Comprehensive Threat Exposure Management Platform
 Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the Report
Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the ReportThere’s often a huge gap between knowing about a threat and knowing if you’re protected from it. A threat feed might tell you about a new attack campaign, but that information lives in a report. It doesn’t tell you what would happen if that same attack hit your network. This is the difference between theory and reality. Actionable threat intelligence, like the research provided by HiveForce Labs, gives you the context to understand what attackers are doing. Breach and Attack Simulation (BAS) then lets you take that context and apply it directly to your environment, safely running simulations to see where your defenses bend or break. This guide shows you how to connect these two powerful tools to close that gap and turn abstract threat data into concrete security improvements.
Behind every smart security decision is even smarter intelligence. That’s where HiveForce Labs comes in. It’s our in-house threat intelligence and research division, dedicated to uncovering threats so you can address them before they become problems. This team of security experts works around the clock to provide the context you need to move from simply managing vulnerabilities to actively reducing your threat exposure. Think of them as your dedicated research team, constantly scanning the horizon for what’s next so you can stay focused on what’s now.
The primary mission of HiveForce Labs is to keep your security team one step ahead of attackers. Instead of just reacting to alerts, you get access to proactive intelligence that helps you anticipate the next move. The team provides real-time alerts, expert analysis, and daily threat warnings designed to strengthen your security posture. This continuous stream of information allows your team to understand emerging dangers and respond with speed and confidence. It turns threat data into a strategic advantage for your organization, helping you make informed decisions that protect your most critical assets.
This isn’t a one-size-fits-all operation. HiveForce Labs is composed of four distinct teams, each focusing on a critical piece of the threat landscape to provide comprehensive coverage. This specialized structure ensures you get deep, relevant insights across the board.
The intelligence from HiveForce Labs isn’t just for reports; it’s the fuel for our Uni5 Xposure Platform. This direct integration means the platform is always armed with the latest threat context. It uses this intelligence to pinpoint where your organization is exposed to active threats, test how well your security controls would hold up against an attack, and guide your teams in fixing the most critical exposure points first. This seamless connection transforms raw data into a clear, actionable path for reducing risk across your entire attack surface, ensuring your efforts are always focused on the threats that matter most.
Think of HiveForce Labs as your dedicated threat research partner, working around the clock to uncover the risks that could impact your organization. The intelligence we gather isn’t just a list of potential problems; it’s a curated stream of actionable insights designed to help you make smarter, faster security decisions. Our research covers everything from emerging zero-day threats to the specific tactics used by cybercriminals. This information is the foundation of a proactive security strategy, helping you understand not just what to fix, but why it matters right now. By translating raw data into clear context, we give your team the clarity needed to focus on the threats that pose a genuine risk to your business.
To stay ahead, you need a constant flow of reliable information. HiveForce Labs delivers exactly that, providing real-time alerts and daily briefings that cut through the noise. We help your security team stay informed about the latest online threats with expert analysis and timely warnings. This isn’t just about sending notifications; it’s about strengthening your security posture by giving you the context to react quickly and effectively to new dangers. When a critical vulnerability emerges, you’ll know about it right away, armed with the information you need to take immediate action and protect your assets.
Not all vulnerabilities are created equal. Our team focuses on identifying the weaknesses that attackers are actively using in the wild. For example, in just one recent week, HiveForce Labs uncovered two major cyberattacks and nine serious vulnerabilities that were being actively exploited. This focus on real-world exploitation is critical. It allows you to move beyond a simple CVSS score and understand which issues require your immediate attention. By pinpointing these high-risk vulnerabilities, including zero-days, we help you direct your resources to the fixes that will have the biggest impact on your security.
Understanding your enemy is half the battle. That’s why one of our expert teams is dedicated to studying cyber attackers and how they operate. We track threat actors, analyze their methods, and map out their attack patterns. This intelligence helps you understand the “who, what, and why” behind potential attacks on your organization. Are you being targeted by a specific APT group? Are attackers using a new phishing technique that could bypass your current defenses? Answering these questions allows you to build a more resilient security strategy that anticipates and counters the specific tactics your adversaries are likely to use.
Patch fatigue is a real problem for security teams. With thousands of vulnerabilities disclosed every month, it’s impossible to fix everything at once. HiveForce Labs provides quick, intelligent updates on the software fixes you need to apply to secure your systems. We help you with vulnerability and threat prioritization by connecting patches directly to active threats and exploits. This means you can confidently focus your remediation efforts on the updates that will close the most dangerous security gaps first, ensuring your team’s time and effort are spent where they matter most.
We believe that every organization deserves access to high-quality threat intelligence. That’s why HiveForce Labs offers free daily, weekly, and monthly threat advisories and digests. These aren’t just high-level summaries; they are practical reports that include clear, actionable steps your security team can take to mitigate risks. Each advisory breaks down complex threats into understandable components and provides concrete guidance for remediation. This resource ensures your team is always equipped with the knowledge to defend against the latest threats, without adding to your budget.
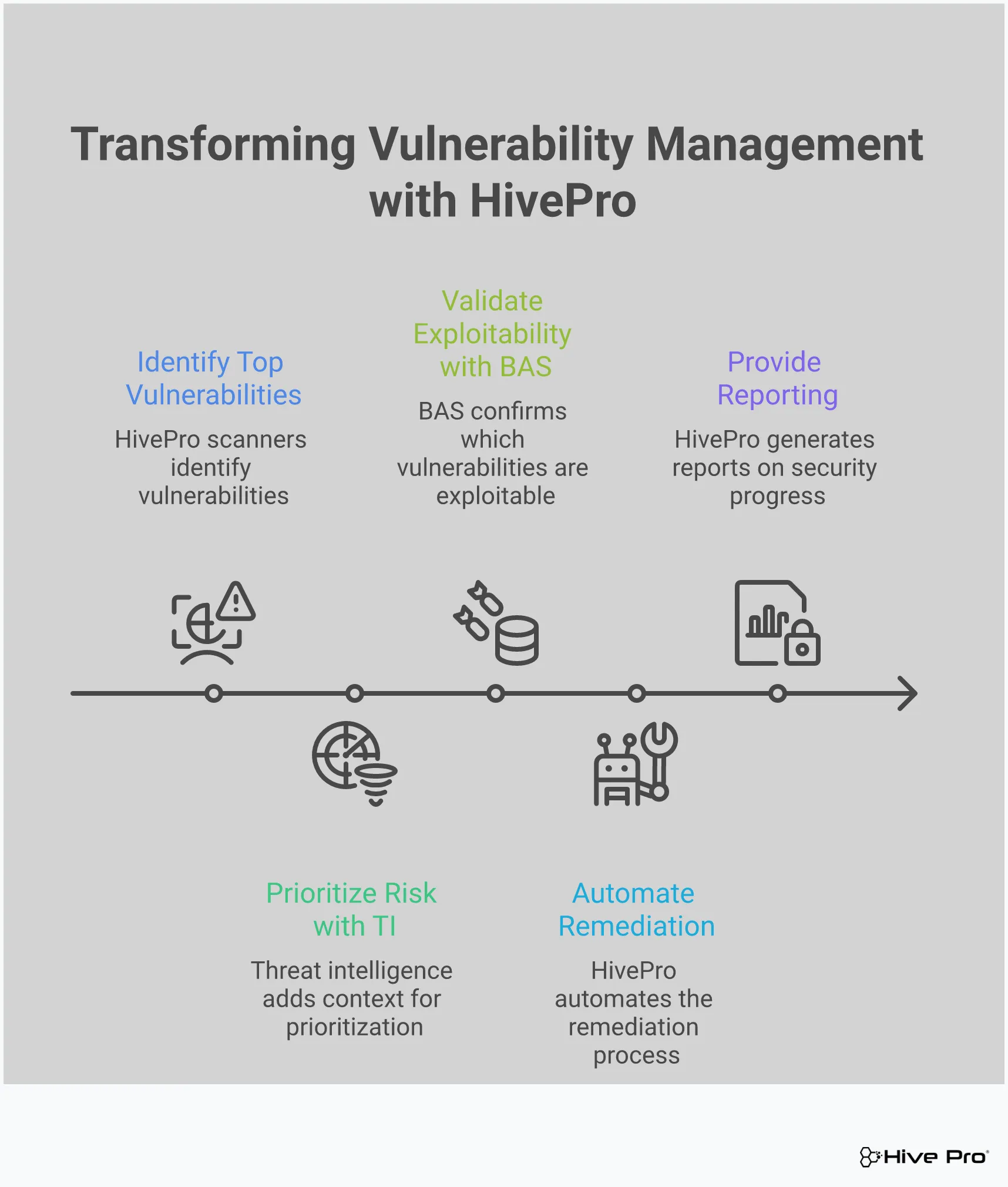
Effective vulnerability management is about more than just running scans and patching systems. It’s about making smart, informed decisions to stay ahead of attackers. For years, security teams have been stuck on a treadmill, trying to patch an endless flood of vulnerabilities without a clear sense of which ones truly matter. This approach is exhausting and, frankly, not very effective. The key to breaking this cycle is timely and relevant threat intelligence. By understanding which vulnerabilities are being actively targeted and how threat actors operate, you can move from a reactive state of constant firefighting to a proactive stance that anticipates and neutralizes threats before they cause damage.
This is where the intelligence from HiveForce Labs becomes your most valuable asset. Our research team lives and breathes the threat landscape, dedicating their time to tracking attacker campaigns, reverse-engineering malware, and identifying the specific exploits that pose a real danger. We translate this deep research into clear, actionable insights that are fed directly into your security workflow. This gives your team the context and clarity needed to stop guessing and start making confident, data-driven decisions to protect your organization.
For too long, security teams have been stuck in a reactive cycle, scrambling to patch vulnerabilities only after they become widely known or, worse, after an incident. This approach leaves you perpetually one step behind attackers. HiveForce Labs helps you break that cycle for good. With real-time alerts, expert analysis, and daily threat briefings, you gain the foresight to see what’s coming. Instead of just responding to yesterday’s news, you can anticipate attacker movements and strengthen your defenses accordingly. This proactive approach allows you to build a more resilient security posture, focusing your team’s valuable time and energy on preventing breaches rather than just cleaning them up after the fact.
Your team doesn’t have the time or resources to fix every single vulnerability, and they shouldn’t have to. The sheer volume of CVEs is overwhelming, and the truth is, most of them will never be exploited. HiveForce Labs cuts through the noise by identifying the vulnerabilities that attackers are actively using in the wild. This is the core of intelligent vulnerability and threat prioritization. By focusing on the threats that pose a clear and present danger to your organization, you can direct your resources where they will have the greatest impact. This allows you to significantly reduce your exposure with much less effort, freeing your team from the pressure of an impossible patching backlog.
Generic threat feeds can often feel like drinking from a firehose, full of information that isn’t relevant to your specific environment or industry. The intelligence from HiveForce Labs is different. We provide detailed, actionable threat advisories that give you the full picture. Each advisory includes specifics on affected products, the potential impact, key timelines, and clear recommendations for remediation. This context helps you understand the “why” behind a threat, not just the “what.” It ensures your security efforts are precisely aligned with the current threat landscape, making every action your team takes more meaningful and effective in protecting your critical assets.
Threat intelligence is most powerful when it’s easy to act on. That’s why all the insights from HiveForce Labs are seamlessly integrated into the Uni5 Xposure platform. This connection creates a unified workflow, linking threat discovery directly to your asset inventory and remediation processes. When a new, critical threat is identified, you can instantly see which of your assets are vulnerable and orchestrate a response without switching between different tools or spreadsheets. This closes the gap between knowing about a threat and actually fixing it, creating a smooth, end-to-end process that transforms intelligence into decisive, confident action.
Threat intelligence tells you what attackers are doing out in the wild. But how would your specific environment hold up against those same tactics? Answering that question is where Breach and Attack Simulation (BAS) comes in. Instead of waiting for a real incident to test your defenses, BAS lets you safely and continuously run simulated attacks against your own systems. It’s like having a dedicated red team on call 24/7, constantly checking your security controls for weaknesses.
This proactive approach moves you beyond vulnerability scanning and into true exposure management. You get to see exactly how your security stack performs against the latest threats, from initial access attempts to lateral movement. By integrating BAS into your strategy, you can find and fix security gaps before an attacker has a chance to exploit them. This process provides the hard data you need to confirm your security posture is as strong as you think it is and helps you make smarter decisions about where to invest your time and resources.
You have firewalls, endpoint detection, and other security tools in place, but are they configured correctly to stop the threats that matter right now? BAS platforms allow you to test how your security controls perform against potential exploitation. Using threat intelligence from sources like HiveForce Labs, these simulations mimic the exact techniques used by active threat actors. This allows you to see if your defenses can detect and block a simulated attack in a controlled environment. It’s a practical way to move from a theoretical security posture to one that is battle-tested against realistic attack scenarios, helping you identify vulnerabilities before they can be exploited.
Patching a vulnerability is only half the battle. You also need to confirm that the fix was successful and didn’t leave any residual risk. After your team applies a patch or reconfigures a system, you can use BAS to run the same attack simulation again. This process provides immediate feedback on whether your remediation efforts were effective. By simulating attacks, you can validate that your security measures are working as intended and that the vulnerability is truly closed. This step is a crucial part of the vulnerability management lifecycle, ensuring that your actions are having a real impact on reducing your organization’s threat exposure.
Even with a robust security program, gaps can exist. A misconfigured firewall rule, a disabled security agent, or a new, unmonitored asset can create an opening for an attacker. BAS helps you find these blind spots by testing your entire attack surface. The platform identifies where your organization is exposed to active threats and pinpoints weaknesses in your security posture. This insight is critical for understanding your true risk level. With a clear view of where your defenses are falling short, you can take targeted action to address those gaps and strengthen your overall security strategy.
The threat landscape is always changing, which means your security strategy can’t be static. What works today might not be effective tomorrow. Continuous adversarial exposure validation through BAS allows your organization to adapt to these evolving threats. By regularly testing your defenses against the latest attack methods, you can ensure your security controls remain effective over time. This ongoing validation provides detailed insights into potential threats and their impact, helping you allocate resources more effectively. It transforms your security program from a series of one-off projects into a dynamic, intelligence-driven operation that is always prepared for what’s next.
The threat landscape is always changing, which is why our team is constantly on the lookout for new attack methods and vulnerabilities. The intelligence we gather isn’t just theoretical; it’s based on real-world attacks happening right now. Here are a few examples of the kinds of threats our HiveForce Labs team has recently identified and analyzed.
Enterprise software is the backbone of most organizations, but it’s also a prime target for attackers. When a vulnerability is discovered in a widely used application, it creates a massive window of opportunity for threat actors. Our team continuously tracks these weaknesses, focusing on those that are being actively exploited in the wild. This allows us to cut through the noise of thousands of potential vulnerabilities and help you focus on the ones that pose an immediate risk. By understanding which flaws are being weaponized, you can move beyond a simple CVSS score and adopt a truly risk-based vulnerability and threat prioritization strategy.
Unlike opportunistic hackers, Advanced Persistent Threat (APT) groups are sophisticated, well-funded, and patient. These threat actors often have specific targets and can remain hidden within a network for long periods, quietly gathering intelligence before they strike. Keeping up with their evolving tactics is a full-time job. HiveForce Labs closely monitors the activity of multiple APT groups, analyzing their methods and motivations. This intelligence helps you understand not just what vulnerabilities are being exploited, but who is exploiting them and how. This context is critical for building a defense that can stand up to the most determined adversaries.
A zero-day exploit is one of a security team’s biggest challenges. It targets a vulnerability that the software vendor doesn’t even know about yet, meaning there’s no patch available when the attack begins. We’ve seen a significant rise in zero-days targeting essential business tools, including popular browsers, VPNs, and email servers like Microsoft Exchange. These attacks on cloud and remote access infrastructure can be devastating. Our team works to identify and issue threat advisories on these unknown weaknesses as quickly as possible, giving you the information you need to implement compensating controls and protect your systems until a patch is released.
Ransomware has evolved far beyond simply encrypting files. Modern ransomware groups are more strategic, often targeting backup systems first to eliminate an organization’s ability to recover without paying the ransom. For example, our team has tracked groups like Storm-0501, which specifically targets cloud environments. They work to gain administrative control, delete backups, and then encrypt data directly in the cloud, making recovery incredibly difficult. This tactic underscores the importance of not just having backups, but also ensuring they are secure and isolated. It also shows why continuous adversarial exposure validation is necessary to test if your defenses can stop these multi-stage attacks.
Having access to high-quality threat intelligence is one thing, but the real value comes from putting it into practice. Integrating this knowledge into your daily security operations is what turns information into action. It’s how you make smarter, faster decisions that actively reduce your threat exposure. Let’s break down how you can use this intelligence to shift your security posture from reactive to proactive.
This is about making threat intelligence a constant, living part of your security program. Instead of waiting for a weekly digest or a monthly report, your team gets a continuous feed of information. HiveForce Labs provides real-time alerts and daily briefings that drop right into your workflow, giving you a heads-up on emerging threats as they appear. This proactive approach means you can start strengthening defenses before an attack campaign gains momentum. By integrating these updates, your security team can shift from chasing alerts to anticipating the adversary’s next move, ensuring you’re always a step ahead.
The old model of trying to patch every single vulnerability is a losing battle. There are simply too many. A smarter approach is to focus on what attackers are actively exploiting right now. HiveForce Labs intelligence shows you which vulnerabilities are being used in the wild, so you can prioritize your patching efforts with surgical precision. This intelligence-driven strategy helps your team focus its limited time and resources on the fixes that will have the biggest impact on your security. You can finally move away from guesswork and use a vulnerability and threat prioritization process backed by real-world data.
Threat intelligence isn’t just for patching. The insights from HiveForce Labs can inform your entire security architecture. Are you seeing a rise in attacks targeting a specific protocol? You can adjust your firewall rules. Is a new phishing technique making the rounds? You can update your employee security training. This is about building a defense-in-depth strategy where every layer is strengthened by the latest threat data. We share valuable intelligence, including free Threat Advisories, to help you make these informed decisions. It’s how you build a resilient security posture that can adapt to the changing threat landscape.
How do you prove your security strategy is working? By measuring it. With a constant flow of threat intelligence, you can track meaningful metrics that show real progress. You can monitor how quickly your team remediates vulnerabilities that are actively being exploited or validate that your security controls are effective against the latest attack techniques. The Uni5 Xposure platform gives you a unified view to see these improvements over time. This allows you to demonstrate risk reduction to leadership with hard data, showing exactly how your intelligence-led approach is making the organization safer.
How is the intelligence from HiveForce Labs different from a standard threat feed? Think of it as the difference between a raw list of ingredients and a curated recipe. Many threat feeds give you a massive stream of data, like CVE numbers or suspicious IP addresses, but leave the hard work of figuring out what it means for you. HiveForce Labs provides the essential context. We tell you which vulnerabilities are actually being used in attacks, who is behind them, and what their motives are, so you can focus on the threats that pose a genuine risk to your organization.
My team is already overwhelmed with alerts. How does this intelligence actually help? This intelligence is designed to reduce noise, not add to it. The core problem for most security teams isn’t a lack of data; it’s a lack of clear priorities. By identifying the small fraction of vulnerabilities that are actively being exploited, HiveForce Labs allows your team to safely ignore the thousands that aren’t. This shrinks your massive to-do list down to a manageable, high-impact set of tasks, freeing your team to focus on preventing real-world breaches instead of chasing every single alert.
How does Breach and Attack Simulation (BAS) use the intelligence from HiveForce Labs? They work together to answer two critical questions: “What are attackers doing?” and “Could they do it to us?” HiveForce Labs provides the intelligence on the latest attack techniques being used in the wild. Our Breach and Attack Simulation module then uses that information to run safe, controlled simulations against your security controls. This lets you see if your defenses would actually stop a real-world attack, helping you find and fix gaps before an attacker can exploit them.
Do I have to be a customer to benefit from HiveForce Labs research? While our deepest, most integrated intelligence is built directly into the Uni5 Xposure platform for customers, we believe in supporting the entire security community. That’s why we offer free resources, including our daily, weekly, and monthly Threat Advisories. These reports provide actionable insights and clear remediation steps that any security team can use to better defend their organization against current threats.
How can this intelligence help me communicate risk to our leadership team? It helps you shift the conversation from technical details to business impact. Instead of reporting that you patched hundreds of vulnerabilities, you can show that you neutralized the top threats actively targeting your industry. By connecting your security efforts directly to real-world attack campaigns and validating your defenses, you can provide clear, data-driven evidence of risk reduction. This demonstrates a measurable return on your security investments and builds confidence that your strategy is working.