential weakness until a threat actor decides to exploit it. This is why active threat intelligence is a game-changer for prioritization. By integrating real-world data on which vulnerabilities are being actively exploited in the wild, you can separate theoretical risks from immediate threats. Threat actors don’t target every vulnerability—they focus on the ones that offer the best return on their effort. Your team should, too. Using up-to-date intelligence from sources like HiveForce Labs allows you to focus on the vulnerabilities that attackers are using right now, helping you stay ahead of emerging campaigns.
Finally, you need to pull all these factors together and apply them to your specific environment. Your organization’s security posture is unique. A vulnerability might be technically exploitable, but a compensating control you have in place—like a web application firewall (WAF) or strict network segmentation—could make a successful attack highly unlikely. Understanding your total attack surface is essential. This means considering how different assets are connected, what security controls are in place, and what potential attack paths exist within your network. This final layer of context ensures your prioritization is based on the actual risk to your business, not just generic scores.
Raw vulnerability data is just noise. The real skill is turning that noise into a clear signal of actual risk. This isn’t about just looking at a CVSS score and calling it a day. True risk assessment is a more nuanced process that balances technical details with real-world implications for your business. It involves asking smarter questions: How likely is this vulnerability to be exploited? What path would an attacker take to get to our most critical assets? And what would the damage be to our business if they succeed? Answering these questions accurately is the core of effective threat exposure management.
By looking at vulnerabilities through these three lenses—likelihood versus impact, potential attack paths, and business context—you can move from a chaotic “fix everything” mindset to a focused, strategic approach. This method helps you pinpoint the threats that genuinely threaten your organization, allowing your team to direct their limited time and resources where they’ll have the greatest effect. It’s the difference between being busy and being effective, and it’s how you transform a reactive vulnerability management program into one that proactively reduces exposure.
This is the foundational question of risk assessment. On one side, you have likelihood: How probable is it that an attacker will exploit this specific weakness? This considers factors like the complexity of the exploit and, most importantly, whether threat actors are actively using it in the wild. On the other side is impact: If an attacker succeeds, how bad will the damage be? This could mean anything from operational downtime and financial loss to a full-blown data breach. Your highest priorities are the vulnerabilities where high likelihood and high impact intersect. A risk-based approach helps you filter out the noise of low-impact or hard-to-exploit flaws so you can focus on the clear and present dangers.
Vulnerabilities rarely exist in a vacuum. Attackers often chain together multiple, seemingly minor weaknesses to reach a high-value target. That’s why you have to think like an attacker and map out potential attack paths. A low-severity vulnerability on a public-facing web server might seem trivial, but if it gives an attacker a foothold to pivot to a critical database server, its risk profile changes completely. Understanding how your assets are connected is crucial. By visualizing these connections, you can see how a small crack can lead to a catastrophic failure, helping you prioritize the initial entry points that enable larger attacks and manage your total attack surface.
A vulnerability’s risk is directly tied to the asset it affects. A critical flaw on a developer’s test machine simply doesn’t carry the same weight as the same flaw on your primary revenue-generating application. This is where business context comes in. You need to ask: What does this system do for the business? Does it store sensitive customer data? Is it essential for daily operations? Does it fall under specific compliance regulations like PCI DSS or HIPAA? Layering this business intelligence over your technical vulnerability data is what separates a good vulnerability management program from a great one. It ensures you’re always protecting what matters most to the organization.
When you’re staring at a list of thousands of vulnerabilities, you need a system to sort through the noise. Over the years, several frameworks have emerged to help teams do just that. The reality is that no single framework is a magic bullet. The most effective strategies borrow the best elements from each one to create a hybrid model that fits the unique needs of your organization. Think of these frameworks not as competing options, but as different lenses you can use to view the same problem. By understanding what each one brings to the table—from static severity scores to real-time threat data—you can build a prioritization process that is both logical and defensible. Let’s walk through the major frameworks you’ll encounter and see how they stack up.
The Common Vulnerability Scoring System (CVSS) is often the first stop for any vulnerability management team. It provides a standardized numerical score from 0 to 10 to rate the technical severity of a vulnerability. This gives you a consistent, universal language for discussing how technically dangerous a flaw is. However, relying solely on CVSS is a common pitfall. While the scores show how severe a weakness is in a vacuum, they don’t tell you if it’s a genuine risk to your company. A high CVSS score doesn’t mean attackers are actively using it, nor does it consider the importance of the asset it affects. It’s a critical data point, but it should be a starting point for your analysis, not the final word.
If CVSS tells you how bad a vulnerability could be, the Exploit Prediction Scoring System (EPSS) tells you how likely it is to be exploited. EPSS provides a probability score, from 0% to 100%, on the chances that a vulnerability will be exploited in the wild within the next 30 days. This adds a much-needed layer of timeliness to your prioritization. A vulnerability with a moderate CVSS score but a high EPSS score might deserve your attention far more urgently than a critical one that attackers are ignoring. Using EPSS helps you shift your focus from theoretical severity to the practical likelihood of an attack, allowing you to address the threats that pose the most immediate danger.
A risk-based approach moves the conversation beyond the vulnerability itself and connects it to your business. This framework combines technical severity with the criticality of the asset involved. After all, risk is a function of both likelihood and impact. A critical vulnerability on an isolated, non-essential laptop is a much lower priority than a medium-severity flaw on your primary financial database. To do this well, you need a clear inventory of your assets and an understanding of their business value. By applying this context, you can create a vulnerability and threat prioritization strategy that directs your resources toward protecting what truly matters to the organization.
Threat-informed prioritization is the most proactive strategy, as it uses real-world intelligence to guide your efforts. This approach focuses on vulnerabilities that are actively being exploited by threat actors, especially those targeting your industry or region. It answers the crucial question: “What are the attackers actually doing right now?” By leveraging up-to-date threat advisories and intelligence, you can concentrate on closing the security gaps that adversaries are most likely to use against you. This method helps you see your environment from an attacker’s perspective, identifying and fortifying the most probable paths they would take to reach your critical assets.
If you feel like you’re drowning in a sea of vulnerabilities, threat intelligence is the lifeline you need. It’s the crucial context that transforms a long list of CVEs from a theoretical problem into a manageable, prioritized action plan. Instead of just asking, “Is this vulnerability severe?” you can start asking, “Is anyone actually exploiting this vulnerability against companies like mine?” This shift is fundamental to building a proactive security posture.
By integrating real-world threat data, you move beyond static scores and start seeing your environment through an attacker’s eyes. You gain insight into which vulnerabilities are being actively used in attacks, which threat actors are using them, and what their targets are. This intelligence allows your team to focus its limited time and resources on fixing the issues that pose a genuine, immediate threat to your organization. It’s the difference between patching everything and patching what truly matters right now, making your entire vulnerability and threat prioritization process smarter and more efficient.
A high CVSS score doesn’t always mean a high real-world risk. Many critical vulnerabilities are difficult to exploit and are never used in a widespread attack. On the other hand, a medium-severity vulnerability with a publicly available exploit code can become a massive problem overnight. This is where real-world exploit data comes in. By using up-to-date information on how attackers are currently operating, you can pinpoint which vulnerabilities are being actively weaponized. This allows you to address the most critical threats swiftly, even if their base scores don’t scream “urgent.” This data-driven approach ensures your team is always focused on the vulnerabilities that present a clear and present danger, not just a theoretical one.
Not all threats are created equal, and not all attackers are interested in your organization. Threat intelligence helps you understand the tactics, techniques, and procedures (TTPs) of specific threat actor groups, including which industries they target and what vulnerabilities they prefer to exploit. If a threat group known for targeting financial institutions is actively using a specific exploit, and you work for a bank, that vulnerability’s priority should be at the top of your list. By analyzing who is behind the attacks, you can better predict which of your weaknesses are most likely to be targeted next. This insight comes from dedicated research teams like HiveForce Labs, which provide the context needed to make these critical decisions.
The threat landscape is constantly changing, with new vulnerabilities and exploits emerging daily. A static prioritization strategy simply can’t keep up. Timely threat intelligence gives you an early warning system for zero-day threats and newly discovered attack vectors. Instead of waiting for a vendor patch or the next scheduled scan, you can get ahead of the curve. This allows you to implement compensating controls or prepare for rapid patching as soon as a fix is available. Staying informed with regular updates, like those found in threat digests, ensures your vulnerability management program is agile and can adapt to new threats the moment they appear, minimizing your window of exposure.
Ultimately, the goal of threat intelligence is to create focus. Security teams are almost always under-resourced, and it’s impossible to fix every single vulnerability. An intelligence-driven approach helps you cut through the noise and concentrate your efforts where they will have the greatest impact. By combining data on active exploits, threat actor TTPs, and emerging threats, you can build a prioritization model that reflects your unique risk profile. This ensures your security efforts are directly aligned with the real-world threats you face, making your program more effective and defensible. This is a core principle of a modern Threat Exposure Management platform, which helps you confidently address your most significant risks.
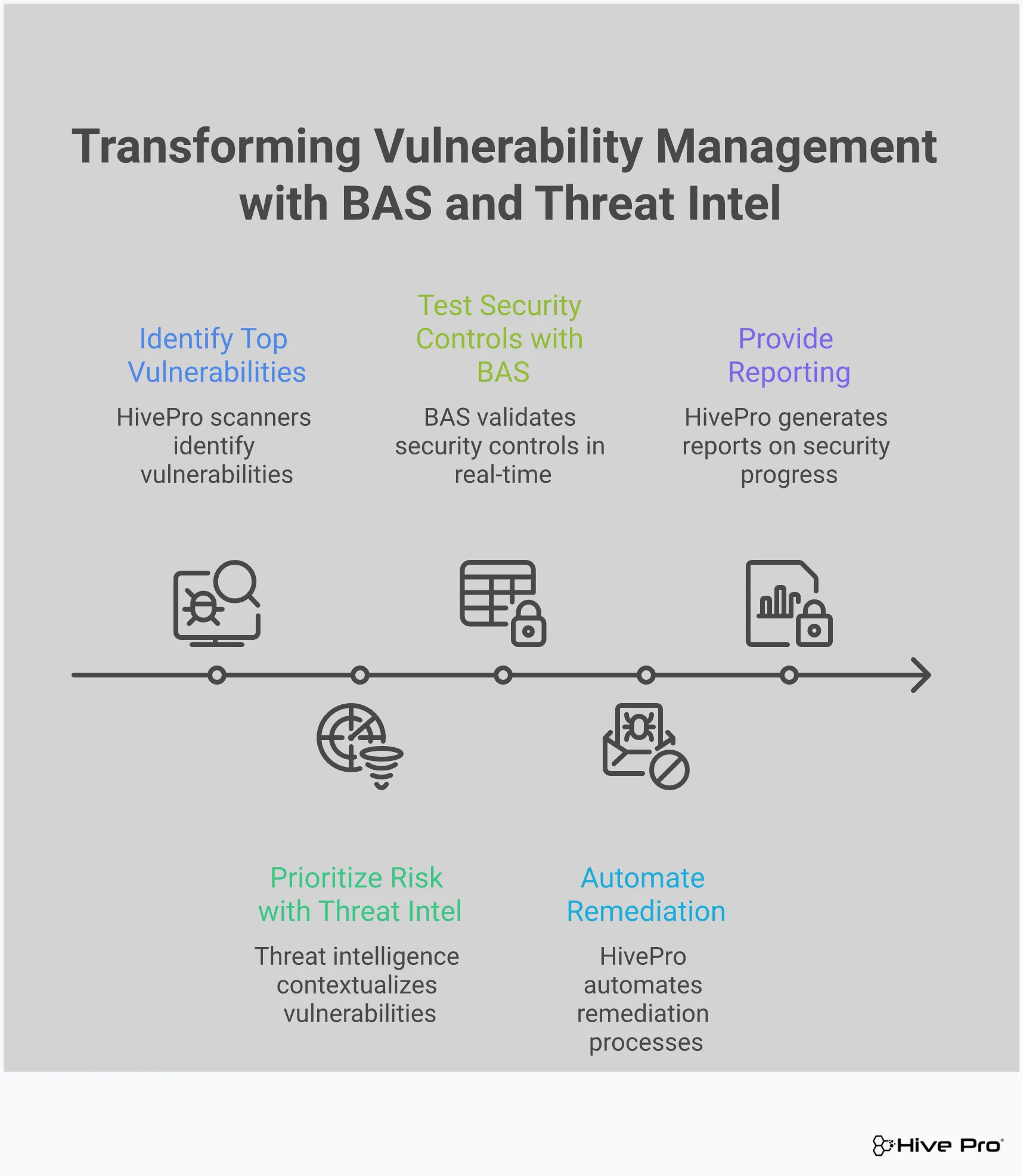
Let’s be honest: a long list of vulnerabilities with high CVSS scores can feel overwhelming. How do you know which ones pose a genuine, immediate threat to your organization? This is where Breach and Attack Simulation (BAS) changes the game. Instead of relying on theoretical risk scores, BAS platforms actively test your defenses by simulating the same tactics, techniques, and procedures (TTPs) that real-world attackers use. It’s like having a dedicated red team on staff, constantly and safely probing your systems for exploitable weaknesses.
This proactive approach moves your vulnerability management program from a reactive, list-checking exercise to a strategic, evidence-based operation. By running these simulations, you get concrete answers to critical questions: Is this vulnerability actually exploitable in our environment? Are our security controls configured correctly to stop an attack? Where are the gaps in our defenses that an attacker could slip through? This process of adversarial exposure validation provides the context you need to stop guessing and start focusing your resources on the risks that truly matter, making your entire security posture stronger and more resilient.
A high CVSS score doesn’t automatically mean a vulnerability is a ticking time bomb for your specific setup. Your unique configuration, compensating controls, or network segmentation might render it non-exploitable. Breach and attack simulation tools cut through the noise by attempting to exploit vulnerabilities in a safe, controlled manner. This allows you to validate the exploitability within your own environment. Instead of working from a theoretical assessment, you get definitive proof of which vulnerabilities pose a clear and present danger, allowing your team to prioritize with confidence and precision.
You’ve invested heavily in firewalls, EDR solutions, and other security tools, but are they working as expected? BAS helps you answer that question by putting your defenses to the test. By simulating real-world attack scenarios against known vulnerabilities, you can see exactly how your security stack performs. This proactive testing reveals misconfigurations, policy gaps, or tools that aren’t providing the protection you thought they were. It gives you the hard data needed to fine-tune your controls and ensure your defenses can actually withstand an attack before a real one occurs.
The threat landscape is constantly changing, and so is your IT environment. A security posture that was strong yesterday might have a critical gap today. This is why continuous validation is so important. BAS platforms automate the process of regularly testing your defenses against the latest threats and vulnerabilities. This creates a cycle of continuous improvement, ensuring you are always aware of your current security posture. By regularly testing for exploitability, your team can adapt quickly to new threats and maintain a robust, resilient defense against potential breaches on your entire attack surface.
One of the biggest challenges in vulnerability management is alert fatigue. When your team is buried under a mountain of potential threats, it’s easy for a critical one to get missed. BAS helps solve this by providing a clear signal through the noise. By focusing on vulnerabilities that have been proven exploitable in your environment, it effectively filters out the theoretical risks and low-priority alerts. This allows your security team to stop chasing ghosts and concentrate their valuable time and energy on remediating the vulnerabilities that pose a genuine threat to the organization.
Having a solid framework for prioritization is one thing, but putting it into practice requires the right technology. The days of juggling spreadsheets and manually cross-referencing threat feeds are over. Modern tools are designed to automate the heavy lifting, giving your team the clarity needed to act decisively. The most effective solutions bring scanning, intelligence, and risk assessment together into a single, cohesive view, helping you manage the entire exposure lifecycle. A unified threat exposure management platform can replace a disjointed collection of point solutions, providing a single source of truth for your security posture.
Everything starts with visibility. You can’t prioritize what you can’t see. Automated scanning and assessment platforms are the foundation of any vulnerability management program, acting as your eyes across the entire digital landscape. These tools continuously search for weaknesses in your systems, applications, and cloud environments. The best platforms provide a comprehensive view of your total attack surface, using techniques like agentless scanning to discover assets and vulnerabilities quickly without requiring software installation on every device. This foundational data feeds every other step of the prioritization process.
Once scanners identify vulnerabilities, threat intelligence provides the critical context to understand which ones truly matter. This isn’t just a “nice-to-have”—it’s essential for cutting through the noise. By integrating real-time data on attacker tactics and active exploits, you can see which vulnerabilities are being used in campaigns right now. This allows you to focus on the weaknesses that pose an immediate danger. In-house research from teams like HiveForce Labs delivers curated intelligence that helps you spot emerging threats and fix the riskiest flaws before they can be widely exploited.
A long list of “critical” vulnerabilities isn’t an action plan. This is where risk calculation engines come in. These tools move beyond static severity scores by combining vulnerability data with asset criticality and active threat intelligence. Instead of just looking at the technical severity of a flaw, a risk-based approach helps you understand its potential business impact. This is the core of smart vulnerability and threat prioritization, as it synthesizes multiple data points to generate a truly customized risk score that reflects what’s most important to your organization.
Finding and prioritizing vulnerabilities is pointless if they never get fixed. Remediation tracking systems close the loop by integrating with your IT and DevOps workflows. These tools help you manage and accelerate the fixing process by automating ticket creation, assigning tasks to the right teams, and monitoring progress toward resolution. By streamlining these handoffs, you can ensure that high-priority issues are addressed quickly and efficiently. This operational efficiency is key to reducing your overall exposure and making your prioritization efforts count.
Even with the best intentions, vulnerability prioritization can quickly go off the rails. Many security teams find themselves stuck in a cycle of chasing high-severity scores and struggling to show meaningful risk reduction. This often happens because they’ve fallen into a few common traps that prevent them from seeing the full picture of their exposure. The goal isn’t just to patch vulnerabilities; it’s to reduce the likelihood of a successful attack. To do that, you need to avoid the mistakes that lead to wasted effort and lingering risk.
Shifting from a volume-based patching frenzy to a risk-based strategy requires a clear understanding of what not to do. It means moving beyond static scores and embracing a more dynamic, context-aware approach. By recognizing these common pitfalls, you can refine your process, focus your team’s efforts where they matter most, and build a more resilient security posture. A modern threat exposure management platform is designed to help you sidestep these issues by providing a unified view of your assets, threats, and business context, guiding you toward the fixes that truly count.
The Common Vulnerability Scoring System (CVSS) is a great starting point, but it should never be the final word on priority. A high CVSS score indicates the potential severity of a vulnerability in a vacuum, not its actual risk to your organization. For example, a vulnerability with a 9.8 CVSS score on an isolated, non-critical test server is far less urgent than a 7.5 on your primary, customer-facing database.
Teams that treat their CVSS report as a simple to-do list often spend countless hours patching issues that pose little real-world threat. This is because CVSS lacks critical context about your specific environment. True vulnerability and threat prioritization requires looking beyond the score to see how a weakness actually impacts your unique attack surface.
What happens if this asset goes down? That’s the question you should be asking, but it’s one that gets ignored far too often. Prioritizing without considering business impact is like a doctor treating a patient’s symptoms without knowing their medical history. You might fix a problem, but it may not be the most pressing one. You need to understand which systems are critical for revenue, operations, and data protection.
A moderate vulnerability on a server that processes all your financial transactions is infinitely more important than a critical one on a marketing team’s internal blog. By mapping vulnerabilities to asset criticality, you can ensure your remediation efforts are aligned with protecting what matters most to the business. This context transforms your prioritization from a technical exercise into a strategic business function.
A vulnerability is just a weakness; a threat is what makes it dangerous. Without up-to-date threat intelligence, you’re essentially guessing which vulnerabilities an attacker might use. Threat actors don’t care about CVSS scores; they care about what works. They follow the path of least resistance, targeting known vulnerabilities with readily available exploits.
Integrating real-world threat data shows you which vulnerabilities are being actively exploited in the wild. This intelligence, often curated by research teams like HiveForce Labs, helps you focus on the imminent dangers rather than the theoretical ones. A lower-severity vulnerability with a public exploit and active chatter on dark web forums should jump to the top of your list, well ahead of a critical vulnerability that is difficult to exploit and has no known attacks.
Vulnerability management isn’t just a security problem; it’s an organizational one. The most common point of failure is the handoff between the security team that finds the vulnerability and the IT or development team that has to fix it. When security simply “throws a report over the wall,” it creates friction, delays, and frustration. The remediation team has its own priorities and may not understand the urgency or context behind the request.
Building a successful program requires breaking down these silos. Create a shared process where security, IT, and development teams work together to assess risk and plan remediation. When everyone understands the business impact and the threat landscape, you can create a collaborative workflow that ensures critical vulnerabilities are addressed quickly and efficiently, without the usual back-and-forth.
Knowing which vulnerabilities to fix is one thing; actually getting them fixed is another. Building a solid, repeatable process is what separates effective teams from those who are constantly putting out fires. It’s about creating a system that works for everyone, from the security analysts who find the flaws to the IT and development teams who patch them. A well-defined process ensures that critical vulnerabilities are handled swiftly and that nothing falls through the cracks. It brings order to the chaos by setting clear expectations, defining responsibilities, and creating a feedback loop for getting better over time. Here’s how you can build a process that sticks.
Before you can prioritize anything, you need to agree on what “important” actually means. This starts with establishing clear criteria for how you score and rank vulnerabilities. While CVSS scores are a useful starting point for understanding severity, they don’t tell the whole story. Your criteria should also factor in exploitability—is there known exploit code in the wild? Is it easy for an attacker to use this flaw?
Your scoring model should also weigh the business context of the affected asset. A medium-severity vulnerability on a critical, internet-facing server is likely more urgent than a critical one on an isolated test machine. Document these criteria and create a simple scoring system that produces a clear vulnerability and threat prioritization rank. This ensures everyone is working from the same playbook.
Vulnerability management is a team sport. Your security team can identify risks all day, but they often rely on IT operations or development teams to implement the fix. This is where so many programs break down. To avoid friction, you need to create clear, cross-functional workflows that define how information is shared and how handoffs occur.
Map out the entire process, from detection to remediation. Who is responsible for validating a vulnerability? Who opens the ticket? Who deploys the patch? Getting buy-in from all involved teams is essential. When engineering, security, and IT teams work together and have a unified view of cyber risks, the remediation process becomes faster and more efficient. This collaborative approach ensures everyone understands their role and the importance of their contribution.
What happens when you find a five-alarm fire? You need a playbook. Defining clear escalation and remediation procedures ensures that the most critical vulnerabilities get immediate attention. This means creating Service Level Agreements (SLAs) for different priority levels. For example, a critical vulnerability might require a ticket to be opened within one hour and a patch deployed within 24 hours, while a low-priority issue might have a 90-day window.
Your procedure should detail the exact steps to take, including who needs to be notified and how to track the issue. Always use a ticketing system to create an audit trail. This isn’t about assigning blame; it’s about ensuring accountability and having a record that you reported the problem. Clear procedures remove ambiguity and empower your teams to act decisively.
Your vulnerability management process shouldn’t be set in stone. The threat landscape is constantly changing, and your process needs to adapt with it. Schedule regular reviews—quarterly is a good cadence—to assess what’s working and what isn’t. Are your teams meeting their SLAs? Are there bottlenecks in the workflow? Use this time to refine your criteria, update your procedures, and incorporate feedback from all teams.
Part of this cycle involves verification. Don’t just assume a patch was successful. Your process should include a step to rescan and confirm that the vulnerability is gone. You should also check for any previously fixed vulnerabilities that have reappeared. A continuous improvement mindset helps you strengthen your defenses over time and maintain a clear picture of your total attack surface.
Identifying and prioritizing vulnerabilities is only half the battle. The other half—and often the more challenging part—is communicating those priorities to get the necessary buy-in and action from other teams. If your carefully crafted priority list sits in a spreadsheet, it’s not reducing any risk. Effective communication turns your analysis into action, ensuring that executives understand the business implications and technical teams have the clear guidance they need to remediate threats.
The key is to tailor your message to your audience. Executives don’t need to know the technical details of a CVE, but they do need to understand the potential impact on revenue or reputation. Likewise, developers need specific, actionable information, not high-level business metrics. Using a platform that provides a unified view of cyber risks can be a game-changer, creating a single source of truth that helps bridge the gap between technical findings and business context. This ensures everyone is working from the same information, which streamlines the entire remediation process.
When you’re presenting to leadership, your goal is to translate technical risk into business impact. Forget about CVSS scores and complex exploit chains. Instead, focus on what matters to them: potential financial loss, operational disruption, and reputational damage. Use clear visuals, dashboards, and executive summaries that get straight to the point. Frame your reports around key performance indicators that align with business objectives. And remember to always document your findings. Opening a ticket for every reported vulnerability isn’t just about process; it protects you and your team. It creates a paper trail that demonstrates due diligence, which is invaluable during audits and proves your team is actively managing risk.
Working with engineering, development, and IT teams requires a different approach. These are the people on the front lines who will be implementing the fixes, and they need clear, concise, and actionable information. Simply handing them a list of CVEs isn’t helpful. Your report should include the exact location of the vulnerability, the affected assets, and specific remediation guidance. Getting different teams to work together can be tough, so it’s crucial to build a collaborative relationship. Frame the work as a shared responsibility for securing the company’s assets. Integrated ticketing systems and clear workflows are essential for tracking progress and ensuring nothing falls through the cracks.
Setting realistic timelines is critical for a successful vulnerability management program. Not every vulnerability requires an immediate, all-hands-on-deck response. Your remediation timelines should directly reflect your prioritization framework. Critical, actively exploited vulnerabilities might require a 24-hour turnaround, while many other serious issues have a standard fix time of around 30 days. It’s important to establish these Service Level Agreements (SLAs) in collaboration with the technical teams who will be doing the work. This ensures the timelines are achievable and creates shared ownership over the remediation process. A solid vulnerability and threat prioritization strategy provides the foundation you need to set these deadlines confidently.
True alignment happens when everyone, from the C-suite to the DevOps team, understands their role in managing risk. This requires continuous communication and a shared language. A great first step is to talk to business leaders to understand the potential cost and impact of each weakness. This context is invaluable for both prioritizing vulnerabilities and for making a compelling case for remediation resources. Regular meetings, consistent reporting formats, and a centralized platform where all stakeholders can view the same data are key. When everyone is looking at the same picture of the organization’s threat exposure, it’s much easier to agree on priorities and work together toward the common goal of reducing risk.
Why can’t I just focus on fixing all my ‘critical’ vulnerabilities first? Focusing only on critical-rated vulnerabilities sounds logical, but it often leads to wasted effort. A vulnerability’s score doesn’t account for your specific environment. You might spend weeks patching a “critical” flaw on an isolated test server that poses no real danger, while a “medium” flaw on your main payment server gets ignored. A smarter approach considers the business impact of the asset and whether attackers are actively exploiting the weakness, ensuring you fix the problems that present a genuine threat to your business.
My team is still just using CVSS scores. What’s the first practical step to improve our process? The best first step is to add a layer of business context. You don’t need a complex new tool to start. Begin by identifying your most critical assets—the servers, applications, and databases that are essential to your operations. Start mapping your vulnerabilities to these assets. This simple action immediately helps you see which flaws, regardless of their score, pose the most significant risk. It shifts the conversation from “how severe is this flaw?” to “how much would this hurt us?”
How is a threat-informed approach different from a risk-based one? Think of it as the difference between knowing a door is unlocked and knowing a burglar is actively checking the doors on your street. A risk-based approach combines a vulnerability’s severity with the importance of the asset it’s on—that’s the unlocked door. A threat-informed approach adds real-time intelligence, telling you which unlocked doors burglars are actually using right now. It uses data on active exploits and attacker campaigns to help you prioritize the weaknesses that are most likely to be targeted.
How does Breach and Attack Simulation (BAS) actually help with prioritization? Breach and Attack Simulation gives you proof instead of just theory. A vulnerability scanner tells you a window might be unlocked, but a BAS platform will safely and automatically check if someone can actually open it and climb through. By simulating real attack techniques, it validates whether a vulnerability is truly exploitable in your specific environment. This helps you filter out the noise of theoretical risks and focus your team’s time on fixing the flaws that have a confirmed path for an attacker to follow.
Our IT and security teams don’t always see eye-to-eye. How can we get them on the same page for remediation? This is a classic challenge, and the key is to create a shared sense of purpose. Instead of just sending over a list of vulnerabilities, work with the IT team to establish clear, agreed-upon timelines for different priority levels. Use a unified platform where both teams can see the same risk data, asset information, and remediation status. When the IT team understands the business context—that this isn’t just another security task, but a direct protection for a critical business function—collaboration becomes much smoother.