Comprehensive Threat Exposure Management Platform
If your vulnerability backlog feels like an endless to-do list, you’re not alone. Security teams are often buried under a mountain of alerts, with constant pressure to patch every “critical” flaw immediately. But the truth is, not all critical vulnerabilities are created equal. A high-severity flaw on an isolated test server is far less urgent than a medium-severity one on your primary customer database. This is where the noise of traditional vulnerability management can lead to wasted effort and burnout. True progress comes from clarity, not volume. By implementing risk scoring in vulnerability management, you can cut through the chaos and create a focused, prioritized list based on what actually poses a threat to your business.
Let’s start with the basics. Vulnerability risk scoring is a way to quantify the real-world danger a specific vulnerability poses to your organization. Instead of just having a long list of security weaknesses, you assign each one a numerical score. This score isn’t arbitrary; it’s calculated based on a mix of factors like how easy it is for an attacker to exploit the vulnerability, what kind of damage they could do, and how important the affected system is to your business.
Think of it as a threat rating system tailored specifically for your environment. It helps you move from a reactive state of patching everything that looks scary to a proactive strategy focused on what’s actually dangerous. The core idea is to create a clear, consistent method for measuring risk across your entire attack surface. This gives you a data-driven way to compare a vulnerability in your web server against one in your internal database, allowing you to see which one truly needs your attention first. It’s about adding context to the chaos and making sense of the thousands of alerts your team faces every day.
In cybersecurity, we often have to make tough calls with limited resources. Risk scoring is essential because it helps you shift from making educated guesses to making decisions based on solid data. It provides clear, measurable information about your most significant threats, which is exactly what you need to justify where you spend your time, budget, and effort. When you can show leadership a high-risk score tied to a critical business function, the conversation about remediation resources becomes much simpler.
This data-driven approach creates a common language for everyone involved, from the security operations team to the C-suite. It helps translate technical vulnerabilities into tangible business risks that everyone can understand. A robust threat exposure management platform uses risk scoring to provide a unified view of these risks, ensuring that your security efforts are always aligned with your organization’s most important goals. It’s about making smarter, more defensible decisions that genuinely reduce your overall risk.
If your team is still prioritizing vulnerabilities based only on CVSS scores, you’re likely wasting valuable time. While CVSS is a decent starting point for assessing severity, it lacks critical business context. A vulnerability with a “critical” CVSS score on a development server is far less urgent than a “medium” one on your customer-facing payment portal. This is where risk scoring completely changes the game.
Risk-based vulnerability and threat prioritization adds layers of context that CVSS alone can’t provide. It considers the criticality of the asset, whether the vulnerability is being actively exploited in the wild, and what security controls you already have in place. This transforms your endless backlog of vulnerabilities into a focused, actionable to-do list. Instead of chasing every high-severity alert, your team can concentrate on fixing the flaws that pose a clear and present danger to your business.
At its core, calculating a vulnerability risk score isn’t about complex, abstract algorithms. It’s about applying practical math to real-world data to answer a simple question: “How much should I worry about this?” The goal is to create a consistent, data-driven number that helps you sort through the noise and focus on what truly matters.
Think of it as a credit score for your vulnerabilities. A higher score signals a bigger risk that demands your immediate attention, while a lower score can probably wait. This scoring process combines the inherent danger of a vulnerability with the current likelihood of it being used against you. By turning abstract threats into concrete numbers, you can build a much more efficient approach to vulnerability and threat prioritization. It’s the first step in moving from a reactive, “patch everything” mindset to a proactive, risk-based strategy.
So, how does the calculation actually work? It’s usually a weighted formula that balances a few key factors. Imagine you’re blending two main ingredients: the severity of the vulnerability and the existence of a known exploit. Each ingredient is given a certain weight based on its importance. The formula then combines these weighted scores to produce a final risk score. This ensures that a highly severe vulnerability with no known exploit might score lower than a moderately severe one that attackers are actively using. Some models produce a score on a simple scale, while others use a multi-faceted approach with a wider range, like 0 to 1000. This allows for more nuance, factoring in not just severity and exploitability but also other metrics. The specific math can vary, but the principle is always the same: it’s a logical way to quantify risk.
The math is only as good as the data you feed it. A reliable risk score is built on a foundation of timely and accurate information. It starts with foundational metrics like the Common Vulnerability Scoring System (CVSS), which provides a standardized way to rate the technical severity of a flaw. But that’s just the beginning. To get a true picture of risk, you need to layer in real-time threat intelligence. This includes data from threat feeds that tell you if a vulnerability has a known public exploit or if it’s part of an active attack campaign. This process of risk profiling and scoring assigns a score based on likelihood and potential impact, giving you a much clearer, more contextual understanding of your exposure.
A truly effective vulnerability risk score is much more than a single, static number. Think of it as a dynamic profile that pulls together different data points to paint a realistic picture of the threat a vulnerability poses to your organization. A high score on paper doesn’t always mean it’s your biggest problem, and a low score doesn’t mean you can ignore it. To accurately prioritize your remediation efforts, you need to look at the complete context. The most robust scoring models consider a blend of universal severity metrics, the specific value of the affected asset, your unique environmental conditions, and real-time threat intelligence.
The Common Vulnerability Scoring System (CVSS) is the industry-standard starting point for assessing a vulnerability. It provides a numerical score from 0 to 10, giving you a universal baseline for how severe a flaw is in a general sense. This score helps you quickly sort vulnerabilities into categories like Critical, High, Medium, or Low.
While CVSS is an essential first step, it’s important to remember that it measures potential severity, not immediate risk to your business. It tells you how bad a vulnerability could be if exploited under ideal conditions, but it doesn’t know anything about your specific environment or whether attackers are actively using it. Use the CVSS score as your initial filter, but don’t let it be your only one.
Not all assets are created equal. A critical vulnerability on a developer’s test machine is a problem, but that same vulnerability on your primary customer database is a potential catastrophe. This is where business context comes in. To calculate a meaningful risk score, you must factor in the value of the asset the vulnerability affects.
Start by identifying your organization’s crown jewels: the servers, applications, and data stores that are essential for your operations. A true risk score weighs the technical severity of a flaw against the business impact of a compromise. By understanding your total attack surface, you can ensure that vulnerabilities on your most critical assets get the immediate attention they deserve, regardless of their CVSS score.
Your specific IT environment plays a huge role in determining a vulnerability’s actual risk. A high-severity vulnerability might be present, but if it’s on an internal, air-gapped system with no connection to the outside world, the immediate risk is low. Conversely, a medium-severity flaw on a public-facing web server that lacks proper security controls could be a ticking time bomb.
Consider these environmental questions: Is the asset exposed to the internet? Are there compensating controls, like a web application firewall (WAF) or access restrictions, that reduce the likelihood of an exploit? An accurate risk score must account for these unique conditions. Without this environmental context, you’re simply guessing at which vulnerabilities pose a clear and present danger.
This is the factor that separates proactive security from reactive cleanup. Real-time threat intelligence answers the most important question: Are attackers actively exploiting this vulnerability in the wild? A flaw might have a perfect 10.0 CVSS score, but if no one has developed a working exploit for it, it may be less of an immediate priority than a lower-scored vulnerability that is part of an active ransomware campaign.
This is where data from sources like the Exploit Prediction Scoring System (EPSS) becomes invaluable. By integrating threat advisories and intelligence on weaponized exploits, you can focus your team’s efforts on the vulnerabilities that attackers are using right now. This intelligence-driven approach allows you to fix the most likely points of attack first, significantly reducing your exposure.
You don’t have to reinvent the wheel when calculating risk. Several established methodologies provide a solid foundation for your vulnerability management program. Each framework offers a different lens for viewing risk, from static severity scores to predictive models. Understanding these common approaches is the first step toward building a risk scoring model that truly reflects your organization’s unique threat landscape. A hybrid approach often yields the most accurate and actionable insights.
The Common Vulnerability Scoring System (CVSS) is a widely used standard for rating vulnerability severity. It assigns a score from 0 to 10 based on a vulnerability’s core characteristics, like its exploitability and potential impact. While CVSS is an excellent starting point for understanding intrinsic severity, it’s a static score. It tells you how bad a vulnerability could be in a vacuum, but not how bad it is for your specific environment or in light of current threats.
Where CVSS is static, the Exploit Prediction Scoring System (EPSS) is predictive. It answers a critical question: What is the probability this vulnerability will be exploited in the wild? By analyzing real-world exploit data, EPSS generates a probability score from 0% to 100%. This forward-looking approach helps your team cut through the noise of high CVSS scores and focus resources on the vulnerabilities threat actors are most likely to target, making your remediation efforts far more efficient.
For a more structured approach, many organizations use the NIST SP 800-30 Risk Assessment Framework. This guide provides a systematic process for managing risk across the organization. It walks you through identifying threats and vulnerabilities, determining their likelihood and impact, and deciding on the right course of action. It’s less of a simple scoring system and more of a complete methodology for understanding how technical vulnerabilities translate into tangible business risk, considering your specific assets and objectives.
If you need to communicate risk in financial terms, the Factor Analysis of Information Risk (FAIR) framework is your best tool. FAIR is a quantitative model that helps you measure information risk in dollars and cents. It breaks down risk into measurable factors, like threat event frequency and probable loss magnitude. This allows you to move beyond qualitative labels like ‘high’ or ‘medium’ risk and have data-driven conversations with business leaders about the potential financial impact of a security incident, helping justify security investments.
A vulnerability’s CVSS score gives you a solid, standardized starting point. It tells you the potential severity if an attacker were to exploit it. But here’s the catch: it doesn’t tell you the likelihood of that happening. It exists in a vacuum, without the context of what’s happening in the real world. This is where threat intelligence comes in. It adds the dynamic, real-time context you need to understand which vulnerabilities pose an immediate threat to your organization.
By layering threat intelligence over your vulnerability data, you shift from a static, theoretical view of risk to a proactive and predictive one. Instead of just knowing what could happen, you gain insight into what attackers are doing right now. This intelligence helps you see which vulnerabilities are being actively exploited, which are part of a trending threat campaign, and which have been weaponized for widespread use. This approach transforms your vulnerability and threat prioritization process, allowing you to focus your team’s limited time and resources on the threats that truly matter.
Think of all the vulnerabilities in your environment. Now, which ones have known, public exploits? Which of those are being used by attackers today? Answering these questions is the first step in sharpening your risk scores. Threat intelligence provides this crucial data, allowing you to see which theoretical risks have become practical realities. By combining a vulnerability’s severity score (like CVSS) with data on its real-world exploitation, like the Exploit Prediction Scoring System (EPSS), you get a much clearer picture of its true risk. This allows you to prioritize vulnerabilities that are not only severe but are also proven to be exploitable and are actively being targeted.
Knowing a vulnerability is being exploited is good. Knowing it’s being exploited by a threat actor who targets your industry is even better. High-quality threat intelligence connects vulnerabilities to specific threat campaigns and adversary groups. For example, if a ransomware group known for attacking healthcare institutions is actively using a certain exploit, any hospital with that vulnerability needs to treat it as a critical priority. This correlation allows you to be more proactive. Instead of reacting to a breach, you can anticipate an attacker’s next move by following the latest threat advisories and patching the vulnerabilities they are currently using.
A weaponized vulnerability is one for which a reliable exploit has been developed, packaged, and is readily available for attackers to use. It’s the difference between a blueprint for a weapon and a loaded gun. Threat intelligence helps you identify these weaponized threats, which often appear in exploit kits or are used in widespread automated attacks. When you combine this intelligence with your business context, you can determine the true risk to your organization. A weaponized vulnerability in a public-facing, business-critical application represents a far greater risk than a theoretical vulnerability on an isolated internal server, helping you allocate resources with precision.
A vulnerability risk score gives you a solid, data-driven starting point, but it’s still a theoretical number. It tells you how risky a vulnerability could be, not necessarily how risky it is in your specific environment. Factors like your existing security stack, network segmentation, and compensating controls can dramatically alter a vulnerability’s real-world impact. Relying solely on scores can lead to chasing ghosts, where your team spends valuable time patching vulnerabilities that pose little actual threat. This is where you need to move from theory to practice. How do you confirm that a high-risk vulnerability is actually exploitable and that your security controls will perform as expected?
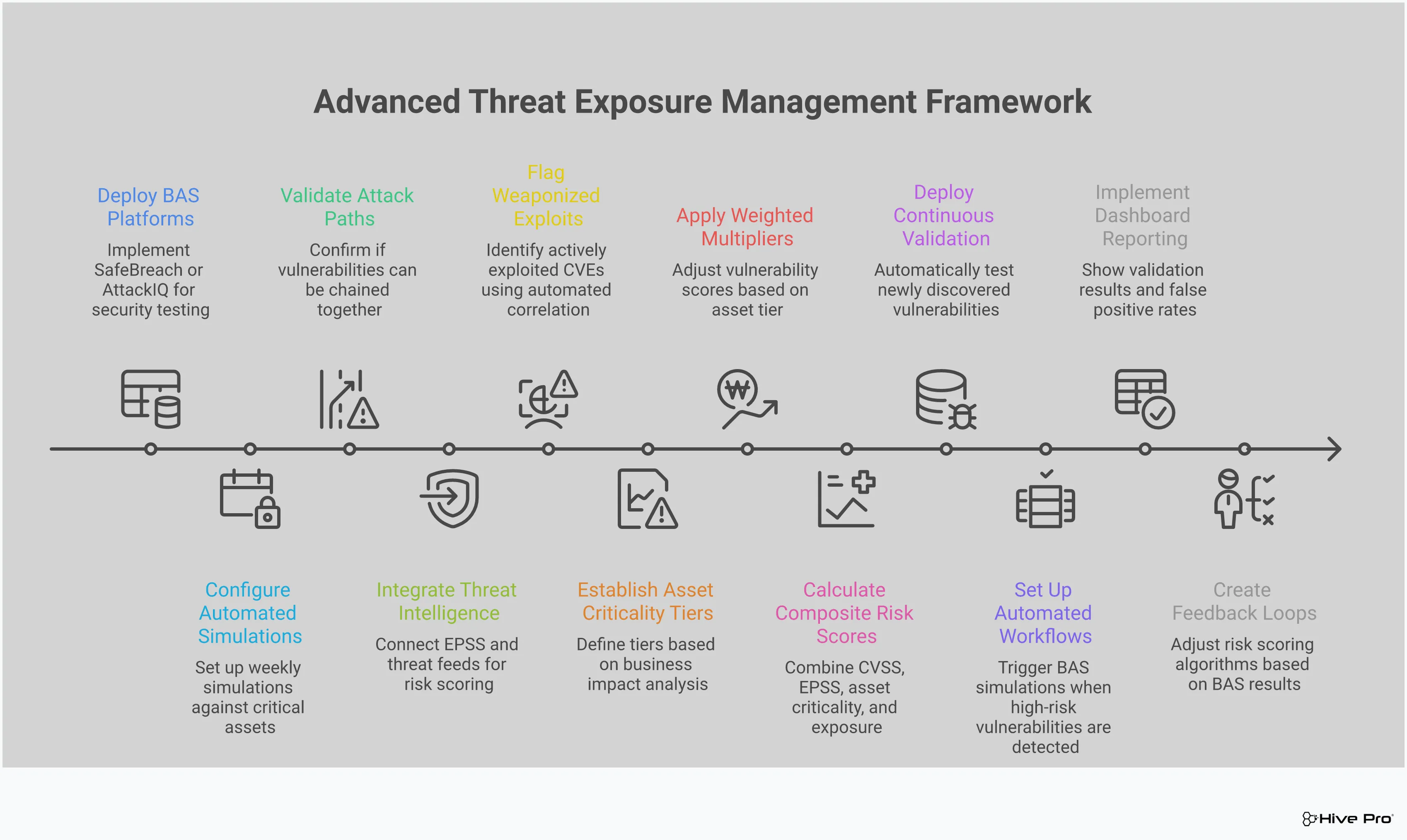
This is the job of Breach and Attack Simulation (BAS). BAS platforms act as a sparring partner for your security posture, safely emulating the tactics and techniques real attackers use. Instead of just trusting a score, you can actively test your defenses against simulated attacks. This process provides concrete evidence of your true exposure, validating which scores demand immediate attention and which ones are mitigated by your existing controls. By integrating adversarial exposure validation, you can transform your vulnerability management program from a reactive, score-chasing exercise into a proactive, evidence-based strategy that focuses on what truly matters.
A high risk score on paper doesn’t always translate to a genuine threat. Your unique security stack, configurations, and compensating controls might render a critical vulnerability non-exploitable. Breach and Attack Simulation helps you find out for sure. By emulating the behavior of real-world threat actors, BAS moves beyond single vulnerabilities to test entire attack paths. This allows you to see exactly how an attacker could chain together different weaknesses to breach your defenses. The simulation results provide clear proof of which theoretical risks are practically exploitable in your environment. This context is crucial for focusing your team’s efforts on the vulnerabilities that pose a clear and present danger.
Your IT environment is constantly changing. New assets come online, software gets updated, and configurations are tweaked. A risk score that was accurate last week might be outdated today. This is why periodic assessments like annual penetration tests are no longer enough. BAS provides the continuous validation needed to keep pace with this dynamic landscape. By running automated attack simulations regularly, you get a near real-time view of your security posture. This ongoing testing ensures your risk scores always reflect your current state of exposure. As your environment evolves, the Uni5 Xposure platform can continuously validate your defenses, helping you maintain an accurate understanding of your risk and ensuring your prioritization efforts remain effective over time.
The ultimate goal of BAS is to close the gap between your perceived security and your actual security. When a simulated attack succeeds, it pinpoints exactly which security controls failed and why. This gives you a clear, actionable roadmap for remediation that is based on proven weaknesses, not just theoretical risk. The results from BAS tests show you where your calculated risk scores might be misleading. For example, a vulnerability with a medium score could become part of a critical attack path if a key security control fails. By identifying these gaps, you can allocate your resources more effectively, directing your team to fix the issues that have the greatest impact on your real-world resilience.
Adopting a risk-scoring model isn’t just about adding another number to your dashboard. It’s about fundamentally changing how your team approaches vulnerability management. By moving beyond basic severity ratings, you gain a clear, contextualized view of your threat landscape. This clarity allows you to shift from a reactive, volume-based patching cycle to a proactive, risk-based strategy. The result is a more efficient, effective, and resilient security program that protects what matters most to your organization. This approach brings several key benefits that directly impact your team’s daily operations and your company’s overall security posture.
Your security team has a finite amount of time and energy. Risk scoring acts as a powerful filter, ensuring those limited resources are spent on the threats that pose a genuine danger to your business. Instead of trying to patch every single vulnerability with a high CVSS score, your team can concentrate on the much smaller subset of flaws that are actually exploitable and target your critical assets. This targeted approach cuts through the noise of thousands of alerts, allowing you to address the 2-5% of vulnerabilities that truly matter. With a clear vulnerability and threat prioritization system, you can stop chasing ghosts and start neutralizing real threats, maximizing the impact of every action your team takes.
When you have a risk score that blends technical severity with business context and real-time threat intelligence, decision-making becomes much simpler and faster. You no longer have to spend hours debating whether a vulnerability on a non-critical server is more important than a lower-severity flaw on a mission-critical database. The risk score provides a data-driven answer. This empowers your team to act with confidence and speed. It also makes it easier to communicate risk to leadership and other stakeholders in a way they can understand, justifying resource allocation and demonstrating the value of your security efforts with clear, quantifiable data from intelligence sources like HiveForce Labs.
A direct outcome of better focus and faster decisions is a significant reduction in your Mean Time to Remediation (MTTR). When your remediation workflow starts with a clearly prioritized list, the entire process accelerates. Your team can immediately get to work on the most critical fixes without getting bogged down in analysis paralysis. A risk-based vulnerability management platform ingests data from all your scanners, correlates it with threat intelligence, and can even automate remediation workflows. By streamlining the path from detection to resolution, you shrink the window of opportunity for attackers and measurably improve your security effectiveness with a unified platform like Uni5 Xposure.
Adopting a risk-based approach is a game-changer for any vulnerability management program. But let’s be real, it’s not as simple as flipping a switch. Getting your risk scoring framework off the ground comes with its own set of hurdles. You’ll need to wrangle your data into shape, fine-tune your scoring for accuracy, and make sure your team has the bandwidth and skills to manage it all. Let’s walk through some of the most common challenges you’ll likely encounter and how you can prepare to tackle them head-on.
Your risk score is only as reliable as the data feeding it. If you’re working with incomplete or inaccurate information, your prioritization efforts will miss the mark. Many organizations struggle with outdated scanning methods and incomplete asset visibility, leading to overwhelming data volumes that obscure true risk. You can’t protect what you don’t know you have. Creating a total attack surface management strategy is the foundational step, but it’s often the most difficult. Pulling together a complete picture means integrating data from a dozen different tools, from your CMDB to cloud environment monitors, to get a single, reliable source of truth.
Once your data is in order, the next challenge is ensuring your risk scores accurately reflect reality. If your team is constantly chasing down alerts that turn out to be low-priority, they’ll quickly lose faith in the system. This often happens when teams rely too heavily on a single metric. As experts from Optiv note, “prioritizing vulnerabilities solely based upon the CVSS scoring will not help security teams focus remediation efforts to address vulnerabilities with the highest risk for critical assets.” A vulnerability with a ‘critical’ CVSS score might pose little actual threat to your specific environment. True vulnerability and threat prioritization comes from enriching that base score with business context, asset criticality, and real-time threat intelligence.
Finally, even the best risk scoring model needs skilled people to run it. Implementing and maintaining a sophisticated framework requires a specific skillset that can be hard to find and expensive to hire. In fact, many organizations identify budget constraints and skill shortages as major barriers to improving their vulnerability management programs. Your team needs the capacity not just to operate the tools but also to interpret the results, fine-tune the scoring logic, and communicate risk effectively to the rest of the business. This is where automation and intuitive platforms become so important, as they help your existing staff work more efficiently and make a bigger impact without needing a dedicated data science team.
A solid risk scoring framework is built on a foundation of clear, consistent, and integrated practices. It’s not just about adopting a model; it’s about tailoring it to your environment and keeping it sharp. By focusing on a few key areas, you can create a system that delivers accurate, actionable insights and helps your team focus on the vulnerabilities that truly matter.
With the sheer volume of findings from security scanners, the prioritization of risk is more important than ever. Your first step is to define what risk means to your organization. Establish a clear set of baseline criteria that will be applied consistently across all assets. This should include standard metrics like CVSS scores but must also incorporate business context. What is the asset’s role? What data does it hold? Who uses it? Answering these questions helps you create a scoring rubric that reflects actual business impact, moving you away from generic severity ratings and toward a truly risk-based approach.
Your attack surface is not static, and neither is the threat landscape. A risk score calculated three months ago may be irrelevant today. That’s why continuous calibration is essential. As your asset inventory changes and new threats emerge, your model needs to adapt. Continuous scanning gives you the complete asset visibility needed to reduce blind spots and manage vulnerabilities across your entire attack surface. Regularly review and update your asset criticality ratings, integrate fresh threat intelligence, and adjust scoring logic as your business priorities evolve. This ensures your prioritization efforts remain accurate and aligned with your current security posture.
Your risk scoring framework becomes exponentially more powerful when it’s connected to the rest of your security ecosystem. A risk-based vulnerability management platform should ingest data from all your scanners, correlate it with threat intelligence, and help automate the response process. By integrating your scoring engine with your CMDB, asset management systems, and ticketing platforms, you create a seamless workflow. This integration provides the rich, contextual data needed for accurate scoring and ensures that prioritized vulnerabilities are quickly routed to the right teams for remediation, all within a unified platform.
What’s the real difference between a CVSS score and a risk score? Think of a CVSS score as a vulnerability’s technical rating in a perfect, isolated lab. It tells you how severe the flaw is on its own. A risk score, however, tells you how dangerous that same flaw is to your specific business. It adds essential context, like whether the vulnerability is on a critical server or a test machine, and if attackers are actually using it right now. A high CVSS score is a warning sign, but a high risk score is a call to action.
How do I start building a risk scoring model if I don’t have one? You don’t need a complex algorithm from day one. Start with the basics by identifying and tagging your most critical assets, the systems your business cannot function without. Then, layer in a standard severity metric like CVSS. The final, most important step is to integrate a source of real-time threat intelligence. This will show you which vulnerabilities have known exploits, allowing you to immediately focus on the intersection of critical assets and active threats.
Is Breach and Attack Simulation (BAS) really necessary if I have good risk scores? A risk score is an educated guess about your exposure, while a Breach and Attack Simulation is the proof. BAS validates your scores by safely testing if a high-risk vulnerability is actually exploitable in your environment. It also confirms whether your security controls are working as you expect. It’s the step that moves you from knowing your theoretical weaknesses to understanding your practical, real-world resilience.
My team is small. Is risk scoring too complex for us to implement? Actually, risk scoring is what makes it possible for a small team to be effective. Without it, you’re trying to fix everything at once. A solid risk scoring framework does the heavy lifting of analysis for you, automatically filtering thousands of vulnerabilities down to the handful that truly require your attention. This allows your team to stop wasting time on low-impact issues and focus their limited resources where they can make the biggest difference.
How often should I be re-evaluating my risk scores? Your risk scores should be re-evaluated continuously. Risk is not a static number you calculate once a quarter. The threat landscape changes daily, and your own IT environment is constantly evolving. An effective risk management program uses automation to constantly update scores as new threat intelligence becomes available or as changes are detected on your attack surface, ensuring your priorities are always based on the most current information.