Actors, Threats and Vulnerabilities 13 February to 19 February 2023
For a detailed threat digest, download the pdf file here
Summary
For a detailed threat digest, download the pdf file here
HiveForce Labs identified seven active actors over the past week. There were three prominent Russian actors, namely TA505, Nodaria, and KillNet. Additionally, three Chinese actors, Tonto Team, DEV-0147, and Dalbit, were also identified. It should be noted that Red Eyes is a threat actor from North Korea. For more information, please refer to the key takeaway section on Actors.
Last week, five new active malware strains were identified. Three of these were ransomware: Clop Ransomware, DarkBit ransomware, and MortalKombat ransomware. Additionally, a ProxyShellMiner was discovered exploiting Microsoft Exchange Server vulnerabilities. Another new malware found was GlobeImposter. For more information, please refer to the key takeaway section on Attacks.
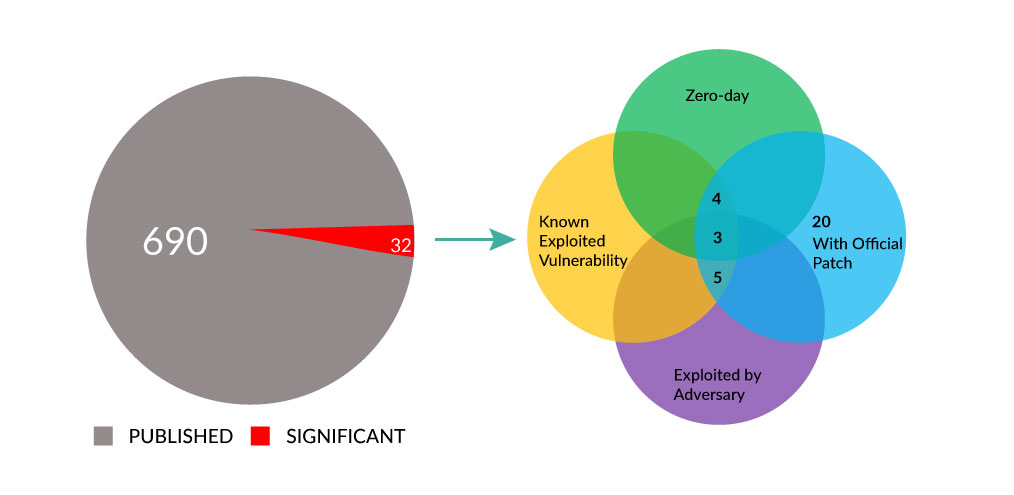
Last week, we found a total of 32 vulnerabilities that organizations should prioritize. Specifically, Apple had three vulnerabilities addressed, Microsoft had 17 vulnerabilities addressed, and Citrix had four flaws identified. Additionally, there were seven zero-day vulnerabilities that were actively exploited last week. For more information, please refer to the key takeaway section on vulnerabilities.



