Comprehensive Threat Exposure Management Platform
Your security team runs scans from five different tools. Each one gives you a different number of assets, a different count of vulnerabilities, and a different view of your risk. Meanwhile, your CMDB is outdated, shadow IT keeps expanding, and nobody can confidently answer a basic question: “What do we actually have, and where are we exposed?”
This is the problem Cyber Asset Attack Surface Management (CAASM) was built to solve. CAASM creates a unified, continuously updated inventory of every asset in your environment by aggregating data from the security and IT tools you already use, then maps those assets to their exposures.
This guide explains what CAASM is, how it works, how it differs from related approaches like EASM and CSPM, and why it has become essential for organizations serious about reducing their attack surface.
See how Uni5 Xposure delivers complete cyber asset visibility across your entire attack surface →
Cyber Asset Attack Surface Management (CAASM) is a technology category that aggregates, normalizes, and correlates asset data from multiple internal and external sources to create a comprehensive, unified view of an organization’s cyber asset inventory and associated exposures.
The term was coined by Gartner to describe a growing need: security teams operate dozens of tools, each scanning a slice of the environment, but no single tool provides a complete picture. CAASM platforms integrate with these existing tools through APIs, pulling asset and vulnerability data into one place without deploying additional agents or scanners.
The core value of CAASM is visibility. You cannot protect what you cannot see, and most organizations significantly undercount their assets. Research consistently shows that the average enterprise has 20-30% more assets than what appears in their CMDB. CAASM closes that gap by cross-referencing data from every source: vulnerability scanners, endpoint detection and response (EDR) tools, cloud security posture management (CSPM) platforms, IT service management (ITSM) databases, and identity providers.
CAASM platforms follow a systematic process to build and maintain a complete asset inventory:
CAASM connects to your existing security and IT infrastructure through API integrations. Common data sources include:
The key distinction: CAASM does not scan your environment itself. It aggregates data from tools that already do, which means zero additional network overhead and no new agents to deploy.
Different tools describe the same asset differently. Your vulnerability scanner might identify a server by its IP address, your EDR by its hostname, and your cloud platform by its instance ID. CAASM normalizes these records and deduplicates them, creating a single authoritative record for each unique asset.
This deduplication is critical. Without it, organizations routinely overcount assets (inflating risk) or undercount them (creating blind spots). A well-implemented CAASM solution typically resolves 15-25% duplicate records across data sources.
Once assets are identified and deduplicated, CAASM enriches each record with context from across all integrated sources:
With a complete, enriched asset inventory, CAASM can identify coverage gaps that individual tools miss:
These gaps represent your highest-risk blind spots. An unscanned asset with no endpoint protection is an open door that no amount of vulnerability prioritization can address.
CAASM is often confused with related security categories. Here is how they differ:
| Attribute | CAASM | EASM | CSPM |
|---|---|---|---|
| Full Name | Cyber Asset Attack Surface Management | External Attack Surface Management | Cloud Security Posture Management |
| Scope | All assets (internal + external) | External-facing assets only | Cloud infrastructure only |
| Discovery Method | API-based aggregation from existing tools | Outside-in scanning and reconnaissance | Cloud API queries and policy checks |
| Primary Value | Complete asset inventory and gap analysis | Unknown external exposure discovery | Cloud misconfiguration detection |
| Deployment Impact | No new agents or scanners | No internal access needed | Cloud-native integrations |
| Best For | Asset visibility and coverage gap identification | Shadow IT and external exposure | Cloud compliance and configuration |
The critical point: these categories are complementary, not competing. EASM discovers what is exposed externally. CSPM monitors your cloud configurations. CAASM unifies everything into a single asset-centric view that connects internal and external data.
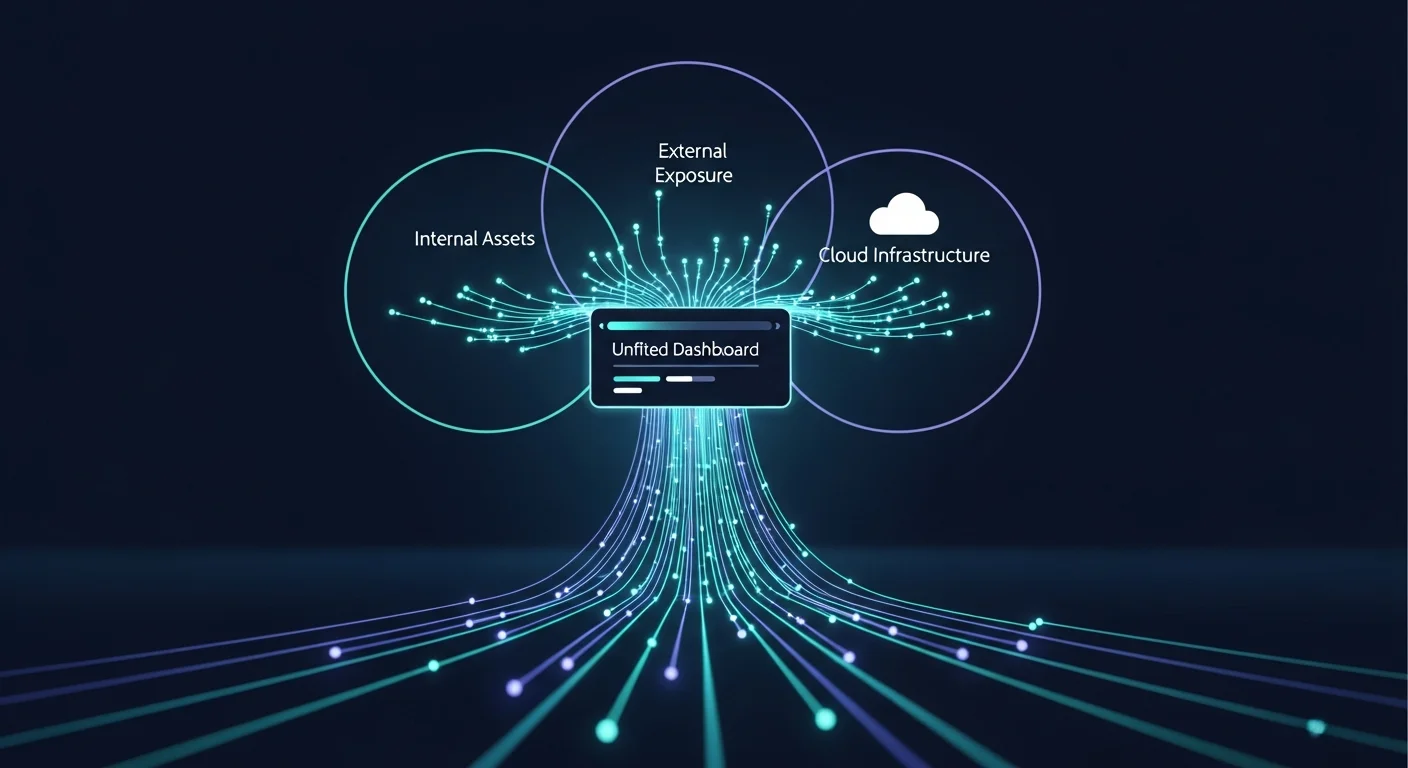
Organizations that deploy all three capabilities together, ideally within a unified platform, achieve the most complete visibility of their attack surface.
When evaluating CAASM solutions, look for these core capabilities:
The value of CAASM is directly proportional to how many data sources it can ingest. Leading platforms integrate with 50 or more security and IT tools out of the box. The more sources connected, the more complete and accurate the asset inventory becomes.
The platform must automatically match and merge records across data sources without manual mapping. This requires sophisticated correlation logic that goes beyond simple hostname or IP matching, handling dynamic IPs, ephemeral cloud instances, and containerized workloads.
Security teams need to answer complex questions: “Show me all internet-facing servers running unpatched Apache with no EDR agent.” A strong CAASM platform provides a flexible query interface that lets analysts explore the asset inventory and build custom reports for compliance, risk, and operational purposes.
Visual dashboards that immediately highlight where security tool coverage is incomplete: which assets lack vulnerability scanning, which endpoints are missing EDR, which cloud resources are not monitored. These dashboards drive remediation priorities.
Define security policies (e.g., “every production server must have EDR + vulnerability scanning + backup agent”) and have the platform continuously validate compliance against those policies, alerting when drift occurs.
CAASM addresses several persistent challenges that plague security teams:
The average data breach goes undetected for 204 days. Many of these breaches begin with assets that security teams did not know existed or did not adequately monitor. CAASM eliminates blind spots by ensuring every asset is accounted for and assigned appropriate security controls.
When a new critical vulnerability is disclosed, your team needs to answer quickly: “How many of our assets are affected?” Without CAASM, this question triggers a multi-day fire drill across multiple tool consoles. With CAASM, the answer is a single query against the unified inventory.
Raw CVSS scores do not account for asset context. A critical vulnerability on an isolated test server is not the same risk as the same vulnerability on a customer-facing database. CAASM provides the asset context that enables intelligent vulnerability prioritization, moving beyond severity scores to real business risk.
Regulatory frameworks like PCI DSS, HIPAA, and SOC 2 require accurate asset inventories and evidence that security controls cover the complete environment. CAASM provides the automated, continuously updated documentation that auditors need, replacing spreadsheet-based asset tracking.
Gartner’s Continuous Threat Exposure Management (CTEM) framework positions CAASM as the foundation layer. You cannot manage exposure across assets you do not know about.
Within the five stages of CTEM, CAASM plays a direct role:
For security leaders building a CTEM program, CAASM is not optional. It is the data foundation that every other capability depends on. Without accurate, complete asset visibility, prioritization is incomplete, validation is unfocused, and remediation lacks context.
Platforms like Uni5 Xposure integrate CAASM capabilities directly into the CTEM workflow, aggregating data from existing scanners and IT tools into a unified asset and exposure view that drives every downstream security decision.

Discover how Uni5 Xposure’s Total Attack Surface Management gives you complete asset visibility →
CAASM stands for Cyber Asset Attack Surface Management. It is a technology category defined by Gartner that focuses on creating a unified inventory of all cyber assets by aggregating data from existing security and IT tools through API integrations.
CAASM aggregates data from internal and external tools to create a complete asset inventory (inside-out view). EASM discovers and monitors externally facing assets from an attacker’s perspective (outside-in view). They are complementary: EASM finds what is exposed, CAASM unifies everything into a single inventory.
No. CAASM does not scan for vulnerabilities itself. It aggregates and normalizes data from your existing vulnerability scanners, EDR tools, cloud platforms, and other sources. CAASM adds value on top of scanners by providing complete asset visibility and identifying coverage gaps.
CAASM provides the asset context that vulnerability management programs need for accurate prioritization. By knowing which assets are business-critical, internet-facing, or lacking security controls, teams can focus remediation on the exposures that represent the highest real risk.
Yes. Gartner positions CAASM as a foundational capability within the CTEM framework. CAASM provides the comprehensive asset inventory that powers every stage of CTEM, from scoping and discovery through prioritization, validation, and mobilization.
Cyber Asset Attack Surface Management solves one of security’s most persistent problems: knowing exactly what you have and where it is exposed. By aggregating data from every security and IT tool in your environment, CAASM creates the single source of truth that every other security capability depends on.
The organizations that manage their exposure most effectively are not the ones with the most scanners. They are the ones that have unified their asset intelligence into a continuous, comprehensive view that drives prioritized action. Without CAASM, your CTEM program is built on incomplete data, and incomplete data leads to incomplete protection.