Comprehensive Threat Exposure Management Platform
Attackers don’t see your organization as a list of CVEs. They see a web of interconnected systems, looking for the path of least resistance to their target. They find one small weakness, then another, and chain them together to create a breach. So why would we defend our networks any differently? An effective exposure management strategy is about adopting this attacker’s mindset. It’s a continuous process of discovering your full attack surface, identifying the “toxic combinations” of exposures that create real risk, and validating that your defenses can actually stop a real-world attack. It’s time to stop thinking in isolated vulnerabilities and start seeing the bigger picture.
Let’s get straight to it. Exposure management is the process of continuously identifying, assessing, and reducing cybersecurity risks across your organization’s entire digital attack surface. Think of it as a security strategy that looks at the big picture. Instead of just patching individual vulnerabilities as they pop up, it helps you understand how different weaknesses could connect and create a pathway for an attacker. The main goal is to find and fix these security gaps before they can be exploited, effectively lowering the chance of a breach.
This approach covers every digital asset you own, from on-premise servers and cloud infrastructure to web applications and employee laptops. It’s about seeing your organization from an attacker’s perspective to understand which exposures are most likely to be targeted. By adopting this mindset, you can shift your security program from a constant state of reaction to a more confident, proactive stance. A unified threat exposure management platform brings all these moving parts together, giving you a single, clear view of your security posture and guiding you toward the most impactful actions.
For too long, security teams have been caught in a reactive cycle, drowning in an endless sea of vulnerability alerts. Exposure management offers a way out. It fundamentally changes the question from “Is this a critical vulnerability?” to “Could an attacker actually use this exposure to harm our business?” This shift is crucial because it focuses on real-world risk and business impact.
Instead of treating every vulnerability in isolation, this approach looks for “toxic combinations”—seemingly minor issues that, when chained together, create a clear and dangerous attack path. It’s about moving beyond the CVE score and understanding the context of each weakness within your specific environment. This allows for a much smarter way to prioritize threats, ensuring your team spends its valuable time fixing the problems that truly matter.
An effective exposure management program is built on a few core principles that work together in a continuous cycle. First is comprehensive discovery. You can’t protect what you don’t know you have, so the process starts with continuously mapping your entire attack surface to maintain a complete asset inventory.
Next is risk-based prioritization, which uses real-time threat intelligence to pinpoint which exposures pose the most immediate danger to your organization. After that comes validation, where you actively test your security controls through simulations to confirm they work as expected. Finally, there’s effective remediation—mobilizing the right teams to fix the most critical issues quickly. Together, these principles create a framework for systematically reducing your exposure over time.
If you’ve spent years in vulnerability management, you might see exposure management as just another buzzword. But it represents a fundamental shift in how we approach cybersecurity. Think of it as an evolution. Traditional vulnerability management programs have us chasing an endless list of CVEs, often without a clear sense of which ones pose a genuine threat to the business. It’s a reactive cycle of scanning and patching that can leave security teams feeling like they’re always one step behind.
Exposure management changes the game by moving from a narrow, vulnerability-focused view to a holistic perspective of your entire attack surface. It connects the dots between individual weaknesses to show you the actual paths an attacker could take to reach your most critical assets. It’s about understanding context, prioritizing what truly matters, and proactively closing the doors on attackers before they can even get a foot in. Let’s break down the key differences.
Traditional vulnerability management is focused on finding and fixing known vulnerabilities in your software and hardware. The process is straightforward: you run a scan, get a list of CVEs, and your team starts working through them. While essential, this approach is like checking every window and door of a fortress but ignoring the unsecured secret tunnels underneath. It misses a huge part of the picture.
Exposure management broadens the scope to cover every potential point of attack. It looks at your total attack surface, which includes not just software flaws but also cloud misconfigurations, weak or exposed credentials, insecure APIs, and even risky user permissions. It treats your entire IT ecosystem—from on-prem servers to cloud assets and employee devices—as one interconnected environment. This wider view helps you see how an attacker could chain together seemingly low-risk issues to create a critical threat.
One of the biggest challenges in vulnerability management is prioritization. Relying on CVSS scores alone often leads to alert fatigue, as teams scramble to patch “critical” vulnerabilities that may not be exploitable in their specific environment. A high-severity vulnerability on an isolated, internal server is far less urgent than a medium-severity one on a public-facing system that protects customer data.
Exposure management brings business context into the equation. Instead of just asking, “How severe is this vulnerability?” it asks, “What is the actual risk to our business?” It helps you prioritize threats by considering factors like asset criticality, real-world exploitability, and the presence of compensating controls. This approach helps you identify “toxic combinations”—multiple exposures that, when linked, create a direct path to your most valuable assets—so you can focus your resources where they’ll have the greatest impact.
In a traditional vulnerability management world, remediation usually means one thing: patching. While patching is crucial, it’s not the only way to reduce risk. Sometimes a patch isn’t available, or deploying it would cause significant business disruption. This is where the limitations of a patch-centric approach become clear.
Exposure management offers a more flexible and strategic approach to remediation. The goal is to break the attack path. This might involve applying a patch, but it could also mean changing a system configuration, strengthening access controls, or segmenting a network to isolate a vulnerable asset. By providing a complete view of your exposures, a platform like Uni5 Xposure gives you multiple options for remediation. This allows you to take decisive, proactive steps to reduce risk, even when a patch isn’t the immediate answer.
An effective exposure management program isn’t just a single tool or a one-off project; it’s a continuous cycle built on a few core pillars. Think of it as a strategic framework that moves your security posture from reactive to proactive. When you put these components together, you create a system that not only finds weaknesses but also helps you understand which ones truly put your organization at risk and validates that your fixes are working. This approach helps you focus your resources where they’ll have the greatest impact, ensuring your team isn’t just busy, but effective. By adopting this holistic view, you can stop chasing down every single alert and start making strategic decisions that measurably reduce your overall risk. It’s about creating a resilient security program that can adapt to the constantly changing threat landscape.
You can’t protect what you don’t know you have. The first step in any solid exposure management program is getting a complete and continuous picture of your entire attack surface. This goes beyond your known servers and applications to include cloud assets, IoT devices, and even physical systems that could be exploited. An effective program helps you find and map all the potential entry points an attacker could use. By maintaining a complete inventory of your digital and physical assets, you can ensure there are no blind spots where a threat could hide, giving you the foundation needed to manage your total attack surface.
Finding a vulnerability is one thing; knowing if attackers are actively exploiting it is another. This is where threat intelligence comes in. Integrating real-world data gives you the context needed to understand the true risk a vulnerability poses. Instead of treating all CVEs as equal, you can see which ones are being used in active campaigns or are part of an attacker’s toolkit. This intelligence, often curated by research teams like HiveForce Labs, transforms your vulnerability list from a theoretical catalog of weaknesses into a practical, prioritized action plan focused on the threats that are most likely to impact you right now.
With thousands of potential vulnerabilities, you need a smart way to decide what to fix first. Effective exposure management moves beyond basic CVSS scores and helps you prioritize based on actual business risk. This means considering factors like how accessible a vulnerability is, what its potential impact on critical systems would be, and whether it’s relevant to real-world attack scenarios. A strong vulnerability and threat prioritization engine considers this rich context, allowing your team to focus its remediation efforts on the exposures that represent the greatest danger to your organization, ensuring your most critical assets are protected first.
Once you’ve identified and prioritized your exposures, how do you know your security controls will actually stop an attack? That’s the role of breach and attack simulation (BAS). By safely simulating real-world attack techniques, you can test your defenses and validate whether your remediation efforts were successful. This process helps you find gaps in your security posture before an actual attacker does. Adversarial exposure validation provides concrete proof that your security controls are working as expected, turning assumptions into certainty and helping you demonstrate measurable improvements in your security posture over time.
Think of threat intelligence as the missing link between knowing you have a vulnerability and understanding if it actually matters. Without it, your security team is stuck in a cycle of patching an endless list of CVEs, many of which pose little to no real danger to your organization. This is where a modern exposure management program changes the game. By integrating real-world threat data, you can finally see which vulnerabilities are just theoretical weaknesses and which ones are being actively targeted by attackers.
Effective exposure management isn’t about finding more vulnerabilities; it’s about finding the right ones to fix first. This requires a constant stream of high-fidelity intelligence that provides context about attacker tactics, techniques, and procedures. When you know what adversaries are doing right now, you can connect those actions directly to the exposures in your environment. This intelligence-led approach, powered by research teams like HiveForce Labs, transforms your security strategy from a reactive checklist to a proactive, attacker-informed defense. It allows you to focus your resources on the handful of issues that present a genuine risk to your business.
A vulnerability score on its own is just a number. To make smart decisions, you need context. By integrating threat intelligence, you can frame your vulnerabilities within the landscape of real-world threats, which leads to much more informed decision-making. Instead of just asking, “How severe is this CVE?” you can start asking better questions: “Are threat actors actively exploiting this? Is it part of a known attack chain? Does it affect our most critical assets?” This is how you move beyond generic scores and begin a true vulnerability and threat prioritization process. This context turns a long list of potential problems into a short, manageable list of immediate priorities.
Knowing which vulnerabilities are being actively exploited in the wild is a massive advantage. Threat intelligence allows you to track these trends and see which weaknesses are popular targets for ransomware gangs, state-sponsored actors, or other adversaries. A vulnerability with a “critical” CVSS score that no one is exploiting is far less urgent than a “medium” one that’s part of a widespread campaign. This focus on active exploits helps your team respond faster and more effectively, directing their efforts where they can have the greatest impact. Following timely threat advisories ensures you’re always aware of the exploits that demand your immediate attention, helping you stay ahead of attackers.
Ultimately, the goal is to focus your team’s limited time and resources on the most pressing threats. Drowning in alerts and low-priority vulnerabilities leads to burnout and leaves critical gaps open. Threat intelligence provides the necessary insights to cut through the noise, ensuring that your remediation efforts are allocated efficiently. It helps you pinpoint the exposures that represent the greatest business risk based on exploitability, potential impact, and relevance to current attack scenarios. By adopting a platform that unifies this intelligence, you can confidently address the threats that matter now and measurably reduce your organization’s overall risk.
Let’s be honest: after you’ve patched a vulnerability or configured a new security tool, there’s always a lingering question: Did it actually work? For years, security teams have had to rely on periodic penetration tests and a bit of hope to answer that. But hope isn’t a strategy. This is where Breach and Attack Simulation (BAS) changes the entire dynamic. Think of it as having a friendly, in-house red team that’s working for you 24/7, constantly and safely testing your defenses against the latest real-world attack techniques.
BAS platforms don’t just look for vulnerabilities in isolation. They simulate the full attack lifecycle, from initial access to data exfiltration, to see how your security stack holds up under pressure. It’s a continuous, automated process that moves you from assuming your defenses are working to knowing exactly where they stand. By running these controlled attack scenarios, you get concrete, evidence-based insights into your security posture. This allows you to perform Adversarial Exposure Validation on an ongoing basis, ensuring your tools, teams, and processes are ready for a real incident. It’s the difference between having a fire alarm and actually running a fire drill to see if everyone knows what to do.
You’ve invested heavily in firewalls, EDR, SIEMs, and other security tools. But are they configured correctly? Are they actually detecting and blocking the threats they’re supposed to? BAS gives you the definitive answer. By continuously running simulations that mimic the tactics, techniques, and procedures (TTPs) of known threat actors, BAS tests whether your security controls perform as expected. If a simulated attack gets through, you know there’s a gap—a misconfiguration, a policy that needs tuning, or a blind spot you didn’t know you had. This provides clear, actionable data to fine-tune your defenses and prove the value of your security investments to leadership.
Patching a vulnerability is only half the battle. The other half is confirming the fix was effective and didn’t inadvertently open another door. BAS closes the loop on your remediation workflow. After your team deploys a patch for a critical vulnerability, you can immediately run a specific attack simulation that targets it. If the attack is blocked, you have undeniable proof that your remediation was successful. This verification step transforms your vulnerability management from a checklist of deployed patches into a results-driven program focused on tangible risk reduction. It ensures you’re not just busy, but effective.
Attackers don’t think in terms of single vulnerabilities; they think in attack paths. They look for a series of small weaknesses they can chain together to achieve their objective. BAS adopts this same mindset. It continuously probes your environment to find these potential attack paths, identifying misconfigurations and security gaps that might seem minor on their own but become critical when combined. This proactive approach allows you to see your organization through an attacker’s eyes and find the holes before they do. By constantly assessing your defenses, you can prioritize the most critical weaknesses and strengthen your overall security posture against the threats that matter most.
Making the switch to a proactive exposure management strategy is a smart move, but it’s not always a straight path. Like any significant operational shift, it comes with a few common challenges. Anticipating these hurdles is the first step to clearing them, allowing you to build a program that’s both effective and sustainable. From wrangling your existing tech stack to getting teams on the same page, let’s walk through the main obstacles you might face and how to think about them.
Most security teams are already working with a suite of tools for things like application security, cloud security, and asset management. The problem isn’t a lack of data; it’s that the data lives in separate silos. Each tool provides a piece of the puzzle, but no one is putting it together to show you the full picture. A true exposure management program requires a unified view. Without it, you’re left trying to manually connect dots between different dashboards, which is inefficient and prone to error. The goal is to find a way to aggregate all this information into a single source of truth, giving you a complete and contextualized understanding of your total attack surface.
Technology alone can’t solve your exposure challenges. A successful program depends on having the right people with the right skills to manage it. This means dedicating team members who can analyze exposure data, prioritize risks based on business context, and drive remediation efforts. It also requires getting buy-in from leadership to secure the necessary budget and resources. This isn’t just about purchasing a new platform; it’s a strategic investment in a more resilient security posture. You need to ensure your team has the bandwidth and support to move beyond reactive fire-fighting and focus on proactive risk reduction.
Shifting from traditional vulnerability management to exposure management is as much a cultural change as it is a technical one. Teams are often accustomed to established workflows, like patching based on CVSS scores alone. Introducing a new, risk-based approach requires a change in mindset across security, IT, and even development teams. Getting everyone to collaborate and adopt new processes can be tough. The key is to clearly communicate the “why” behind the change. By demonstrating how a focus on validated threats and business impact reduces noise and allows everyone to focus on the risks that truly matter, you can build the cross-functional alignment needed for success.
Shifting to a proactive exposure management strategy feels good, but you need to prove it’s working. Tracking the right metrics shows the value of your efforts and helps you justify your program to leadership. It’s not just about counting patched vulnerabilities; it’s about demonstrating a measurable reduction in risk. Success in exposure management is measured by how quickly you can find and fix what matters most, how efficiently you close critical gaps, and whether your overall security posture is actually getting stronger over time. These key performance indicators (KPIs) move the conversation from activity to impact, showing exactly how your team is making the organization safer.
How long does it take your team to realize a security incident has occurred? That’s your Mean Time to Identify (MTTI). Once you know something is wrong, how long does it take to pinpoint the threat? That’s your Mean Time to Detect (MTTD). These are arguably the most important metrics in exposure management because they measure speed. The faster you can find a threat, the less time an attacker has to cause damage. A platform that continuously scans the attack surface is essential for driving these numbers down. By getting a constant, real-time view of your environment, you can spot anomalies and potential threats almost as soon as they appear, shrinking the window of opportunity for attackers.
This metric isn’t about how many patches you deploy; it’s about how successful you are at fixing the vulnerabilities that truly matter. Are you closing the gaps that attackers are actively exploiting? Patching effectiveness measures the success rate of your remediation efforts on prioritized threats. An effective exposure management program helps you focus on the vulnerabilities that pose a genuine risk to your business, based on real-world threat intelligence. This allows your team to direct its resources efficiently, ensuring that your patching efforts have the greatest possible impact on reducing your organization’s exposure. It’s the difference between being busy and being effective.
Ultimately, the goal of any security program is to reduce risk. Tracking your overall risk reduction provides a high-level view of your program’s success. By evaluating performance over time, you can see a clear trendline showing whether your organization’s exposure is decreasing. This metric is powerful because it translates technical activities into business-level outcomes. Instead of reporting on the number of tickets closed, you can show leadership a quantifiable improvement in the company’s security posture. A unified view of cyber risks in a single platform makes it much easier to monitor this trend and communicate your team’s value in clear, compelling terms.
Transitioning to an exposure management program is more than a technology upgrade; it’s a strategic shift in how your organization handles security. A successful rollout isn’t about flipping a switch overnight. It’s about building a solid foundation with clear workflows, getting the right people involved, and using technology to make everyone’s job easier. By focusing on a few key practices, you can make this transition feel less like a massive overhaul and more like a natural evolution of your security posture. The goal is to move from a state of constant reaction to one of proactive control, and a smooth rollout is the first step in making that a reality for your team. This means thinking critically about your current processes and identifying where you can introduce more continuous, collaborative, and automated approaches. It requires a plan that accounts for both the technical implementation and the cultural change needed to support it. When done thoughtfully, you establish a program that not only reduces risk but also makes your security operations more efficient and effective in the long run. Let’s walk through the practical steps you can take to get your exposure management program up and running effectively.
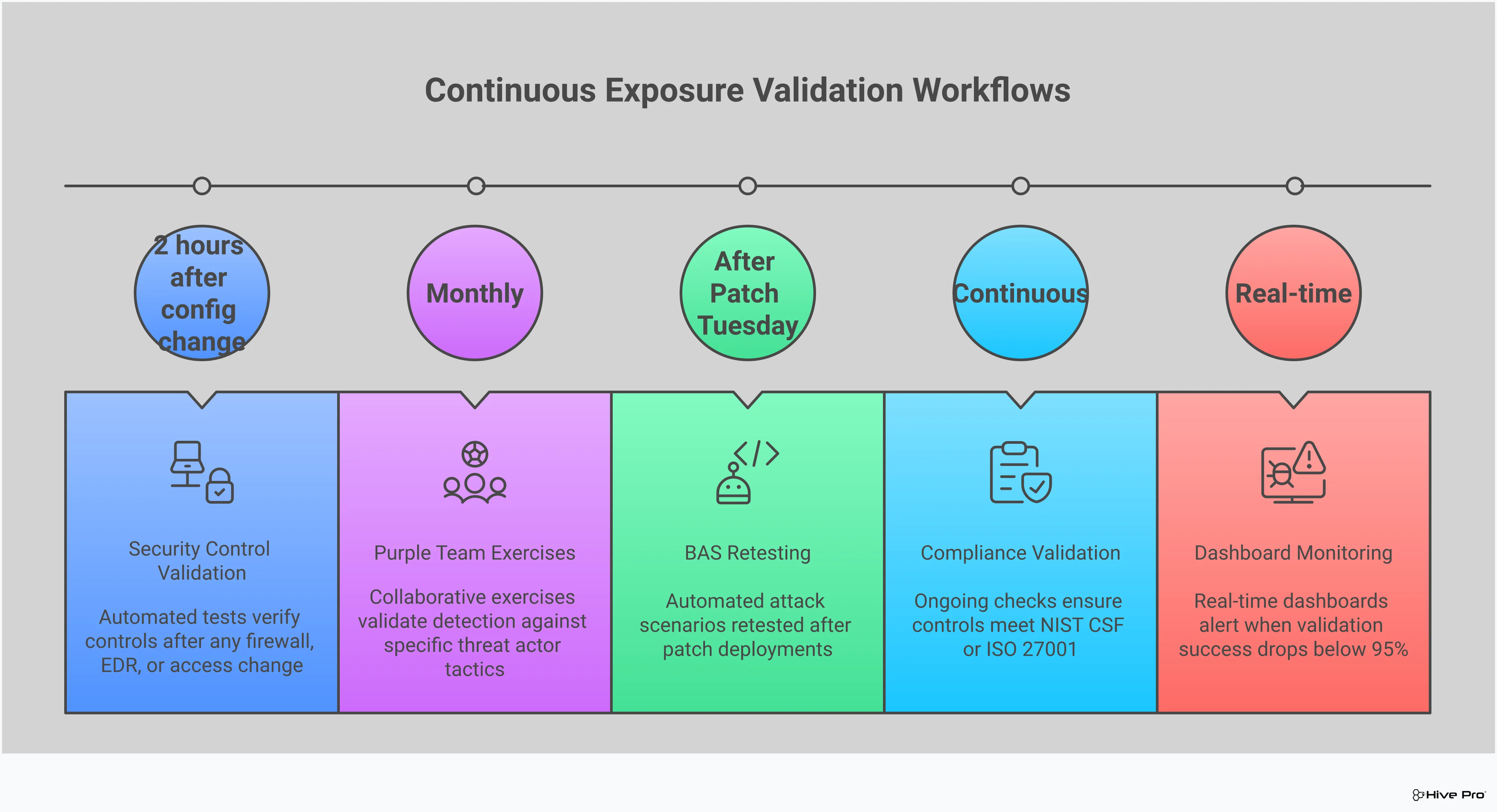
The core of exposure management is its continuous nature. This isn’t about quarterly scans or annual pen tests; it’s about establishing a constant rhythm of discovery, validation, and remediation. Think of it as a strategic framework that keeps a live pulse on your security exposures. Your workflows should systematically find assets across your entire attack surface, validate the risks they pose, prioritize them based on real-world threats, and track remediation efforts. This creates a feedback loop that ensures you’re always aware of your security posture and can adapt quickly as new threats or assets appear. It’s about making security an ongoing, integrated part of your operations, not a series of isolated events.
An exposure management program can’t live in a silo. Its success depends on collaboration between different teams. Your cloud security specialists, network analysts, DevOps teams, and vulnerability management experts all have a piece of the puzzle. Bringing them together creates a shared understanding of the threat landscape and clarifies everyone’s role in managing it. When teams work from a single source of truth and have common goals, you can close gaps much faster. This isn’t just about holding more meetings; it’s about creating a culture where security is a shared responsibility, and everyone is empowered to act on the insights your program generates.
The right technology is what makes a continuous exposure management program manageable. You need tools that can automate the heavy lifting, from discovering new assets to correlating threat intelligence. A unified platform that combines threat intelligence with risk-based prioritization is essential for ensuring your team focuses on what truly matters. Automation helps you swiftly assess and secure any new resource that comes online, cutting down the time an exposure exists. By choosing a comprehensive platform like Uni5 Xposure, you can streamline your workflows, reduce manual effort, and give your team the visibility it needs to act confidently and proactively.
My team is already swamped with vulnerability alerts. Won’t this just create more work? That’s a fair question, and it gets to the heart of the problem this approach solves. Exposure management is designed to reduce your workload, not add to it. Instead of giving you another long list of potential issues, it uses real-world threat intelligence and business context to show you the handful of exposures that create a genuine, provable risk. The goal is to cut through the noise so you can stop chasing down low-risk alerts and focus your team’s valuable time on fixing the critical gaps that attackers are most likely to exploit.
How is this really different from a mature vulnerability management program? Think of it as an evolution. A strong vulnerability management program is great at finding individual flaws, like an unlocked window in a large building. Exposure management steps back to see the whole picture. It looks at how an attacker could get through that window, move through the hallways, and reach the vault. It connects individual weaknesses—like software flaws, cloud misconfigurations, and weak credentials—to map out entire attack paths and prioritizes them based on the actual risk they pose to your most critical assets.
We already do annual penetration tests. Why do we need Breach and Attack Simulation (BAS)? Penetration tests are an incredibly valuable snapshot of your defenses at a single point in time. Breach and Attack Simulation, however, is like having a continuous, automated pen test running all the time. It constantly and safely tests your security controls against the latest attacker techniques to give you a real-time understanding of your security posture. This allows you to validate that your defenses are working as expected day-to-day and immediately confirm that your remediation efforts were successful, rather than waiting a year to find out.
What’s the most important first step to get started with exposure management? The best place to start is by getting a complete and accurate picture of your entire attack surface. You simply can’t protect what you don’t know you have. This means going beyond your known servers and applications to discover all of your assets, including cloud infrastructure, APIs, and shadow IT. Establishing this comprehensive inventory is the foundation upon which you can build the rest of your program, from prioritizing risks to validating your defenses.
Is exposure management only for big companies with huge security teams? Not at all. In fact, the principles of exposure management can be even more critical for smaller teams with limited resources. When you don’t have the capacity to address every single alert, you have to be strategic about where you focus your efforts. An exposure management approach helps you do exactly that by pinpointing the most significant risks to your business. The right platform can automate much of the discovery and prioritization work, making it a manageable and highly effective strategy for teams of any size.