Comprehensive Threat Exposure Management Platform
Relying on weekly or monthly scans to secure your network is like trying to watch a movie by looking at a single photo every hour—you miss the entire plot. The gaps between those snapshots are where attackers find their opportunities. A lot can change in a day, let alone a week. This is why a fundamental shift in security strategy is necessary. It’s time to move from a reactive posture of cleaning up after a breach to a proactive one that stops trouble before it starts. This guide is about building that proactive foundation through continuous monitoring for cyber threats, giving you a live, uninterrupted view of your security posture and closing the dangerous gaps left by periodic assessments.
Think of continuous threat monitoring as a security camera for your entire digital environment that never blinks. It’s the practice of constantly observing your IT systems and networks to spot security threats automatically. Instead of checking in every once in a while, this approach gives you a live feed of what’s happening across your total attack surface. This allows your team to find vulnerabilities and react to potential threats the moment they appear, not days or weeks later after a scheduled scan. It’s about shifting from a reactive stance—cleaning up after a breach—to a proactive one where you can see and stop trouble before it starts. This constant vigilance is the foundation of a modern, resilient cybersecurity program.
So, how does this “always-on” monitoring actually function? Real-time detection works by continuously pulling in and analyzing data from every corner of your digital infrastructure—your servers, endpoints, cloud environments, and applications. This stream of information is automatically sifted through to spot anomalies, suspicious patterns, and known threat signatures. Think of it as an automated security analyst that never sleeps. It’s constantly looking for indicators of compromise and helps you identify vulnerabilities as they emerge. This immediate analysis means you get alerts right away, letting your team respond instantly and contain threats before they can cause significant damage.
The difference between continuous monitoring and periodic scans is like the difference between a live video feed and a single photograph. Periodic scans, which might run weekly or monthly, give you a snapshot of your security posture at that specific moment. The problem is, a lot can happen between those snapshots. New vulnerabilities can appear, and attackers can slip in undetected. Continuous monitoring, on the other hand, provides that live, uninterrupted view. It closes the gaps left by periodic scans, ensuring you’re aware of threats as they happen. This real-time insight is critical for maintaining an accurate picture of your security posture in a threat landscape that changes by the minute.
Shifting from periodic scans to continuous monitoring isn’t just a minor upgrade—it’s a fundamental change in how we approach security. Point-in-time assessments leave dangerous gaps where threats can slip through undetected. In the time between one scan and the next, a new vulnerability could be discovered and exploited, or an attacker could gain a foothold in your network. Continuous monitoring closes these gaps by providing a constant stream of information about your security posture. This allows your team to move from a reactive state, always playing catch-up, to a proactive one where you can identify and address issues before they become full-blown incidents. It’s about maintaining constant vigilance over your entire digital environment.
The threat landscape is anything but static. New vulnerabilities, attack techniques, and malware variants emerge daily. Relying on weekly or monthly scans is like trying to navigate a highway by only looking at the road every few miles. Continuous monitoring gives your team the real-time visibility needed to keep up. It allows you to detect cyber threats and vulnerabilities as they appear, which drastically shortens your response time. When you can spot an issue immediately, you can contain it quickly and prevent it from escalating into a major security incident. This constant awareness of your IT systems and networks is what enables an immediate and effective response when a potential threat is identified.
Let’s be direct: security breaches are expensive. The costs go far beyond immediate remediation efforts, encompassing regulatory fines, legal fees, customer notification expenses, and long-term reputational damage. Data shows that companies suffering a data breach often see their performance lag for years afterward. This is where continuous monitoring delivers a clear return on investment. By minimizing the time it takes to detect and respond to incidents, you can significantly reduce the potential damage and downtime. A proactive threat exposure management program, built on continuous monitoring, helps you focus on the risks that matter most, preventing the kinds of breaches that have a lasting negative impact on the bottom line.
For many organizations, meeting regulatory requirements is non-negotiable. Frameworks like HIPAA, PCI DSS, and GDPR have stringent security and data protection standards, and failing to meet them can result in hefty fines and legal trouble. Continuous monitoring is a cornerstone of a strong compliance program. It provides the evidence and assurance that you are actively managing your security risks in accordance with these mandates. By enabling you to detect and respond to threats in real time, it demonstrates a proactive approach to security that auditors and regulators want to see. This isn’t just about checking a box; it’s about maintaining a consistently strong security posture that is essential for compliance.
Effective continuous monitoring isn’t a single action but a combination of four key practices working in harmony. Think of them as the pillars that support your entire security posture. Each one gives you a different lens to view your environment, and when you bring them all together, you get a clear, comprehensive picture of your organization’s risk. This approach moves you from a reactive state of putting out fires to a proactive one where you can spot and address issues before they become full-blown crises.
You can’t protect what you can’t see. That’s why the first step is getting a complete and current map of your entire digital footprint. This includes everything from servers and laptops to cloud instances, IoT devices, and web applications. Continuous monitoring enhances visibility across your whole IT environment, allowing you to keep an eye on network security, user activity, and system logs. A comprehensive strategy for Total Attack Surface Management is foundational because it ensures there are no hidden corners where threats could be lurking. This complete inventory is the baseline for every other security activity you undertake.
Once you can see everything, the next step is to find the weaknesses. But simply running a scan and getting a list of thousands of CVEs isn’t helpful—it’s overwhelming. Continuous monitoring allows you to detect threats and vulnerabilities in real-time, which is crucial for a fast response. The key is to focus on what matters most. This means moving beyond CVSS scores and using threat intelligence to understand which vulnerabilities pose a genuine, immediate risk to your organization. Effective vulnerability and threat prioritization helps your team focus its limited time and resources on fixing the flaws that attackers are actively exploiting right now.
Not all threats come from the outside. Sometimes, the danger comes from a compromised account or a malicious insider. That’s why monitoring user behavior is so critical. The first step is understanding how your employees normally use your systems and data. From there, you can look for any strange changes in behavior that could signal a security threat. This could be anything from an employee in accounting suddenly trying to access engineering source code to someone logging in at 3 a.m. from a different continent. Spotting these anomalies early allows you to investigate and contain a potential breach before significant damage is done.
Data without context is just noise. Actionable threat intelligence is what turns raw security alerts into a clear roadmap for your team. When your monitoring tools generate an alert, threat intelligence can tell you if that activity is part of a known attacker’s campaign or if a specific vulnerability is being targeted in your industry. This real-world context, often curated by research teams like HiveForce Labs, enables your security teams to act promptly and decisively. Instead of chasing down every minor alert, you can focus on the events that are backed by credible, timely intelligence, making your incident response far more effective.
Think of threat intelligence as the brain of your continuous monitoring operation. It’s the difference between simply collecting data and actually understanding what it means. Without it, you’re just staring at a massive stream of alerts, trying to guess which ones matter. With it, you can cut through the noise and focus your energy on the threats that pose a genuine risk to your organization. This is how you shift from a reactive posture—constantly putting out fires—to a proactive one where you can anticipate and neutralize threats before they cause damage.
Integrating actionable threat intelligence into your monitoring strategy provides the crucial context you need to make informed decisions. It tells you what attackers are doing right now, what vulnerabilities they’re exploiting, and what tactics they’re using to bypass defenses. This real-world insight allows you to fine-tune your security controls, prioritize patching efforts, and give your security team a clear, manageable list of priorities. Instead of treating every alert with the same level of urgency, you can focus on the ones that are backed by intelligence indicating a credible threat. This approach is a core part of a modern Threat Exposure Management program, transforming security from a guessing game into a confident, data-driven practice.
Not all vulnerabilities are created equal. Your scanners might flag thousands of potential weaknesses, but only a small fraction of them are ever actively exploited by attackers in the wild. Threat intelligence helps you zero in on that critical fraction. By understanding which vulnerabilities are being weaponized, you can create a vulnerability and threat prioritization strategy that addresses the most immediate dangers first. This saves your team from wasting countless hours patching low-risk flaws that attackers are ignoring.
Continuous monitoring powered by threat intelligence allows you to detect these high-risk threats in real-time, which drastically improves your response time. When you get an alert for a vulnerability that you know is being used in active campaigns, you can contain the issue quickly and prevent it from escalating into a full-blown breach.
Focusing on exploited vulnerabilities is a great start, but truly effective monitoring requires understanding the attacker’s entire playbook. Threat intelligence gives you insight into the specific tactics, techniques, and procedures (TTPs) that threat actors use. This includes everything from their initial reconnaissance methods and phishing campaigns to how they move laterally within a network and exfiltrate data. You can find detailed breakdowns of these methods in regular threat advisories.
By aligning your monitoring with known attacker TTPs, you can spot malicious activity that might otherwise look like normal user behavior. This helps you detect threats earlier in the attack lifecycle, often before a vulnerability is even exploited. Understanding how attackers operate allows you to anticipate their next move and strengthen your defenses accordingly.
An alert that just says “suspicious login detected” isn’t very helpful. An alert that says “suspicious login detected from an IP address associated with the FIN7 hacking group, which is currently targeting financial institutions with ransomware,” is something you can act on immediately. This is the power of adding real-world context to your security alerts. Threat intelligence from research teams like HiveForce Labs enriches raw security data with crucial details.
This context tells you who the attacker might be, what their motivations are, and which industries they typically target. This information turns a vague alert into a clear, actionable insight. It enables your security team to act promptly and decisively, and it also helps you communicate the real-world risk to leadership in a way they can understand.
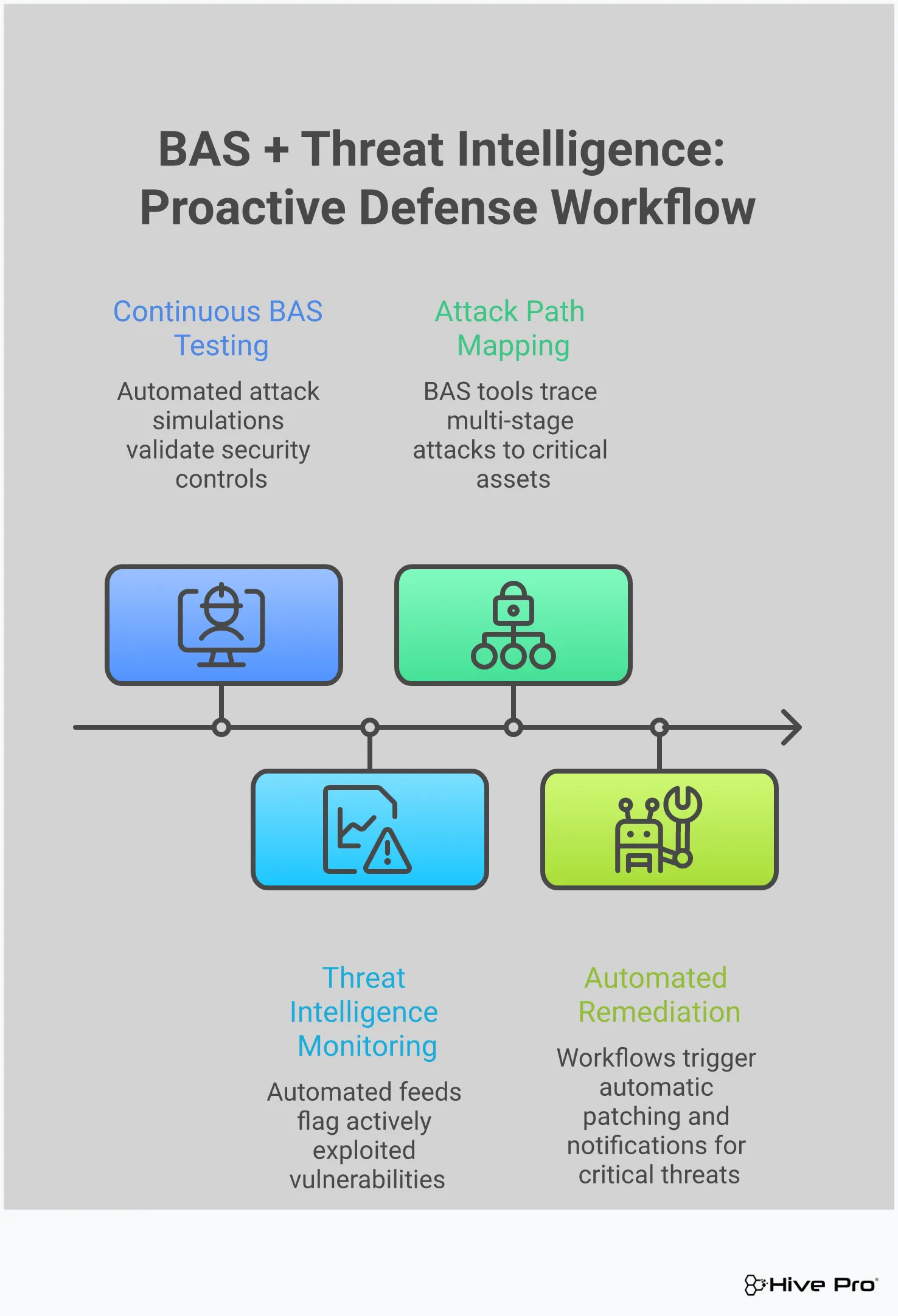
Instead of just waiting for alerts, what if you could safely test your defenses against the latest attack methods? That’s the core idea behind Breach and Attack Simulation (BAS). It’s a proactive approach that moves you from a defensive posture to an offensive one, letting you see your environment through an attacker’s eyes. BAS platforms continuously and automatically run simulated attacks against your security controls to see how they hold up against real-world threats.
This isn’t just about finding individual vulnerabilities; it’s about testing the entire system—your people, processes, and technology. Think of it as a continuous, automated penetration test that doesn’t disrupt your operations. By simulating real-world attack scenarios, you can validate that your security tools are configured correctly, your detection mechanisms are working, and your response team is ready to act. This process of adversarial exposure validation provides hard data on your security posture, replacing assumptions with evidence. It answers the critical question: “If we were attacked today with this specific technique, would we be able to stop it?”
Your security stack is complex, with firewalls, EDRs, and SIEMs all meant to work together. But are they? A simple misconfiguration or a missed update can create a gap an attacker could slip through. BAS helps you continuously validate that these controls are performing as expected. By running simulations based on known threat behaviors, like those outlined in the MITRE ATT\&CK framework, you can get immediate feedback on your defenses.
Instead of waiting for an annual audit or a real incident to find a weakness, BAS provides an ongoing assessment. It confirms that your security tools are not only deployed but are also effective against the tactics and techniques used by today’s adversaries. This constant testing ensures your security posture remains strong over time.
An incident response plan that only exists in a document is just a theory. BAS gives you a safe way to put that theory into practice. By launching controlled, simulated attacks, you can trigger your entire incident response workflow from start to finish. This allows you to see exactly how your team and tools perform under pressure, without the risk of a real breach.
These simulations act as realistic fire drills for your security team. You can identify where communication breaks down, where processes are slow, or where your technology fails to provide the necessary visibility. Continuous monitoring provides the real-time insights needed for an immediate response, and BAS ensures your team knows how to use those insights effectively. It’s the best way to refine your plan and build muscle memory for a real event.
Attackers don’t just exploit a single vulnerability; they chain them together to move through your network. BAS helps you identify these potential attack paths before a real adversary does. By simulating multi-stage attacks that mimic real-world campaigns, you can uncover hidden weaknesses and blind spots in your defenses. This gives you a complete picture of your total attack surface and how it could be compromised.
This proactive approach allows you to see where your visibility is lacking or where a specific control might fail to stop an attacker’s lateral movement. Detecting these gaps in real-time drastically improves your ability to contain a security incident and prevent it from escalating. By combining different security assessment methods, you can build a much more resilient and comprehensive defense strategy.
Having the right strategy is one thing, but you need the right tools to execute it. A solid continuous monitoring program relies on a few key technologies working together. Think of these as the foundational pieces of your security toolkit, each playing a distinct but complementary role in keeping your organization safe. From gathering intelligence and spotting anomalies to automating your response, the right combination of platforms can make all the difference. This isn’t about buying every shiny new tool on the market; it’s about creating a cohesive, integrated system where each component strengthens the others.
Your goal is to build a tech stack that gives your team the visibility to see everything, the intelligence to prioritize what matters, and the automation to act quickly. When these tools are integrated properly, they eliminate manual work, reduce alert fatigue, and give your security team the context they need to make confident, data-driven decisions. A well-designed toolkit breaks down data silos between teams, ensuring that everyone from IT operations to the security operations center (SOC) is working from the same information. This unified approach is what transforms continuous monitoring from a passive, alert-generating activity into an active, risk-reducing function. Below, we’ll look at three essential categories of tools that form the backbone of a modern continuous monitoring strategy.
Think of a Continuous Threat Exposure Management (CTEM) platform as the command center for your security program. It moves you beyond simply listing vulnerabilities and helps you understand your actual exposure to threats. These platforms consolidate data from various sources to give you a unified view of your attack surface, manage and validate threats, and provide a clear path for remediation. By focusing on what attackers are actively exploiting, CTEM helps you make smarter decisions and quickly reduce risk. This approach transforms your security posture from reactive to proactive, ensuring your team is always working on the fixes that matter most.
A SIEM is your organization’s central logbook. These solutions are essential for continuous monitoring because they collect, aggregate, and analyze security data from across your entire IT environment in real time. From network devices and servers to applications, a SIEM gathers event logs to give you a comprehensive view of what’s happening. This allows your team to spot anomalies, investigate potential security incidents, and respond to threats as they emerge. While a SIEM is powerful for data collection and real-time alerting, its true value is realized when integrated with other tools that provide deeper context on which alerts represent the most significant risk.
If a SIEM is your alarm system, a SOAR platform is the automated response team. These tools connect to your other security solutions to streamline workflows and automate your incident response. When an alert comes in, a SOAR platform can automatically perform initial investigation steps, enrich the alert with threat intelligence, and even execute containment actions like blocking an IP address. By automating these repetitive, time-consuming tasks, you free up your security analysts to focus their expertise on investigating and resolving more complex threats. This automation is crucial for keeping up with the high volume of alerts generated by a continuous monitoring strategy.
Setting up a continuous monitoring program is a huge step forward for any security team, but it’s not always a smooth ride. Even the most well-designed strategies can run into common roadblocks that can slow progress and frustrate your team. The good news is that these challenges are well-understood, and with the right approach, you can overcome them. The key is to anticipate these issues and build your strategy around smart, efficient solutions that help your team work more effectively, not just harder.
From drowning in a sea of alerts to struggling with a patchwork of security tools, these hurdles can make a proactive security posture feel out of reach. Let’s walk through some of the most frequent challenges and discuss practical ways to solve them.
When you first turn on continuous monitoring, the sheer volume of alerts can be overwhelming. Your security tools are doing their job by flagging every potential anomaly, but this often creates a constant stream of notifications. Soon, your team is spending more time sifting through alerts than investigating actual threats. This is alert fatigue, and it’s a serious problem. When analysts are bombarded with low-level or false-positive alerts, they can become desensitized and may overlook a critical notification that signals a real attack.
The solution isn’t to turn the monitoring down; it’s to turn the intelligence up. Instead of looking at every single alert, you need a way to prioritize exposure based on genuine risk. This means using a system that adds context, correlating data from multiple sources to distinguish a minor issue from an imminent threat.
Most organizations don’t have the luxury of building their security stack from scratch. You likely have a mix of cloud services, on-premise servers, legacy applications, and various security tools that have been added over the years. Getting these disparate systems to communicate and share data is a major challenge. Without proper integration, you’re left with blind spots and data silos, forcing your team to manually piece together information from different dashboards. This fragmented view makes it nearly impossible to get a clear picture of your true attack surface.
To solve this, you need a central platform that can ingest and normalize data from all your existing tools. A unified view of cyber risks allows you to see everything in one place, creating a single source of truth for your security posture. This approach doesn’t require you to rip and replace your current tools. Instead, it connects them, making the whole security ecosystem more effective.
Effective continuous monitoring requires both technology and talent. The reality is that there’s a significant cybersecurity skills gap, and finding experienced security professionals is difficult and expensive. Even with the right team, managing a 24/7 monitoring program can be a major drain on time and resources. Your team needs to not only run the tools but also analyze the findings, investigate incidents, and coordinate remediation efforts across different departments. This can quickly lead to burnout and high turnover if not managed properly.
The best way to address this is by empowering the team you have with tools that automate routine tasks and provide clear, actionable guidance. By automating data collection, correlation, and prioritization, you free up your analysts to focus on high-impact activities like threat hunting and incident response. A platform that provides guided remediation steps also reduces the burden on your team, allowing them to resolve issues faster without needing to be an expert in every single system.
Putting a continuous monitoring strategy into practice is more than just deploying a new tool. It’s about creating a sustainable program that aligns with your business goals and empowers your security team. A successful strategy doesn’t happen by accident; it’s built on a clear understanding of your environment, smart automation, and a commitment to continuous improvement. By following a structured approach, you can move from a reactive security posture to a proactive one, confidently addressing threats before they cause real damage. Let’s walk through the three essential steps to build a strategy that works for your organization.
Before you can effectively monitor your environment, you need to know what you’re protecting and why. Start by mapping out your entire digital footprint to get a clear picture of your total attack surface. From there, work with business leaders to identify which systems and data are most critical to your operations. Is it your customer database? Your payment processing system? Your intellectual property? As security experts at Bitsight note, “Identifying which information and computer systems are most important for your business is crucial.” This step ensures your monitoring efforts are concentrated where they matter most, so your team can focus its energy on protecting the assets that are truly vital.
A constant stream of alerts without a plan for action is just noise. The real power of continuous monitoring comes from using it to trigger immediate, automated responses. Set up your systems to send alerts directly to the right IT teams when an issue pops up. Better yet, use security orchestration and automation tools to resolve common problems without any human intervention. For example, an alert for a known vulnerability on a non-critical server could automatically trigger a patching workflow. This not only ensures a faster response but also frees up your security analysts to focus on more complex threats, turning your monitoring system into an active defense mechanism.
Your tools are only as effective as the people and processes behind them. It’s essential to establish clear objectives from the start. What are you trying to detect—security threats, performance issues, or both? Define what success looks like and use a unified platform to track your progress with clear metrics. Regularly check in with your teams to see if the monitoring solutions are actually helping them do their jobs better. This feedback loop is critical for refining your strategy and ensuring your tools remain effective. By empowering your team and measuring success against clear goals, you create a culture of continuous improvement that strengthens your security posture over time.
My team is already overwhelmed with alerts. Won’t continuous monitoring just make this worse? That’s a completely valid concern, and it’s one of the biggest misconceptions about this approach. The goal of smart continuous monitoring isn’t to create more alerts, but to generate the right ones. By integrating threat intelligence, the system learns to distinguish between minor anomalies and genuine threats. This allows you to prioritize what needs immediate attention, effectively turning a flood of notifications into a clear, manageable to-do list for your team.
How is Breach and Attack Simulation (BAS) different from a traditional penetration test? Think of it as the difference between an annual physical and a 24/7 heart rate monitor. A penetration test is a deep, manual assessment that happens at a single point in time, giving you a snapshot of your defenses. Breach and Attack Simulation, on the other hand, is an automated and continuous process. It constantly runs safe, simulated attacks against your security controls to ensure they’re working correctly day in and day out, providing constant validation instead of a once-a-year report.
Do I need to replace my existing security tools like my SIEM or vulnerability scanner to adopt this approach? Not at all. A strong continuous monitoring strategy, often managed through a Threat Exposure Management platform, is designed to integrate with the tools you already have. It acts as a central intelligence layer, pulling data from your SIEM, scanners, and other sources. It then enriches that data with context, helping you get more value out of your existing investments by showing you which information from those tools matters most.
How can I justify the shift from periodic scans to my leadership? Focus on the language of risk and time. Periodic scans leave dangerous gaps in visibility—sometimes for weeks or months—where an attacker can get in undetected. Continuous monitoring closes those gaps. You can frame it as moving from a reactive model, where you’re cleaning up after a costly breach, to a proactive one where you can stop incidents before they happen. It’s about reducing the window of opportunity for attackers and, in turn, reducing the financial and reputational risk to the business.
What’s the real difference between finding a vulnerability and understanding my exposure? Finding a vulnerability is like knowing there’s a crack in a window. Understanding your exposure is knowing that the window is on the ground floor, it’s unlocked, and there’s a well-known group of burglars targeting houses on your street. A vulnerability is just a technical flaw. Exposure is the actual, real-world risk that flaw poses to your organization, taking into account its location, its exploitability, and the current threat landscape.