Comprehensive Threat Exposure Management Platform
Modern vulnerability scanners can produce a staggering amount of data, leaving teams drowning in alerts and struggling to figure out what to fix first. This data overload often leads to inaction, while a lack of clear ownership means critical flaws get ignored. A strong policy cuts through this noise. It establishes a clear, risk-based system for prioritization and assigns accountability for every asset, ensuring teams focus on the most critical threats. It transforms a flood of information into a focused, actionable plan. We’ll provide a vulnerability management policy template and guide you through creating a process that brings control and clarity to your program.
A vulnerability management policy is your organization’s official game plan for finding and fixing security weaknesses. Think of it as a structured set of guidelines that details how your team will identify, assess, prioritize, and resolve vulnerabilities across your entire digital landscape, from servers and networks to applications and cloud assets. It’s the document that answers critical questions like: What do we scan? How often? Who is responsible for fixing what? And how quickly do we need to act?
Without a formal policy, vulnerability management can feel like a constant, chaotic fire drill. Your team might be patching furiously but without a clear sense of priority, potentially wasting time on low-risk issues while critical threats slip through the cracks. A well-defined policy transforms this reactive scramble into a proactive, repeatable process. It establishes clear expectations, assigns ownership, and creates a consistent framework for reducing your organization’s threat exposure. This clarity not only strengthens your security posture but also makes your program more efficient and defensible. When everyone from IT ops to security analysts understands the rules of engagement, you get better alignment and faster remediation. It’s the foundation for moving from simply reacting to vulnerabilities to strategically managing your cyber risk.
At its heart, the purpose of a vulnerability management policy is to systematically reduce your attack surface. The goal isn’t just to find every single flaw; it’s to prioritize fixes based on the actual risk they pose to your business. This is crucial because no organization has unlimited resources. With common barriers like budget constraints and skill shortages, you can’t afford to treat all vulnerabilities equally. Your policy provides the framework to focus your team’s time and energy on the weaknesses that attackers are most likely to exploit, ensuring your most critical assets are protected first. It turns vulnerability data into actionable, risk-informed decisions.
Your vulnerability management policy isn’t a standalone document; it’s a cornerstone of your entire cybersecurity strategy. It connects directly to other key security functions, including asset management, configuration management, and incident response. Effective vulnerability management is a continuous process that feeds critical data into your broader risk management program, helping you make more informed decisions about where to invest in security controls. By integrating this policy, you shift from a narrow focus on patching to a more holistic approach of managing your total attack surface. It helps you build a resilient security program that can adapt to new threats and protect the business from disruption.
A vulnerability management policy is more than just a document you write once and file away. Think of it as the strategic playbook that guides your entire security program. Without one, teams often operate in a reactive mode, chasing down the latest threats without a clear plan or consistent process. This approach is exhausting and, frankly, ineffective against sophisticated attackers. A well-defined policy transforms this chaos into a structured, proactive process that everyone can follow, creating a predictable rhythm for your security operations.
It sets clear expectations for everyone involved, from identifying assets and scanning for weaknesses to prioritizing and remediating risks. Who is responsible for patching a critical server? How quickly must it be done? Your policy answers these questions before they become a problem during a real incident. This document ensures consistency, accountability, and a unified approach to protecting your organization’s most critical assets. It’s the foundation that allows you to build a mature security posture, moving from simply putting out fires to strategically managing your threat exposure. It aligns your technical teams with business objectives, ensuring that security efforts are focused on what truly matters to keep the business running safely and smoothly.
Let’s be direct: managing vulnerabilities is a significant challenge for most security teams. A formal policy provides the structure needed to move from simply reacting to threats to proactively reducing your attack surface. It establishes a repeatable process for finding, assessing, and fixing security weaknesses across your entire network. By defining procedures and responsibilities, you create a system that doesn’t rely on last-minute heroics. This framework is essential for using vulnerability management tools effectively, allowing you to automate scanning and remediation workflows. A policy turns your security efforts into a well-oiled machine, consistently protecting your organization from potential breaches.
In many industries, having a documented vulnerability management policy isn’t just a good idea, it’s a requirement. Frameworks like PCI DSS, HIPAA, and ISO 27001 mandate that organizations have formal processes for managing security weaknesses. A clear policy is your first line of defense during an audit, demonstrating that you take security and governance seriously. It helps you align your security practices with compliance frameworks, ensuring you meet your legal and contractual obligations. This document proves you have a systematic approach to discovering your assets, identifying risks, and holding teams accountable for remediation, which is crucial for maintaining trust with customers and partners.
Ultimately, the goal of vulnerability management is to prevent security incidents that could disrupt your business. A policy ensures you have a plan to spot and address potential issues before they can be exploited by attackers. By mandating continuous scanning and establishing a system for risk-based prioritization, you can focus your team’s limited time and resources on the threats that pose the greatest danger to your operations. This proactive stance minimizes the likelihood of a breach that could lead to downtime, data loss, or reputational damage. A solid policy is a cornerstone of business continuity, helping you maintain operational resilience in the face of constant threats.
A strong vulnerability management policy is your roadmap for finding and fixing security weaknesses. Think of it as the essential framework that guides your team’s efforts, ensuring everyone is on the same page. It moves your program from a chaotic, reactive scramble to a structured, proactive operation. To be effective, your policy needs to be clear, comprehensive, and actionable. It should detail every step of the process, from discovering assets to confirming a fix is in place. Here are the five core components every solid policy should have.
First things first, you need to define exactly what you’re protecting. Your policy’s scope should clearly outline all the assets covered, including servers, endpoints, network devices, applications, and cloud environments. Be specific about what’s in-scope and, just as importantly, what’s out-of-scope. This clarity prevents confusion and ensures no critical assets are overlooked. A complete and continuously updated asset inventory is the foundation of this step. After all, you can’t protect what you don’t know you have. Having a clear scope helps your team focus its resources on the systems that matter most and provides a solid baseline for your entire threat exposure management program.
Once you know what you’re protecting, you need to decide who is responsible for protecting it. A policy without clear ownership is just a document that collects dust. Define and assign specific roles for every stage of the vulnerability management lifecycle. Who is responsible for running scans? Who analyzes the results? Who owns the remediation of a specific application or system? Who verifies that a patch has been successfully applied? Clearly documenting these responsibilities in a RACI (Responsible, Accountable, Consulted, Informed) chart can eliminate confusion and finger-pointing when a critical vulnerability appears. This creates a culture of accountability and ensures that tasks don’t fall through the cracks.
This section gets into the “how” of your program. It should detail the procedures for identifying vulnerabilities across your defined scope. Specify the tools your team will use for scanning and the required frequency of these scans. For example, you might mandate weekly authenticated scans for internal servers and continuous monitoring for external-facing applications. Your policy should also describe the different types of assessments you’ll perform, such as network scans, web application tests, and agent-based scans. Automating these procedures with a unified platform is key to managing this process at scale, allowing your team to find weaknesses consistently and efficiently without constant manual effort.
Not all vulnerabilities carry the same level of risk. A critical flaw in a public-facing server is much more urgent than a low-risk issue on an isolated internal workstation. Your policy must establish a clear system for classifying risk and prioritizing remediation efforts. While CVSS scores are a common starting point, a mature policy goes further by incorporating business context and real-world threat intelligence. You need a process that answers questions like: Is this vulnerability being actively exploited in the wild? Does it affect a critical business application? A risk-based prioritization model helps you focus on the threats that pose the greatest danger to your organization, ensuring your team’s time is spent wisely.
Finding vulnerabilities is only half the battle; fixing them is what truly reduces risk. Your policy needs to set firm deadlines for remediation based on the vulnerability’s severity level. These Service Level Agreements (SLAs) create urgency and provide a clear benchmark for success. For instance, you might require critical vulnerabilities to be patched within 15 days, high-severity ones within 30, and so on. The policy should also outline the entire remediation workflow, from initial notification to patch deployment and final verification. This includes procedures for handling exceptions, such as when a patch is not available and mitigating controls are needed instead.
A template is a fantastic starting point, but it’s not a one-size-fits-all solution. To create a vulnerability management policy that actually works, you need to tailor it to your organization’s specific environment. Think of it as a blueprint; you still need to choose the materials and make adjustments based on the landscape. A policy that isn’t customized to your reality will likely end up on a digital shelf, collecting dust.
The most effective policies are living documents that reflect your company’s unique operational context. This means digging into the details of your industry, your company’s size and structure, your leadership’s appetite for risk, and the security tools you already have in place. By customizing your policy around these core areas, you move from a generic checklist to a practical guide that your teams can use to make smart, consistent decisions about managing vulnerabilities. This process ensures your policy is not just compliant, but truly effective in reducing your threat exposure.
Every industry faces a different set of threats and regulatory pressures. A healthcare organization handling patient data under HIPAA has vastly different compliance requirements than a retail company processing credit cards under PCI DSS. Your policy must reflect these specific obligations. Start by identifying the regulations and standards that govern your industry and build your policy to meet them. This includes defining which assets are subject to which rules and outlining the specific scanning, reporting, and remediation activities required for compliance. A generic approach won’t cut it when auditors come knocking or when you’re facing industry-specific attack campaigns.
The way you manage vulnerabilities at a 100-person startup is fundamentally different from how you’d do it at a global enterprise with thousands of employees. Your policy needs to be realistic for your team’s scale and structure. For smaller companies, the policy might assign multiple responsibilities to a single person, while larger organizations will need to define complex workflows across different teams like IT, DevOps, and security. Be honest about your resources. Outdated scanning methods and a lack of accountability are common struggles, so your policy must clearly designate who owns each step of the process, from discovery to remediation, in a way that fits your organizational chart.
How much risk is your organization willing to accept? The answer to this question should be the foundation of your vulnerability prioritization and remediation timelines. Your policy needs to formally define your organization’s risk tolerance and translate it into concrete service level agreements (SLAs) for fixing vulnerabilities. For example, your policy might state that critical vulnerabilities on internet-facing systems must be patched within 7 days, while low-risk issues on internal development servers can be addressed within 90 days. This alignment ensures that your team focuses its limited time and resources on the threats that pose the greatest danger to your business operations.
Your vulnerability management policy shouldn’t operate in a silo. It needs to plug directly into your broader security program and any frameworks you follow, like the NIST Cybersecurity Framework or ISO 27001. This integration ensures consistency across all your security efforts. For instance, the risk classifications in your policy should match those used in your incident response plan. Likewise, your remediation workflows should align with your IT change management processes. Using a unified platform like Hive Pro Uni5 can help connect these dots, creating a seamless flow from vulnerability detection to remediation and validation. This creates a cohesive strategy rather than a collection of disconnected security tasks.
Having a policy on paper is a great first step, but putting it into practice is where the real work begins. Even the most well-crafted vulnerability management policy can stumble if you don’t anticipate the common hurdles that can derail implementation. Many organizations find themselves struggling with the same set of challenges, from resource constraints to technical blind spots.
The key is to recognize these potential roadblocks early and build strategies to address them directly within your plan. It’s not just about writing rules; it’s about creating a living process that your team can realistically follow. Let’s walk through some of the most frequent challenges and discuss practical ways to handle them so your policy can move from a document to a dynamic part of your security culture.
It’s a familiar story for many security teams: you have a solid plan but lack the funding or specialized talent to execute it perfectly. In fact, many organizations point to budget constraints and skill shortages as the biggest barriers to effective vulnerability management. When you can’t hire more analysts, the goal becomes making your current team more efficient. This is where automation and smart tooling come in. A modern threat exposure management platform can automate routine scanning, data analysis, and reporting, freeing up your team to focus on critical remediation and strategic tasks. By leaning on technology to handle the heavy lifting, you can bridge resource gaps and empower your existing staff to achieve more.
You can’t protect what you don’t know you have. A major challenge for any vulnerability management program is maintaining a complete and accurate inventory of all your assets. Outdated scanning methods often miss cloud instances, remote devices, and shadow IT, leaving dangerous blind spots in your defenses. Your policy needs to be supported by a process for continuous discovery. Implementing a solution for total attack surface management ensures you have full visibility across your entire environment. This allows you to apply your policy consistently everywhere, from on-premise servers to ephemeral cloud containers, ensuring no asset is left unsecured.
Modern vulnerability scanners can produce a staggering amount of data, leaving teams drowning in alerts and struggling to figure out what to fix first. Without a clear system for prioritization, this data overload leads to inaction. At the same time, a lack of defined accountability means critical vulnerabilities can be ignored because no one knows who is responsible for fixing them. Your policy must establish a clear, risk-based approach to prioritize vulnerabilities and assign ownership for every asset. This ensures that teams focus on the most critical threats and that every vulnerability has a designated owner responsible for its remediation.
Many security teams operate with a collection of disconnected tools that don’t share information, creating manual work and slowing down response times. If your vulnerability scanner, ticketing system, and patch management tools aren’t integrated, your team is likely wasting valuable time copying and pasting data between systems. A successful policy implementation depends on a seamless workflow. By integrating your security tools, you can automate the entire lifecycle of a vulnerability, from detection to remediation. This creates an efficient ecosystem where data flows freely, tasks are automatically assigned, and your team can resolve issues faster.
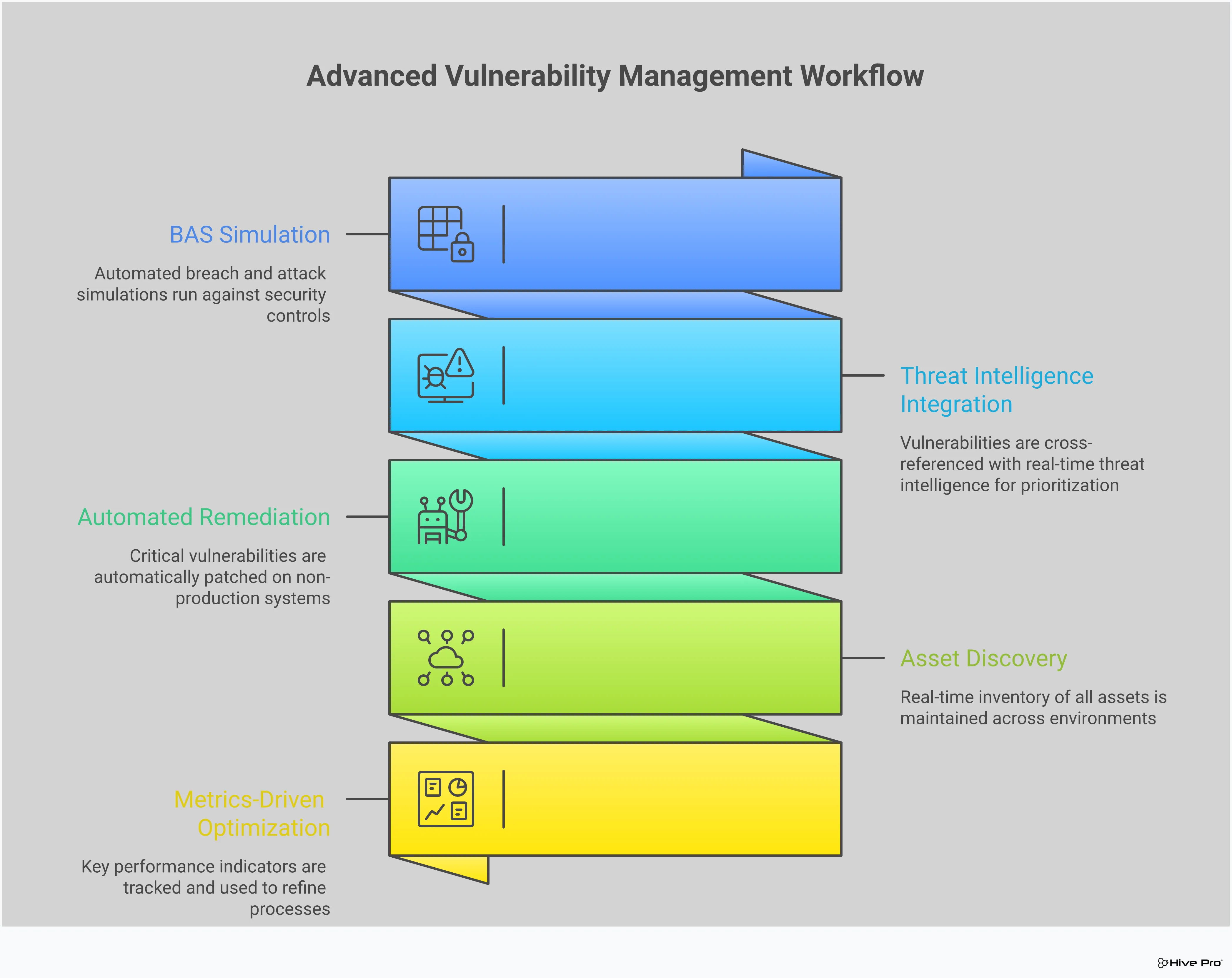
A solid vulnerability management policy sets the ground rules, but truly effective programs go beyond simple compliance. To stay ahead of attackers, you need to adopt strategies that are proactive, intelligent, and automated. This means moving from a reactive cycle of scan-and-patch to a continuous process of exposure management. By incorporating advanced tactics, you can focus your team’s efforts where they’ll have the greatest impact, validate your security controls, and significantly reduce your organization’s risk profile. Let’s look at four strategies that can transform your vulnerability management program from a necessary chore into a strategic advantage.
Your scanners will likely find thousands of vulnerabilities, and trying to patch them all is an impossible task. This is where threat intelligence becomes your most valuable asset. Instead of working through a massive list, you can focus on the vulnerabilities that attackers are actively exploiting right now. High-quality threat intelligence provides the context you need to understand which threats pose a genuine, immediate risk to your organization. By layering this data over your scan results, you can implement a truly risk-based approach. This allows your team to prioritize remediation efforts effectively, tackling the most dangerous exposures first and making the best use of limited resources.
Patching a vulnerability is one thing, but how do you know your security controls will actually stop an attack? That’s the question Breach and Attack Simulation (BAS) helps you answer. BAS platforms continuously and safely simulate real-world attack tactics, techniques, and procedures (TTPs) against your security infrastructure. This process validates whether your firewalls, EDR, and other controls are configured correctly and working as expected. It’s a crucial step beyond traditional scanning, providing concrete proof of your security posture’s effectiveness. By using adversarial exposure validation, you can identify and close gaps before an actual attacker finds them, ensuring your defenses are truly resilient.
The Common Vulnerability Scoring System (CVSS) is a useful starting point, but relying on it alone can be misleading. A CVSS score doesn’t understand your unique environment. For example, a “critical” vulnerability on an isolated development server may pose less risk than a “medium” one on your customer-facing payment portal. To make smart decisions, you need context-aware prioritization. This means considering the asset’s business criticality, its network exposure, and whether there’s active exploitation in the wild. Combining these factors with the CVSS score gives you a true picture of risk, helping you create a vulnerability and threat prioritization strategy that protects what matters most to your business.
Manual remediation processes are a major bottleneck in vulnerability management. They are slow, prone to human error, and simply can’t scale to meet the speed of modern threats. Integrating automation into your remediation workflows is essential for reducing your exposure window. By connecting your vulnerability management platform with IT ticketing systems, patch management tools, and SOAR platforms, you can create a seamless process. This shifts vulnerability management from a reactive, report-driven task to a continuous, autonomous security function. Automation handles the repetitive work, like creating tickets and deploying patches, freeing up your security and IT teams to focus on more complex and strategic initiatives.
A policy on paper is just the beginning. Bringing it to life requires a thoughtful rollout strategy that embeds these new practices into your company culture. It’s about turning rules into routines and ensuring everyone, from the security team to developers, understands their part. A successful launch isn’t a single event; it’s a continuous process of communication, training, and refinement. By focusing on these key practices, you can make sure your vulnerability management policy is not only implemented but also truly effective in protecting your organization.
Your attack surface is always changing, so your scanning should be constant. Moving away from scheduled, periodic scans to a continuous model gives you a real-time view of your security posture. But finding vulnerabilities is only half the battle. The sheer volume can be overwhelming, which is why vulnerability and threat prioritization is so critical. Instead of just relying on CVSS scores, focus on vulnerabilities that pose a genuine threat to your specific environment. Automation is essential for managing this process at scale, allowing your team to find, assess, and trigger remediation workflows for the weaknesses that matter most without constant manual oversight.
A policy is only effective if your team understands and follows it. That’s why comprehensive training is non-negotiable. Your program should go beyond simply handing out a document. It needs to educate employees on the “why” behind the policy, their specific responsibilities, and the potential consequences of inaction. This isn’t a one-and-done event. Ongoing security awareness helps keep security top of mind and reinforces best practices. By investing in your people, you turn your entire organization into an active participant in your defense, spotting potential issues before they can be exploited and creating a stronger security culture.
Vulnerability management isn’t just a security team problem; it’s an organizational responsibility. Your policy rollout must break down silos between security, IT operations, and development teams. When everyone understands their role and feels a sense of ownership, remediation happens faster and more effectively. The policy should clearly define accountability, so there’s no confusion about who is responsible for patching a specific server or updating a piece of software. Fostering this collaborative security culture ensures that vulnerabilities don’t fall through the cracks and that your security framework is strengthened by teamwork, not hindered by departmental divides.
The digital world doesn’t stand still, and neither should your vulnerability management policy. Treating it as a one-time project is a common mistake that leaves organizations exposed. Your infrastructure evolves, new technologies are adopted, and attackers constantly develop new techniques. To remain effective, your policy must be a living document. Schedule regular reviews, at least annually or after any significant change like a major system deployment or a security incident. This continuous improvement cycle ensures your policy stays relevant to the current threat landscape and continues to provide a strong foundation for your security program.
A policy is a great starting point, but it’s the technology you use that brings it to life. Without the right tools, your vulnerability management policy is just a document collecting dust on a server. The right tech stack automates the tedious parts of the process, gives you clear visibility across your entire environment, and empowers your team to act decisively. Think of it as the engine that powers your policy, turning guidelines into concrete actions that strengthen your defenses.
When your tools work together, they create a seamless workflow from discovery to remediation, making it possible to manage risk effectively at scale. This integrated approach helps you move from a reactive stance, where you’re constantly chasing alerts, to a proactive one focused on reducing your overall threat exposure. A modern Threat Exposure Management Platform unifies these capabilities, providing a single source of truth for your security posture. Instead of juggling multiple dashboards and trying to connect the dots manually, your team gets a clear, prioritized list of what needs to be fixed now. This is how you transform vulnerability management from a compliance checkbox into a strategic security function. Let’s look at the key pieces of technology that make this possible.
At the core of any vulnerability management program are the tools that find the weaknesses in the first place. Vulnerability management platforms automate how your organization finds, assesses, and reports on security flaws across your networks, applications, and cloud infrastructure. Automation is the key here; it’s what allows you to continuously scan all your assets and assess risks without requiring constant manual oversight. A strong platform gives you a unified view of all your cyber risks in one place, cutting through the noise so you can see what truly matters and begin the process of remediation.
Finding vulnerabilities is only half the battle. The real goal is fixing them, and that’s where automation and remediation tools come in. These systems connect your vulnerability data with your other security tools, like SIEM or SOAR platforms, to create a smooth and efficient security ecosystem. Instead of just getting a list of problems, you can trigger automated workflows for patching, configuration changes, or ticketing. This approach helps your team respond to and remediate vulnerabilities much faster. It closes the loop between detection and response, ensuring that critical weaknesses don’t linger for weeks or months.
You can’t protect what you don’t know you have, and you can’t prioritize what you don’t understand. This is why asset discovery and threat intelligence are so critical. Asset discovery tools continuously scan your environment to give you a complete and up-to-date inventory of your entire attack surface. At the same time, threat intelligence provides crucial context, telling you which vulnerabilities are being actively exploited by attackers in the wild. This intelligence, often curated by research teams like HiveForce Labs, allows you to focus your remediation efforts on the threats that pose an immediate danger to your organization, rather than just chasing high CVSS scores.
A great vulnerability management policy is more than a document; it’s a framework that guides your security efforts. But how do you know if it’s working? Measuring success isn’t just about feeling secure, it’s about proving it with data. This is how you show the value of your program, prepare for audits without the last-minute scramble, and build a culture of continuous improvement that keeps you ahead of threats.
You can’t improve what you don’t measure. To gauge your policy’s effectiveness, you need to track the right Key Performance Indicators (KPIs). These metrics offer a clear picture of your performance and help justify security investments, especially when facing common barriers like budget constraints. Track essentials like Mean Time to Remediate (MTTR), vulnerability age, and scan coverage. A platform that provides a unified view of cyber risks can make tracking these metrics simple, turning raw data into actionable insights for your team and clear reports for leadership.
Audits don’t have to be a source of stress. With a well-defined policy, you can turn audit preparation into a routine process. Auditors want to see a structured, repeatable system for identifying, prioritizing, and fixing security weaknesses. Your policy is your playbook, and your reporting is the proof you’re following it. Many organizations struggle with incomplete asset visibility, which can make reporting a nightmare. By implementing a policy that mandates comprehensive asset discovery and continuous scanning, you create a single source of truth. This makes it easy to generate the reports needed to demonstrate compliance.
Cybersecurity is not a set-it-and-forget-it discipline. The threat landscape is always changing, so your program must adapt. Committing to a continuous improvement cycle means your policy is never static. It’s a living document you regularly review and update based on new threats, IT environment changes, and your KPIs. This proactive approach is about more than just finding flaws; it’s about knowing what matters and remediating efficiently. By integrating ongoing assessments and feedback loops, you can spot potential issues before they become critical incidents and ensure your security program grows stronger over time.
What’s the single most important part of a vulnerability management policy to get right? If you only get two things right, make them scope and ownership. You must clearly define which assets your policy covers and, just as importantly, assign a specific person or team responsible for every step of the process. Without a clear scope, critical systems get missed. Without clear ownership, vulnerabilities get discovered but never fixed because everyone assumes someone else is handling it. Nailing these two components creates the foundation of accountability that your entire program will be built on.
How often should we really review and update our policy? You should plan to review your policy at least once a year. However, treating it as only an annual task is a mistake. A better approach is to treat it as a living document. You should trigger a review anytime there’s a significant change in your organization. This could be the adoption of a new cloud platform, a major business acquisition, or even after a security incident. This ensures your policy always reflects your current environment and the threats you face today, not the ones from last year.
My team is already swamped. How can a policy help instead of just adding more work? This is a common concern, but a good policy actually reduces chaotic, unplanned work. It replaces last-minute fire drills with a structured, predictable process. By defining priorities and setting clear remediation timelines, your team can stop guessing what to fix and focus their energy on the risks that truly matter. When supported by the right automation tools, the policy streamlines workflows, cutting down on manual tasks and freeing your team to work on more strategic security initiatives.
You mentioned using threat intelligence. How does that practically change our day-to-day process? Practically speaking, it transforms your team’s to-do list from an overwhelming catalog of thousands of vulnerabilities into a short, manageable list of immediate threats. Instead of starting your day looking at every “critical” vulnerability based on a generic score, you start by asking what attackers are actively using right now. This allows your team to fix the handful of weaknesses that pose a clear and present danger first, which is a much more efficient and impactful way to reduce real-world risk.
How does a policy help us prepare for a security audit? A policy is your best friend during an audit. It serves as the official documentation of your process, showing auditors that you have a formal, repeatable system for managing security weaknesses. Instead of scrambling to prove you’re doing the right things, you can simply point to the policy and the reports from your tools that show you’re following it. It demonstrates a mature approach to security and governance, which is exactly what auditors are looking for.