Comprehensive Threat Exposure Management Platform
Communicating the value of your security program to leadership can be a challenge. Pointing to a lack of breaches isn’t a metric; it’s a temporary state. To justify budgets and prove your strategy is working, you need hard data. This is where Breach and Attack Simulation platforms provide immense value. By continuously testing your controls, BAS tools generate concrete metrics on your security effectiveness, risk reduction over time, and overall defensive posture. This evidence-based approach transforms security from a cost center into a measurable business function, giving you the data you need to demonstrate a clear return on investment.
How do you know if your security controls will actually work during a real attack? You can have the best firewalls, EDRs, and security policies in place, but without testing them against realistic threats, you’re operating on assumptions. This is where Breach and Attack Simulation (BAS) comes in. Think of it as a continuous, automated fire drill for your entire security infrastructure. A BAS platform safely simulates the tactics, techniques, and procedures (TTPs) used by actual adversaries to see how your defenses hold up.
Unlike traditional penetration testing, which provides a point-in-time snapshot of your security posture, BAS offers a dynamic and ongoing assessment. It helps you move from a reactive stance to a proactive one by constantly validating your security controls. By automating these attack simulations, you can identify gaps and misconfigurations in your defenses before a real attacker exploits them. This process of adversarial exposure validation gives you a clear, evidence-based picture of which attack paths are viable and where your security investments are paying off.
The real value of BAS is its ability to provide actionable insights. Instead of just generating a long list of potential vulnerabilities, it shows you exactly how those weaknesses could be exploited. This context is critical for prioritizing remediation efforts. When you understand which vulnerabilities are part of a successful attack chain, you can focus your team’s limited resources on fixing the issues that pose the greatest risk. By using real-time threat intelligence to inform its simulations, a BAS tool ensures you’re always testing against the most current and relevant threats, helping you stay ahead of attackers.
Choosing the right BAS tool can feel overwhelming, but it really comes down to finding the best fit for your team’s specific needs and existing security stack. The market offers several strong platforms, each with a slightly different focus. Some excel at deep, customizable adversary emulation, while others prioritize automated testing or integration with threat intelligence feeds. The key is to understand what problem you’re trying to solve. Are you looking to validate specific controls against known adversary TTPs? Or do you need a broader, automated way to find holes in your defenses? Maybe your biggest priority is integrating BAS insights directly into your vulnerability management workflow.
To help you get a clearer picture, let’s walk through some of the leading BAS tools and what makes each one unique. We’ll look at how each platform approaches attack simulation, what kind of intelligence it uses, and how it presents its findings. This comparison will give you a solid starting point for figuring out which solution aligns with your security goals and helps you move from a reactive to a proactive security posture. We’ll cover everything from integrated platform solutions to specialized emulation tools, so you can make an informed decision.
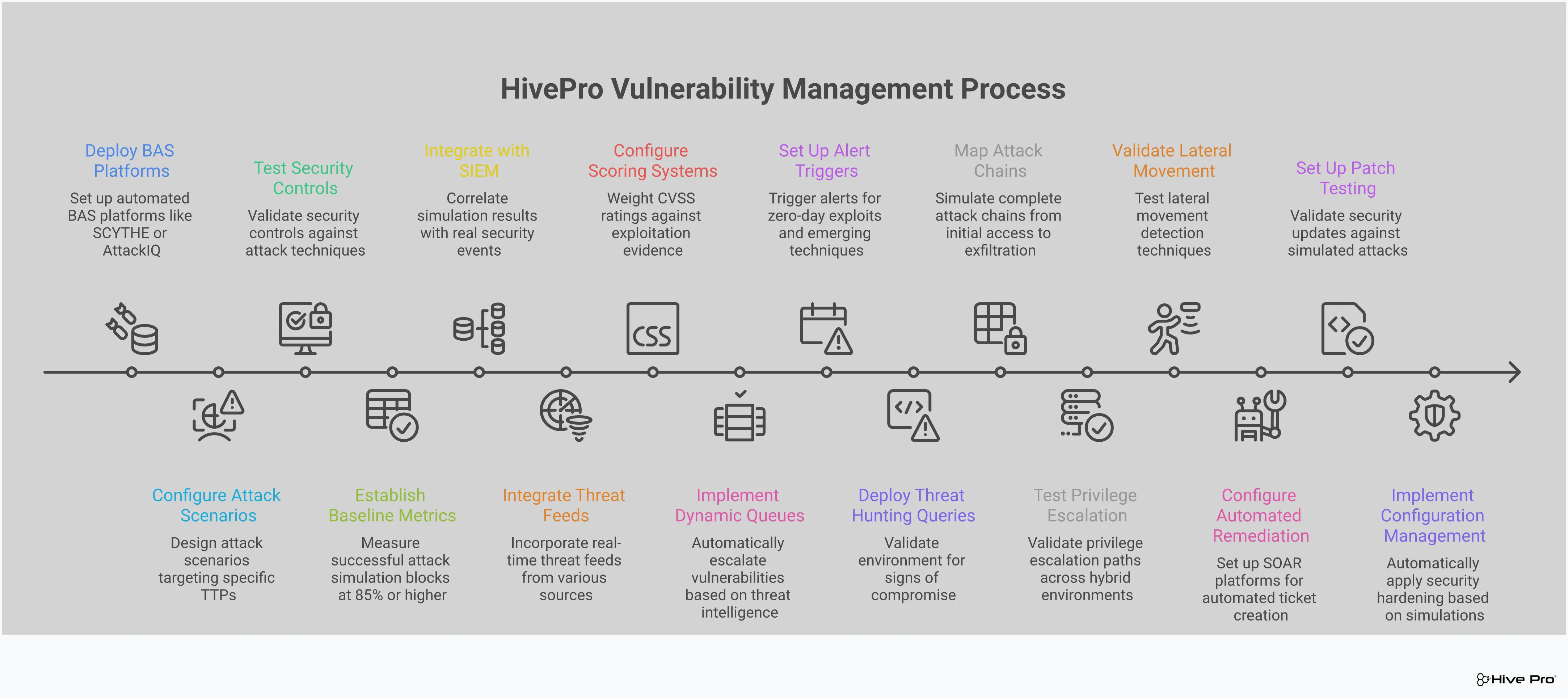
What makes Hive Pro’s approach stand out is that its BAS capabilities are an integral part of a complete threat exposure management platform. Instead of being a standalone tool, the Adversarial Exposure Validation feature works within a unified system that covers the entire exposure management lifecycle. This allows you to continuously, systematically, and automatically run attack simulations to assess how well your security controls hold up against real-world threats. Because it’s integrated, the insights from these simulations directly inform your vulnerability prioritization and remediation efforts, creating a more cohesive and proactive security workflow. This is ideal for teams looking to streamline their tools and get a single, clear view of their cyber risks.
SCYTHE is a great choice for teams that want to get deep into the weeds with adversary emulation. It focuses on giving you the power to create highly customizable and detailed security simulations. Think of it as a toolkit for building and running attack scenarios that mimic the exact threats you’re most concerned about. This level of control helps your organization pinpoint specific weak spots in your defenses, validate your security posture against known adversary tactics, and accurately measure your risk. If your team has the expertise and a need for granular, bespoke attack emulation, the SCYTHE platform provides the flexibility to do just that.
SafeBreach is built around the principle of continuous validation. Its platform is designed to constantly run a wide variety of real-world attack scenarios across your entire environment, from cloud to endpoint. The goal is to proactively find hidden weaknesses and security gaps before an actual attacker does. By simulating the full attacker kill chain, SafeBreach gives you a clear and ongoing assessment of your security posture. It’s a solid option for organizations that want to move away from periodic testing and adopt a more persistent, automated approach to validating their defenses against an ever-changing threat landscape.
If your security program is closely aligned with the MITRE ATT\&CK framework, AttackIQ is a tool worth exploring. It helps organizations systematically test, validate, and improve their cyber defenses using ATT\&CK as a blueprint. The platform provides critical insights into where your security controls are effective and where they fall short, all mapped directly to specific adversary techniques. This framework-centric approach makes it easier to communicate security performance to stakeholders and ensures your defensive strategy is comprehensive. AttackIQ is particularly useful for teams that want to measure their security effectiveness against a widely accepted industry standard.
Pentera carves out its niche by focusing on automated security validation and penetration testing. It’s designed to show you exactly how an attacker could breach your network by safely and automatically replicating their techniques. One of its key strengths is its ease of setup and operation, allowing security teams to get up and running quickly without a steep learning curve. The platform is also frequently updated with the latest exploits, ensuring your tests remain relevant to current threats. For teams that need the insights of a pen test but want the speed and scale of automation, Pentera offers a compelling solution.
Backed by Google’s extensive resources, Mandiant’s BAS solution is heavily driven by deep threat intelligence. It excels at managing your digital footprint and uses up-to-the-minute intelligence, including active monitoring of the dark web, to inform its attack simulations. This provides you with a highly accurate picture of the threats you are most likely to face. For organizations that prioritize intelligence-led security and want their validation efforts to be based on the very latest threat actor behaviors, Mandiant’s top-tier security validation is a significant advantage. It’s a powerful choice for mature security programs focused on staying ahead of sophisticated adversaries.
Choosing the right Breach and Attack Simulation (BAS) tool can feel overwhelming, but it boils down to finding a platform that fits your team’s workflow and gives you clear, actionable results. Not all BAS solutions are built the same. Some are great at running specific attack scenarios, while others provide a more holistic view of your security posture. As you evaluate your options, focus on tools that don’t just find problems but also help you fix them efficiently. A great BAS platform should feel like an extension of your security team, continuously testing your defenses and providing the insights you need to stay ahead of threats. Look for a solution that offers a blend of comprehensive testing, smart automation, and real-world threat context.
Your organization’s attack surface is vast, spanning everything from cloud infrastructure and web applications to endpoints and user credentials. A top-tier BAS tool needs to be able to simulate attacks across all of these vectors. It should safely mimic real-world attack techniques to test whether your existing security controls, like firewalls, WAFs, and EDR, are actually effective. This gives you a true picture of your defensive gaps. A platform that only tests one area, like email phishing, leaves you with significant blind spots. The goal is to achieve a complete total attack surface management strategy, and that starts with a tool that can challenge your entire security stack from every possible angle.
The threat landscape changes daily, which is why annual penetration tests are no longer enough to keep you secure. The real power of a BAS tool comes from its ability to run attack simulations continuously and automatically. Instead of a once-a-year snapshot, you get a constant stream of feedback on your security posture. This automated approach allows your team to validate controls around the clock without causing operational disruption or requiring manual intervention for every test. This continuous validation cycle ensures that your defenses are always working as expected and helps you quickly identify when a configuration change or a new threat has created a new vulnerability in your environment.
A BAS tool shouldn’t operate in a silo. To be truly effective, it needs to integrate smoothly with your existing security ecosystem, including your SIEM, SOAR, and ticketing systems. This integration streamlines the entire process from detection to remediation. For example, when a simulated attack successfully bypasses a control, the BAS platform can automatically create a ticket with all the relevant details for your team to investigate. This tight integration with your security stack turns insights into action much faster, reducing the manual effort required to manage and respond to identified weaknesses. It ensures that the valuable data from your BAS tool gets to the right people at the right time.
The MITRE ATT\&CK framework has become the common language for describing attacker behaviors. It’s a globally accessible knowledge base of adversary tactics and techniques based on real-world observations. Any BAS tool worth its salt will align its simulated attacks to this framework. This mapping ensures that your testing covers a comprehensive range of known threat actor behaviors, from initial access and execution to lateral movement and exfiltration. By using a framework-aligned tool, you can systematically measure your defenses against the same TTPs (tactics, techniques, and procedures) that real attackers use, making it easier to identify and prioritize your most critical security gaps.
Simulating generic attacks is useful, but simulating the exact attacks happening in the wild right now is a game-changer. The best BAS platforms are powered by real-time threat intelligence that informs which attack scenarios to run. This intelligence-led approach helps you focus on the threats that pose the most immediate risk to your organization. For instance, Hive Pro integrates threat intelligence from our in-house HiveForce Labs research team to ensure simulations are based on current, relevant attacker campaigns. This allows you to move beyond theoretical risks and concentrate your resources on defending against the active threats you are most likely to face.
Identifying a vulnerability is only the first step. A great BAS tool won’t just tell you what’s broken; it will give you clear, actionable guidance on how to fix it. After a simulation identifies a gap in your defenses, the platform should provide specific, step-by-step remediation advice. This might include vendor-specific configuration changes, general security best practices, or patches that need to be applied. This focus on vulnerability and threat prioritization helps your team cut through the noise and take immediate, effective action. The goal is to close security gaps quickly, and that can only happen when your team has clear instructions to follow.
Finding the right Breach and Attack Simulation (BAS) tool isn’t a one-size-fits-all process. The value you get from a platform depends entirely on your organization’s size, budget, and security maturity. A sprawling enterprise has very different needs than a nimble small business, and the pricing models reflect that. Let’s break down what to look for across different market segments so you can find a solution that fits your team and your wallet.
For large enterprises, a BAS tool must do more than just run simulations. It needs to be a core part of a comprehensive threat exposure management program. These organizations require a platform that can handle a massive and complex attack surface, integrate seamlessly with dozens of existing security tools, and provide a unified view of risk. The main value here is clarity and scale. Top-tier solutions use real-world threat intelligence to help you prioritize vulnerabilities based on active threats, not just theoretical risks. They offer adversarial exposure validation to safely mimic sophisticated attacks, testing whether your expensive security controls are actually working as expected.
Mid-market companies need to find the sweet spot between powerful capabilities and cost-effectiveness. You likely don’t have the same budget or team size as an enterprise, so efficiency is everything. The best BAS tools for this segment offer continuous and automated testing, which helps you assess your security posture without dedicating a full-time employee to the task. Look for platforms with inclusive pricing models where BAS is a core feature, not an expensive add-on. This approach lowers your total cost of ownership and ensures you get the tools you need to make a real impact. The goal is to find a unified platform that simplifies your security stack and gives you actionable insights without the enterprise-level price tag.
If you’re running a small business, every dollar counts. You need security tools that are both effective and affordable. BAS platforms can be a game-changer for small teams, offering a cost-effective way to find weak points in foundational security tools like firewalls and antivirus software. Leveraging adversarial simulations helps you identify and fix critical gaps before an attacker finds them. For small businesses, the value of a BAS tool lies in its ability to provide proactive security insights without requiring a team of dedicated analysts. It helps you focus your limited resources on the most pressing threats, ensuring you get the biggest security impact for your investment.
When you’re evaluating Breach and Attack Simulation tools, it helps to know what the market leaders do well and where they often fall short. This gives you a solid baseline for comparing features and finding the right fit for your team. Understanding these common strengths and weaknesses will help you ask the right questions during demos and trials.
Leading BAS platforms excel at continuously testing your defenses from an attacker’s perspective. They help you find security gaps by running realistic, simulated attacks against your systems, which is crucial for validating that your security controls are actually working and configured correctly. A key benefit is getting detailed reports that don’t just point out problems but also provide clear, actionable steps for remediation. Many top tools also feature extensive libraries of threat scenarios, ensuring your testing is comprehensive and relevant to the threats you face. This proactive approach helps you measure your risk against real-world threats and shorten the time it takes to find and fix critical issues.
Even the most popular BAS tools can come with challenges. Some teams find that user interfaces are confusing or that dashboards aren’t intuitive, making it difficult to get clear insights. The initial setup can also be a hurdle, sometimes requiring significant time and expert knowledge to get running. Users have reported issues with frequent bugs, slow updates, and the potential for false alarms that can lead to alert fatigue for your security team. Finally, the cost can be a major factor, with some platforms being too expensive for smaller organizations, limiting their accessibility. These hurdles can make it tough to get the full value out of the tool without dedicated resources.
For years, vulnerability management has felt like a constant, reactive scramble. A new critical vulnerability is announced, and teams rush to scan, identify, and patch thousands of assets, often relying on theoretical severity scores that don’t reflect real-world risk. It’s an exhausting cycle that leaves many security professionals wondering if their efforts are truly making a difference. This is where Breach and Attack Simulation (BAS) changes the game entirely.
Instead of just cataloging potential weaknesses, BAS platforms actively test your defenses. They run safe, controlled simulations that mimic the exact tactics, techniques, and procedures (TTPs) used by actual attackers. This approach moves your security program from a passive, checklist-based model to an active, evidence-based one. You stop guessing where you’re vulnerable and start knowing. By continuously testing your security controls against simulated attacks, you gain a clear, real-time picture of your security posture and can finally focus on the exposures that matter most. This is a core component of a modern Threat Exposure Management Platform.
Traditional vulnerability management often puts teams on the back foot, forcing them to react to an endless stream of newly discovered vulnerabilities. A BAS tool flips this dynamic. It allows you to get ahead of attackers by proactively seeking out weaknesses in your defenses before they can be exploited. Instead of waiting for a real incident to find out your firewall was misconfigured or your EDR solution missed a new attack technique, you can discover these gaps through automated simulations. This proactive stance helps you continuously harden your environment, prove the value of your security investments to leadership, and build a more resilient security program.
You’ve invested heavily in a suite of security tools, but how do you know they’re actually working as intended? BAS provides the answer by putting your security stack to the test. These platforms run simulations that directly challenge your firewalls, endpoint detection and response (EDR), email gateways, and other controls to see how they perform against common attack methods. This process of Adversarial Exposure Validation moves you beyond assumptions and provides concrete proof of your defensive capabilities. It helps you measure your true readiness to prevent and detect threats, identifying configuration drift or gaps in coverage so you can fix them before they become a real problem.
One of the biggest challenges in vulnerability management is figuring out what to fix first. A high CVSS score doesn’t always translate to high risk for your specific organization. A BAS platform helps you cut through the noise by showing you which vulnerabilities are truly exploitable in your environment. By simulating attack paths, you can see how an adversary could chain together multiple lower-risk vulnerabilities to achieve a critical objective. This context allows you to focus your team’s limited time and resources on the issues that pose an immediate danger, ensuring your vulnerability and threat prioritization is driven by actual, demonstrable risk.
A Breach and Attack Simulation tool is powerful on its own, but adding threat intelligence makes it a truly strategic asset. Without this intelligence, BAS is like a boxer training against a generic punching bag. It’s good practice, but it doesn’t prepare you for a specific opponent. With threat intelligence, you’re sparring against a partner who mimics your next opponent’s exact fighting style, weaknesses, and signature moves.
This context allows your security team to move beyond generic testing and start validating defenses against the specific threats targeting your industry and infrastructure. It transforms BAS from a simple testing tool into a proactive defense mechanism. Instead of just asking, “Are our controls working?” you can ask, “Are our controls working against the threats we are most likely to face today?” This shift is fundamental to building a resilient security posture that can stand up to real, active adversaries. By integrating real-time data, you ensure your simulations are not just theoretical exercises but practical, relevant tests that provide a clear picture of your security readiness.
Threat intelligence gives your BAS tool a direct line to what’s happening on the front lines of cyber warfare. It provides the playbook, detailing the latest tactics, techniques, and procedures (TTPs) that attackers are using. This allows the BAS platform to run simulations that mirror these real-world attack paths, testing your defenses against the same methods an actual adversary would use. Instead of running a generic malware simulation, you can simulate an attack from a specific ransomware group known to target your industry. This gives you a much more accurate and actionable assessment of your security controls’ effectiveness against relevant threats.
Your vulnerability scanner probably gives you a list a mile long, and trying to patch everything at once is impossible. Threat intelligence helps you cut through the noise by highlighting which vulnerabilities are being actively exploited in the wild. A BAS tool with integrated threat intelligence can then focus its attack simulations on these high-risk areas. This approach allows you to prioritize vulnerabilities based on actual, immediate danger, not just a theoretical CVSS score. You can confidently direct your remediation efforts to the flaws that matter most, knowing you’re fixing the exact holes that attackers are targeting right now.
The threat landscape changes constantly. What was a major threat last month might be old news today, and new attack methods appear all the time. A BAS tool needs a constant stream of fresh information to stay effective, and that’s where intelligence feeds come in. These feeds provide continuous updates, ensuring your simulations reflect the very latest attack techniques. This means your BAS platform can safely mimic emerging threats to test if your security controls, from firewalls to EDR, are prepared. This ongoing process of adversarial exposure validation ensures your testing is always relevant, giving you an accurate picture of your readiness.
Adopting a BAS tool can be a game-changer for your security posture, but it’s not always a simple plug-and-play process. Like any powerful technology, it comes with its own set of implementation hurdles. Being aware of these common challenges ahead of time can help you plan your strategy, choose the right tool, and get the most value from your investment. Understanding these potential roadblocks is the first step toward building a more resilient and proactive security program that truly strengthens your defenses against real-world attacks.
One of the first things teams notice is that BAS tools can generate a lot of noise. Because these platforms are designed to simulate attacks, they can trigger alerts that aren’t tied to a real threat. Without proper tuning, this can quickly lead to alert fatigue, where your security team is so overwhelmed with notifications that they start to overlook them. This constant stream of alerts can diminish the effectiveness of security operations as your team struggles to separate the simulated noise from a genuine incident. It’s crucial to configure your BAS tool and downstream systems to differentiate between simulations and actual attacks.
A BAS platform is a powerful instrument, but it needs a skilled musician to make it sing. Implementing and managing these tools effectively requires time and expertise. Your team needs to know how to design relevant attack scenarios, interpret the results, and translate those findings into actionable remediation steps. For smaller organizations or teams that are already stretched thin, finding the necessary resources and skilled personnel can be a significant challenge. When evaluating tools, consider the user interface and the level of support and training the vendor provides to help your team get up to speed quickly.
The cat-and-mouse game between attackers and defenders never stops. New vulnerabilities, tactics, and procedures emerge all the time. A BAS tool is only as effective as its ability to simulate these modern threats. If its library of attack simulations is outdated, you’re essentially testing your defenses against yesterday’s problems. The landscape of cyber threats is constantly changing, so it’s vital to choose a BAS solution that receives regular updates based on the latest threat intelligence. This ensures your simulations remain relevant and provide a true test of your organization’s resilience against current attack methods.
Your security stack is likely already a complex ecosystem of different tools, from firewalls and endpoint detection to SIEM and SOAR platforms. Introducing another tool can be a major integration headache. A BAS platform needs to communicate with your existing infrastructure to run simulations and gather results effectively. Many organizations struggle with this complexity. This is where unified platforms can make a difference. Solutions that combine BAS with other security functions help you prioritize vulnerabilities based on simulation results and real-time data, streamlining the process from testing to remediation without the friction of integrating disparate systems.
Investing in a Breach and Attack Simulation (BAS) tool is a significant step, but the real work begins after implementation. How do you prove it’s actually making a difference? Measuring the value of your BAS tool isn’t just about justifying the expense to leadership; it’s about confirming that your security posture is genuinely improving. The right metrics show you where your defenses are getting stronger and where you still have work to do. Thinking about value goes beyond a simple ROI calculation. It involves tracking risk reduction, seeing how much faster your team responds to threats, and even making audits less painful. When you can connect your BAS tool directly to these improvements, you’re not just showing its worth, you’re building a stronger case for a proactive security strategy.
The most direct way to see the value of a BAS tool is by tracking how it reduces your overall risk. Start by establishing a baseline of your security performance before you fully implement the tool. Then, you can measure progress against it. Key metrics to watch include the percentage of simulated attacks that are successfully blocked, the reduction in critical vulnerabilities that are exploitable, and the overall improvement in your security control effectiveness. You can use BAS tools for network device testing and to verify which threats are being caught and which aren’t. Over time, you should see a clear downward trend in your exposure, providing concrete proof that your defenses are getting stronger and your investment is paying off.
A BAS platform is like a sparring partner for your security team. It constantly tests their readiness and helps them sharpen their skills. By running regular, automated attack simulations, you can measure improvements in your team’s incident response capabilities. Track metrics like Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR) for simulated incidents. As your team becomes more familiar with the attack patterns, you should see these times decrease significantly. BAS helps you understand your true risk from sophisticated attacks and check if your detection and response systems are good enough. This ensures your security staff are ready to protect important company information when a real attack happens.
While risk reduction is the primary goal, you also need to demonstrate financial value. A cost-benefit analysis helps you frame the investment in terms your CFO will appreciate. The “cost” includes the platform’s subscription fee and any time your team spends managing it. The “benefit” is where it gets interesting. Calculate the potential cost of a breach that your BAS tool helped you prevent. Factor in the time and resources saved by automating security testing that was previously done manually. Over time, a stronger security posture can even lead to lower cyber insurance premiums. By collecting and analyzing this data, you can clearly communicate the results and prove the tool’s positive financial impact on the organization.
Meeting compliance requirements can be a constant headache, but a BAS tool can make the process much smoother. Many regulations and frameworks, like PCI DSS, HIPAA, and NIST, require regular security control validation and testing. Instead of scrambling to gather evidence before an audit, a BAS platform provides a continuous, automated record of your testing activities. It generates reports that clearly demonstrate due diligence and show that your controls are working as expected. BAS provides proof of ongoing security testing, which helps with compliance and audits. This not only saves your team countless hours but also gives you confidence when the auditors arrive, turning a stressful event into a routine check-in.
Choosing a Breach and Attack Simulation (BAS) tool is a significant investment, and you want to be sure it’s the right fit for your environment. Most vendors understand this and offer ways to test their platforms before you commit. Taking advantage of these trials is the smartest way to see firsthand how a tool performs against your specific security controls and infrastructure. It’s your chance to move past the sales pitch and see real results, ensuring the platform can deliver on its promises to strengthen your security posture.
Most BAS vendors offer free trials or paid proof-of-concept (PoC) programs to let you test drive their software. These trials are your opportunity to see how different security validation technologies work within your unique environment. A trial allows your team to run simulated attacks and see exactly which security controls pass, fail, or miss the threat entirely.
This hands-on experience is invaluable. It helps you assess the tool’s user interface, the quality of its reporting, and how easily it integrates with your existing systems. Think of it as a trial run for your security team, giving them a feel for the day-to-day reality of using the platform to find and fix security gaps before you sign a long-term contract.
To get the most out of a trial, go in with a clear plan. Start by identifying your main security concerns. Are you worried about ransomware, phishing attacks, or lateral movement within your network? Choose a BAS tool that can simulate a wide range of these real-world threats across all your security layers, from your network and endpoints to email and web applications.
During the trial, focus on how the tool integrates with your security stack. A good BAS platform should not only find weaknesses but also provide clear, actionable guidance to help your team fix them. The goal is to measure your actual readiness to prevent and detect threats, rather than just guessing. Use the trial period to confirm the tool helps you do just that.
How is a Breach and Attack Simulation (BAS) tool different from the penetration tests we already run? Think of it this way: a penetration test is like an annual inspection, providing a deep, point-in-time snapshot of your security. A BAS tool, on the other hand, is like a 24/7 security camera system that is constantly testing your defenses. It runs automated, continuous simulations to give you ongoing feedback on your security posture. The two are complementary. A pen test offers creative, human-driven analysis, while BAS provides the consistent, automated validation you need to ensure your controls are working correctly day in and day out.
My security team is already dealing with alert fatigue. Won’t a BAS tool just make that worse? That’s a completely valid concern. A poorly configured tool can definitely add to the noise. However, a good BAS platform is designed to test your entire security response, not just trigger alerts. The key is proper implementation and tuning. You can configure the system to differentiate between simulated and real threats, which helps refine your detection rules. Over time, this actually reduces fatigue by making your real alerts more accurate and actionable, because you’ve already weeded out the false positives through simulation.
We already use a vulnerability scanner, so why would we need BAS? A vulnerability scanner is great at creating an inventory of potential weaknesses, like telling you which doors and windows in your house are unlocked. A BAS tool takes the next step; it actually tries to open those doors and windows to see if they lead to anything valuable. It provides the critical context of exploitability. By simulating attack paths, it shows you which vulnerabilities can be chained together to create a real threat, helping you prioritize fixing the issues that pose an immediate danger instead of just working through a long list of theoretical risks.
How do I choose the right BAS tool for my team? Instead of just comparing feature lists, focus on how a tool will fit into your team’s existing workflow. Look for a platform that uses real-time threat intelligence to ensure its simulations are relevant to the attacks you’re most likely to face. It should also provide clear, step-by-step remediation guidance, not just a list of problems. Consider whether a standalone tool or one integrated into a broader threat exposure management platform makes more sense. An integrated solution can often streamline the process from discovery to remediation more effectively.
What’s the best way to demonstrate the value of a BAS tool to my leadership? Focus on communicating risk reduction in clear, measurable terms. You can show a downward trend in the number of successful simulated attacks over time, proving your security controls are improving. Track metrics like how much faster your team can detect and respond to these simulated incidents. You can also highlight the time and resources saved by automating security testing and streamlining compliance audits. When you frame the conversation around concrete data that shows a stronger, more efficient security posture, the value becomes undeniable.