Comprehensive Threat Exposure Management Platform
 Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the Report
Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the ReportThink of your security posture like a fortress. Traditional vulnerability management gives you a long list of every potential weakness—a loose stone here, a weak gate there. A cyber threat exposure management (CTEM) program acts as your chief strategist, analyzing intelligence to show you exactly where enemy scouts have been seen and which gate they plan to attack. Instead of trying to fix every loose stone at once, you can focus your resources on reinforcing the gate that is under imminent threat. This context-driven approach is the key to moving from simply finding flaws to actively preventing breaches.
Let’s cut through the jargon. Cyber Threat Exposure Management, or CTEM, is a strategic approach for continuously finding, prioritizing, and fixing the security weaknesses that attackers are most likely to exploit. Think of it less as a single tool and more as a continuous program that brings together different parts of your security practice. It combines attack surface visibility, vulnerability management, and real-world threat intelligence to give you a clear, unified view of your actual risk. The goal is to move beyond simply identifying vulnerabilities and start managing your exposure—the real-world possibility of a breach.
Instead of just handing you a massive list of potential problems, a CTEM program helps you focus your team’s limited time and resources on the exposures that pose a genuine threat to your business. It’s about understanding your environment from an attacker’s perspective and proactively closing the security gaps that matter most. This ongoing cycle, managed through a comprehensive Threat Exposure Management Platform, helps you move from a state of constantly reacting to threats to confidently reducing your overall exposure. It provides the business context needed to communicate risk effectively to stakeholders and answers the critical question: “Of all the things we could fix, what should we fix right now?”
For years, security teams have been stuck in a reactive loop. A scanner runs, spits out a report with thousands of CVEs, and the team scrambles to patch as many as they can before the next report arrives. This approach is overwhelming and inefficient because it treats all vulnerabilities as equally urgent. CTEM flips this model on its head. It’s a fundamental shift from reactive fire-fighting to proactive risk reduction. By constantly monitoring your digital environment and enriching vulnerability data with insights from threat intelligence, you can get ahead of attackers. You start focusing on the specific weaknesses that threat actors are actively targeting, making your security posture much stronger against real-world risks.
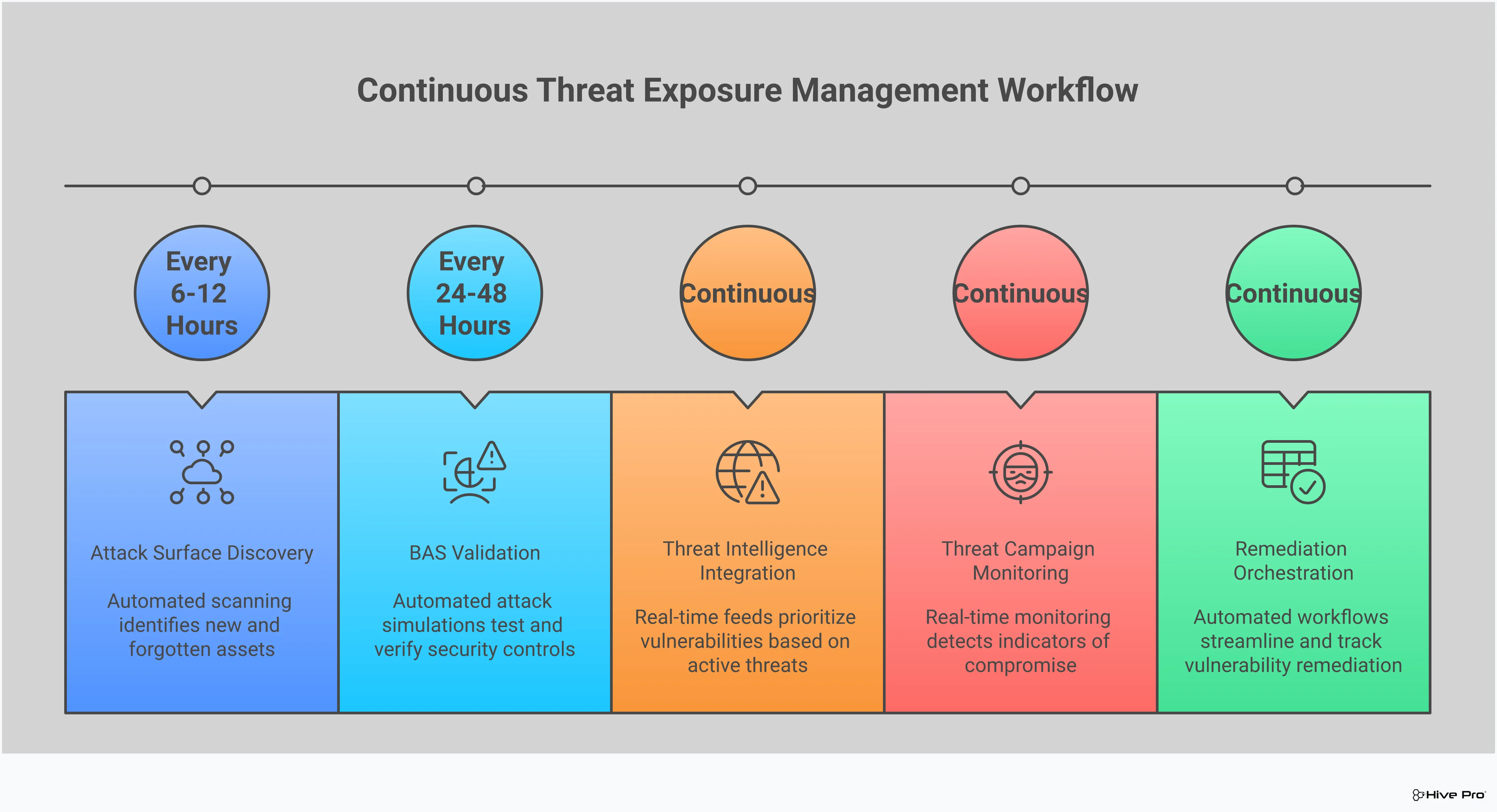
A successful CTEM program isn’t random; it’s a structured, repeatable cycle. This framework is typically broken down into five core stages that guide your team from understanding your environment to fixing the most critical issues. These stages are: Scoping, Discovery, Prioritization, Validation, and Mobilization. Think of it as a continuous loop. You first define what you need to protect (Scoping) and then find all your digital assets (Discovery). Then, you use threat intelligence to identify the most urgent risks (Prioritization). Next, you confirm if those risks are truly exploitable (Validation), and finally, you coordinate the remediation efforts (Mobilization). This methodical process ensures you’re always focused on the most impactful actions.
If you’ve ever felt like you’re drowning in a sea of vulnerability alerts, you’re not alone. For years, security teams have relied on traditional vulnerability management, a process that often feels like a never-ending game of whack-a-mole. It’s a reactive cycle: scan, find thousands of vulnerabilities, patch the critical ones based on a generic severity score, and repeat. This approach was functional for a simpler time, but it struggles to keep up with today’s sprawling attack surfaces and sophisticated threats.
Continuous Threat Exposure Management (CTEM) represents a fundamental shift in mindset—from reactive patching to proactive risk reduction. Instead of just identifying isolated weaknesses, CTEM provides a holistic view of your entire attack surface, connecting vulnerabilities to real-world threats and potential business impact. It answers the questions that matter most: Which of these thousands of vulnerabilities are attackers actually exploiting? And which ones could cause the most damage to our organization? This context-driven approach helps you focus your resources where they can make a real difference.
Traditional vulnerability management often creates more noise than signal. Scanners generate massive, unmanageable lists of vulnerabilities, leaving teams to sort through the chaos. The primary focus is on finding and fixing software flaws (CVEs) based on their CVSS score, a static metric that doesn’t account for your unique environment or the current threat landscape. This approach leads to “alert fatigue,” where security professionals are so overwhelmed by the volume of data that they can’t distinguish between a minor issue and a ticking time bomb. It’s a system that prioritizes fixing individual problems quickly, often without understanding the bigger picture of organizational risk.
CTEM transforms vulnerability management into actionable risk reduction by adding critical layers of context. Instead of just looking at a severity score, a CTEM program analyzes how a vulnerability could actually be exploited in your environment. It incorporates attack path analysis and validation to determine if a weakness is truly a threat. This allows for a more intelligent approach to vulnerability and threat prioritization, focusing on issues that pose the greatest risk to your critical assets and business operations. It’s the difference between being handed a phone book of problems and being given a short, targeted to-do list of what to fix first.
A core component of any effective CTEM program is the integration of timely, relevant threat intelligence. This means using data from security research teams like HiveForce Labs, government advisories, and even chatter on the dark web to understand emerging threats. By knowing which vulnerabilities are being actively targeted by threat actors, you can proactively strengthen your defenses before an attack occurs. This intelligence provides the “why” behind your remediation efforts, ensuring you’re not just patching for compliance but are actively making your systems more resilient against real-world risks. It’s about getting ahead of attackers by understanding their tactics and targets.
A Continuous Threat Exposure Management (CTEM) program isn’t a one-off project; it’s a cyclical, five-stage framework designed to give you a constant, clear view of your security posture. Think of it as a repeatable process that helps you move from a reactive state of patching fires to a proactive strategy of preventing them. Each stage builds on the last, creating a comprehensive loop that identifies, prioritizes, validates, and fixes your most critical security gaps. By adopting this structured approach, you can systematically reduce your threat exposure and make more informed, risk-based decisions for your organization.
Before you can protect your assets, you have to know what you’re trying to protect. The first stage is all about defining the boundaries of your digital footprint. This means identifying every area of your organization, both internal and external, that an attacker could potentially target. It’s more than just your on-premise servers; you need to consider your cloud infrastructure, web applications, APIs, and even subsidiary networks. This foundational step sets the parameters for your entire program, ensuring you have a complete picture of your potential total attack surface and don’t leave any critical areas unmonitored. It’s about asking, “Where could we possibly be attacked?” and drawing a map to guide the rest of your efforts.
Once you’ve defined your scope, the next step is to discover and catalog every single asset within those boundaries. This is where you create a comprehensive inventory of your digital environment. You’ll need to identify all your web apps, APIs, endpoints, IoT devices, cloud services, and code repositories. This isn’t a one-time task; continuous discovery is key because your environment is always changing as new devices are added and software is updated. An accurate and up-to-date asset inventory is the bedrock of effective exposure management. Without it, you’re operating with blind spots, and you can’t protect what you don’t know you have.
Not all vulnerabilities are created equal. With a complete list of assets and their associated weaknesses, the next stage is to prioritize them based on actual risk. This is where CTEM truly separates itself from traditional vulnerability management. Instead of relying solely on generic CVSS scores, you should use real-world threat intelligence to understand which vulnerabilities are being actively exploited by attackers in the wild. By focusing on the weaknesses that pose an imminent threat to your specific industry and assets, you can direct your team’s limited resources to the issues that matter most. This approach to vulnerability and threat prioritization ensures you’re fixing the most dangerous problems first.
After prioritizing your vulnerabilities, you need to validate whether they are truly exploitable in your environment. This stage involves testing your security controls and identified weaknesses using simulated attacks. Tools like Breach and Attack Simulation (BAS) can safely mimic the techniques used by real attackers to see if a vulnerability can actually be leveraged to breach your defenses. This adversarial exposure validation provides concrete proof of risk, helping you cut through the noise of theoretical vulnerabilities. It answers the critical question: “Could an attacker actually use this weakness against us?” This confirmation helps you justify remediation efforts and ensures your team isn’t wasting time on low-impact issues.
The final stage is all about taking action. Once you’ve identified, prioritized, and validated your exposures, it’s time to mobilize your teams to fix them. This involves translating your findings into clear, actionable remediation tasks and assigning them to the appropriate teams, whether that’s IT, DevOps, or security operations. Effective mobilization relies on clear communication, streamlined workflows, and the ability to track progress through dashboards and reports. The goal is to ensure that critical risks are addressed quickly and efficiently, closing the loop on the CTEM cycle. This stage turns insight into action, strengthening your security posture and demonstrating measurable risk reduction.
If your security team feels like they’re drowning in a sea of vulnerability alerts, you’re not alone. Traditional scanners can generate an overwhelming amount of data, making it nearly impossible to know where to start. The reality is you can’t fix everything, and you shouldn’t have to. This is where threat intelligence becomes your most valuable asset. It acts as a filter, cutting through the noise to show you which threats actually pose a clear and present danger to your organization.
Effective threat exposure management isn’t just about finding vulnerabilities; it’s about understanding their real-world context. Are threat actors actively exploiting a specific CVE? Is there a new ransomware campaign targeting your industry? Answering these questions is the key to moving from a reactive, checklist-based approach to a proactive, risk-based strategy. By integrating up-to-the-minute intelligence into your program, you can connect the dots between a vulnerability on your network and an active threat campaign in the wild. This allows you to focus your team’s limited time and resources on the exposures that matter most, giving you a clear path for vulnerability and threat prioritization.
Threat actors don’t just pick vulnerabilities at random; they run coordinated campaigns with specific goals, often targeting certain industries or technologies. To defend against them, you need to understand how they operate. High-quality threat intelligence pulls from diverse sources—government advisories, security research, social media, and even the dark web—to give you a clear picture of these active campaigns. This insight helps you understand the tactics, techniques, and procedures (TTPs) being used right now. Instead of just seeing an isolated CVE, you can see the threat actor behind it and anticipate their next move, allowing you to strengthen your defenses accordingly.
One of the biggest challenges in vulnerability management is that not all vulnerabilities are created equal. Many have a high CVSS score but no known public exploit, meaning the immediate risk is low. Threat intelligence provides the crucial context needed to separate the theoretical risks from the imminent threats. It tells you which vulnerabilities are not only exploitable but are actively being used in attacks. This is the single most important factor for prioritization. When you know a vulnerability is part of an attacker’s toolkit, you know it needs to be patched immediately. This is the kind of actionable insight that teams like HiveForce Labs provide to help you stay ahead.
Ultimately, the goal of using threat intelligence is to work smarter, not harder. Your security team has a finite amount of time, budget, and personnel. Wasting those resources on low-risk vulnerabilities leaves you exposed to the ones that can cause real damage. By combining threat intelligence with your attack surface data, you can create a truly risk-based remediation plan. This means focusing on the handful of exposures that pose a genuine threat to your business operations, rather than getting lost in an endless list of CVEs. This focused approach is the foundation of an effective threat exposure management platform, ensuring your efforts have the greatest possible impact on reducing your organization’s risk.
After you’ve prioritized your vulnerabilities using threat intelligence, you need to answer a critical question: Can an attacker actually exploit these weaknesses in your environment? This is where Breach and Attack Simulation (BAS) comes in. Instead of relying on theoretical risk scores, BAS platforms provide a way to safely and continuously test your defenses against the same tactics and techniques real attackers use.
Think of it as a sparring partner for your security program. By running automated, controlled attack simulations, you can see exactly how your security controls would perform during an actual incident. This process of adversarial exposure validation is a core part of a modern CTEM program because it moves you from guesswork to certainty. You get concrete evidence of which attack paths are open, which security tools are misconfigured, and which high-priority vulnerabilities represent a clear and present danger. This allows your team to stop chasing thousands of potential threats and focus on closing the specific gaps that attackers could use to breach your network.
Your security stack is made up of many layers—firewalls, endpoint detection, email gateways, and more. But are they all configured correctly and working together? Breach and Attack Simulation lets you find out by continuously testing your security controls against real-world attack scenarios. These simulations mimic attacker behavior to see if your defenses can detect and block them as expected. This helps you identify not just vulnerable assets, but also gaps in your security posture, like a misconfigured firewall rule or an EDR solution that fails to flag a malicious process. It’s a practical way to ensure the tools you’ve invested in are actually delivering the protection you need.
Prioritizing vulnerabilities with threat intelligence is a huge step forward, but BAS takes it even further. By running simulations, you can validate your prioritization efforts by seeing which vulnerabilities are the easiest to exploit in your specific environment. A vulnerability might have a high CVSS score, but a BAS test can show that it’s not exploitable because of other compensating controls you have in place. This ensures your team spends its time and resources fixing the issues that pose the most immediate risk. It’s the ultimate reality check, helping you focus on the vulnerabilities that truly matter.
Many vulnerability scanners flag issues that are only theoretically dangerous. Breach and Attack Simulation provides a practical way to confirm if a vulnerability is truly exploitable in your environment. By executing controlled attacks, security teams can see firsthand if a weakness can be leveraged by an attacker. This provides a much clearer picture of your actual risk. For example, a Common Vulnerabilities and Exposures (CVE) entry might exist for a piece of software you use, but the simulation might fail because your unique configuration prevents the attack from succeeding. This confirmation helps you avoid wasting time on low-risk findings and direct your remediation efforts toward proven exposures.
Adopting a CTEM program is about more than just new technology; it’s a strategic shift that helps you make data-driven decisions to reduce risk. Instead of getting caught in an endless cycle of scanning and patching, a CTEM framework helps your team work more efficiently and prove its value to the organization. This proactive stance delivers clear advantages that strengthen your entire security posture.
Security teams are often overwhelmed with vulnerability data, making it hard to know what to fix first. A CTEM program cuts through that noise. By combining asset context with real-world threat intelligence, you can instantly see which vulnerabilities are not only exploitable but are actively being targeted. This focus allows your team to stop debating priorities and get straight to work on the threats that matter. This direct approach is proven to significantly reduce the Mean Time to Remediation (MTTR), a key metric for measuring the effectiveness of your vulnerability and threat prioritization efforts.
No security team has unlimited time or budget. The goal is to make sure every action delivers the biggest possible impact. CTEM is built around this principle. By aligning security tasks with business priorities and validating which risks are truly exploitable, you can channel your resources with confidence. Instead of trying to patch everything, your team can concentrate on the exposures that pose a genuine threat to your most critical assets. This ensures your experts are spending their valuable time on high-impact work, not chasing down vulnerabilities that attackers are unlikely to ever use.
A long list of CVEs doesn’t tell you much about your actual risk. A ‘critical’ vulnerability on a test server is far less concerning than a ‘high’ one on your main payment application. CTEM provides the business context needed to see the difference. It gives you a unified view of your digital footprint and maps exposures back to their potential business impact. This full-context approach transforms security conversations from technical details to strategic risk management. Gaining this level of insight starts with a complete picture of your total attack surface.
Adopting a Continuous Threat Exposure Management (CTEM) program is a significant step forward for any security organization, but it’s not as simple as flipping a switch. This is a strategic shift that changes how your team operates, thinks, and measures success. While the move from a reactive to a proactive security posture is invaluable, it comes with a few common hurdles. Understanding these challenges ahead of time is the best way to prepare for them and ensure your implementation is successful.
The main obstacles aren’t technical limitations but rather operational and cultural shifts. You’ll need to think about how your existing tools work together, where your team’s strengths lie, and how to foster a forward-thinking security culture. The goal isn’t just to adopt a new process but to build a sustainable program that continuously reduces your organization’s risk. By anticipating these challenges, you can create a clear roadmap for integrating CTEM into your security operations, making the transition smoother and more effective from day one.
Most security teams are already dealing with “tool sprawl”—a collection of disconnected solutions for asset discovery, vulnerability scanning, and threat detection. A CTEM program doesn’t just add another tool to the pile; it aims to unify the data from these systems to create a single, coherent view of your attack surface. The challenge lies in integrating these disparate data sources effectively. Pulling everything together to identify, assess, and prioritize exposures requires a platform built for aggregation and analysis. Without a central hub, your team will spend more time trying to connect the dots between different dashboards than actually managing threats.
A successful CTEM program relies on more than just technology; it requires people with the right skills. Expertise in areas like threat modeling, risk analysis, and interpreting threat intelligence is essential for turning raw data into actionable security plans. However, many security teams are already stretched thin, and finding professionals with this specific skill set can be difficult. This is where a strong CTEM platform can help augment your team’s capabilities. By leveraging curated intelligence from research teams like HiveForce Labs, you can offload some of the analytical heavy lifting, allowing your team to focus on validation and remediation instead of getting lost in research.
Perhaps the most significant challenge is cultural. Traditional vulnerability management often operates in a reactive cycle: scan, find thousands of vulnerabilities, and then struggle to patch them all. CTEM demands a fundamental shift from this “patch everything” mentality to a proactive, risk-based approach. It’s about asking different questions: Which of these vulnerabilities are actually exploitable in our environment? What are active attackers targeting right now? How does this exposure impact our most critical business operations? This change requires buy-in from leadership and a new way of communicating risk, moving the conversation from technical details to business impact.
Once you launch a Continuous Threat Exposure Management (CTEM) program, how do you know if it’s actually working? Shifting from a traditional vulnerability management mindset means your definition of success has to change, too. It’s no longer about simply counting how many CVEs you’ve patched. Instead, success is measured by a tangible reduction in business risk and a stronger, more resilient security posture.
Proving the value of your CTEM program requires tracking the right metrics. This not only helps justify security investments but also guides your team’s efforts toward what truly matters. Measuring your effectiveness allows you to show progress, identify areas for improvement, and communicate your security wins in a language the entire business can understand. To do this effectively, you need to focus on a few core areas: establishing clear goals, tracking your overall exposure footprint, and measuring the speed and efficiency of your response.
You can’t improve what you don’t measure. The first step in gauging your CTEM program’s success is to establish clear Key Performance Indicators (KPIs) that align with your security and business objectives. Think of KPIs as the specific, measurable signposts that tell you you’re on the right track. According to the Cloud Security Alliance, measuring the effectiveness of a CTEM strategy is all about setting up these metrics to track progress over time. Instead of just tracking the total number of vulnerabilities, focus on KPIs like the reduction in critical exposures on business-critical assets, the percentage of your attack surface actively monitored, or the time it takes to validate a newly discovered threat.
A successful CTEM program actively shrinks your attack surface. One of the best ways to measure this is by tracking Vulnerability Density, which looks at the number of vulnerabilities relative to the number of assets you have. If this number is consistently going down, it’s a strong sign that your security hygiene is improving across the board. The goal is to move beyond just finding flaws and focus on demonstrating a real decrease in risk. Tracking your Vulnerability Detection Rate is also useful, but the ultimate goal is to see the overall number of exploitable exposures on your critical systems diminish over time.
Speed and efficiency are at the heart of a proactive security strategy. Two of the most critical metrics for any CTEM program are Mean Time to Detect (MTTD) and Mean Time to Remediate (MTTR). MTTD measures how quickly your team can identify a new exposure, while MTTR tracks how long it takes to fix it. These metrics are essential for assessing the responsiveness of your security posture. A core goal of CTEM is to shrink the window of opportunity for attackers. By consistently working to lower your MTTD and MTTR—especially for the high-priority threats identified through threat intelligence and validation—you can demonstrate a direct improvement in your ability to neutralize threats before they can be exploited.
Deciding to adopt a Continuous Threat Exposure Management (CTEM) program isn’t about your company’s size or industry. It’s about your security mindset. If your team is tired of chasing endless vulnerability alerts and wants to shift from a reactive posture to a proactive one, CTEM is likely the right move. It’s a pragmatic approach for teams that need to manage risk effectively without trying to patch everything at once. Think of it as a strategic framework that helps you walk the tightrope between securing everything and focusing only on what’s actively on fire.
A CTEM program helps you focus on the threats that genuinely matter to your business. Instead of getting lost in a sea of low-risk vulnerabilities, you can concentrate your efforts on the exposures that attackers are actively targeting. This strategic shift allows security leaders to manage threats more efficiently and align their work directly with business objectives. It’s about answering the question, “What should we fix today?” with confidence. If you’re ready to move beyond guesswork and make data-driven decisions about your security, it’s time to consider a CTEM program.
If your security team feels like they’re constantly playing catch-up, a CTEM program can provide much-needed structure and focus. It’s a great fit for enterprises struggling to see the big picture amidst a flood of vulnerability data from various scanners. CTEM helps you cut through the noise by providing a unified view of your cyber risks. Instead of just handing you a list of problems, a CTEM framework helps you understand which vulnerabilities are truly exploitable and pose a real threat to your critical assets. This approach allows you to align security efforts with specific business outcomes, making it easier to communicate risk to leadership. By implementing a system for vulnerability and threat prioritization, your team can stop reacting to every alert and start proactively reducing your most significant exposures.
Every industry faces unique security challenges. A financial institution’s primary concern might be protecting sensitive customer data, while a manufacturing company might worry about operational technology on the factory floor. CTEM is flexible enough to address these specific needs. For example, a retail company can use CTEM to secure its e-commerce platforms and complex supply chains, systematically evaluating the security posture of its third-party vendors and partners. Because CTEM focuses on your entire attack surface, it helps you identify and address vulnerabilities wherever they exist—from on-premise servers to cloud environments and partner networks. This comprehensive approach to total attack surface management ensures that you can build resilience and protect what matters most, no matter your industry’s specific risk landscape.
A CTEM program is a journey, not a destination. It’s a continuous cycle of identifying, assessing, prioritizing, and remediating exposures across your organization. To figure out if you’re ready, consider your current processes. Are you able to see your entire attack surface? Do you have a clear method for prioritizing vulnerabilities based on real-world threat intelligence? If your security program is still maturing, a CTEM platform can provide the foundation you need to build a more proactive defense. For more advanced teams, it can streamline existing workflows and provide deeper, more actionable insights into your exposure landscape. The goal is to move toward a state of continuous improvement, where your security posture gets stronger every day. A platform like Uni5 Xposure can help you manage this entire lifecycle, enabling your team to respond effectively to evolving threats.
Building a Continuous Threat Exposure Management (CTEM) program is a strategic move that shifts your security posture from reactive to proactive. It’s more than just implementing a new tool; it’s about adopting a cyclical process that aligns your security efforts with real-world business risks. An effective program gives you a clear, continuous view of your attack surface, helps you prioritize the threats that actually matter, and validates that your defenses are working as expected.
The goal is to create a sustainable framework that matures with your organization. This involves three core pillars: selecting the right technology to serve as your foundation, integrating it deeply into your existing security ecosystem, and committing to a cycle of continuous improvement. By focusing on these areas, you can move beyond chasing an endless list of vulnerabilities and start making strategic decisions that genuinely reduce your organization’s exposure to threats. Let’s walk through how to put these pillars into practice.
The foundation of your program is a platform that can manage the entire exposure lifecycle. This means it needs to do more than just scan for vulnerabilities. Look for a comprehensive CTEM platform that can handle all five stages: scoping, discovery, prioritization, validation, and mobilization. The key is its ability to connect technical vulnerabilities to business context. Your platform should help you answer questions like, “Which of these exposures could an attacker actually exploit?” and “What business-critical assets are at risk?” This alignment ensures your team focuses its limited time and resources on fixing the problems that pose the greatest threat to your organization’s goals.
A CTEM program shouldn’t operate in a silo. To be truly effective, it must integrate with the security tools you already use. Think of it as the connective tissue that brings your entire security stack together, from asset inventories and vulnerability scanners to SIEMs and ticketing systems. This integration creates a single source of truth for your security posture, breaking down data silos and enabling a more coordinated response. When your CTEM platform can pull data from and push actions to other tools, you get a real-time, holistic view of your exposure and can streamline your remediation workflows without adding manual work for your team.
The “C” in CTEM stands for “continuous,” and that’s the most critical part. Your program isn’t a one-and-done project; it’s an ongoing cycle of refinement. This means establishing a process for regularly evaluating your security posture and adapting to new threats. Use the insights from your validation stage—like results from Breach and Attack Simulation—to ask tough questions. Are your security controls effective? Is your prioritization logic sound? Are your remediation efforts actually reducing risk? This feedback loop is essential for maturing your security program and ensuring it remains effective as your attack surface evolves and new threats emerge.
My team is already doing vulnerability management. How is CTEM really that different? That’s a great question because it gets to the heart of the matter. Think of it this way: traditional vulnerability management often gives you a massive to-do list based on what could be a problem. CTEM, on the other hand, gives you a much shorter, targeted list based on what is a problem right now. It adds critical context by asking if a vulnerability is on an important asset, if attackers are actively exploiting it, and if your current security controls would even stop an attack. It’s the difference between patching for compliance and remediating based on genuine business risk.
We get tons of threat intelligence feeds. How does a CTEM program make that data actually useful? Many teams feel like they’re drinking from a firehose when it comes to threat intelligence. A CTEM program acts as a filter. Instead of just collecting data, it integrates that intelligence directly into your prioritization process. It automatically correlates information about active threat campaigns and exploited vulnerabilities with the specific assets in your environment. This turns a generic stream of threat data into a specific, actionable alert, like “This vulnerability on your customer database is being actively targeted by a ransomware group.” It makes the intelligence relevant to you.
We already prioritize vulnerabilities based on severity scores. Why do we also need to validate them with attack simulations? Relying only on severity scores is like reading a weather report that says there’s a 90% chance of a hurricane without checking to see if you have storm shutters. A high CVSS score tells you a vulnerability is theoretically dangerous, but it doesn’t tell you if it’s exploitable in your unique environment. Breach and Attack Simulation (BAS) is your reality check. It safely tests if an attacker could actually use that vulnerability to get through your defenses, confirming whether the threat is real or if other security controls you have in place mitigate the risk.
What’s the first practical step my team can take to move toward a CTEM approach? The best place to start is by getting a complete and accurate picture of your attack surface. You can’t protect what you don’t know you have. Begin by focusing on the “Discovery” stage to create a comprehensive inventory of all your assets, from servers and cloud instances to web applications and APIs. Once you have that clear view, you can begin layering on threat intelligence to see which of those assets have weaknesses that are being actively targeted. This foundational step provides the context you need for all the other stages.
How do I explain the value of CTEM to my leadership team who might just see it as another expense? Focus on communicating in terms of business risk, not technical details. Instead of talking about patching CVEs, explain how a CTEM program helps the company avoid specific business disruptions, like a data breach or operational downtime. You can frame it as a way to make the security budget work smarter by focusing resources on the handful of threats that pose a genuine danger to revenue or reputation. Using data from the program, you can show a measurable reduction in your organization’s most critical exposures over time, which is a language every executive understands.