Comprehensive Threat Exposure Management Platform
 Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the Report
Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the ReportYou’ve invested in a full stack of security tools, but how can you be sure they’re configured correctly and will actually work during an attack? Waiting for a real incident to test your defenses is a risk no one wants to take. This is why validating your security posture is so critical. It’s about moving from assuming you’re protected to proving it. By combining proactive testing with a solid foundation of continuous monitoring and threat detection, you can safely simulate real-world attacks to see how your defenses hold up. This approach turns your monitoring from a passive observation tool into an active, self-improving defense system.
Think of continuous monitoring as your organization’s digital nervous system. Instead of relying on periodic check-ups or annual scans that only give you a snapshot in time, continuous monitoring is an always-on, automated process. It constantly observes your network, systems, and applications to give you a live feed of your security posture. This approach moves you away from a reactive “point-in-time” security model to a proactive, ongoing strategy that keeps pace with your dynamic environment.
The goal is to maintain constant awareness of your entire IT environment. This means you can identify vulnerabilities, misconfigurations, and potential threats the moment they appear, not weeks or months later during a scheduled audit. By collecting and analyzing data around the clock, you get a clear, up-to-the-minute picture of your risks. This is a fundamental shift that allows security teams to stop playing catch-up and start getting ahead of attackers. It’s a core component of a modern Continuous Threat Exposure Management (CTEM) program, providing the real-time data needed to make smart, fast decisions and truly understand your security landscape as it evolves.
Real-time assessment is about closing the gap between when a vulnerability appears and when you find out about it. Traditional security methods often involve scheduled scans—daily, weekly, or even monthly. The problem is that a lot can happen in the time between those scans. A new vulnerability could be discovered, a developer could accidentally introduce a misconfiguration, or an attacker could find a new way in. Continuous monitoring replaces this outdated model with an ongoing, automated process that assesses your security posture as it changes. It gives you immediate insight into your full attack surface, helping you spot weaknesses as they emerge. This means you’re not working with old information; you have a current, accurate view of your security landscape at all times.
The sheer volume of activity across a modern network makes manual threat hunting nearly impossible. This is where automation becomes your best ally. Continuous monitoring uses automated tools to sift through endless streams of data, rapidly identifying suspicious activities or anomalies that could signal an attack. By automating this initial detection phase, you can significantly reduce the “dwell time”—the critical period between when a compromise occurs and when it’s discovered. This speed allows your security team to respond to threats as they happen, minimizing potential damage. Instead of drowning in alerts, your team can focus on investigating and mitigating the most credible threats. This automated approach is essential for effectively prioritizing vulnerabilities and ensuring your resources are directed where they’ll have the most impact.
Simply put, you can’t protect what you can’t see. In a security landscape where new threats emerge daily, periodic or manual checks just don’t cut it anymore. Continuous monitoring shifts your security program from a state of reaction to one of readiness. It’s about maintaining constant visibility across your entire digital environment—from your cloud instances to your on-prem servers—so you can spot and handle threats before they escalate into full-blown incidents. This constant vigilance is the foundation of a strong, proactive security posture and is essential for effective threat detection. By always keeping an eye on your systems, you’re better equipped to understand your baseline for normal activity, making it much easier to identify deviations that could signal an attack.
Waiting for a security alert to tell you something is wrong means you’re already behind. A proactive approach is about getting ahead of the threat. Continuous monitoring enables the rapid identification of suspicious activities or anomalies as they occur. This proactive approach significantly reduces attacker dwell time by swiftly identifying and mitigating security incidents, thereby minimizing the potential impact on your organization. Instead of just responding to fires, your team can identify the conditions that might lead to one. This is the core principle of a modern Threat Exposure Management program—moving from a defensive crouch to an assertive, forward-leaning security posture that anticipates and neutralizes threats.
Every second an attacker spends in your network undetected increases your risk. Mean Time to Detection (MTTD) is a critical metric that measures how long it takes your team to discover a potential security threat. The goal is always to get this number as low as possible. Continuous monitoring is the ongoing, real-time process of collecting, analyzing, and acting on data across all IT environments to detect and address threats and vulnerabilities before they impact users. This capability is crucial for reducing your MTTD, allowing your organization to respond to threats more swiftly and effectively. By shrinking the window of opportunity for attackers, you dramatically limit their ability to move laterally, exfiltrate data, or cause significant damage.
Your security tools generate a massive amount of data and alerts. Without a way to filter the signal from the noise, your team can quickly become overwhelmed, leading to alert fatigue where critical warnings are missed. A smart continuous monitoring strategy helps solve this. It not only helps in identifying threats but also plays a critical role in managing the overwhelming amount of data generated. Integrating threat intelligence into your monitoring strategy helps prioritize vulnerabilities that are most relevant to your organization, effectively cutting through the noise. This allows your team to focus their limited time and resources on the alerts that pose a genuine risk, turning a flood of information into a stream of actionable insights.
A strong continuous monitoring strategy isn’t just about installing a tool and hoping for the best. It’s a dynamic process built on a few core pillars that work together. Think of it as building a foundation for your entire security posture. When you get these components right, you move from simply collecting data to generating real, actionable security insights. This approach helps you see what’s happening across your environment, understand the context behind events, and respond effectively before a minor issue becomes a major breach.
You can’t protect what you don’t know you have. The first step is to create and maintain a complete inventory of every asset across your digital footprint—servers, endpoints, cloud instances, applications, and IoT devices. By continuously observing activity on your network, you can detect suspicious behavior and act on threats before they escalate. A comprehensive Total Attack Surface Management approach is crucial. Once you have a full inventory, you can classify assets based on their criticality to the business. This helps you prioritize your monitoring efforts, ensuring your most valuable data and systems get the attention they deserve.
Continuous monitoring and vulnerability management go hand in hand. While monitoring spots active threats, regular vulnerability assessments find the weaknesses those threats could exploit. Integrating these two processes allows you to connect the dots between a potential attack and a known vulnerability on a critical asset. This significantly reduces the time it takes to identify and mitigate security incidents, minimizing their potential impact. By combining real-time monitoring with a solid vulnerability and threat prioritization process, you can focus your remediation efforts on the flaws that pose the most immediate risk to your organization.
Threats aren’t always external; sometimes, the biggest risks come from unusual activity inside your network. That’s why analyzing user and system behavior is so important. This involves establishing a baseline for what “normal” activity looks like for every user and system. Continuous analysis helps you examine network data and security events to uncover patterns and potential vulnerabilities. When behavior deviates from this baseline—like a user accessing sensitive files at 3 a.m. or a server making unusual outbound connections—your monitoring system can flag it as a potential threat. This proactive approach helps you spot insider threats and compromised accounts early.
Your continuous monitoring strategy shouldn’t operate in a silo. To be truly effective, it needs to integrate with your existing security stack—your SIEM, firewalls, endpoint detection, and more. A unified platform like Uni5 Xposure can pull in data from these disparate sources to give you a single, correlated view of your security posture. Good log management is essential for collecting data about user activities from various systems. By connecting your tools, you eliminate blind spots, reduce manual correlation efforts, and ensure your security team has the complete context needed to make fast, informed decisions.
Putting a continuous monitoring strategy in place does more than just collect data—it fundamentally changes how you detect and respond to threats. Instead of waiting for a major incident to reveal a weakness, you can spot the subtle signs of trouble as they appear. This proactive approach allows you to move faster, make smarter decisions, and build a more resilient security posture. By turning raw data into actionable insights, you can sharpen your detection capabilities and stay ahead of attackers.
Effective threat detection starts with seeing everything clearly. Continuous monitoring gives you a live, unfiltered view of your entire environment, from on-premise servers to cloud assets and endpoints. This allows you to spot suspicious activities and anomalies the moment they occur, rather than days or weeks later. By catching potential threats early, you can dramatically reduce attacker dwell time and minimize the potential impact of a breach. This constant vigilance is key to maintaining a complete picture of your total attack surface and ensuring no threat goes unnoticed.
Not all assets carry the same level of risk, so your monitoring efforts shouldn’t be one-size-fits-all. A strong continuous monitoring strategy is adaptable, allowing you to tailor your focus based on your organization’s unique risk profile. You can apply more stringent monitoring to critical systems that house sensitive data while using broader surveillance for less critical assets. This risk-based approach ensures your team’s time and resources are spent on the most significant threats, helping you protect what matters most without getting bogged down by low-priority alerts.
Monitoring in a vacuum is like trying to find your way without a map. To make your detection efforts truly effective, you need to integrate them with live threat intelligence. By feeding real-world data from sources like HiveForce Labs into your monitoring tools, you add crucial context to the alerts you receive. This helps you understand which vulnerabilities are actively being exploited in the wild and which threats are targeting your industry. This intelligence-driven approach allows you to prioritize alerts that pose a genuine risk and focus your response on the dangers that are most relevant to you.
Identifying a threat is only the first step; the real goal is to neutralize it quickly. Continuous monitoring platforms can trigger automated response and remediation workflows to handle threats without manual intervention. For example, an alert could automatically generate a ticket, isolate a compromised endpoint, or block a malicious IP address. This automation is essential for responding at machine speed, reducing the burden on your security team, and ensuring that security issues, operational problems, and compliance violations are addressed consistently and reliably. It’s how you turn detection into decisive action with the Uni5 Xposure platform.
Setting up a continuous monitoring program isn’t just a matter of flipping a switch. It’s a strategic shift that comes with its own set of hurdles. While the benefits are clear, anticipating the challenges helps you create a smoother, more effective rollout. Most organizations run into similar issues related to people, technology, and process. Getting ahead of these common roadblocks means you can spend less time troubleshooting your setup and more time actually detecting threats.
The main obstacles you’ll likely encounter involve staffing your team, connecting your existing systems, and figuring out where automation fits best. Let’s break down each of these so you can build a plan that addresses them from the start.
Finding and keeping talented cybersecurity professionals is a well-known challenge across the industry. The demand for skilled analysts far outstrips the supply, which can lead to high turnover and a constant need for training. When you’re trying to implement a 24/7 monitoring strategy, a small or overworked team can quickly become a major bottleneck. This can lead to burnout and, even worse, missed alerts.
To counter this, look for solutions that act as a force multiplier for your team. A platform that automates data collection and provides clear, prioritized guidance reduces the manual workload on your analysts. This allows them to focus their expertise on investigating and responding to the most critical threats, rather than getting lost in the noise. It helps you bridge the skills gap without needing to double your headcount.
Most established organizations don’t have the luxury of building their tech stack from scratch. Your IT environment is likely a complex mix of modern cloud services, on-premise servers, and legacy applications that are critical to business operations. Getting all of these disparate systems to talk to each other and feed data into a central monitoring tool can be a significant technical challenge. Without a unified view, you’re left with blind spots that attackers can easily exploit.
The key is to adopt a platform designed for this kind of complexity. A modern Threat Exposure Management platform should offer broad integration capabilities, allowing you to pull data from across your entire hybrid environment. This consolidates your security data into a single source of truth, giving you a complete picture of your attack surface without requiring a massive overhaul of your existing infrastructure.
Automation is essential for modern threat detection. With the sheer volume of data and alerts, it’s impossible for any human team to keep up manually. AI and machine learning can process information at scale, spotting anomalies and identifying potential threats in real time. However, relying too heavily on automation without human oversight can lead to a flood of false positives or, conversely, a false sense of security.
The most effective approach combines the speed of automation with the nuanced context of human expertise. Use automated tools to handle the heavy lifting of data analysis and initial alert triage. This frees up your security analysts to apply their critical thinking skills to complex investigations, validate findings, and make strategic decisions about remediation. This partnership ensures you get the efficiency of machines without losing the invaluable judgment of your team.
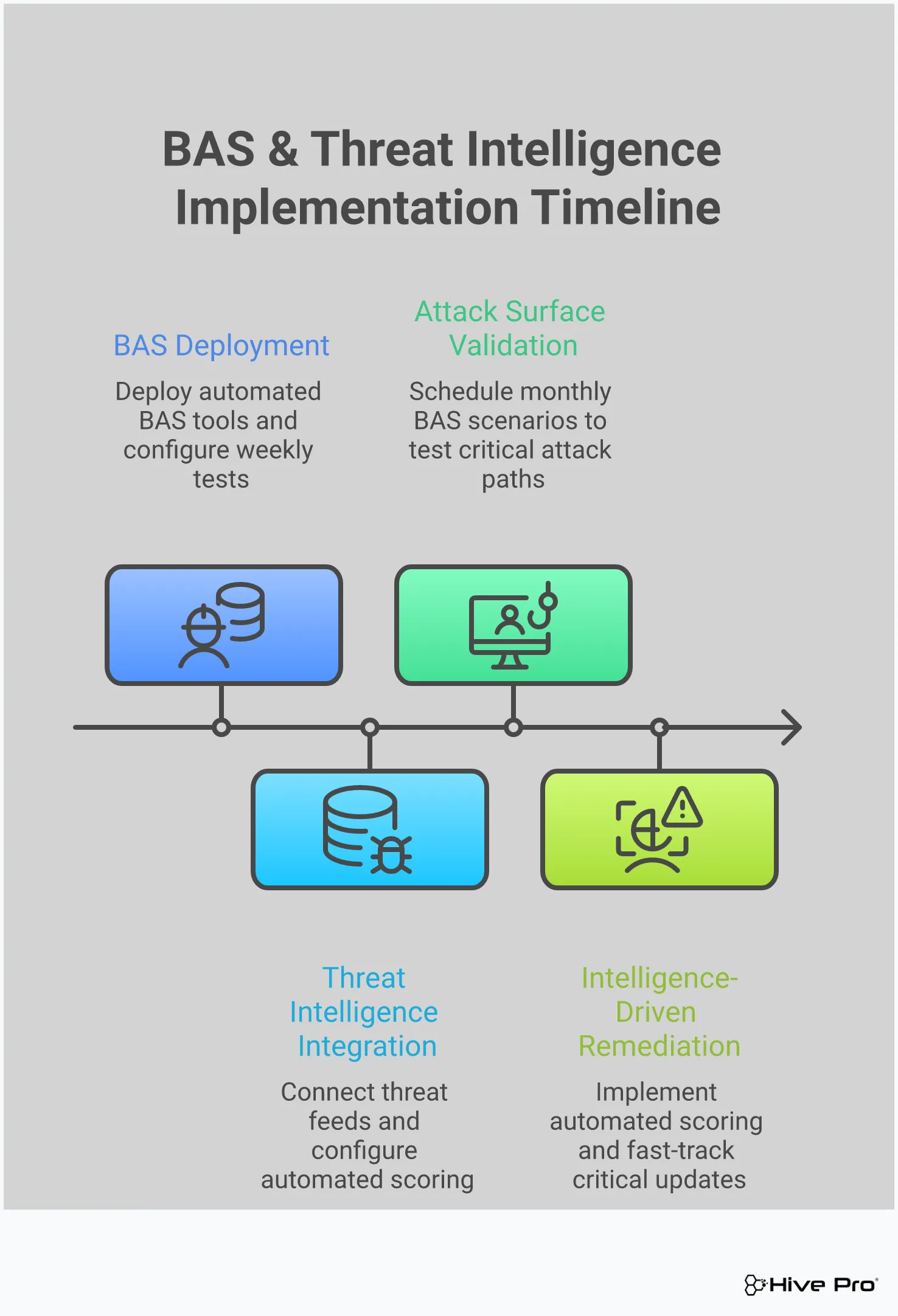
Continuous monitoring is fantastic for seeing what’s happening across your network, but how do you know if it’s actually working? Waiting for a real attack to find out is a high-stakes gamble. This is where Breach and Attack Simulation (BAS) comes in. Think of it as a fire drill for your entire security program. Instead of passively collecting data and waiting for an alert, BAS lets you safely and continuously simulate real-world attack techniques to see how your defenses hold up.
By integrating BAS into your monitoring strategy, you move from a theoretical understanding of your security posture to a practical, evidence-based one. It’s no longer about assuming your SIEM is configured correctly or that your EDR will catch a specific threat. It’s about proving it. This proactive testing validates your tools, fine-tunes your processes, and trains your team. It helps you answer the critical question, “Are we secure?” with data, not just hope. This approach transforms your monitoring from a simple observation tool into an active, self-improving defense system. Hive Pro’s approach to adversarial exposure validation helps you run these simulations to see exactly where you stand against current threats.
You’ve invested heavily in security tools designed to detect suspicious activity, but are they firing when they should? BAS allows you to validate your detection capabilities by running controlled simulations of known attack paths. These simulations mimic the tactics, techniques, and procedures (TTPs) used by actual adversaries, from initial access to data exfiltration. By running these tests, you can confirm that your security tools are not only deployed but are also effectively configured to identify threats in real-time. If a simulated attack goes unnoticed, you know immediately that there’s a gap in your detection logic or a misconfiguration that needs fixing, long before a real attacker can exploit it.
An incident response (IR) plan that only exists on paper is more of a liability than an asset. BAS provides a safe environment to put your IR plan through its paces. When a simulated attack is launched, you can see how your team reacts. Do they follow the documented procedures? Are communication channels clear? Do they have the access and tools they need to investigate and contain the threat? Running these drills helps your team build muscle memory and uncovers weaknesses in your response process. It’s much better to discover that a key team member doesn’t have the right permissions during a simulation than in the middle of a genuine, high-pressure security incident.
Your security controls—firewalls, endpoint protection, access policies—are the barriers standing between an attacker and your critical assets. BAS helps you pinpoint gaps in these controls by showing you exactly how an attacker could bypass them. By simulating real-world attacks, you can identify vulnerabilities that might otherwise go unnoticed. For example, a simulation might reveal a misconfigured firewall rule or a missing patch that creates a clear path to a sensitive server. This provides your team with concrete, actionable data to guide vulnerability and threat prioritization, ensuring you focus your remediation efforts on the weaknesses that pose the greatest risk.
Building an effective monitoring framework is less about buying another tool and more about creating a smart, repeatable process. A threat-informed approach connects the dots between what’s happening in the wild and what’s vulnerable inside your own environment. It’s a strategy that helps you cut through the noise of endless alerts and focus your team’s limited time and resources on the threats that actually pose a risk to your business.
Instead of reacting to every single alert, you can proactively hunt for and fix the security gaps that attackers are most likely to exploit. This requires a structured approach that integrates intelligence into your daily operations. By building a framework around this principle, you can create a sustainable and effective monitoring program that adapts as new threats emerge. The following steps will guide you in creating a system that doesn’t just find problems, but helps you solve the right ones first.
Your security team is likely facing a mountain of vulnerabilities with not enough time to patch them all. This is where threat intelligence becomes your most valuable filter. Instead of working through a list based solely on CVSS scores, you can integrate real-world data on which vulnerabilities are being actively discussed, weaponized, and used in attacks. This allows you to practice effective vulnerability and threat prioritization by focusing on issues that present a clear and present danger. This intelligence-driven approach ensures your team spends its time on fixes that deliver the biggest impact on your security posture, moving you from a “patch everything” to a “patch what matters” mindset.
Not all vulnerabilities are created equal. One might have a critical CVSS score but no known public exploit, while another with a lower score is being actively used in ransomware campaigns. A threat-informed framework helps you focus on the latter. By understanding the attacker’s playbook and the specific exploits they favor, you can fine-tune your detection rules and monitoring efforts. Keeping up with the latest Threat Advisories gives you the context to spot the early warning signs of an attack. This focus on actively exploited vulnerabilities is one of the fastest ways to reduce your risk and shorten the time it takes to spot and stop a real incident.
Finding a critical threat is only half the job. A strong monitoring framework must connect detection directly to action. When your system flags a high-priority vulnerability, the next step shouldn’t be a mystery. The process should automatically generate a clear remediation plan: Who is responsible for the patch? What is the deadline? How will we verify the fix was successful? Your monitoring data provides the rich context needed to build these plans, helping you understand the potential impact and the best way to mitigate the risk. A unified platform like Uni5 Xposure can turn your monitoring system from a simple alarm into a complete workflow engine that drives remediation.
The threat landscape is constantly shifting, which means your monitoring framework can’t be a “set it and forget it” project. True continuous monitoring is a loop: you monitor, analyze, act, and then refine your approach based on what you’ve learned. This means regularly reviewing your intelligence sources, updating your detection rules, and assessing the effectiveness of your remediation workflows. Committing to this cycle ensures your defenses evolve alongside attacker tactics. This ongoing process is the foundation of a proactive security culture and is essential for maintaining Total Attack Surface Management over time.
What’s the real difference between continuous monitoring and just running frequent scans? Think of it this way: scheduled scans are like taking a photo of your security posture. You get a clear image, but it’s only accurate for that specific moment. Continuous monitoring is like a live video feed. It gives you an always-on, real-time view of your entire environment, allowing you to see changes and potential threats as they happen, not just when the next scan is scheduled to run.
My team is already drowning in alerts. Won’t this just add to the noise? That’s a completely valid concern, and it’s a problem many teams face. A smart continuous monitoring strategy actually does the opposite. By integrating threat intelligence and understanding which of your assets are most critical, it helps you filter out the low-level noise. The goal isn’t to create more alerts, but to surface the right ones—the ones that indicate a genuine, high-priority risk to your organization—so your team can focus on what truly matters.
How is Breach and Attack Simulation (BAS) different from a regular penetration test? While both are used to test your defenses, they serve different purposes. A penetration test is typically a manual, point-in-time engagement where an expert tries to find a way into your network. Breach and Attack Simulation, on the other hand, is an automated and continuous process. It safely runs simulations of known attacker techniques to constantly validate that your security tools are configured correctly and are detecting threats as you expect them to. It’s less about finding a single new way in and more about ensuring your existing defenses are working 24/7.
Why is incorporating threat intelligence so important for monitoring? Threat intelligence provides the essential context that turns raw data into actionable insight. Without it, a vulnerability is just a technical flaw with a score. With threat intelligence, you know if that same vulnerability is being actively used in ransomware campaigns targeting your industry. This allows you to prioritize your team’s efforts with incredible precision, focusing on fixing the weaknesses that attackers are actually exploiting right now.
What’s the most important first step to building a continuous monitoring program? Before you can monitor anything effectively, you have to know what you need to protect. The foundational first step is to conduct a thorough discovery and inventory of all your assets. This means identifying every server, endpoint, cloud instance, and application across your entire environment. You can’t secure what you can’t see, and a complete asset inventory gives you the map you need to build a meaningful and comprehensive monitoring strategy.