Comprehensive Threat Exposure Management Platform
If you tried to fix every vulnerability your scanners found, your team would never do anything else. The truth is, not all vulnerabilities are created equal. A high CVSS score doesn’t always translate to high risk for your specific business. The real danger comes from weaknesses that are actively being exploited by attackers in the wild. The challenge is cutting through the noise to find them. This is where an enterprise data security platform changes the game. By enriching your vulnerability data with real-time threat intelligence, it helps you prioritize the fixes that will have the biggest impact, allowing your team to focus its limited resources on the threats that truly matter.
Think of an enterprise data security platform as your central command center for protecting sensitive information. It’s a unified solution designed to find, classify, protect, and monitor your data, no matter where it lives—whether it’s on-premises, in the cloud, or spread across multiple cloud environments. The main goal is to give you a clear, comprehensive view of your data landscape so you can prevent breaches, stay on top of regulatory requirements, and confidently use your data without putting it at risk. Instead of juggling multiple, disconnected security tools, a dedicated platform brings everything together, simplifying how you manage and secure your most critical assets.
A solid data security platform handles several critical jobs. First, it excels at data discovery and classification, continuously scanning your environments to find sensitive data and label it appropriately. It also provides robust data protection and encryption, ensuring information is unreadable to unauthorized users, both at rest and in transit. Another key piece is access control and governance, which lets you define and enforce policies about who can see and interact with specific data. Finally, it offers real-time monitoring and response, flagging suspicious activity and giving you the tools to act quickly when a potential threat is detected.
Relying on a patchwork of security tools creates gaps that attackers can exploit. A dedicated platform closes those gaps by providing a single source of truth for your data security. This unified approach is crucial for reducing the financial and reputational impact of a data breach. It also makes achieving and maintaining compliance with regulations like GDPR, CCPA, and HIPAA much simpler, as you can easily demonstrate that the right controls are in place. Ultimately, a data security platform doesn’t just protect your data; it enables you to use it securely for analytics, AI, and other business drivers, turning security from a roadblock into a business advantage.
When you’re evaluating different data security platforms, it’s easy to get lost in a sea of features and buzzwords. The right platform isn’t just about adding another tool to your stack; it’s about finding a central hub that simplifies your security posture and gives you a clear path to action. A truly effective platform moves beyond simple detection and helps you proactively manage your entire threat exposure. To cut through the noise, focus on a few core capabilities that are essential for building a resilient security program. These features work together to give you a comprehensive view of your data, your defenses, and the threats you face.
Think of it as building a foundation. Without knowing what data you have, you can’t protect it. Without controlling access, your data is open to anyone. And without testing your defenses, you’re just hoping they work. The best platforms integrate these functions seamlessly, so you’re not juggling multiple dashboards and conflicting reports. They provide a single source of truth that helps your team move from a reactive, fire-fighting mode to a proactive, strategic one. This shift is critical for staying ahead of attackers and ensuring your security efforts are focused on what matters most.
You can’t protect what you don’t know you have. That’s why the first critical feature of any data security platform is its ability to discover and classify your data across your entire environment—from on-premise servers to multi-cloud deployments. A strong platform automatically scans your assets to find sensitive information, such as customer PII, intellectual property, or financial records. Once found, it should help you label that data based on its importance and sensitivity. This process is the foundation of your entire security strategy, as it tells you where your most valuable assets are and allows you to apply the right level of protection to the right data.
Once you know where your sensitive data lives, the next step is to control who can access it. A top-tier platform should provide robust tools for managing encryption and access controls. This includes securing data both at rest in your databases and in transit as it moves across your network. Look for features that enforce the principle of least privilege, ensuring that users and applications only have the minimum level of access necessary to perform their functions. This is often managed through role-based and policy-driven controls that you can configure and automate, which drastically reduces the risk of both accidental exposure and malicious insider threats.
The threat landscape is constantly changing, so your security platform needs to be able to keep up. Real-time monitoring is non-negotiable. This capability involves continuously watching for unusual activity or unauthorized access to your sensitive data. Modern platforms achieve this through a strategy known as Data Detection and Response (DDR), which uses behavioral analysis and machine learning to spot potential threats as they happen. When the platform detects a suspicious event, it should trigger an immediate alert and, in many cases, initiate an automated response to contain the threat before it can escalate into a full-blown breach. This proactive monitoring is key to shortening your response time and minimizing potential damage.
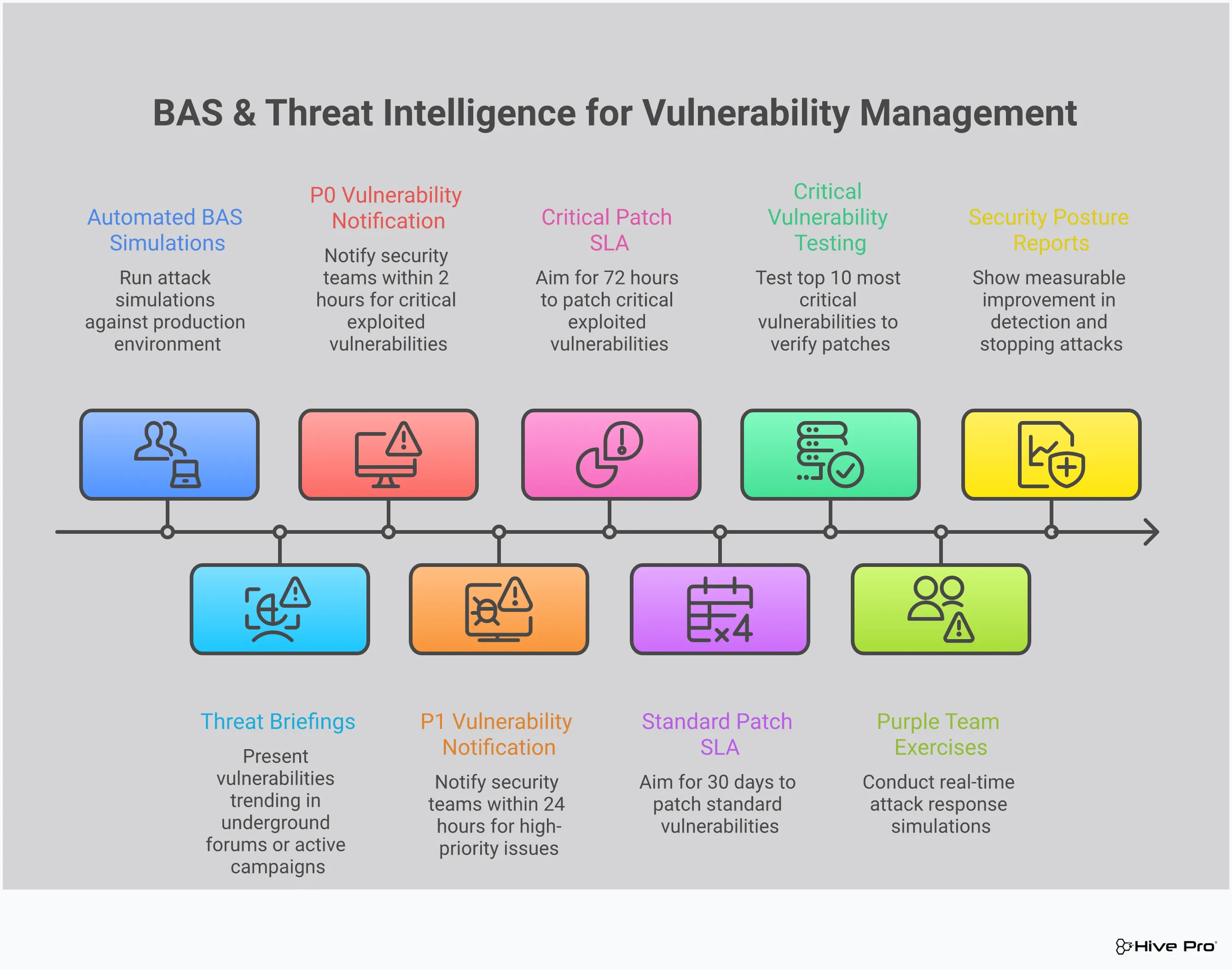
Having security controls in place is one thing, but knowing if they actually work against a real-world attack is another. This is where Breach and Attack Simulation (BAS) comes in. Instead of waiting for an attack to happen, a platform with BAS capabilities allows you to safely simulate common attack methods to test the effectiveness of your defenses. This process of adversarial exposure validation helps you identify gaps in your security posture—like misconfigured firewalls or ineffective endpoint protection—before an attacker can exploit them. It’s like having a dedicated red team on-demand, giving you concrete evidence of what’s working and what needs to be fixed.
Your team can’t fix every single vulnerability at once—it’s just not feasible. That’s why a great data security platform uses threat intelligence to help you prioritize. Threat intelligence provides context about which vulnerabilities are actively being exploited by attackers in the wild. By integrating this intelligence, the platform can highlight the risks that pose the most immediate danger to your organization. This allows your team to move away from a frantic “patch everything” approach and focus their limited time and resources on the threats that truly matter. This risk-based approach is the core of an efficient and effective vulnerability and threat prioritization program.
A robust data security platform does more than just check boxes; it becomes the central nervous system for your entire security strategy. By integrating various functions, it provides the clarity and control needed to move from a reactive to a proactive security posture. Instead of juggling dozens of disconnected tools, your team gets a single, coherent view of your environment. This allows you to identify genuine threats, meet compliance demands without the usual headache, and respond to incidents with speed and precision. It’s about transforming security from a constant fire drill into a well-managed, strategic operation that truly protects your most valuable asset: your data.
The best way to handle a security breach is to prevent it from ever happening. A data security platform shifts your focus from simply reacting to alerts to proactively reducing your exposure. It works by continuously identifying and assessing potential security gaps across your entire digital landscape. This approach, known as Continuous Threat Exposure Management, gives you a real-time understanding of where you’re vulnerable. By finding and addressing these weaknesses before an attacker can exploit them, you fundamentally strengthen your defenses and significantly lower the likelihood of a successful attack. It’s the difference between putting out fires and making your infrastructure fire-resistant in the first place.
Meeting compliance standards like GDPR, HIPAA, or PCI DSS can feel like a moving target. A data security platform helps you consistently meet these requirements by centralizing your security controls and data governance. It provides the visibility and documentation needed to demonstrate due diligence to auditors, showing exactly how you’re protecting sensitive information. Instead of scrambling to gather evidence from multiple systems, you have a single source of truth. This not only simplifies audits but also embeds compliance into your daily operations, making it a sustainable practice rather than a periodic scramble. Your team can focus on security, knowing compliance is an outcome of good practice, not a separate task.
Security teams often struggle with data overload from dozens of siloed tools, making it difficult to see the big picture. A data security platform cuts through the noise by consolidating information from across your environment into a single, unified view. This gives you a complete and accurate map of your entire attack surface, from on-premise servers to cloud assets and IoT devices. With this comprehensive visibility, you can easily spot hidden risks, understand how different assets are connected, and prioritize the threats that pose the greatest danger to your business. You can’t protect what you can’t see, and a unified platform ensures nothing slips through the cracks.
When your security tools are integrated into one platform, your team becomes more efficient and effective. You can eliminate the time wasted switching between different dashboards and correlating data manually. This streamlined workflow allows your team to focus on high-impact activities like threat hunting and strategic improvements. When a security incident does occur, having all the necessary context in one place enables a faster and more coordinated response. Your team can quickly understand the scope of the incident, contain the threat, and begin remediation, minimizing business disruption and reducing the overall impact of an attack.
Juggling dozens of security tools is exhausting. When your data is scattered across different dashboards, it’s nearly impossible to get a clear, accurate picture of your actual risk. You end up with blind spots, duplicated efforts, and a constant feeling that you’re one step behind. This is where a unified platform changes the game. Instead of patching together disparate systems, a comprehensive solution brings all your threat exposure data into one place, giving you a single source of truth.
The Hive Pro Uni5 Xposure Platform is designed to do exactly that. It’s a Continuous Threat Exposure Management (CTEM) platform that moves you from a reactive, vulnerability-focused mindset to a proactive, exposure-reduction strategy. Think of it as your command center for cybersecurity. It continuously scans your entire attack surface—from your cloud environments to your on-premise assets—to identify, prioritize, and validate your security posture. By integrating asset discovery, vulnerability prioritization, and security control validation, it provides a complete, end-to-end workflow. This unified approach helps you focus on the threats that pose a genuine risk to your business and gives you the actionable guidance you need to fix them efficiently.
Let’s be honest: you can’t protect what you can’t see. When your security team has to pull data from multiple scanners and spreadsheets, it’s easy for critical assets to fall through the cracks. A unified platform solves this by consolidating all your security data into a single, intuitive dashboard. This gives you a complete and continuous view of your entire attack surface, so you always know what assets you have and what vulnerabilities they carry. With Hive Pro, you can finally ditch the manual data correlation and get a clear, real-time understanding of your organization’s cyber risk without switching between a dozen different tools.
Not all vulnerabilities are created equal. A high CVSS score doesn’t automatically mean a vulnerability is your biggest problem. The real risk comes from vulnerabilities that are actively being exploited by attackers. That’s why intelligent vulnerability and threat prioritization is so critical. Hive Pro’s platform uses threat intelligence from our in-house HiveForce Labs to enrich your vulnerability data. This helps you see which threats are trending, which are tied to active ransomware campaigns, and which pose the most immediate danger to your specific environment. This allows your team to focus its time and resources on the fixes that will have the biggest impact on your security.
Having security controls in place is one thing, but knowing they’ll work during an actual attack is another. This is where Breach and Attack Simulation (BAS) comes in. Instead of waiting for a breach to find your weaknesses, you can proactively test your defenses against real-world attack scenarios. Hive Pro’s Adversarial Exposure Validation capabilities allow you to safely simulate attacks to see how your security stack holds up. This process helps you identify gaps in your defenses, validate that your configurations are working as intended, and prove the value of your security investments with concrete data. It’s about moving from assumptions to certainty.
The ultimate goal of any security program isn’t just to react to alerts—it’s to proactively reduce your overall threat exposure. A unified platform makes this possible by connecting the dots between asset discovery, vulnerability prioritization, and security validation. By seeing the full picture, you can make more strategic decisions that strengthen your security posture over time. The Uni5 Xposure Platform provides the tools and insights you need to build a resilient, proactive security program. It helps you shift from a constant cycle of firefighting to a continuous loop of discovery, prioritization, validation, and remediation, making your organization a much harder target for attackers.
Selecting an enterprise data security platform is a major decision that will shape your security posture for years to come. It’s not just about ticking off feature boxes; it’s about finding a solution that fits your unique environment, supports your team, and can grow with you. To make the right choice, you need to look past the marketing materials and focus on a few core capabilities that truly make a difference. Think about how a potential platform will integrate with your existing tools, whether it can handle your future growth, how it helps you focus on what matters, and what the true cost will be over time. Let’s walk through the key criteria to keep in mind during your evaluation.
Your security tools shouldn’t operate in isolation. A strong data security platform acts as a central hub, pulling in data from your existing stack—firewalls, endpoint detection, and cloud services—to give you a single source of truth. This prevents the visibility gaps where threats can hide. When evaluating options, ask how they connect with your current systems. Look for robust APIs and pre-built integrations that make this process smooth, not a months-long custom project. A platform that offers seamless integration creates a more resilient and responsive security posture, ensuring all your defenses are working together.
Your business isn’t static, and your security platform shouldn’t be either. As you add new assets, expand to the cloud, or grow your team, your platform needs to scale effortlessly. Can it handle a significant increase in data volume without slowing down? How easy is it to add new users or activate new features? A platform designed for growth will support your business goals instead of holding you back. You need a solution that can adapt to your evolving needs without requiring a complete overhaul every few years, ensuring your investment remains valuable long-term.
Finding vulnerabilities is only half the battle. The real challenge is knowing which ones to fix first. Drowning in a sea of alerts leads to burnout and inaction. Look for a platform that uses automation and threat intelligence to prioritize risks based on their real-world exploitability and potential business impact. This is where you move from a reactive checklist approach to a proactive, risk-based strategy. Effective vulnerability and threat prioritization means your team spends its time on the threats that actually matter, significantly reducing your overall exposure.
When you think about cost, look beyond the initial price tag. Consider the total cost of ownership, which includes implementation time, training for your team, and ongoing maintenance. A unified platform often proves more cost-effective than trying to stitch together multiple point solutions. Juggling different vendors and complex integrations can create security gaps and drive up hidden costs. A platform with a straightforward deployment process gets you to value faster and frees up your team to focus on security, not system administration. This approach simplifies your security stack and often leads to a lower overall investment.
When it comes to data security, what you don’t know can definitely hurt you. Misconceptions about how security platforms work can leave you with a false sense of security and significant gaps in your defenses. Let’s clear the air and bust a few common myths so you can make more informed decisions about protecting your organization’s most valuable assets.
It’s easy to think that once you’ve installed a data security platform, you can check a box and consider the job done. The reality is that effective security isn’t a one-and-done project; it’s an ongoing process. A platform is a powerful tool, but it needs continuous attention to be effective. Threats are constantly changing, and your environment is too. That’s why continuous threat exposure management is so critical. You need to actively manage, monitor, and update your security posture to adapt to new vulnerabilities and attack methods. Think of it as a security partnership, not just a purchase.
This is an outdated idea that doesn’t reflect how modern businesses operate. Your data is constantly moving—between servers, across networks, and on employee devices. A comprehensive data security platform is designed to protect data in all its states: at rest (in storage), in transit (moving across the network), and in use (being processed). Focusing only on data at rest is like locking the front door but leaving all the windows wide open. To truly secure your information, you need a solution that provides visibility and protection across your total attack surface, safeguarding data throughout its entire lifecycle.
Cybercriminals don’t discriminate based on company size. In fact, smaller businesses are often seen as easier targets because they may have fewer security resources. The idea that robust data security is only for large corporations is simply not true anymore. Modern SaaS platforms are designed to be scalable and affordable, making enterprise-grade security accessible to organizations of all sizes. Whether you’re a growing startup or a global enterprise, you face real threats. The right platform can provide the protection you need without the enterprise-level price tag or complexity.
Trying to manage compliance as a separate task from your daily security operations is a recipe for headaches and potential fines. The two are deeply intertwined. Regulatory requirements like GDPR, HIPAA, and PCI DSS are all about protecting sensitive data, which is the core function of a security platform. An effective platform integrates compliance management into its core, helping you automatically map your security controls to specific regulatory frameworks. This not only saves time but also ensures you can consistently prove compliance and avoid the risks of falling out of step with legal requirements.
Once your data security platform is up and running, how do you know it’s actually working? Proving the value of any security investment is key, not just for your budget but for your peace of mind. Moving beyond a gut feeling of being “more secure” requires a clear, data-driven approach. It’s about turning your security efforts into a story of tangible improvement, backed by solid numbers that resonate with everyone from your technical team to the board room.
Defining your key performance indicators (KPIs) before you even start is a critical step. What does success look like for your organization? Is it about patching vulnerabilities faster, reducing the overall number of critical alerts, or shortening the time it takes to detect and respond to an incident? The right platform will provide you with the dashboards and reporting tools to track these metrics effortlessly. This practice of using well-defined cybersecurity metrics is essential for quantifying your security posture, tracking progress, and allocating resources where they’ll have the most impact. This isn’t just about generating reports; it’s about gaining actionable insights that help you continuously refine your security strategy. By focusing on the right metrics, you can clearly communicate your team’s wins and justify continued investment in your security program.
The ultimate goal of a security platform is to make your organization a harder target. The most direct way to measure this is by tracking your overall threat exposure reduction. This isn’t just about the number of vulnerabilities you find; it’s about seeing a steady decrease in the critical risks across your entire attack surface. A platform that provides a unified view of cyber risks makes this easy to visualize. You can create a baseline of your exposure level and then report on the percentage of reduction month over month. This single metric powerfully demonstrates how your security program is shrinking the opportunities for an attacker and directly contributes to a stronger defense.
Finding vulnerabilities is only half the battle—fixing them is what counts. Measuring your vulnerability remediation rates gives you a clear picture of your team’s efficiency and effectiveness. Key metrics to watch are Mean Time to Remediate (MTTR) and the patch rate for critical vulnerabilities. Are you closing high-risk gaps faster than before? Is your team able to focus on what matters most? An effective platform helps you prioritize threats so your team isn’t wasting time on low-impact issues. Tracking these numbers helps you spot bottlenecks in your remediation process and shows a clear return on investment by demonstrating improved operational speed and risk reduction.
When a threat does emerge, every second matters. A successful platform should significantly shorten your incident response and detection times. You can measure this by tracking Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR). A lower MTTD shows that your platform is giving you the visibility needed to spot suspicious activity quickly. A lower MTTR indicates that your team has the context and tools to contain and neutralize threats before they can cause significant damage. By continuously testing your defenses through adversarial exposure validation, you can fine-tune your controls and processes, driving these critical time-based metrics down and proving your resilience.
How is a unified data security platform different from the collection of security tools I already use? Think of it as the difference between having a pile of car parts and a fully assembled car. Your individual tools—like your vulnerability scanner, firewall, and endpoint protection—are essential parts, but they don’t talk to each other. A unified platform connects all those pieces, giving you a single dashboard to see how a vulnerability on one asset could be exploited by a threat that your firewall is seeing. It eliminates the manual work of piecing together reports and gives you a complete, accurate picture of your actual risk.
My team already does vulnerability scanning. How does Breach and Attack Simulation (BAS) add to that? Vulnerability scanning is like checking all the doors and windows of your house to see if any are unlocked. It’s a crucial first step. Breach and Attack Simulation goes further by actually trying to open the unlocked doors and windows to see if your security system—like alarms or cameras—would catch the intruder. BAS safely mimics real-world attack techniques to test if your security controls are configured correctly and would actually work during an attack, helping you find and fix gaps before a real attacker does.
We have thousands of vulnerabilities. How does a platform help us decide what to fix first? This is a huge challenge for most teams. A smart platform moves you beyond just looking at a vulnerability’s severity score. It layers in threat intelligence to add critical context. It answers questions like, “Is this vulnerability being used by ransomware groups right now?” or “Is there an easy-to-use exploit kit available for this?” By highlighting the vulnerabilities that pose a clear and present danger, the platform helps your team focus its limited time and energy on fixing the problems that truly matter most.
Is a platform like this overkill for a smaller security team with limited resources? Actually, it’s often the opposite. For a smaller team, a unified platform acts as a force multiplier. It automates the tedious, time-consuming work of manually collecting data from different tools and trying to connect the dots. By centralizing information and automatically prioritizing the biggest risks, it allows a smaller team to be far more efficient and strategic. It helps you focus your limited resources on the actions that will have the biggest impact on your security.
How does this kind of platform help prove the value of our security program to leadership? A good platform translates your team’s technical work into a clear story of business value. Instead of just presenting a list of patched vulnerabilities, you can show a measurable reduction in your organization’s overall threat exposure over time. With clear dashboards and reporting, you can track metrics like how much faster you’re fixing critical issues and how your security posture is improving. This provides concrete data that demonstrates a tangible return on investment and justifies your security efforts in a language that leadership understands.