Comprehensive Threat Exposure Management Platform
 Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the Report
Critical Threat Research : Middle-East at WAR: The Rapidly Escalating Iranian Cyber Threat Download the ReportIf you’re on a vulnerability management team, you’re likely drowning in a sea of CVEs. Your scanners produce massive lists of potential weaknesses, but with limited time and resources, which ones do you fix first? A high CVSS score doesn’t always translate to real-world risk. You need context to prioritize effectively. This is the problem that Breach and Attack Simulation (BAS) solves. It goes beyond just identifying vulnerabilities by safely testing if they are actually exploitable in your environment. This allows you to focus your team’s efforts on the critical exposures that pose a genuine threat to your organization.
Think of Breach and Attack Simulation (BAS) as your security team’s personal sparring partner. It’s an automated method that continuously runs safe, simulated cyberattacks against your own environment. Instead of waiting for a real attacker to show you where your defenses are weak, a BAS platform proactively tests them with simulations of malware, phishing, and other common attack techniques. This gives you a constant, real-time view of your security posture.
This proactive approach helps you move beyond just hoping your security controls are working. It provides concrete proof. By safely replicating the methods real attackers use, you can find and fix security gaps before they can be exploited. It’s a fundamental part of a modern adversarial exposure validation strategy, allowing you to test your defenses against the kinds of threats you’re most likely to face. This continuous feedback loop is essential for understanding how resilient your organization truly is.
So, how does this actually work? BAS platforms typically place lightweight simulators or agents across your network—in endpoints, on servers, and in the cloud. These agents then execute a wide range of attack scenarios, mimicking the tactics, techniques, and procedures (TTPs) used by actual threat actors. The platform then observes what happens. Did your firewall block the connection? Did your EDR solution detect the simulated malware? Did your email gateway flag the phishing attempt?
The beauty of this process is that it’s automated and continuous. You can run these simulations 24/7 without disrupting your business operations or requiring a massive hands-on effort from your team. The results give you immediate, actionable insights into whether your security tools are configured correctly and are performing as expected, helping you fine-tune your defenses and response plans.
At its heart, a BAS platform is designed to answer one critical question: “Are my security controls working?” A primary function is to assess the performance of your entire security stack, from firewalls and antivirus software to more advanced threat detection systems. Instead of relying on vendor claims or assumptions from your last audit, BAS provides measurable data on how your tools stand up to simulated attacks.
Another key component is the ability to map potential attack paths and identify exploitable vulnerabilities. By analyzing how far a simulated attack can get, BAS platforms can estimate the potential impact of a breach. This helps you focus your remediation efforts where they matter most. This kind of data-driven insight is crucial for effective vulnerability and threat prioritization, ensuring your team spends its time on the risks that pose the greatest threat to your organization.
Traditional security testing methods like penetration testing and vulnerability scanning are foundational to any security program. But they often provide a static snapshot in time. Breach and Attack Simulation (BAS) offers a more dynamic and realistic view of your security posture. It doesn’t replace these traditional methods but works alongside them to move your testing from a periodic check-up to continuous, automated validation. Let’s break down how it’s different.
Penetration testing is like hiring a skilled ethical hacker to find and exploit vulnerabilities over a set period. It’s a manual, point-in-time assessment that’s great for uncovering unknown weaknesses. BAS, however, automates this process by continuously running simulated attacks based on known adversary tactics, techniques, and procedures (TTPs). Instead of a one-time test every quarter, you get ongoing validation that your defenses can block real-world threats. This allows you to test your adversarial exposure against a wide range of attack scenarios, not just what a single tester can find in a limited timeframe.
Think of a red team exercise as a deep, manual, and objective-driven campaign mimicking a specific adversary. These exercises are incredibly valuable for testing your team’s response but are also resource-intensive and infrequent. BAS offers a more scalable approach. It uses automation to replicate attacker behaviors, allowing you to run thousands of simulations across your entire infrastructure continuously. While a red team provides unparalleled depth for a specific scenario, BAS provides the breadth and consistency needed to test all your defenses all the time, without the heavy manual lift and associated costs.
Vulnerability scanners are great at inventorying potential weaknesses. They tell you where you might have an unlocked door. The problem is, they don’t confirm if an attacker could actually walk through it. A scanner might flag a high-severity vulnerability, but another control could be blocking any attempt to exploit it. BAS closes this gap. It safely simulates an attack to see if your security controls actually work as expected. This helps you prioritize vulnerabilities based on validated risk, so your team can focus on fixing the exposures that truly matter.
Let’s be honest: managing a sprawling attack surface can feel like a constant game of catch-up. You patch vulnerabilities, configure firewalls, and deploy security tools, but a nagging question always remains: Is it actually working? This is where Breach and Attack Simulation (BAS) changes the game. Instead of waiting for an incident to reveal a weakness, BAS lets you proactively test your defenses against the same tactics real attackers use. It’s about shifting from a reactive posture—where you’re always responding to alerts—to a proactive one where you’re actively hunting for gaps before they can be exploited.
Think of it as a continuous, automated sparring partner for your security team. BAS platforms don’t just point out theoretical weaknesses; they safely simulate attacks to see how your security controls respond in real-time. This gives you concrete proof of what’s working and, more importantly, what isn’t. By integrating BAS into your security program, you move beyond assumptions and checklists. You get clear, actionable data on your security posture, helping your team focus its limited time and resources on the fixes that matter most. It’s the difference between hoping you’re secure and knowing you are.
You’ve invested heavily in firewalls, EDR, and other security tools, but how do you know they’re configured correctly and performing as expected? BAS provides the answer by running safe, simulated cyberattacks to test your defenses. This isn’t a one-and-done check; it’s a continuous process that validates your security controls around the clock. This constant testing ensures that a misconfiguration or a missed update doesn’t leave a critical gap in your defenses. By automating this process, you get a real-time view of your security effectiveness, allowing you to prove that your investments are delivering the protection you need. This is a core part of adversarial exposure validation, giving you confidence in your security stack.
Traditional vulnerability scanning is essential, but it often produces a long list of issues with little context. BAS complements this by showing you which vulnerabilities are truly exploitable in your environment. It helps you find the weak spots that scanners might miss, like policy gaps or misconfigurations that create an attack path. By simulating attacks, BAS helps you move beyond simple scanning to a more robust program for vulnerability and threat prioritization. Instead of just knowing a vulnerability exists, you’ll understand how an attacker could leverage it. This context is crucial for focusing your remediation efforts on the flaws that pose the most immediate risk to your organization.
Penetration testing and red team exercises are valuable, but they are often expensive, time-consuming, and only provide a point-in-time snapshot of your security. BAS offers a more scalable and cost-effective alternative. Because the simulations are automated, you can run them continuously across your entire infrastructure without the high costs associated with manual testing. This ongoing approach means you can identify and fix issues as they arise, rather than waiting months for the next scheduled pen test. This allows your team to maintain a consistent security posture and adapt quickly to new threats, all while making the most of your security budget.
The ultimate goal of any security program is to stop attacks before they cause damage. BAS helps you achieve this by putting you in the attacker’s shoes. It uses automated tools to simulate real-world cyberattacks, giving your security team a clear view of all the ways an adversary could breach your network. By running these simulations, you can identify and close security gaps before a real attacker finds them. This proactive approach helps you stay ahead of emerging threats and harden your defenses against sophisticated attack techniques. It’s a key component of a modern threat exposure management platform that helps you secure your organization from the inside out.
A Breach and Attack Simulation (BAS) platform is a powerful tool on its own, but it becomes truly strategic when you infuse it with threat intelligence. Without it, you’re essentially testing your defenses against a generic library of potential attacks. While that’s useful, it’s not efficient. It’s like preparing for every possible weather event at once instead of just checking the forecast for a hurricane warning.
Threat intelligence acts as that forecast. It provides the context needed to focus your simulations on the threats that are most likely to target your organization. Instead of running random attack scenarios, you can emulate the specific tactics, techniques, and procedures (TTPs) used by threat actors who are active in your industry or region. This intelligence-driven approach transforms BAS from a broad security validation tool into a precision instrument for proactive defense. By understanding which vulnerabilities are being actively exploited, you can direct your BAS platform to test your resilience against those specific threats, ensuring your security team is spending its time on what matters most.
The primary function of a BAS platform is to automatically test your security posture by emulating real-world attack scenarios. But how does it know which scenarios are “real-world”? That’s where threat intelligence comes in. It provides the data on current attacker behaviors, malware, and campaigns circulating in the wild. This allows the BAS tool to move beyond theoretical attack paths and run simulations that mirror what’s actually happening. This process of adversarial exposure validation ensures your tests are grounded in reality, giving you a much more accurate picture of how your defenses would perform against a genuine threat.
Your vulnerability scanner probably gives you a list of weaknesses as long as your arm. The challenge isn’t finding vulnerabilities; it’s knowing which ones to fix first. Threat intelligence helps BAS solve this problem by highlighting which vulnerabilities are not just theoretical but are actively being exploited by attackers. By focusing your simulations on these high-risk vulnerabilities, you can quickly see if your existing controls can block an exploit. This helps you prioritize remediation efforts based on active threats, not just on a CVSS score, allowing your team to address the most critical gaps first.
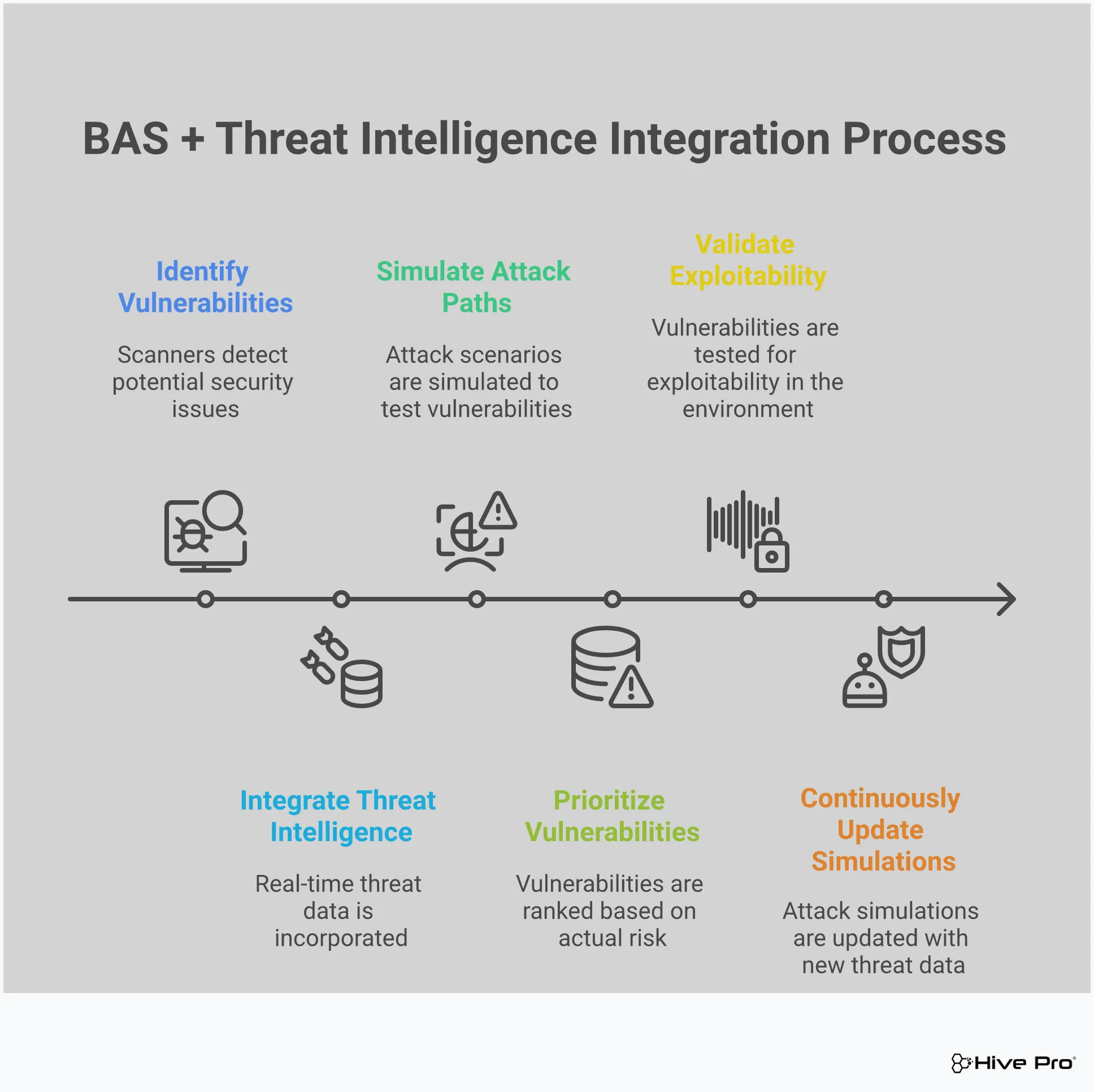
Effective BAS platforms use “attack playbooks” to run their simulations. These are pre-defined scripts that mimic a specific type of attack from start to finish. When these playbooks are informed by up-to-the-minute threat intelligence, they become incredibly powerful. You can create tailored playbooks that reflect the current threat landscape, testing your defenses against the exact methods a specific ransomware group or APT might use. This intelligence-driven approach allows you to automate tests for specific threat vectors, helping you continuously validate your security posture against the evolving tactics detailed in the latest threat advisories.
Once you’ve decided to bring Breach and Attack Simulation into your security program, the next step is choosing the right platform. Not all BAS solutions are created equal, and the one you pick should align with your specific environment, team capabilities, and security goals. Think of it less like buying an off-the-shelf product and more like finding a partner for your security team. A great BAS platform doesn’t just run simulations; it provides context, integrates with your existing tools, and gives you a clear path to improve your defenses.
The right solution moves beyond simply identifying gaps. It helps you understand the potential impact of those gaps and prioritize fixes based on real-world threats. As you evaluate your options, focus on a few key areas: the depth and breadth of the attack library, how well it plays with your current security stack, the quality of its reporting and remediation guidance, and whether it’s powered by timely threat intelligence. These components are what separate a basic testing tool from a true adversarial exposure validation platform that strengthens your security posture.
The heart of any BAS platform is its library of attack simulations. You need a tool that offers a wide variety of tests covering the full spectrum of attacker tactics, techniques, and procedures (TTPs). Look for a library that is mapped to established frameworks like MITRE ATT&CK, as this ensures you’re testing against recognized adversary behaviors. Just as important is how often the library is updated. Cyber threats change constantly, so your BAS platform should be fed with new simulations that reflect the latest malware, ransomware, and attack campaigns. The ability to create custom attack scenarios is also a huge plus, as it lets you test for threats specific to your industry or organization.
A BAS platform shouldn’t operate in a silo. To get the most value, it needs to integrate smoothly with the security tools you already use. Think about your SIEM, SOAR, EDR, and vulnerability management solutions. When your BAS platform can communicate with these systems, you can create a powerful, closed-loop security process. For example, an integration with your EDR can confirm whether it detected and blocked a simulated attack. Connecting to your vulnerability scanner can help correlate a failed security control with a specific unpatched vulnerability. This level of integration turns siloed data into a unified view of your cyber risks, making your entire security ecosystem more effective.
Running simulations is just the first step. The real value comes from the output. A good BAS solution provides clear, automated reports that are easy to understand for both technical teams and executive leadership. These reports should highlight security gaps, show trends over time, and demonstrate the effectiveness of your security controls. But reporting isn’t enough. Look for a platform that offers actionable remediation guidance. Instead of just telling you a control failed, it should provide specific, step-by-step instructions on how to fix the issue. This helps your team move from detection to remediation much faster, reducing your overall exposure.
What makes an attack simulation truly powerful? When it’s based on what’s actually happening in the wild. The best BAS platforms are fueled by built-in, up-to-the-minute threat intelligence. This ensures that the simulations you’re running mimic the real-world attacks your organization is most likely to face. A platform backed by a dedicated research team, like HiveForce Labs, can provide context on which vulnerabilities are being actively exploited and which attacker groups are targeting your industry. This intelligence-driven approach allows you to prioritize your defensive efforts, focusing on the threats that pose the most immediate and significant risk to your business. It’s a key part of building a proactive security strategy.
If you’re on a security team, you’re constantly asked to prove your defenses work against an ever-changing threat landscape. It’s a tough spot to be in. Breach and Attack Simulation (BAS) helps you move from assuming you’re protected to knowing where you stand. By safely and continuously simulating real-world attacks, BAS platforms provide concrete answers to your most pressing security questions and help you tackle some of the most persistent challenges in cybersecurity.
Annual penetration tests are useful, but they only give you a snapshot in time. Attackers, on the other hand, work 24/7. A BAS platform acts like a persistent, automated red team, constantly running safe attack simulations to find new gaps as they emerge. This continuous testing cycle means you’re not waiting months to discover a critical misconfiguration or an unpatched system. Instead, you get real-time visibility into vulnerabilities across your entire digital footprint. By proactively identifying these weaknesses, your team can manage your total attack surface and fix gaps before an actual attacker finds them, keeping you a step ahead.
You’ve invested heavily in a security stack with firewalls, EDR, and other tools. But are they configured correctly and actually stopping threats? It’s a question that keeps security leaders up at night. BAS provides the answer by putting your defenses to the test. It simulates specific attack techniques—like ransomware deployment or data exfiltration—to see if your security controls detect and block them as expected. This process of adversarial exposure validation helps you identify configuration drift, policy gaps, and tools that aren’t performing. It gives you hard data to optimize your security stack and ensure you’re getting the full value from your investments.
Communicating security effectiveness to the board or executive leadership can be difficult. Technical jargon and vulnerability counts don’t always translate into business context. BAS helps bridge this gap by generating clear, data-driven reports that demonstrate your security posture in an easy-to-understand way. Instead of saying, “We think we’re secure,” you can show, “We tested our defenses against the latest threats targeting our industry, and here’s how we performed.” This evidence-based approach builds trust, justifies security spending, and provides the documentation needed to demonstrate compliance with regulatory requirements. It turns security from a cost center into a proven business enabler.
Breach and Attack Simulation is a powerful technology, but like any emerging tool, it’s surrounded by a few misconceptions. It’s easy to get the wrong idea about what BAS can and can’t do for your security program. Let’s clear the air and debunk some of the most common myths so you can see exactly where it fits into your strategy.
Understanding the reality of BAS helps you set the right expectations and use the tool for what it does best: providing continuous, automated insights into your security posture. It’s not a magic bullet, but it is a game-changer for teams looking to move from reactive defense to proactive security validation. By separating fact from fiction, you can make a more informed decision about how to integrate BAS into your existing workflows and get the most value from your investment.
One of the biggest myths is that BAS makes penetration testing obsolete. This couldn’t be further from the truth. Think of it this way: BAS and penetration testing are partners, not rivals. BAS provides continuous, automated testing against known threats, giving you a constant pulse on your security controls. It’s like having an automated system that checks all your doors and windows every single day.
Penetration testing, on the other hand, is a deep, manual dive conducted by a human expert who tries to find and exploit vulnerabilities using creativity and intuition—things an automated tool can’t replicate. BAS works with other security tests to create a more robust adversarial exposure validation strategy. You need both the daily automated checks and the periodic deep-dive inspections to be truly secure.
No single tool can offer a complete, 100% view of your security posture, and BAS is no exception. While it gives you an incredible amount of insight into how your defenses stand up to known attack techniques, it doesn’t fully replicate the unpredictable nature of a human attacker. Just because you run a BAS test doesn’t mean you’ve tested every possible way a real hacker might operate.
BAS platforms excel at simulating tactics, techniques, and procedures (TTPs) from frameworks like MITRE ATT&CK. This is essential for validating your controls against real-world threats. However, true security visibility comes from combining automated simulation with human-led threat intelligence and other testing methods. BAS gives you a clear, evidence-based picture of your resilience against known threats, which is a massive advantage, but it’s one important piece of a larger security puzzle.
It’s easy to assume that advanced security tools like BAS are only for massive enterprises with huge budgets and dedicated security teams. In reality, BAS solutions are valuable for organizations of all sizes. For mid-sized businesses with limited security staff, BAS can be a force multiplier. It automates the kind of continuous testing that would otherwise require a full-time red team, which many companies simply can’t afford.
By automating security validation, BAS helps smaller teams focus their limited resources on the most critical risks. It provides clear, actionable data that allows them to prioritize remediation efforts effectively. A modern Threat Exposure Management Platform makes this technology accessible, helping any organization, regardless of size, validate its security controls and prove its defensive posture with confidence.
Adopting any new technology comes with a few hurdles, and Breach and Attack Simulation is no exception. But thinking through these potential challenges ahead of time is the best way to ensure a smooth rollout and get the most value from your platform. A little preparation goes a long way in turning your BAS implementation from a project into a core part of your security strategy.
By focusing on a few key areas—managing alerts, empowering your team, and ensuring seamless integration—you can set your BAS program up for long-term success. This approach helps you avoid common pitfalls that can slow down progress and ensures your team can hit the ground running.
One of the first challenges teams often face is an influx of alerts. If not managed properly, this can lead to alert fatigue, where your team starts tuning out important notifications. The goal is to filter the noise and focus on actionable insights. Start by fine-tuning your BAS platform’s settings to align with your specific environment and risk tolerance. Establish clear, documented procedures for how your team should investigate and validate alerts. This ensures that everyone follows a consistent process, helping to quickly distinguish real threats from false alarms and keeping your team focused on what matters most.
A BAS platform is a powerful tool, but it’s the people behind it who make it effective. Before you roll out a solution, take stock of your team’s current skills. Do they have experience with similar security testing tools? Answering this will help you identify any training needs. When evaluating BAS solutions, look for ones that are intuitive and minimize manual effort. A platform with clear reporting and guided remediation can significantly lower the learning curve. Investing in training and tools that empower your security team will ensure you can fully utilize the technology and get the security outcomes you’re looking for.
For a BAS platform to be truly effective, it can’t operate in a silo. It needs to become part of your existing security ecosystem. A successful implementation requires seamless integration with the tools you already use, like your SIEM, SOAR, and ticketing systems. This allows the insights from your attack simulations to flow directly into your remediation workflows, making them immediately actionable. When choosing a BAS solution, prioritize platforms that offer robust APIs and pre-built integrations. This ensures that your new tool will enhance, not complicate, your overall security operations and strategy.
Adopting a Breach and Attack Simulation (BAS) platform is a fantastic step toward a more proactive security posture. But like any powerful tool, its effectiveness depends on how you use it. Simply running simulations isn’t enough; you need a strategy to turn those automated attacks into meaningful security improvements. Getting the most out of your BAS investment comes down to thoughtful planning and integration. By following a few key practices, you can ensure your BAS platform delivers continuous value, helping your team stay ahead of threats and keep your security controls sharp. These steps will help you move from simply testing your defenses to actively hardening them based on real-world attack scenarios.
Before you run your first simulation, take a step back and ask: What do we want to achieve? Your goals for BAS should align directly with your broader security strategy. Are you trying to validate the effectiveness of a new firewall? Do you need to prove compliance for an upcoming audit? Or is your main goal to reduce the time it takes to detect and respond to threats? Defining these objectives upfront is critical.
Once you know what you’re aiming for, you can establish clear metrics to measure success. This could be a percentage reduction in critical security gaps, an improvement in your security control validation scores, or a faster mean time to remediation (MTTR) for issues identified by the BAS platform. Having these key performance indicators (KPIs) in place allows you to track progress and demonstrate the value of BAS to stakeholders.
A BAS platform shouldn’t operate in a silo. To get the full benefit, you need to weave it into the fabric of your daily security operations. The insights from BAS simulations are incredibly valuable for your vulnerability management team. When a simulation successfully exploits a weakness, that finding should automatically feed into your vulnerability and threat prioritization process, pushing that issue to the top of the remediation list.
This integration extends to your Security Operations Center (SOC) as well. Use BAS to run attack scenarios and see if your detection and response tools, like your SIEM and SOAR platforms, trigger the right alerts. This helps you fine-tune your detection rules and ensures your incident response playbooks are effective. By making BAS a core part of your existing workflows, you create a continuous feedback loop that strengthens your entire security program.
The threat landscape is anything but static; new attack techniques and vulnerabilities emerge constantly. Your BAS platform must keep pace. A key practice is to ensure your tool’s attack simulation library is continuously updated with the latest threat intelligence. This guarantees you’re testing your defenses against the same tactics that real-world adversaries are using right now. Check that your provider offers regular updates based on sources like the MITRE ATT&CK framework and current threat advisories.
Beyond updates, you also need to calibrate the platform for your specific environment. Regularly review simulation results to identify trends and fine-tune the tests to minimize noise and false positives. As your IT environment changes with new applications and infrastructure, your BAS configuration should evolve with it. This ongoing process of updating and calibrating ensures your simulations remain relevant and your security insights stay sharp.
Adopting a Breach and Attack Simulation (BAS) platform is more than just deploying a new tool; it’s about building a proactive security process. To make the transition smooth and effective, you need a clear plan. Start by defining your security objectives and identifying the specific threats you want to simulate. What are your biggest concerns? Are you worried about ransomware spreading through your network, or are you focused on protecting specific high-value assets? Answering these questions helps you tailor the simulations to your organization’s unique risk profile and ensures you’re testing for the threats that matter most.
Next, think about how your BAS platform will fit into your current security stack. A BAS solution delivers the most value when it works with your other tools. You should plan on integrating BAS tools with your Security Information and Event Management (SIEM) and Endpoint Detection and Response (EDR) solutions. This integration creates a feedback loop, allowing you to see not only if an attack could succeed but also if your existing tools detected and responded to it correctly. This gives you a much clearer picture of your true security posture.
Once you’re set up, remember that BAS is not a one-time test. The threat landscape is always changing, and so are your systems. It’s essential to establish a continuous testing cycle to regularly assess your security controls and adapt to new threats as they appear. This ongoing approach turns security validation from a periodic event into a consistent, automated process. Finally, be prepared for a few bumps in the road. Addressing these challenges early, like managing false positives or making sure your team isn’t overwhelmed with data, will help you get the most out of your BAS platform from day one.
My vulnerability scanner already tells me what’s broken. How is BAS any different? That’s a great question because it gets to the heart of the issue. A vulnerability scanner is fantastic at creating an inventory of potential weaknesses—think of it as a list of all the unlocked doors and windows in your building. A Breach and Attack Simulation (BAS) platform, however, actually tries to open them. It safely simulates an attack to see if an adversary could truly walk through that unlocked door, or if another security control, like a motion detector, would stop them. BAS provides the real-world context to your scanner’s findings, helping you see which theoretical weaknesses pose an actual, verifiable risk.
We already do annual penetration tests. Do we still need BAS? Penetration tests and BAS are partners, not competitors. A pen test is like hiring a highly skilled inspector for a deep, one-time assessment of your security. It’s incredibly valuable for finding unknown or complex flaws. BAS, on the other hand, is your automated, 24/7 security guard. It continuously runs simulations of known attack methods to ensure your defenses are working as expected day in and day out. You need both: the periodic deep dive from a human expert and the constant, automated validation to catch misconfigurations or gaps that appear between those tests.
Will a BAS platform just flood my team with more alerts? This is a common concern, but a well-implemented BAS platform should actually do the opposite. Instead of adding to the noise, it helps you filter it. By validating which vulnerabilities are truly exploitable, it allows your team to focus on a shorter, more critical list of confirmed exposures. It answers the question, “Of the thousands of alerts we have, which ones represent an immediate, provable threat?” This helps your team direct their energy toward fixing the problems that matter most, rather than chasing down every low-level alert.
What’s the most important feature to look for in a BAS solution? While many features are important, the one that makes the biggest difference is the quality and timeliness of its built-in threat intelligence. A BAS platform is only as good as the attacks it can simulate. Look for a solution that is constantly updated with information on the latest attacker tactics, techniques, and procedures. This ensures you aren’t just testing against a static library of old attacks, but against the real-world threats that are actively targeting organizations right now.
How does BAS help us prioritize which vulnerabilities to fix first? BAS helps you move beyond prioritizing based on generic severity scores alone. It adds two crucial layers of context. First, it validates whether a vulnerability is actually exploitable in your specific environment, given your unique security controls. Second, when powered by threat intelligence, it highlights which of those exploitable vulnerabilities are being actively used by attackers in the wild. This combination allows you to focus your team’s limited time and resources on fixing the exact weaknesses that pose the most immediate and realistic danger to your organization.