Comprehensive Threat Exposure Management Platform
You wouldn’t wait for a real fire to find out if your smoke detectors work or if your team knows the evacuation route. You run fire drills. So why would you wait for a real cyberattack to test your security defenses? This is the simple, powerful idea behind security controls validation. It’s the essential, ongoing fire drill for your entire security program. By safely and automatically simulating the exact tactics, techniques, and procedures used by real attackers, you can see how your tools, processes, and people hold up under pressure. It’s about proactively finding and fixing your weaknesses before an adversary can exploit them.
Think of Security Controls Validation (SCV) as a continuous fitness test for your security stack. You’ve invested heavily in firewalls, endpoint detection, email filters, and other tools, but how do you know they’re configured correctly and actually stopping threats? SCV is the process that answers that critical question. It uses automated tests to safely simulate real-world attack techniques, giving you a clear, ongoing picture of how well your defenses hold up against the methods attackers are using right now.
Instead of just assuming your security tools are working because the dashboard is green, validation puts them to the test in a controlled environment. It moves beyond basic configuration checks to see if your controls can actually block the specific tactics, techniques, and procedures (TTPs) that define modern cyberattacks. This approach provides constant, real-world evidence of your security effectiveness, not just a theoretical assessment. With a solid Adversarial Exposure Validation strategy, you can find and fix the gaps in your defenses before an actual attacker finds them for you. It’s about making sure your security investments are delivering the protection you paid for and transforming your security posture from reactive to proactive.
For years, security testing relied on point-in-time assessments like penetration tests and vulnerability scans. While valuable, these methods are like taking a single snapshot of your security posture. They tell you how things looked on a specific day, but they don’t provide a continuous view. Security Controls Validation is different. It’s an ongoing, automated process that reflects the dynamic nature of both your environment and the threat landscape.
This evolution is a shift from theory to practice. Traditional testing often focuses on identifying potential weaknesses or misconfigurations. SCV goes a step further by actively simulating attacks to see how your controls perform under pressure. It’s the difference between reading the user manual for a fire extinguisher and actually pulling the pin to see if it works.
An effective validation program isn’t just about running random tests. It’s a structured approach built on several core components that work together. First is continuous monitoring, which ensures your controls are being tested around the clock, not just once a quarter. Next is threat emulation, where you run safe, controlled simulations of real attacker behaviors against your systems to see what gets through.
Other key pieces include attack surface analysis to understand your potential entry points and incident response validation to ensure your team can react effectively when a threat is detected. When these components are integrated into a unified platform, like the Uni5 Xposure Platform, they provide a complete and actionable view of your security effectiveness, helping you prioritize fixes and prove your defenses are ready for real-world threats.
You’ve invested heavily in a security stack designed to protect your organization. You have firewalls, endpoint detection and response (EDR) tools, security information and event management (SIEM) systems, and more. On paper, your defenses look solid. But here’s the tough question: how do you know they’re actually working? Assuming your security controls are effective simply because they’re deployed is a risky strategy. Misconfigurations, software updates, and evolving attacker techniques can create gaps in your defenses that you won’t find until it’s too late.
This is where security controls validation comes in. It’s the process of continuously and safely testing your security tools and processes against real-world attack scenarios to see how they hold up. Think of it as a fire drill for your entire security program. Instead of waiting for a real incident to discover a weakness, you proactively find and fix issues before an attacker can exploit them. This shifts your security posture from reactive to proactive, providing concrete evidence of your security effectiveness. It helps you ensure your investments are paying off, stay ahead of sophisticated threats, and simplify the complex world of compliance.
Let’s be honest: security tools are expensive. You spend a significant portion of your budget on technology meant to keep the business safe, and leadership wants to see a return on that investment. Security controls validation provides the proof you need. By simulating real attacks, you can objectively measure whether your tools are detecting, preventing, and alerting as expected. This process reveals your organization’s true security effectiveness and the real-world impact of your investments.
This isn’t just about finding flaws; it’s about optimization. Maybe your EDR is configured too loosely, or a firewall rule is creating an unforeseen blind spot. Validation helps you fine-tune your stack to get the maximum value out of every tool. With Hive Pro’s approach to Adversarial Exposure Validation, you can move beyond assumptions and generate hard data that demonstrates the effectiveness of your security program to stakeholders.
Attackers don’t stand still. Their tactics, techniques, and procedures (TTPs) are constantly evolving to bypass traditional defenses. A security control that worked yesterday might be ineffective against a new threat tomorrow. Point-in-time assessments like annual penetration tests can’t keep up with this rapid pace of change. You need a continuous approach to stay ahead.
By regularly testing your controls against the latest threats, you can adapt your defenses in near real-time. This continuous validation process has been shown to make security operations teams significantly more efficient while reducing potential risks. Instead of reacting to the latest breach headline, you can proactively test your resilience against the very techniques being used in the wild. The threat intelligence from research teams like HiveForce Labs can feed directly into your validation strategy, ensuring you’re always testing against the most relevant and current threats.
Meeting compliance requirements for frameworks like PCI DSS, HIPAA, or ISO 27001 can be a major headache. Auditors don’t just want to see that you have security controls in place; they want proof that those controls are effective. Security controls validation delivers that proof on a silver platter. It provides clear, repeatable evidence that your security infrastructure can detect and respond to threats as required by various regulations.
This turns compliance from a frantic, manual, checkbox-ticking exercise into a natural byproduct of a strong security program. By continuously validating your controls, you always have up-to-date documentation on your security posture. This not only makes audits smoother but also gives you a much clearer picture of your overall cyber risk. Platforms that provide a unified view of cyber risks make it easier to connect your validation results directly to your risk management and compliance efforts, giving you confidence in your ability to protect sensitive data.
If you’ve been in security for a while, you’re familiar with traditional assessments like penetration testing and vulnerability scans. While these methods are still valuable, they represent a point-in-time snapshot of your security posture. Security Controls Validation (SCV) is different. It’s not about a once-a-year check-up; it’s about continuous, automated testing that shows you how your defenses perform against real-world attack scenarios, day in and day out.
Think of it this way: a traditional pen test is like an annual physical. It gives you a great baseline, but it doesn’t tell you what your blood pressure is during a stressful meeting. SCV is the fitness tracker that monitors your vitals 24/7, giving you a live, dynamic view of your security health. This shift from periodic snapshots to continuous validation helps you understand if your security tools are not just present, but actually effective.
Traditional security assessments, like annual penetration tests or compliance audits, provide a valuable but limited view. They capture your security posture at a single moment, which can become outdated the minute a new threat emerges or a configuration changes. Security Controls Validation, on the other hand, offers a continuous security assessment approach. It constantly evaluates your prevention and detection tools against the latest threats. This means you get a current, accurate picture of how well your controls are working, allowing you to identify and fix gaps before an attacker can exploit them, rather than waiting for your next scheduled test.
Penetration testing relies on the incredible skill of ethical hackers to manually find and exploit vulnerabilities. It’s deep, but it can be time-consuming and expensive. SCV complements this by using automated tests that emulate the tactics, techniques, and procedures (TTPs) of real attackers. These simulations run constantly, testing your defenses against a wide range of threats without the manual effort. This automated approach makes it possible to test at scale and with a frequency that manual testing just can’t match, giving your team a powerful tool for adversarial exposure validation on an ongoing basis.
Many traditional audits focus on compliance—making sure the right boxes are checked and the right configurations are in place. But a correctly configured firewall doesn’t guarantee it will block a sophisticated attack. SCV moves beyond basic configuration checks by simulating real-world cyber-attacks to see how your security stack actually performs under pressure. It answers the critical question: “Will this tool stop this specific threat?” By focusing on performance against realistic attack scenarios, you can prove the true effectiveness of your security investments and move from a compliance-driven mindset to a threat-informed defense.
If traditional validation methods are like a scheduled fire drill, Breach and Attack Simulation (BAS) is like having a system that safely tests your smoke detectors and sprinkler systems around the clock. Instead of relying on periodic, manual tests, BAS platforms continuously and automatically launch simulated cyberattacks against your live environment. These aren’t real attacks, of course—they’re safe emulations of the exact tactics, techniques, and procedures (TTPs) that threat actors use.
This approach gives you a real-time, evidence-based understanding of how your security controls hold up against specific threats. Think of it as a constant, friendly sparring partner for your defenses. It helps you move beyond assumptions and answer critical questions with certainty: Is that new EDR solution configured correctly? Can our firewall actually block this specific ransomware strain? By providing a platform for adversarial exposure validation, BAS transforms your validation process from a periodic check-up into a continuous, proactive program. It allows you to find and fix gaps before they can be exploited, shifting your security posture from reactive to resilient. This continuous feedback loop is essential for keeping pace with a threat landscape that changes daily, ensuring your defenses are always tuned to counter the most relevant and current attack methods.
Let’s be honest, manual testing can’t keep up. Your environment is constantly changing, with new applications, users, and devices coming online daily. Trying to manually test every potential attack path is an impossible task. This is where BAS completely changes the game. It automates the process by running thousands of attack simulations across your network, endpoints, and cloud environments.
This continuous, automated testing allows you to implement proactive validation without draining your team’s time and resources. Instead of waiting for an annual pen test to find a critical misconfiguration, BAS tools can spot it right away. This means you’re constantly aware of your true security posture and can identify and close defensive gaps as soon as they appear.
The best security outcomes happen when your offensive (red) and defensive (blue) teams work together—a practice known as purple teaming. BAS acts as the perfect collaboration platform to make these exercises more effective. It provides a shared, data-driven view of security performance that both teams can use.
The red team can use BAS to launch specific, controlled attack scenarios, while the blue team can monitor their tools to see what gets detected and what is missed. This creates a tight feedback loop. Instead of a red team report that lands on someone’s desk weeks later, this process of security control validation helps fine-tune detection rules, improve response playbooks, and train analysts on real-world threat behaviors.
Are your security tools actually earning their keep? With BAS, you don’t have to guess. It provides concrete metrics on the performance of each control in your security stack. After running a simulation, the platform gives you a clear report card showing which attacks were prevented, which were detected, and which slipped through completely.
This data is incredibly powerful. It allows you to move from a compliance-based mindset (“Is the firewall turned on?”) to an effectiveness-based one (“Is the firewall blocking the latest TTPs used by this threat group?”). In fact, one study found that continuous validation led to a 44 percent reduction in potential risks and made security teams more efficient. This empirical evidence helps you justify security spending and focus investments where they’ll have the greatest impact.
Traditional penetration tests are valuable, but they are also expensive, time-consuming, and only provide a snapshot of your defenses at a single point in time. Your environment changes the day after the pen testers leave, and that report becomes outdated. BAS offers a more sustainable and scalable alternative.
Because the attack simulations are automated, you can run them continuously across your entire organization for a fraction of the cost of repeated manual assessments. This allows you to validate your controls as often as you need to—after a major software update, a network change, or when new threat intelligence emerges. A security controls validation assessment powered by BAS gives you an ongoing, comprehensive view of your security effectiveness, ensuring your defenses remain strong day in and day out.
Validating your security controls without threat intelligence is like trying to navigate a new city without a map. You might eventually find your way, but you’ll likely take a lot of wrong turns. Threat intelligence provides that map, giving you the context needed to focus your validation efforts where they matter most. Instead of testing against a generic list of potential attacks, you can simulate the exact threats that are actively targeting organizations like yours.
This intelligence-driven approach transforms your validation from a simple check-the-box exercise into a strategic defense-building activity. You’re no longer just asking, “Do my controls work?” Instead, you’re asking, “Do my controls work against the specific ransomware strain targeting my industry?” or “Can we detect the TTPs used by a threat group known for attacking financial services?” By integrating real-world data from sources like our own HiveForce Labs, you can prioritize your testing, find your most critical gaps, and make smarter decisions about where to invest your time and resources. It’s about shifting from a reactive stance to a proactive one, using attacker insights to strengthen your defenses before an incident occurs.
The most effective way to test your defenses is to pit them against the same threats they’ll face in the real world. Threat intelligence gives you a direct line of sight into what attackers are doing right now—which vulnerabilities they’re exploiting, what malware they’re deploying, and which phishing tactics are getting clicks. By using this information, you can simulate real-world cyber-attacks to see if your security stack can actually handle them. This means your validation program isn’t just based on theoretical risks; it’s a practical test against current and credible threats. This approach ensures your security tools are configured to stop today’s attacks, not just the ones from last year.
Knowing what to test for is only half the battle; you also need to know how attackers operate. Threat intelligence provides deep insights into the tactics, techniques, and procedures (TTPs) that adversaries use to move through a network, escalate privileges, and exfiltrate data. An effective validation strategy uses this information to emulate attacker behavior step-by-step. By running proactive validation tests that mimic these TTPs, you can see exactly where your defenses hold up and where they fall short. This gives you a much clearer picture of your security posture from an attacker’s perspective, allowing you to close gaps you might have otherwise missed.
No security team has unlimited resources. Threat intelligence is essential for making sure your time, budget, and effort are spent on the risks that pose the greatest danger to your organization. Instead of trying to validate every control against every conceivable threat, you can use intelligence to prioritize. By understanding which threats are most likely to target your industry and which vulnerabilities are most critical, you can focus your validation efforts accordingly. This data-driven approach helps you make informed decisions, ensuring your team is working on the most impactful tasks and that your security investments are directed at your most significant exposures.
Ultimately, integrating threat intelligence into your validation strategy is about building a proactive defense. It allows you to get ahead of attackers by testing your controls against emerging threats before they become widespread. This continuous, intelligence-led cycle of testing and hardening creates a more resilient security posture. In fact, studies show that continuous security control validation can lead to significantly more efficient security operations and a reduction in potential risks. By consistently validating your defenses against the latest threats, you move beyond reactive incident response and build a program that can confidently anticipate and neutralize attacks.
An effective validation program is much more than a one-time audit or an annual penetration test. It’s a living, breathing part of your security operations that provides a constant feedback loop on your defensive capabilities. Think of it as a continuous fitness test for your security posture. It’s built on a foundation of ongoing assessment, a deep understanding of your attack surface, practical drills for your response teams, and strong collaboration across the entire organization. When these elements work together, you move from hoping your controls work to knowing they do.
Your security environment is always changing—new assets come online, configurations drift, and threat actors develop new techniques. That’s why a “set it and forget it” approach to validation just doesn’t work. An effective program involves continuously testing your security measures to ensure they are performing as expected against the latest threats. This isn’t just about finding gaps; it’s about improving efficiency. Studies show that continuous security control validation can lead to a 47% increase in security operations efficiency and a 44% reduction in potential risks. By making validation an ongoing process, you can maintain a clear, real-time picture of your security effectiveness with a unified view of cyber risks.
You can’t effectively validate controls if you don’t have a complete picture of what you’re trying to protect. A strong validation program begins with a thorough analysis of your entire attack surface, from on-premise servers to cloud assets and user endpoints. This means identifying all potential entry points an attacker could use. Once you have this map, you can simulate real-world cyberattacks to test whether your controls—like email gateways and endpoint detection tools—are actually blocking threats. This approach helps you systematically check your defenses across every part of your total attack surface, ensuring there are no blind spots for an adversary to exploit.
Security controls aren’t just about technology; they also include your people and processes. An effective validation program tests your incident response (IR) plan with realistic attack simulations. This goes far beyond basic configuration checks by showing you how your team performs under pressure. Can they detect the threat? Do they follow the right procedures to contain it? These simulated drills are the best way to find weaknesses in your IR plan before a real incident occurs. By practicing your response, you can refine your playbooks, train your team, and significantly reduce the impact of an actual breach through adversarial exposure validation.
Security is a team sport. A successful validation program breaks down silos between security, IT, and DevOps teams by providing a common language to discuss risk. The data and insights generated from validation assessments show everyone the real-world impact of security gaps and the value of your security investments. When teams have a shared understanding of the organization’s security effectiveness, they can work together more effectively to prioritize remediation efforts. This collaborative approach ensures that everyone is aligned on protecting the business, turning security from a siloed function into a shared responsibility.
Putting a security controls validation program in place is one of the smartest moves you can make for your security posture. But let’s be real—it’s not always a simple plug-and-play process. Many teams run into a few common roadblocks on the way to continuous validation. Knowing what these hurdles are ahead of time can help you plan a smoother, more effective implementation. From tangled tech stacks to tight budgets, these challenges are manageable with the right strategy and tools. The key is to move past simply checking if your defenses are configured correctly and start testing if they are truly effective against real-world threats.
Today’s IT environments are a mix of on-premise servers, multi-cloud deployments, IoT devices, and a remote workforce. This complexity makes it incredibly difficult to even map out your full attack surface, let alone validate the controls protecting it. When your assets are scattered everywhere, how can you be sure your security measures are working as they should to protect your data? A foundational step is to gain complete visibility. Without a clear and continuous picture of your entire digital footprint, any validation effort will have blind spots. This is where a strong attack surface management practice becomes non-negotiable, providing the comprehensive view needed to test controls effectively across your whole environment.
Let’s face it: security teams are almost always asked to do more with less. Implementing a thorough validation program requires time, budget, and specialized expertise—three things that are often in short supply. As one expert puts it, “It takes enough money, people, and knowledge to do a full check.” The persistent cybersecurity skills gap means that finding professionals with experience in adversarial simulation or purple teaming can be tough. This is where automation becomes a game-changer. Breach and Attack Simulation (BAS) tools can run thousands of tests automatically, giving smaller teams the power to validate their defenses continuously without needing a dedicated staff of penetration testers.
Your security infrastructure is likely a collection of tools from different vendors, including firewalls, EDR, SIEMs, and more. Getting these disparate systems to work in concert is a challenge in itself. An effective validation program must be able to test this entire ecosystem, not just individual tools in isolation. The goal is to see if your security stack can collectively detect and respond to a simulated attack as it unfolds. A validation platform that doesn’t integrate smoothly with your existing tools will only create more work and deliver an incomplete picture of your true security posture. Your program needs to test how your systems and teams actually perform when faced with a realistic threat.
Security controls validation isn’t just a task for the security team; it requires collaboration and support from across the business. You’ll need buy-in from IT, DevOps, and especially from executive leadership who approve the budgets. The best way to get this support is to frame the conversation around business risk, not just technical vulnerabilities. A validation assessment clearly “reveals your organization’s security effectiveness, associated risks, and impacts of threats.” By demonstrating how validation proves the value of your security investments and protects the business from tangible threats, you can turn it from a technical line item into a strategic business priority that everyone can get behind.
Running a security controls validation program without measuring its success is like driving without a destination. You’re moving, but you have no idea if you’re making progress. To get real value from your efforts, you need to prove that your program is actually reducing risk and strengthening your defenses. This isn’t just about generating reports; it’s about creating a feedback loop that drives continuous improvement and demonstrates the value of your security investments to the rest of the organization.
Measuring success helps you answer critical questions: Are our security tools configured correctly? Is our team responding effectively to threats? Are we spending our budget on the right things? By tracking the right metrics, you can move from simply testing controls to strategically managing your security posture. It’s how you turn data into decisions and transform your security program from a reactive cost center into a proactive, data-driven function that protects the business.
You can’t improve what you don’t measure. Before you even start testing, you need to decide what success looks like for your organization. This is where Key Performance Indicators (KPIs) come in. These aren’t just vanity metrics; they are specific, measurable data points that show how well your security controls are performing against your goals. Defining your KPIs is the first step in understanding the real-world effectiveness of your security program.
A Security Controls Validation Assessment can reveal your organization’s security effectiveness and the associated risks, which helps you set meaningful targets. Good KPIs might include Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR) for simulated attacks, the percentage of threats blocked by a specific control, or the reduction in successful attack simulations over a quarter. The key is to choose metrics that directly reflect your ability to defend against threats, not just the number of tests you run.
Cybersecurity isn’t a one-and-done activity. Your environment is constantly changing, and so are the threats you face. That’s why tracking the effectiveness of your controls over time is so important. A control that worked perfectly last month might fail tomorrow due to a simple configuration drift or a new attacker technique. Continuous validation provides the ongoing visibility you need to catch these issues before they become real problems.
The data shows that this approach works. One study found that continuous security control validation led to a 47% increase in security operations efficiency and a 44% reduction in potential risks. By trending your KPI data, you can spot degrading performance, identify recurring misconfigurations, and confirm that remediation efforts are actually working. This historical view gives you the context to make smarter, more informed decisions about your security strategy.
Technology is only part of the solution. An effective validation program also depends on clear processes and people who know their roles. Security control validation is ultimately about testing whether your tools and your teams can detect and respond to real-world threats. If a test fails, who is responsible for fixing it? How is the remediation process tracked? Without clear answers, your findings will just sit in a report.
This is why establishing clear documentation and accountability is non-negotiable. Document your testing procedures, the expected outcomes, and the step-by-step process for remediation. Assign clear ownership for each security control and for every step in the response plan. When everyone understands their responsibilities, you create a culture of accountability where issues get fixed quickly and your security posture steadily improves.
Security teams are constantly asked to justify their budgets. Demonstrating your Return on Security Investment (ROSI) is how you prove that your program is worth the cost. Security controls validation provides the hard data you need to connect your team’s efforts to tangible business value. Instead of just saying you need a new tool, you can show precisely which security gaps it will fill and how it will perform against specific, simulated threats.
This evidence-based approach helps your organization decide wisely where to spend money and effort on cybersecurity. For example, you can show that a specific control blocked 95% of simulated ransomware attacks, helping to avert millions in potential losses. By translating technical results into financial terms, you can have more productive conversations with leadership and secure the resources you need. This turns security controls validation from a technical exercise into a powerful business enablement tool.
Putting a security controls validation program into practice doesn’t have to be a massive undertaking. The key is to approach it methodically, focusing on creating a sustainable process rather than a one-time project. By establishing clear goals, fostering teamwork, and using the right technology, you can build a program that delivers continuous insight into your security posture. These best practices will help you lay a solid foundation for a validation strategy that strengthens your defenses and demonstrates real security value.
Effective security controls validation is a team sport. It’s not just about whether a firewall blocks a connection; it’s about whether your entire security ecosystem—people, processes, and technology—works together to stop an attack. Simulating real-world threats tests how your SOC, MDR, and NDR teams actually perform under pressure. To make this work, you need to break down silos. Get your security, IT operations, and even development teams in the same room (virtual or otherwise). When everyone understands the goals and sees the results, you can identify and fix gaps in your response chain, not just in your tech stack. This collaborative approach turns validation from a simple check into a powerful training and improvement exercise.
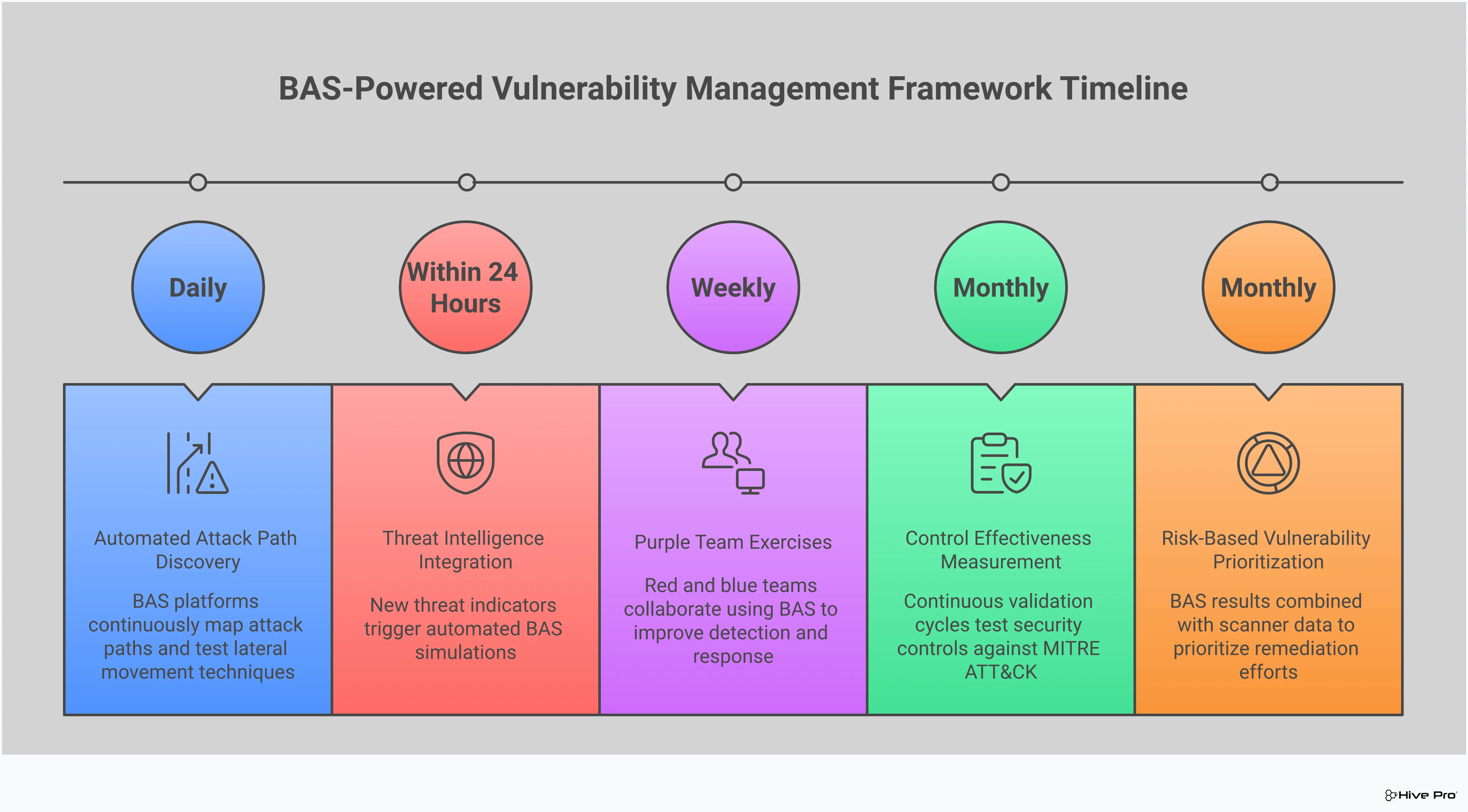
You can’t test everything all the time, so it’s important to be strategic. Start by defining a clear scope for your validation efforts. What are your most critical assets? Which attack scenarios pose the greatest risk to your business? Use this information to prioritize your testing. A good approach is to align your validation activities with your vulnerability and threat prioritization efforts. From there, establish a regular testing cadence. This might involve daily automated checks on core controls, weekly simulations of common threats, and quarterly deep dives that mimic advanced persistent threats (APTs). The goal is to make validation a continuous, predictable part of your security operations, providing a constant pulse on your security effectiveness.
Manual testing simply can’t keep up with the pace of modern threats. The right technology is essential for implementing a scalable and effective validation program. Breach and Attack Simulation (BAS) platforms are a game-changer here, allowing you to safely and automatically run thousands of attack simulations against your live environment. When choosing a tool, look for one that offers a comprehensive library of up-to-date threats and techniques. It should also provide clear, actionable reporting that helps you pinpoint weaknesses and guide remediation. A platform that offers adversarial exposure validation can help you test your defenses against real-world scenarios and ensure your security controls are configured correctly and performing as expected.
The ultimate goal is to embed security controls validation into the DNA of your security program. This means creating a sustainable framework that goes beyond ad-hoc testing. Think of it as a continuous cycle: test your controls, analyze the results, remediate the gaps, and then test again. Document your processes, define roles and responsibilities, and establish clear metrics for success. This framework ensures that validation becomes a repeatable, measurable, and constantly improving process. By treating validation as an ongoing program, you can move from a reactive security posture to one that is proactive and adaptive, continuously refining your defenses based on empirical data about what truly works.
How is security controls validation different from a regular penetration test? Think of it like this: a penetration test is like an annual, in-depth physical exam. It’s incredibly valuable for finding deep-seated issues at a specific moment in time. Security controls validation, on the other hand, is like a fitness tracker you wear every day. It provides a continuous, real-time pulse on your security health, constantly checking if your defenses are performing as expected against a wide range of common and emerging threats. Both are important, but validation gives you that day-in, day-out assurance that a point-in-time test can’t.
Is Breach and Attack Simulation (BAS) the same as security controls validation? That’s a great question because the terms are often used together. The simplest way to think about it is that security controls validation is the goal—the ongoing process of proving your defenses work. Breach and Attack Simulation (BAS) is the modern, automated technology you use to achieve that goal. A BAS platform is the engine that runs thousands of safe, simulated attacks to continuously test your controls, giving you the data you need for your validation program.
My security tools are all configured correctly. Why do I still need to validate them? A correct configuration is a great starting point, but it doesn’t guarantee real-world effectiveness. Your environment is dynamic; a software update, a change in a firewall rule, or a new application can create unforeseen gaps. Validation moves beyond checking if a tool is set up correctly and asks a more important question: “Does it actually stop an attack?” It tests performance under pressure, ensuring your defenses work in practice, not just on paper.
We’re a small team with a tight budget. How can we get started with validation? This is a common concern, and the good news is you don’t need a massive team to start. The key is to lean on automation. Using a Breach and Attack Simulation (BAS) tool can act as a force multiplier, allowing a small team to run thousands of tests that would be impossible to perform manually. Start by focusing on your most critical assets and the most common threats to your industry. This targeted approach helps you make the biggest impact with the resources you have.
How does this help beyond just finding technical gaps in our tools? While it’s excellent at finding technical weaknesses, one of the biggest benefits of a validation program is testing your people and processes. By simulating a real attack, you can see how your security team actually responds. Do they get the alert? Do they follow the incident response plan correctly? It’s a safe way to run a fire drill for your entire security operation, helping you refine playbooks, improve team collaboration, and ensure everyone is ready before a real incident happens.