Comprehensive Threat Exposure Management Platform
# How to Reduce Mean Time to Remediate (MTTR) in Cybersecurity
Every hour a vulnerability remains unpatched is an hour an attacker can use it against you. That window of exposure is exactly what Mean Time to Remediate (MTTR) measures, and for security leaders, it’s one of the most consequential metrics on the dashboard. A fast MTTR means your team is finding, fixing, and verifying vulnerabilities before adversaries can weaponize them. A slow one means you’re playing defense with the doors wide open.
The challenge is that most organizations measure MTTR incorrectly, chase the wrong improvements, or simply don’t know where the bottlenecks in their remediation lifecycle actually live. This guide breaks down what MTTR really measures, why it matters for your board and your risk posture, and the practical strategies your team can use to drive it down.
See how Uni5 Xposure reduces MTTR with automated remediation orchestration.
Mean Time to Remediate (MTTR) in cybersecurity is the average elapsed time between when a vulnerability is first discovered and when it is confirmed fully resolved. It is calculated by dividing the total remediation time across all resolved vulnerabilities by the number of vulnerabilities fixed in a given period.
The MTTR Formula:
MTTR = Total Remediation Time / Number of Vulnerabilities Remediated
For example, if your team resolved 50 vulnerabilities over a month with a combined remediation time of 1,500 hours, your MTTR is 30 hours per vulnerability.
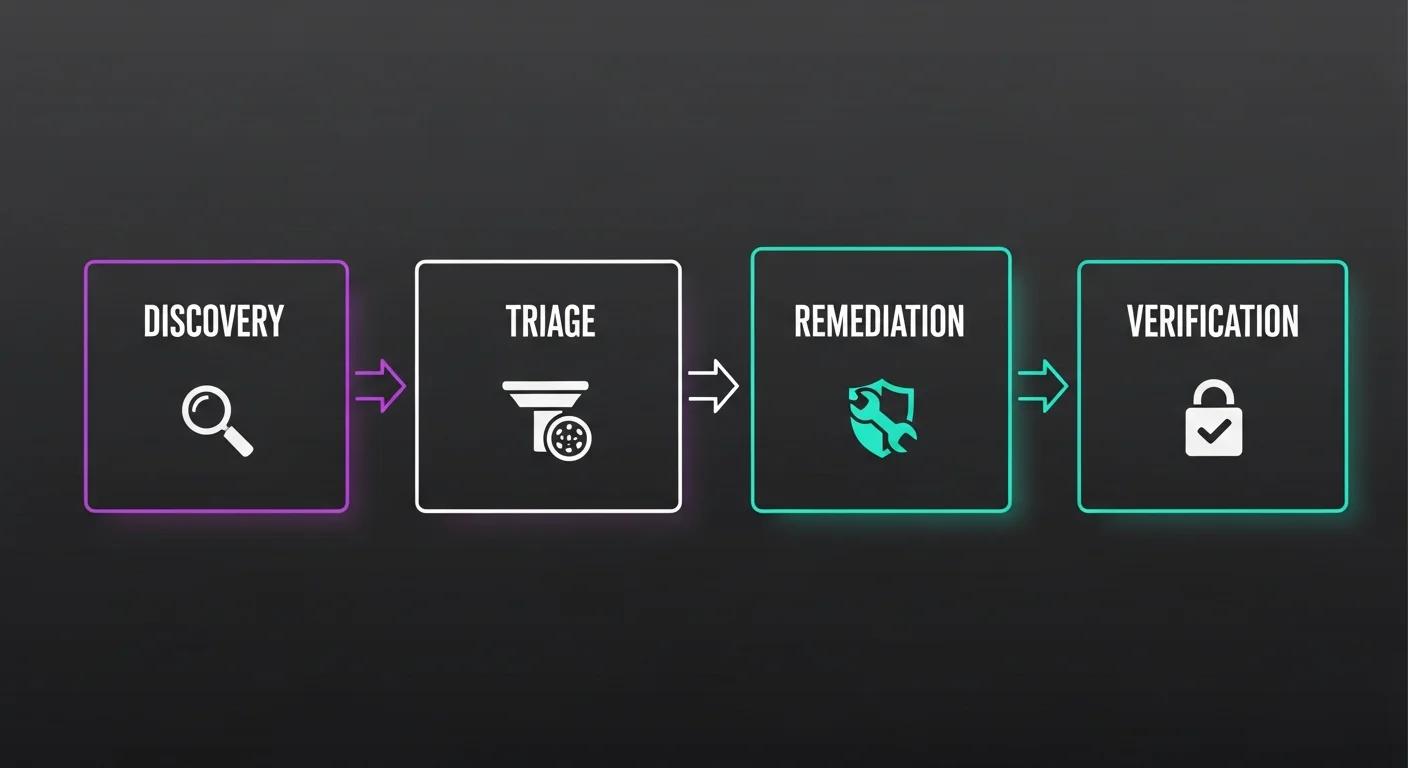
What makes MTTR powerful as a metric, and what makes it tricky to measure correctly, is that it encompasses four distinct phases:
Most organizations only track phase three, the patch deployment. This is a critical mistake. CISA’s Binding Operational Directive 22-01 requires federal agencies to remediate known exploited vulnerabilities within 14 days, and that benchmark has become a de facto standard across both public and private sectors. But if your triage phase alone takes 10 days, you’re already behind before a technician even starts working on the fix.
MTTR isn’t just a technical metric. It’s a measure of business risk. Every day a critical vulnerability sits unpatched, the probability of exploitation increases. For CISOs reporting to the board and security leaders managing SLAs, MTTR translates directly into two things: risk exposure and operational credibility.
The relationship is straightforward. A vulnerability that exists for 45 days gives attackers 45 days to find and exploit it. One that’s closed in 7 days gives them seven. Organizations with high-maturity security operations centers (SOCs) achieve remediation windows of hours for critical findings, while the average enterprise still takes 30 to 90 days. That gap represents real, measurable risk.
Regulatory frameworks like CISA BOD 22-01, FedRAMP, NIST, and PCI DSS all set remediation timelines. SEC cybersecurity disclosure rules now require companies to describe their risk management processes, and MTTR for validated findings is becoming a key piece of evidence that your program is operational, not just aspirational. Cyber insurers increasingly factor remediation speed into underwriting decisions and premium calculations.
When combined with cyber risk quantification, MTTR becomes a financial metric. Each day of reduced MTTR translates to a measurable reduction in annualized breach probability. This gives security leaders a powerful tool for justifying budget, headcount, and tooling decisions in language the board understands: dollars of reduced risk per day of improved MTTR.
Before you can improve MTTR, you need to make sure you’re measuring it correctly. Several common practices inflate MTTR performance and create false confidence.
The most common error is equating patch deployment with remediation. A patch addresses one specific vulnerability, but many findings require additional steps: configuration changes, service restarts, dependency updates, or architectural modifications. If you measure when the patch was applied rather than when the vulnerability was confirmed closed, you’re systematically understating your actual exposure window.
If you mark a finding as “remediated” without retesting, you’re reporting an assumption, not a fact. Across the industry, offensive security teams consistently find that 10 to 20 percent of “remediated” findings remain exploitable after the initial fix attempt. The patch was applied to the wrong server, the configuration change was overwritten by automation, or the fix addressed the symptom but not the root cause.
A single MTTR number is almost meaningless without segmentation. Your MTTR for informational findings will drag down the average, masking the fact that your critical vulnerability remediation might be dangerously slow. Always segment MTTR by severity (critical, high, medium) and report each separately. The board cares most about how fast you close critical, exploitable vulnerabilities, not your blended average.
The time between discovery and assignment is often the largest hidden contributor to MTTR. Automated scanners might find a vulnerability on Monday, but if it sits in a queue until Thursday before someone triages and assigns it, you’ve already burned four days before any remediation work begins.
Benchmarks vary by industry, organization size, and vulnerability severity, but here are the reference points that matter most:
| Severity Level | Leading Organizations | CISA BOD 22-01 | Typical Enterprise |
|—|—|—|—|
| Critical (exploited) | 7-15 days | 14 days | 30-60 days |
| Critical (not exploited) | 15-30 days | N/A | 60-90 days |
| High | 30-45 days | N/A | 90-120 days |
| Medium | 60-90 days | N/A | 120-180 days |
The most meaningful benchmark isn’t an absolute number. It’s your own trend. Consistent quarter-over-quarter improvement in MTTR for critical findings indicates a maturing program, regardless of where you start.
Reducing MTTR requires improvements across the entire discovery-to-verification lifecycle, not just faster patching. Here are seven strategies that target the biggest time sinks in the remediation process.
Not all vulnerabilities deserve the same urgency. A CVSS 9.8 vulnerability with no known exploit on an isolated development server is less urgent than a CVSS 7.5 vulnerability being actively weaponized against your production database. Risk-based vulnerability and threat prioritization combines exploit intelligence, asset criticality, and business context to help your team focus remediation effort on the findings that represent genuine, immediate risk.
This single shift, fixing fewer things but the right things, is the fastest way to reduce your MTTR for the vulnerabilities that actually matter to your business.
If the gap between discovery and assignment is eating days of your MTTR, automate it. Set up severity classification rules that automatically route critical findings to the responsible team with SLA triggers that escalate untriaged findings after defined thresholds. The goal is to ensure that a critical vulnerability discovered at 2 AM on Saturday is assigned and visible to the right team within hours, not days.
Pre-enrich findings with asset context, owner information, and threat intelligence at ingest time so the assigned team can start working immediately rather than spending hours gathering context.
The handoff between security and IT operations teams is where remediation stalls. Manual ticket creation, incomplete context, and unclear ownership cause delays that compound across hundreds of vulnerabilities. Automating the creation and assignment of remediation tickets in systems like Jira or ServiceNow, complete with all the context and step-by-step remediation guidance, establishes clear ownership and accountability.
This approach streamlines the entire workflow from finding to fix. It eliminates manual back-and-forth, ensures nothing falls through the cracks, and creates a consistent, repeatable process for patching and validation. For well-understood vulnerability classes like missing patches, configuration drift, and certificate expiration, automated remediation can dramatically reduce MTTR for those categories while freeing human attention for complex findings.
Book a demo to see how Uni5 Xposure automates vulnerability prioritization and remediation.
Recurring findings indicate that remediation is addressing symptoms rather than root causes. If the same class of vulnerability keeps appearing across your environment, the fix isn’t another patch. It’s a process change, a template update, or an architectural decision. Track vulnerability recurrence rates alongside MTTR. A high recurrence rate inflates your MTTR because you’re fixing the same problems repeatedly. Invest in addressing the underlying cause once, and your future MTTR drops permanently for that entire vulnerability class.
A vulnerability is only a theoretical problem until an attacker decides to exploit it. Integrating real-time threat intelligence, like the data curated by research teams such as HiveForce Labs, gives you a direct line of sight into which vulnerabilities are being actively weaponized. This intelligence allows you to instantly elevate the priority of findings that are under active attack and deprioritize those that aren’t currently being targeted.
This isn’t just about faster prioritization. It’s about smarter allocation of your team’s limited time and resources to the threats that pose a clear and present danger.
A remediated vulnerability that hasn’t been verified is a liability, not a closed ticket. Implement a process for retesting every remediated finding above a defined severity threshold. Without retesting, your MTTR includes an unknown number of false closures that are still exploitable.
Adversarial exposure validation through techniques like Breach and Attack Simulation (BAS) can automate this verification step. By safely simulating real-world attack techniques against remediated vulnerabilities, you confirm that the fix actually works and that the attack path is truly closed. This step adds time to your MTTR initially, but it produces a metric that reflects actual risk reduction, not aspirational patching activity.
Fragmented tooling is a silent MTTR killer. When your vulnerability scanner, asset inventory, ticketing system, and threat intelligence feed don’t talk to each other, your team is manually piecing together data across multiple consoles. Each context switch and manual data transfer adds minutes that compound into days across your vulnerability inventory.
A unified threat exposure management platform that consolidates asset discovery, vulnerability scanning, threat intelligence, prioritization, and remediation orchestration into a single view eliminates these handoff delays. When a vulnerability is discovered, it’s automatically enriched with asset context and threat intelligence, prioritized, and routed to the right team with full remediation guidance, all within one workflow.
Tracking MTTR correctly is just as important as reducing it. Here’s how to build a measurement framework that drives action.
Report MTTR for critical, high, and medium findings separately. A blended average masks the performance issues that matter most. Your board cares about critical vulnerability MTTR, not how fast you close informational findings.
A single month’s MTTR number is noisy. Track rolling 90-day averages and quarter-over-quarter trends. Consistent improvement matters more than hitting an arbitrary benchmark.
Frame MTTR in terms of business risk. Instead of reporting “Our MTTR is 22 days,” say “Our MTTR for critical findings dropped from 45 days to 22 days, reducing our exploitable exposure window by 51 percent.” This connects your team’s work directly to measurable risk reduction.
MTTR doesn’t capture the full story. Mean Time to Detect (MTTD), the average time between when a vulnerability appears and when it’s discovered, represents the invisible exposure window before your MTTR clock even starts. Tracking MTTD alongside MTTR gives you a complete view of your exposure lifecycle from vulnerability creation to confirmed closure.
MTTR should be a living metric tracked on your team’s operational dashboard, not a quarterly report artifact. Real-time MTTR tracking helps you spot triage delays, remediation slowdowns, and verification backlogs as they happen, allowing you to course-correct before they compound into a significant risk.
Reduce your MTTR with Hive Pro’s unified threat exposure management platform.
Even with the right strategies, a few common mistakes can undermine your MTTR improvement efforts.
Rushing patches without proper testing can introduce new vulnerabilities or break critical applications. A fix that causes an outage is worse than a delay. Always test patches in a controlled environment before production deployment.
Vulnerability management is a team sport. Security finds the problems, but IT operations and development teams implement the fixes. If these teams operate in silos with no shared goals or SLAs, your remediation workflows will bottleneck at the handoff every time. Shared dashboards, integrated ticketing, and agreed-upon SLAs keep everyone aligned.
MTTR is one metric in a broader operational picture. Pair it with vulnerability recurrence rate, scan coverage percentage, SLA compliance rate, and mean time to detect (MTTD) for a complete view of your program’s health. Optimizing one metric in isolation can create perverse incentives, like closing tickets without verification to improve the number.
What is a good MTTR for critical vulnerabilities?
Leading organizations target 7 to 15 days for critical validated findings. CISA’s Binding Operational Directive 22-01 mandates 14-day remediation for known exploited vulnerabilities in federal agencies. The most meaningful benchmark, however, is your own trend. Consistent quarter-over-quarter improvement in MTTR for critical findings indicates a maturing program, regardless of where you start.
What is the difference between MTTR and MTTD?
Mean Time to Detect (MTTD) measures how quickly you identify that a vulnerability exists. MTTR measures how quickly you fix it after discovery. Together, they represent the total exposure window. An organization can have a fast MTTR but a slow MTTD, meaning vulnerabilities sit undiscovered for weeks before the remediation clock even starts.
Should MTTR include retesting time?
Yes. MTTR without retesting measures when you attempted a fix, not when the vulnerability was actually closed. Including verification through techniques like Breach and Attack Simulation produces a more accurate but often longer MTTR. This is the correct trade-off: an honest metric that reflects actual risk reduction is far more valuable than an optimistic number that doesn’t.
How does automation reduce MTTR?
Automation reduces MTTR by compressing or eliminating the manual steps in the remediation lifecycle: automated triage and routing cuts the discovery-to-assignment gap, automated ticket creation with full remediation context eliminates handoff delays, and automated retesting confirms fixes without waiting for a manual verification cycle. Organizations leveraging automation across the full lifecycle report 40 to 60 percent reductions in overall MTTR.
Can you have a low MTTR but still be at risk?
Absolutely. If your MTTR only covers patch deployment without verification, you may be reporting a low number while 10 to 20 percent of “fixed” vulnerabilities remain exploitable. Similarly, if you’re measuring MTTR for all vulnerabilities equally, you could have excellent overall numbers while your critical vulnerability MTTR is dangerously high. Segmented, verified MTTR is what matters.