Comprehensive Threat Exposure Management Platform
Your vulnerability scanner tells you that you have hundreds of “critical” issues, but your team only has the bandwidth to fix a handful this week. How do you choose? Relying on CVSS scores alone is a guessing game, as a high score doesn’t always mean high risk in your specific environment. You need to know which vulnerabilities are actually exploitable. This is where Breach and Attack Simulation (BAS) comes in, safely testing your defenses to validate your true exposure. Integrating this practical validation is a key feature of the most advanced tools for erm continuous threat monitoring, helping you move from theory to evidence-based action.
Before we get into the tools, let’s get on the same page about Enterprise Risk Management (ERM). It’s not just another compliance checkbox or a task for a siloed department. At its core, ERM is a company-wide strategy for identifying, assessing, and preparing for potential risks that could interfere with your operations and objectives. It’s about creating a culture where everyone makes smarter, more risk-aware decisions.
This holistic approach means looking beyond just IT and cybersecurity to consider risks across every part of the business—from finance and operations to HR and legal. The goal is to get a complete picture of your risk landscape so you can manage threats proactively instead of just reacting when something goes wrong. A modern ERM program gives you a unified view of cyber risks in one place, helping you focus on what truly matters.
Think of ERM as a game plan for the whole company. It’s a structured way to find, check, and manage potential pitfalls across all departments. Instead of each team handling risk in their own way, ERM brings everyone together under one cohesive strategy. This isn’t just about preventing losses; it’s also about spotting opportunities. By understanding your risks, you can make more confident decisions, whether that’s launching a new product or entering a new market. It’s a way of thinking that helps everyone in the company make smart choices by looking at both the potential downsides and the upsides.
In the past, risk assessments were often a once-a-year event. A team would spend weeks gathering data, creating a report that would sit on a shelf, and then everyone would get back to their day jobs. That approach just doesn’t work anymore. Threats like sophisticated cyberattacks, supply chain disruptions, and sudden regulatory changes are evolving faster than ever. An annual or quarterly snapshot of your risk posture is outdated almost as soon as it’s finished.
This is where continuous monitoring comes in. Instead of periodic check-ins, it involves constantly watching for risks across your entire organization. This approach gives you a live, up-to-the-minute feed of potential dangers, which is essential when you’re dealing with a threat landscape that changes daily. Keeping up with the latest threat advisories shows just how quickly new vulnerabilities can emerge.
Continuous monitoring gives you something that periodic assessments never can: real-time visibility. This is a complete game-changer for how you manage risk. When you can see what’s happening across your network and systems as it happens, you can move from a reactive to a proactive security posture. You’re no longer waiting for a problem to announce itself; you’re spotting the early warning signs and addressing them before they can cause real damage.
Companies that constantly monitor their environment are far better at anticipating changes, adjusting their strategies on the fly, and protecting their most critical assets. This immediate insight into your total attack surface improves not just your security but also your overall operations and business outcomes. It’s the difference between driving with a clear windshield versus only looking at the rearview mirror.
Moving from periodic check-ins to a continuous monitoring model is one of the most significant upgrades you can make to your security program. It’s the difference between looking at a static photograph of your risk landscape and watching a live video feed. A static picture is outdated the moment it’s taken, but a live feed gives you the real-time intelligence needed to make smart, timely decisions. This constant awareness allows your team to shift from a reactive stance, where you’re always playing catch-up, to a proactive one where you can anticipate and neutralize threats before they cause real damage. By integrating continuous monitoring, you’re not just improving a process; you’re fundamentally changing how you see and manage risk across your entire enterprise.
Traditional risk assessments are like a snapshot in time. They give you a clear picture of your vulnerabilities on the day of the scan, but your attack surface changes constantly. New assets come online, software gets updated, and threat actors develop new tactics. Relying on quarterly or even monthly assessments means you’re operating with outdated information, leaving significant gaps where threats can emerge unnoticed. These periodic evaluations can create a false sense of security, as you might be missing critical vulnerabilities that appear between scans. This approach keeps your team in a constant cycle of reaction, always addressing yesterday’s problems instead of preparing for tomorrow’s threats.
Continuous monitoring flips the script by providing a constant stream of data about your security posture. Instead of waiting for a scheduled scan, you get immediate alerts on new risks as they appear. This proactive approach helps you identify and address issues early, long before they can be exploited. Think of it like a factory getting an instant notification about a machine malfunction, rather than discovering it during a weekly inspection. This allows you to maintain operational resilience and build a more robust threat exposure management program. You can stop chasing down old vulnerabilities and start getting ahead of attackers by seeing what they see, as they see it.
Modern monitoring tools use automation to handle the heavy lifting of continuous scanning and data collection. This frees your team from the repetitive grind of manual checks and allows them to focus on what humans do best: analysis, strategy, and problem-solving. With a clear, up-to-the-minute view of your environment, your team can investigate issues faster and respond to incidents in real-time. This shift empowers you to move beyond simply patching vulnerabilities and start making strategic decisions based on a true understanding of your risk. It enables a more confident approach, where you can accurately prioritize threats and allocate resources where they’ll have the most impact.
When you’re evaluating continuous threat monitoring tools, the sheer number of features can feel overwhelming. It’s easy to get distracted by flashy but impractical functions. To cut through the noise, focus on the core capabilities that will actually make your security program more efficient and effective. The right tool should give you clarity, not more complexity. It needs to fit into your existing workflow, provide actionable intelligence, and help your team move faster. Let’s walk through the essential features that separate a must-have platform from just another tool in the stack.
Your team can’t afford to waste time hunting for information across disconnected systems. A quality tool gathers risk data from every corner of your organization and presents it in one unified place. Look for a solution that offers a centralized dashboard, giving you a single source of truth for your entire attack surface. This allows you to see everything at a glance, from asset inventories to vulnerability statuses. Effective tools create reports automatically and transform complex risk data into easy-to-understand visualizations. This consolidated view helps you connect the dots between different threats and assets, making it much easier to manage and prioritize your security efforts without getting lost in spreadsheets.
Modern threat landscapes move too fast for manual analysis alone. That’s why AI-powered threat detection is no longer a “nice-to-have”—it’s essential. The best ERM tools use AI and machine learning to analyze vast amounts of data, identify patterns, and predict potential risks before they can be exploited. Instead of just reacting to alerts, you can proactively address weaknesses that are most likely to be targeted. This capability allows you to focus on imminent risks and attacks, moving your team from a reactive posture to a predictive one. It’s about getting ahead of attackers by understanding your exposure through an intelligent, data-driven lens.
Alert fatigue is a real problem that can cause your team to miss critical threats. A top-tier continuous monitoring tool solves this with smart, automated alerts and reporting. Instead of flooding your inbox, the system should allow you to configure alerts for specific, high-priority events. Good tools automatically generate clear, concise reports tailored to different audiences, from technical teams to executive leadership. Some use AI to find hidden patterns in large datasets, which saves time and helps you spot emerging risks early. This automation frees up your team from manual report-building so they can concentrate on what truly matters: investigating and remediating threats.
A new tool should feel like a natural extension of your existing security stack, not a siloed island. Seamless integration is critical for a smooth workflow and a holistic view of your security posture. Before committing to a platform, check if it can easily connect with the other software your company relies on, such as your SIEM, SOAR, ticketing systems, and cloud environments. A tool with a robust API and pre-built connectors will ensure that data flows freely between systems. This creates a more cohesive and automated security ecosystem, allowing you to unify your cyber risk view and streamline everything from detection to remediation without disruptive manual processes.
Every security team operates a little differently, so a one-size-fits-all approach just doesn’t work. The right tool should be flexible enough to adapt to your organization’s unique processes. Look for customizable workflows that you can tailor to your specific needs, whether it’s for risk assessments, incident tracking, or remediation assignments. The platform should be intuitive and easy for your team to adopt. Make sure it has the specific tools your company needs and is flexible enough to grow with your business. A solution that molds to your team’s way of working will see much higher adoption and deliver far more value in the long run.
Choosing the right tool depends entirely on your organization’s specific needs, existing tech stack, and risk management goals. There are many great options out there, each with its own strengths. Let’s walk through some of the top contenders to see how they approach continuous monitoring and help you find the best fit for your team.
The Hive Pro Uni5 Xposure Platform is designed to provide a unified view of your cyber risks in a single place. It moves beyond traditional vulnerability management by offering a complete Continuous Threat Exposure Management (CTEM) solution. The platform continuously scans your entire attack surface, from internal assets to your external footprint, to identify potential exposures. What makes it stand out is its ability to prioritize threats using in-house intelligence from HiveForce Labs, helping your team focus on the risks that pose an immediate danger. This approach helps you shift from a reactive stance to proactive exposure reduction.
MetricStream is a well-regarded leader in the Governance, Risk, and Compliance (GRC) space. Teams often praise its user-friendly design and reliable support, making it a solid choice for organizations looking to build out their risk management capabilities. It provides a structured framework for managing risk across the enterprise.
Similarly, ServiceNow GRC simplifies risk assessments by using AI to manage issues more effectively. It’s known for its detailed reports and interactive charts, which give teams a clear, visual understanding of their risk landscape. This makes it easier to communicate risk posture to stakeholders and make informed decisions quickly.
OneTrust is particularly strong when it comes to managing risks from external vendors. It connects third-party risk management directly with security incident handling and helps ensure compliance with standards like ISO 27001. If vendor risk is a major concern for your organization, OneTrust offers specialized features to address it.
LogicGate, on the other hand, is known for its flexibility. It’s highly customizable, allowing you to connect risks to different business functions and tailor workflows to your specific processes. The platform also uses Monte Carlo simulations to show the potential financial impact of risks, giving you powerful data to guide strategic planning.
SecurityScorecard and Bitsight are leaders in the security ratings space, offering a unique, outside-in view of your organization’s security posture. These platforms continuously monitor your external attack surface, assigning an easy-to-understand score that reflects your security health. They are incredibly useful for third-party risk management, as you can also monitor the security ratings of your vendors and partners. This provides an objective, data-driven way to assess and compare security performance without needing direct access to internal systems.
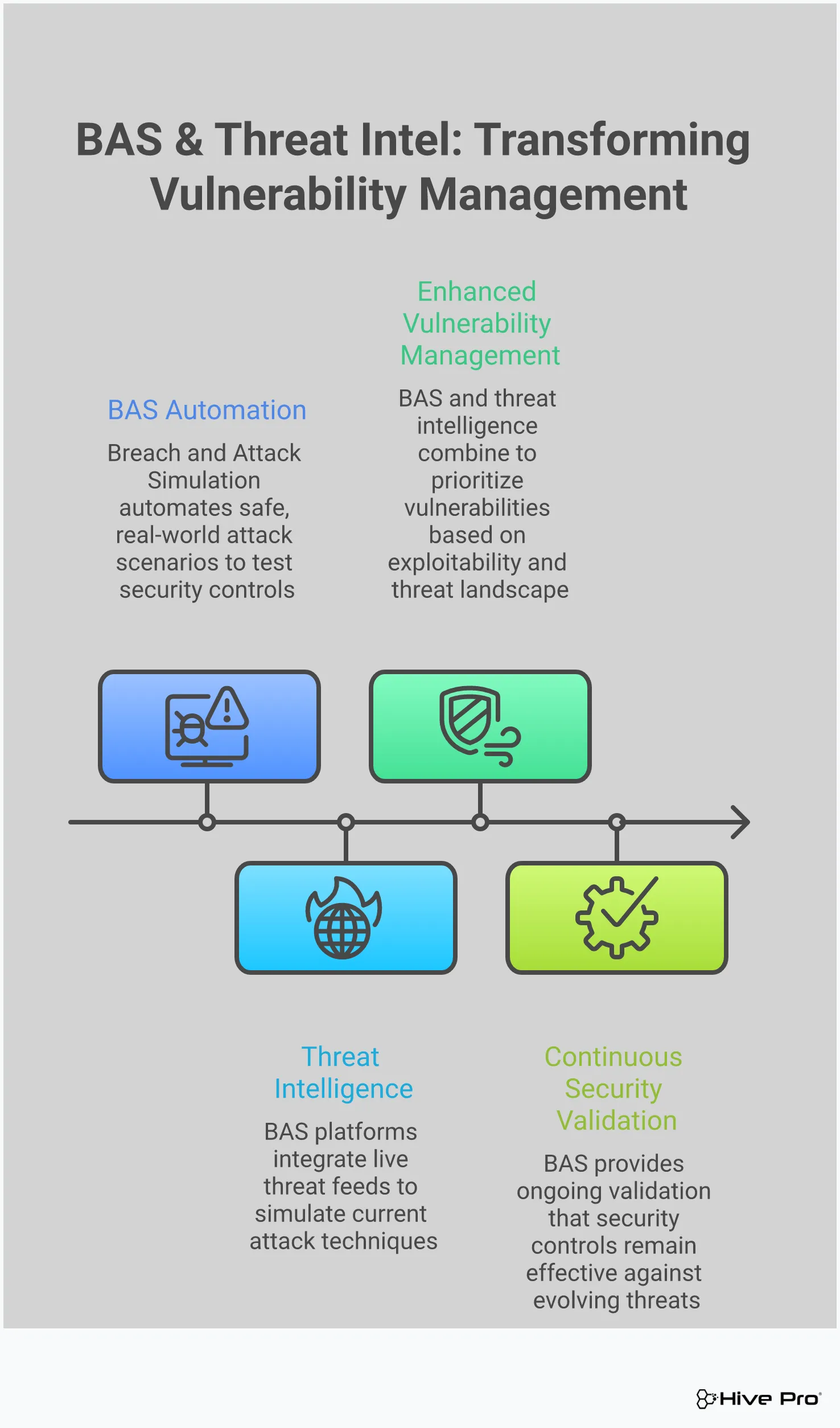
Continuous monitoring is a fantastic step up from periodic scans, but on its own, it can create a ton of noise. You get a constant stream of data about potential vulnerabilities, misconfigurations, and policy violations. The real challenge isn’t just seeing everything; it’s knowing what to look at first. This is where threat intelligence comes in. It acts as a powerful filter, turning that firehose of data into a focused, prioritized list of actionable tasks.
Think of threat intelligence as the context that gives your monitoring data meaning. It tells you which vulnerabilities are being actively exploited in the wild, which ones are being targeted by threat actors in your industry, and which ones are just theoretical risks. By integrating real-world threat data into your monitoring process, you can move beyond simply identifying weaknesses and start proactively managing your true exposure. This intelligence-led approach helps your team focus its limited time and resources on the threats that pose a genuine, immediate danger to your organization, making your entire security program more efficient and effective.
Without threat intelligence, vulnerability prioritization often defaults to relying solely on CVSS scores. While helpful, a high CVSS score doesn’t always translate to high real-world risk. A vulnerability might be technically severe but incredibly difficult to exploit, or it might exist in a non-critical, isolated system. Threat intelligence cuts through this ambiguity by highlighting which vulnerabilities are actually being used by attackers. This allows you to prioritize threats based on evidence, not just theory. Instead of chasing down every “critical” alert, your team can concentrate on the issues that attackers are actively targeting, ensuring your remediation efforts have the greatest possible impact on your security posture.
Knowing a vulnerability can be exploited is one thing; knowing it is being exploited right now is a game-changer. Timely threat intelligence provides crucial alerts about new exploits, malware campaigns, and active attacks targeting specific CVEs. This information is vital for a rapid response. When you learn that a vulnerability in your tech stack is being used in active campaigns, you can immediately escalate the patching process and hunt for any signs of compromise. This proactive stance, informed by up-to-the-minute threat advisories, helps you close critical security gaps before attackers can find them, significantly reducing your window of exposure.
Effective risk management requires seeing the bigger picture. Threat intelligence provides that broader context, offering insights into attacker tactics, techniques, and procedures (TTPs) and trends within your specific industry. Are threat actors targeting financial services with a new type of ransomware? Is there a surge in attacks against cloud infrastructure? Understanding the current threat landscape helps you anticipate potential attacks and make more strategic decisions. This context is also invaluable for communicating risk to leadership, as it helps you explain why a particular vulnerability is a priority and what the potential business impact of an attack could be.
Integrating threat intelligence transforms your continuous monitoring from a simple data collection exercise into a strategic exposure management program. It helps you validate whether your existing security controls are effective against the TTPs used by today’s attackers. This intelligence-driven approach reduces manual effort and eliminates the guesswork involved in prioritization. By focusing on validated, real-world threats, your team can stop wasting time on low-risk issues and dedicate their energy to strengthening defenses where it matters most. A unified threat exposure management platform brings this all together, giving you a clear, focused path to reducing your overall attack surface.
Think of Breach and Attack Simulation (BAS) as a continuous, automated fire drill for your security defenses. While traditional vulnerability management is great at finding potential weaknesses—like an unlocked door—BAS takes the next logical step. It actually tries to open the door, see what’s inside, and map out how far an intruder could get. It’s a proactive approach that moves you from a theoretical understanding of your risks to a practical one.
Instead of just relying on vulnerability scores, BAS platforms let you see exactly how an attack could play out in your specific environment. By safely simulating the latest real-world threats, you can test your security controls, validate your exposure, and find the gaps before an actual attacker does. This process provides concrete evidence of which vulnerabilities pose a genuine threat, allowing your team to focus its remediation efforts on what truly matters. It’s about shifting from asking “Are we vulnerable?” to answering “Are we exploitable?” with confidence.
Your security stack is made up of layers of controls—firewalls, endpoint detection, email filters—all designed to work together to stop an attack. But how do you know they’re configured correctly and actually doing their job? That’s where simulated attacks come in. A BAS platform acts like a dedicated sparring partner for your security team, constantly testing your defenses.
It takes intelligence on the latest threats and runs safe, controlled simulations of those exact attack techniques against your environment. This allows you to see, in real time, if your security tools detect and block the simulated threat as expected. It’s a practical way to find out if a misconfigured firewall rule or an overlooked policy gap could leave you exposed. This kind of adversarial exposure validation helps you find and fix weak spots before they can be exploited in a real breach.
A single vulnerability might not seem like a big deal on its own. But when chained together with other weaknesses, it can create a direct path to your most critical assets. BAS helps you see these attack paths by simulating entire real-world scenarios, from initial compromise to final objective. It doesn’t just test one control in isolation; it shows you how an attacker could move laterally across your network.
This process validates your true exposure by demonstrating whether a series of small weaknesses can be combined to create a major security incident. For example, a simulation might show how a phishing email could lead to credential theft, which then allows an attacker to access a sensitive database. This gives you a clear, evidence-based picture of your risk, helping you understand the potential impact of an attack and prioritize defenses accordingly.
Traditional security assessments like penetration tests are incredibly valuable, but they only provide a snapshot in time. Your environment is dynamic—new assets are added, software is updated, and configurations change daily. A clean bill of health from a pen test last quarter doesn’t guarantee you’re secure today. This is where the “continuous” part of BAS makes all the difference.
Unlike one-time tests, BAS platforms run simulations constantly, providing an ongoing feedback loop on your security posture. As your environment evolves and new threats emerge, BAS continuously validates that your controls are still effective. This automated, persistent testing ensures you can adapt quickly and maintain a strong defensive posture over time, rather than scrambling to catch up after a periodic assessment uncovers new issues.
Integrating BAS into your vulnerability management program fundamentally changes how you prioritize remediation. Instead of relying solely on CVSS scores and theoretical risk ratings, your team gets hard data on which vulnerabilities are actually exploitable in your environment. This allows you to focus your limited time and resources on fixing the problems that pose the most immediate danger.
This approach also makes conversations with IT and DevOps teams much more effective. Rather than just pointing to a high severity score, your team can provide a clear demonstration of how a specific vulnerability was used in a simulated attack to compromise a critical system. This evidence-based approach creates a compelling case for immediate action and helps streamline the entire vulnerability and threat prioritization process, making your entire security program more efficient and impactful.
Adopting a new continuous threat monitoring tool is a major step forward for any security program. But let’s be real—it’s not always as simple as flipping a switch. Even the best platforms can present challenges during rollout. The good news is that these hurdles are common, and with a bit of foresight, you can clear them without breaking a sweat.
Thinking through potential roadblocks ahead of time helps you create a smoother transition for your team and ensures you get the full value from your investment from day one. From managing the firehose of data to getting your team on board, here are the most frequent challenges you might face and, more importantly, how to handle them.
Continuous monitoring generates a massive amount of data, and it’s easy to get lost in the noise. When your team is buried in alerts, they can’t focus on the threats that truly matter. This is a classic case of “too much of a good thing.” Organizations often struggle to sift through vast amounts of data to find the critical risks, leading to alert fatigue and missed threats.
The solution isn’t less data; it’s better focus. Look for a tool that offers intelligent vulnerability and threat prioritization. A platform that uses threat intelligence and understands your unique business context can automatically surface the most urgent issues, allowing your team to stop chasing ghosts and concentrate on genuine exposures.
Your security stack is likely a mix of new and old technologies. Getting a new monitoring tool to communicate effectively with your existing legacy systems can be a significant technical challenge. Poor integration creates data silos, leaving you with blind spots and an incomplete picture of your risk landscape. You can’t protect what you can’t see, and disconnected systems are a major barrier to comprehensive visibility.
To avoid this, prioritize platforms designed for seamless integration. Look for robust API support and a wide range of pre-built connectors for the tools you already use. A unified platform that brings data from various sources into a single view can eliminate the headaches of trying to stitch together disparate systems on your own.
People are often the biggest hurdle in any technology implementation. Your team might see a new tool as just another complicated system to learn or a threat to their established workflows. This resistance can slow down adoption and prevent you from realizing the tool’s full potential. It’s crucial to address these concerns head-on by clearly communicating the benefits.
Frame the new tool as a way to make their jobs easier, not harder. Emphasize how it automates tedious tasks and helps everyone focus on more strategic work. Involve your team in the selection and implementation process, and provide thorough training to build their confidence. When your team understands the “why” behind the change, they’re more likely to become champions for it.
Security budgets are always under scrutiny, and you need to prove that any new investment is worth it. The perception that advanced monitoring solutions are too expensive can stop a project before it even starts. Similarly, if your team is already stretched thin, the idea of adding another tool to manage can seem overwhelming.
Shift the conversation from cost to value. A continuous monitoring tool isn’t just an expense; it’s an investment in risk reduction that prevents far more costly breaches. Build a strong business case that highlights the ROI through improved efficiency and proactive threat mitigation. Look for scalable solutions that offer automation to help your lean team accomplish more with less, turning your security program into a force multiplier.
Bringing a new tool into your workflow can feel like a huge undertaking, but a solid plan makes all the difference. It’s not just about flipping a switch; it’s about integrating a new capability that makes your entire security program stronger. A thoughtful implementation ensures you get the most value from your investment right from the start and helps your team feel confident instead of overwhelmed.
The key is to approach it strategically. By setting clear expectations, preparing your team, leaning on the tool’s strengths, and committing to a cycle of review and improvement, you can make the transition seamless. This isn’t just about installing software—it’s about evolving your approach to risk management. Let’s walk through the four essential steps to get you there.
Before you do anything else, define what success looks like. What specific problems are you trying to solve with a continuous monitoring tool? Getting clear on your objectives will not only guide your implementation but also help you demonstrate the tool’s value to leadership. Instead of vague goals, focus on tangible outcomes. For example, you might aim to reduce the time it takes to detect critical vulnerabilities or decrease the number of security incidents over a quarter.
To track your progress, establish key performance indicators (KPIs) from day one. These could include metrics like the rate of risk remediation, the speed of your team’s response to alerts, or improvements in your compliance posture. Having these numbers handy makes it easy to show how your new threat exposure management platform is directly contributing to a stronger, more resilient security program.
A new tool is only as effective as the people using it. To get your team on board, involve them in the process early and provide comprehensive training. The goal is to show them how this new system helps them do their jobs better, not just adds another task to their list. When your team understands the “why” behind the change and feels confident using the new platform, they become active participants in building a more risk-aware culture.
Focus training on practical, role-specific workflows. Show your vulnerability management team how to use automated prioritization to focus their efforts, and demonstrate to the SOC team how real-time alerts can speed up incident response. Technology alone can’t solve every problem; your team’s expertise is your greatest asset. Empowering them with the right skills ensures they can leverage the new tool to its full potential.
One of the biggest advantages of a modern ERM tool is automation. Let the platform handle the repetitive, time-consuming tasks so your team can focus on what humans do best: strategic analysis and problem-solving. Automated tools can continuously scan your attack surface, correlate threat intelligence, and prioritize risks without manual intervention, freeing up your security experts to work on high-impact remediation projects.
Think of automation as a force multiplier for your team. Instead of spending hours sifting through vulnerability data, your analysts can use that time to investigate the most critical threats identified by the system. By automating routine checks and data collection, you not only improve efficiency but also reduce the chance of human error. This allows your team to move faster and make more informed decisions, turning reactive clean-up efforts into proactive defense.
Implementing a continuous monitoring tool isn’t a one-and-done project. To get long-term value, you need to build a process for regular review and optimization. Your risk landscape is constantly changing, and your strategy should adapt along with it. Schedule periodic check-ins to assess your performance against the goals you set, review the effectiveness of your workflows, and identify areas for improvement.
Keep your risk register dynamic and up-to-date. As new threats emerge or your infrastructure changes, make sure those updates are reflected in your monitoring strategy. This continuous feedback loop is central to a mature vulnerability and threat prioritization program. By consistently refining your approach, you ensure your team is always focused on the most significant risks and that your security posture is continuously improving.
Finding the right continuous monitoring solution is less about picking the one with the most features and more about finding the one that fits your specific needs. A tool that works wonders for a financial institution might be overkill for a retail company. To make the right choice, you need to look inward at your own organization first. By focusing on your unique risks, existing tech stack, and long-term goals, you can select a platform that acts as a true partner in reducing your threat exposure.
Before you start scheduling demos, take the time to map out your organization’s specific risks. What are your most critical assets? Which compliance frameworks do you need to adhere to, like PCI DSS or HIPAA? Understanding where monitoring will deliver the most value is the first step. A clear picture of your risk profile helps you filter out solutions that don’t address your primary concerns. This isn’t just about technology; it’s about aligning your security strategy with your business objectives to ensure you’re protecting what matters most. A complete view of your total attack surface is fundamental to this process.
A powerful monitoring tool that doesn’t communicate with your existing systems will create more problems than it solves. Look for a solution with a robust API and pre-built integrations for your SIEM, ticketing systems, and other security tools. The goal is to create a unified workflow, not another data silo. Think about the future, too. Your company is going to grow, and your security needs will evolve. Choose a platform that can scale with you, whether that means monitoring new cloud environments or handling a larger volume of data without a drop in performance.
It’s easy to get sticker shock, but the initial cost of a tool is only part of the story. A better approach is to consider the return on investment (ROI). Think about the potential savings from preventing a single major breach, the reduction in manual hours your team spends on tracking vulnerabilities, or even lower cyber insurance premiums. A good continuous monitoring solution is an investment that pays for itself by reducing losses and improving operational efficiency. When you present the business case, focus on the value it delivers, not just the line item in the budget.
Beyond high-level integrations, you need to confirm that a new tool will fit neatly into your current tech stack. The solution should connect easily with the software your teams already rely on, from developer tools to IT service management platforms. This ensures that information can flow freely and efficiently, providing a single source of truth for your security posture. When data from your vulnerability scanners and asset inventories feeds directly into your monitoring platform, you can prioritize threats more effectively and streamline your remediation efforts, turning insights into action much faster.
Choosing the right continuous monitoring tool is a huge step, but the real work begins with implementation. A great tool can fall flat without a solid plan for integrating it into your team’s daily workflow. Success isn’t just about technology; it’s about people and processes. By focusing on a few key practices, you can make sure your new tool delivers on its promise and becomes an indispensable part of your security strategy. These steps will help you build a strong foundation, ensuring your team is prepared, your goals are clear, and your approach is built to last.
A new tool can’t do its job in a vacuum. For continuous monitoring to be effective, everyone in the organization needs to understand their role in managing risk. Technology alone isn’t a silver bullet; it’s an enabler for a security-conscious team. Your goal is to create an environment where employees see risk monitoring as a shared responsibility that protects the company, not just another task from the security department. Good communication and ongoing training are essential. When people understand the “why” behind the tool, they become active participants in finding and flagging potential issues, creating a much stronger defense.
Before you roll out your new tool, you need to define what success looks like. What specific outcomes are you aiming for? Are you trying to shorten your remediation times, improve compliance reporting, or get better visibility into your total attack surface? Setting clear objectives and key performance indicators (KPIs) from the start gives you a benchmark to measure progress. You’ll want to track metrics like how frequently risks are assessed, how quickly your team addresses identified threats, and whether your overall compliance posture improves. These KPIs will help you demonstrate the tool’s value and identify areas where your process needs adjustment.
Continuous monitoring isn’t a “set it and forget it” activity. The threat landscape is always changing, and your risk management process should adapt along with it. Think of your implementation as the starting point of an ongoing cycle of review and refinement. Use the real-time data and automated reports from your tool to find bottlenecks and opportunities for improvement. Are alerts being handled efficiently? Is the vulnerability prioritization helping your team focus on what matters most? Regularly asking these questions and tweaking your workflows ensures your program stays effective and efficient over time.
Your team is your greatest asset in risk management, so investing in their success is critical. Get key people involved in the implementation process early, and provide thorough training that shows them how the new tool makes their work easier and more impactful. It’s also helpful to involve experts from different departments when identifying risks to ensure you’re getting a complete picture. Engagement doesn’t stop after the initial training. Hold regular check-ins, share success stories, and provide ongoing education to keep everyone’s skills sharp. When your team feels confident using the tool, they’ll be more proactive in managing threats.
My team is already drowning in alerts. Won’t continuous monitoring just add to the noise? That’s a completely valid concern, and it’s one of the biggest misconceptions about this approach. The goal of a modern continuous monitoring platform isn’t to give you more alerts, but to give you smarter ones. It uses threat intelligence to act as a filter, cutting through the noise to show you which vulnerabilities are actually being exploited by attackers right now. This allows your team to stop chasing down every low-risk finding and focus their energy on the threats that pose a genuine danger to your business.
How is Breach and Attack Simulation (BAS) different from the penetration tests we already do? Think of it this way: a penetration test is like hiring an inspector for a deep, one-time evaluation of your house. It’s incredibly valuable for finding hidden issues, but it only gives you a snapshot of your security on that specific day. A BAS platform is more like a 24/7 security system that is constantly and automatically testing your locks, windows, and alarms. It provides a continuous feedback loop, ensuring your defenses are working as expected even as your environment and the threat landscape change daily.
We’re a smaller team with a limited budget. Is a continuous threat exposure management platform realistic for us? Absolutely. In fact, smaller teams often get the most value out of these platforms. When you’re short on time and people, you can’t afford to waste effort on low-priority tasks. A good tool automates the tedious work of scanning and data collection, acting as a force multiplier for your team. By automatically prioritizing the most critical risks, it allows your team to be far more efficient and strategic, ensuring their limited time is spent on work that has the biggest impact on your security.
What’s the first practical step to move from periodic scans to a continuous monitoring model? The best way to start is by focusing on what matters most. Instead of trying to boil the ocean and monitor everything at once, identify your most critical business assets—the systems and data that are absolutely essential to your operations. Begin your continuous monitoring journey there. By starting with a narrow, high-impact scope, you can demonstrate the value quickly and build a strong case for expanding the program across the rest of the organization.
How does threat intelligence really change how we handle vulnerabilities? Threat intelligence adds crucial real-world context to your vulnerability data. Without it, you’re often just prioritizing based on a theoretical severity score, like a CVSS rating. Threat intelligence tells you which of those vulnerabilities are being actively targeted by attackers in the wild. It’s the difference between knowing a window is unlocked and knowing a burglar is walking down your street checking for unlocked windows. This insight allows you to prioritize fixes based on immediate, tangible risk, not just theory.