Comprehensive Threat Exposure Management Platform
Hive Pro recognized in Gartner® Magic Quadrant™ for Exposure Assessment Platform, 2025 Watch platform in action
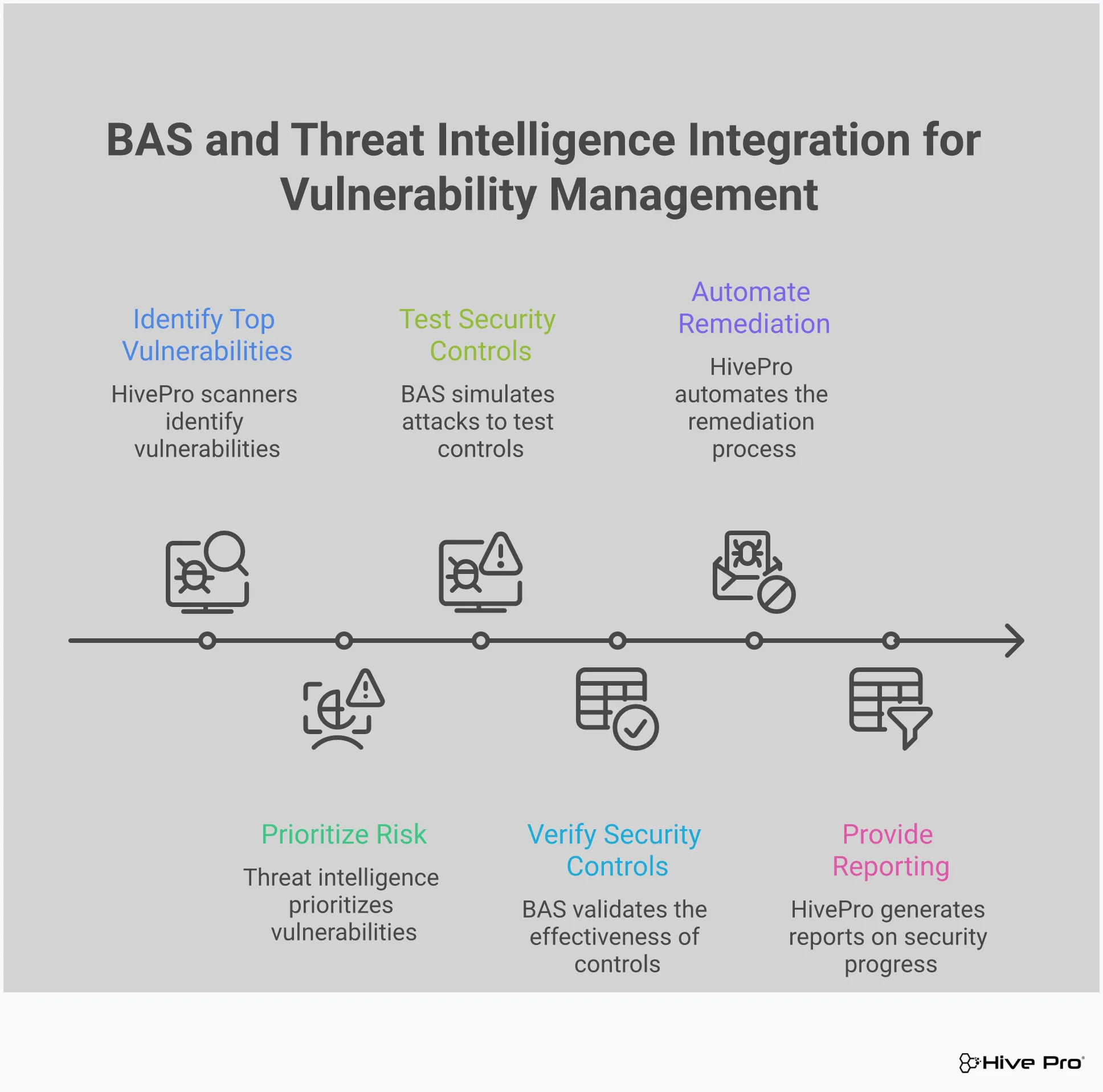
Knowing you have vulnerabilities is one thing; knowing if your defenses can actually stop an attack is another. Traditional vulnerability scanners tell you where the holes are, but they don’t tell you if your security controls are configured correctly or if they’ll perform under pressure. This is where Breach and Attack Simulation (BAS) becomes essential. By safely simulating real-world attack techniques, you can validate your security stack and find gaps before an adversary does. A truly comprehensive Qualys replacement solution goes beyond simple scanning to include these validation capabilities, helping you answer the critical question: “Are we secure?” with confidence, not guesswork.
For years, Qualys has been a familiar name in vulnerability management. But the security landscape is constantly changing, and what worked yesterday might not be enough to handle the threats of tomorrow. Many security teams are finding that legacy tools aren’t keeping up with their needs, prompting them to look for alternatives that offer more flexibility, better performance, and a clearer view of their true risk.
One of the most common frustrations is the tool’s operational footprint. Some users report that Qualys scans can slow down websites and that the platform requires a significant amount of setup and a large team to manage effectively. For organizations that need to stay agile, a resource-intensive tool can become a bottleneck, slowing down both security and development workflows. The goal is to secure the business, not hinder its performance.
Functionality gaps are another major driver. Since Qualys is cloud-based, it can’t scan systems that aren’t connected to the internet, leaving a critical blind spot for organizations with on-premise or air-gapped assets. Teams are also looking for more comprehensive platforms that consolidate security functions. Many want a solution that goes beyond basic scanning to include features like threat hunting or email security in a single interface.
In today’s interconnected environments, integration is everything. A security tool that doesn’t play well with your existing stack is more of a liability than an asset. Teams find that weak correlation and few integrations can create blind spots across the attack surface, especially in complex cloud and hybrid setups. Without a unified view, you can’t accurately assess your exposure or prioritize remediation efforts, leaving you guessing about where your most critical risks truly lie.
If you’re feeling limited by traditional vulnerability scanners, it’s worth looking at platforms built for today’s threat landscape. Hive Pro offers a fresh, integrated approach to threat exposure management that moves beyond simple scanning and reporting. Instead of just identifying vulnerabilities, Hive Pro helps you see your entire attack surface, prioritize the threats that actually matter, and validate that your defenses are working as expected. It’s a complete platform designed to shift your team from a reactive cycle of patching to a proactive strategy of exposure reduction. By bringing together asset discovery, vulnerability prioritization, and security control validation, Hive Pro gives you a single, unified view of your cyber risk. This holistic perspective is a significant departure from legacy tools that often operate in silos, leaving you to piece together the full picture. The goal is to move from asking “Are we vulnerable?” to confidently answering “Where are we exposed, and what should we fix first?” This shift in focus helps security teams work more efficiently, reduce alert fatigue, and demonstrate measurable improvements in their security posture to leadership. It’s about making threat management a more strategic, data-driven function within your organization.
Juggling multiple security tools is a common headache. One tool for asset discovery, another for vulnerability scanning, and a third for reporting creates silos and makes it difficult to see the big picture. Hive Pro’s Uni5 Xposure Platform brings all these functions together. This unified approach streamlines your security workflows and provides a single source of truth for your entire threat exposure program. Instead of patching together data from different systems, your team gets a cohesive, real-time view of your security posture. This means less time spent on manual data correlation and more time focused on reducing risk. It’s about making threat exposure management simpler and more effective.
Not all vulnerabilities are created equal. A long list of CVEs without context can lead to alert fatigue and wasted effort on low-risk issues. Hive Pro tackles this problem with intelligence from HiveForce Labs, its in-house threat research team. This team provides crucial context, like which vulnerabilities are being actively exploited in the wild and which are trending among threat actors. This intelligence-driven approach to vulnerability and threat prioritization helps you cut through the noise. Your team can confidently focus its remediation efforts on the handful of threats that pose a genuine, immediate risk to your organization, ensuring your most critical assets are protected first.
How do you know if your security controls will actually stop an attack? With Hive Pro, you don’t have to guess. The platform includes Breach and Attack Simulation (BAS) capabilities, allowing you to safely run real-world attack scenarios against your environment. This process of adversarial exposure validation tests your defenses to see how they perform under pressure. You can identify gaps in your security posture, from misconfigured firewalls to ineffective endpoint protection, before an attacker does. It’s a practical way to measure your security effectiveness, justify security investments, and continuously harden your defenses against the tactics that attackers are using right now.
You can’t protect what you can’t see. In today’s complex IT environments, assets can easily go untracked, creating dangerous blind spots for security teams. Hive Pro provides total attack surface management by continuously scanning your entire environment, including on-premise infrastructure, cloud instances, web applications, and operational technology. This comprehensive discovery process ensures you have a complete and up-to-date inventory of all your assets and their associated vulnerabilities. By eliminating blind spots, you get a true understanding of your organization’s exposure. This complete visibility is the foundation of a strong security program, allowing you to apply policies and controls consistently across your entire digital footprint.
When you start exploring the market, you’ll find several strong Qualys alternatives, each with its own approach to vulnerability and exposure management. While some are direct competitors offering similar enterprise-level scanning, others focus on specific areas like endpoint protection or cloud security. Understanding these key players and their strengths can help you narrow down what your team truly needs from a modern security platform. Let’s look at four popular options that security teams often consider.
Tenable is a well-known name in the vulnerability management space and a direct competitor to Qualys. Its platform helps organizations identify weaknesses across their infrastructure, secure cloud environments, and manage identity-related risks. A key advantage for some teams is that Tenable offers flexible deployment, including on-premises solutions, not just cloud-based ones. Users often praise its ability to provide real-time risk insights. However, some have pointed out that certain dashboards can experience delays in updating, which might be a consideration if your team needs instantaneous data refreshes across all views.
Rapid7 is frequently highlighted as a strong alternative for its focus on integrated security operations. The platform is designed to bring all your security data into one place, offering a more unified and user-friendly way to monitor your security posture. This contrasts with a common criticism of Qualys, where users sometimes find it challenging to connect disparate information or struggle with tool compatibility. By consolidating security information, Rapid7’s Insight platform aims to give teams a clearer, more cohesive view of their vulnerabilities and potential threats without leaving gaps in coverage.
CrowdStrike takes a different approach by focusing on cloud-native endpoint protection. Its Falcon platform is a comprehensive solution built to detect and respond to threats across all your devices. Beyond just vulnerability management, it includes next-gen antivirus capabilities and delivers valuable cyber threat intelligence. One of CrowdStrike’s biggest selling points is its single, lightweight sensor. This design minimizes the impact on your network and system performance while continuously monitoring for attacks, making it an efficient choice for teams prioritizing endpoint security without sacrificing performance.
For organizations heavily invested in the Microsoft ecosystem, Microsoft Defender for Cloud is a natural and powerful choice. This solution excels at identifying and mitigating threats within Azure and hybrid cloud environments. It helps teams maintain compliance with security standards, scan for vulnerabilities, and provides security management for DevOps pipelines. Because it integrates so seamlessly with other Microsoft products, it offers a streamlined experience and a holistic view of security health for any organization that relies on Azure for its core operations.
When you’re considering a move from an established tool like Qualys, you’re not just looking for a one-to-one replacement. You’re looking for an upgrade. The right alternative should do more than just scan for vulnerabilities; it should fit seamlessly into your existing workflow, provide clearer insights, and ultimately make your security program more effective. The goal is to find a platform that addresses the complexities of modern IT environments, where assets are spread across on-premise servers, cloud instances, and remote endpoints.
A great alternative moves beyond simple vulnerability lists and helps you understand your true exposure. It should connect the dots between a technical flaw, the threat actors exploiting it, and the potential business impact. This means prioritizing what actually matters, not just what has the highest CVSS score. As you evaluate your options, focus on solutions that offer a more holistic and proactive approach to threat exposure management. Look for key features that streamline your processes, from discovery and prioritization to validation and remediation. The best tools give you the clarity and confidence to act decisively.
Static vulnerability data becomes outdated almost as soon as it’s generated. A superior Qualys alternative must be powered by real-time threat intelligence that shows you what attackers are doing right now. This isn’t just about knowing a vulnerability exists; it’s about knowing if it’s being actively exploited in the wild. Getting timely risk insights is crucial for effective vulnerability management because it allows you to focus your team’s limited resources on the threats that pose an immediate danger. With up-to-the-minute information from sources like HiveForce Labs, you can shift from a reactive posture to a proactive one, fixing the most critical gaps before they can be compromised.
Your security tools should reduce complexity, not add to it. An intuitive user interface is essential because it allows your team to find the information they need without fighting the software. A clean, well-designed dashboard makes it easy to visualize your attack surface, understand risk priorities, and track remediation progress at a glance. This is especially important for communicating risk to leadership, who need clear, concise data to make informed decisions. When a platform is easy to use, your team can work more efficiently, respond faster, and spend less time on training and more time securing your organization.
Every organization’s infrastructure is different. Whether you’re fully in the cloud, on-premise, or running a hybrid model, your security tools need to fit your environment. A strong Qualys alternative offers flexible deployment options, allowing you to choose the setup that works best for your specific needs. This adaptability ensures you can get complete visibility across all your assets without having to re-architect your network. A solution that supports both cloud and on-premise deployments gives you the freedom to scale and evolve your security program as your business grows, ensuring consistent protection across your entire attack surface.
While security is a critical investment, budget is always a factor. The best alternatives offer transparent, cost-effective pricing that provides clear value for your money. It’s not about finding the cheapest option, but about finding a solution with a predictable cost structure that aligns with the features you actually need. Look for platforms that don’t surprise you with hidden fees for essential capabilities like API access or standard support. A worthwhile investment will demonstrate its return by reducing your mean time to remediate (MTTR), preventing costly breaches, and improving the overall efficiency of your security operations.
If you’ve ever stared at a list of thousands of “critical” vulnerabilities, you know the feeling of being overwhelmed. Legacy vulnerability scanners are great at finding flaws, but they often fall short in helping you figure out what to fix first. A high CVSS score doesn’t automatically mean a high risk to your specific organization, leaving you with a mountain of data and the impossible task of deciding which alerts represent a genuine, immediate threat. This constant guesswork leads to alert fatigue and a reactive security posture where teams are always playing catch-up.
Modern threat exposure management platforms move beyond these simple scores. They help you see the bigger picture by adding layers of context that legacy tools miss. Instead of just showing you a list of problems, they show you a clear path to reducing your actual risk. This smarter approach focuses on three key areas: understanding the business context of an asset, assessing the real-world impact of a breach, and knowing which vulnerabilities are actively being exploited by attackers right now. By combining these elements, you can finally move from a reactive cycle of patching to a proactive strategy that protects what matters most to your business.
A vulnerability’s technical severity is only half the story. A critical flaw on an internal development server simply doesn’t carry the same weight as a medium-level flaw on your primary e-commerce database. Modern platforms help you understand this difference by incorporating business context into their risk scoring. They allow you to tag critical assets, identify systems that process sensitive data, and map out revenue-generating applications. This approach helps you prioritize threats and vulnerabilities based on their importance to your business operations. Instead of treating every asset as equal, you can focus your team’s limited time and resources on the vulnerabilities that pose the greatest risk to your most valuable systems.
Communicating cyber risk to leadership can be a challenge when you’re speaking in technical terms. Reporting “500 new critical vulnerabilities” often doesn’t resonate in the boardroom. A more effective approach is to translate that technical data into potential business impact. Modern alternatives excel at this, helping you quantify risk in financial terms that everyone can understand. Instead of just listing vulnerabilities, these platforms can help you report on the “estimated potential loss from exploitable flaws on revenue-generating systems.” This reframes the conversation from a technical issue to a business risk. By connecting vulnerabilities to their potential financial impact, you can make a much stronger case for securing the resources you need for remediation.
Not all vulnerabilities are created equal, and the ones being actively exploited in the wild should be at the very top of your to-do list. A theoretical vulnerability is a risk, but a vulnerability with a known, weaponized exploit is a clear and present danger. Modern platforms integrate real-time threat intelligence to give you this crucial insight. By continuously monitoring the threat landscape, these tools can tell you which vulnerabilities are being targeted by ransomware gangs or other threat groups. This intelligence, often curated by in-house research teams like HiveForce Labs, allows you to cut through the noise. You can immediately focus on patching the flaws that attackers are using today, rather than wasting cycles on vulnerabilities that pose little immediate threat.
If vulnerability scans tell you where the holes are in your fortress walls, Breach and Attack Simulation (BAS) tells you if your guards are actually paying attention. It’s a proactive approach that moves beyond just listing potential weaknesses. Instead, BAS tools safely launch simulated attacks, mimicking the exact techniques real-world adversaries use to see how your defenses hold up. This isn’t about finding more vulnerabilities; it’s about testing the security controls you already have in place.
Think of it as a continuous, automated penetration test. BAS helps you answer critical questions like, “Would our EDR solution actually stop this specific ransomware strain?” or “Is our firewall configured to block this command-and-control traffic?” By running these constant, safe attack simulations, you get real, evidence-based insight into your security posture. This process is a core part of modern adversarial exposure validation, helping you confirm that your security investments are delivering the protection you expect. It transforms your security strategy from a reactive guessing game into a confident, proactive operation.
You’ve invested heavily in firewalls, endpoint detection and response (EDR), and other security tools. But how do you know they’re working correctly and configured optimally? BAS provides the answer by continuously validating their effectiveness. It runs simulations of known attacker behaviors to check if your controls can prevent, detect, or generate an alert for malicious activity.
This isn’t a simple pass or fail test. It provides detailed feedback on why a control might have failed, pointing to specific misconfigurations or gaps in coverage. By turning theoretical risk into verified performance data, you can fine-tune your security stack and ensure it’s providing the protection you paid for. It’s the difference between hoping you’re secure and proving it every single day.
Vulnerability scans are great at finding known software flaws, but they don’t always see the bigger picture. An attacker’s path is rarely a straight line; they move laterally, escalate privileges, and chain together seemingly low-risk issues to achieve their goals. BAS tools are designed to think like an attacker, simulating multi-stage campaigns to uncover the hidden pathways and gaps in your defenses that a simple scan would miss.
By emulating the entire attack lifecycle, BAS can reveal weaknesses in your network segmentation, identity and access management policies, or detection logic. This allows you to proactively close these gaps before a real adversary can discover and exploit them, strengthening your overall defensive posture against sophisticated threats.
An incident response (IR) plan that only exists on paper is not much of a plan at all. BAS offers a safe and controlled way to pressure-test your procedures and your team’s readiness. By launching realistic attack scenarios based on frameworks like MITRE ATT&CK, you can see how your security operations team actually responds. Do the right alerts fire? Does your team follow the playbook? How quickly can they contain the simulated threat?
These simulations act as practical drills for your security team, helping them build muscle memory and refine their response processes without the stress of a real breach. It’s an invaluable way to ensure that when a real attack happens, your team is prepared to act swiftly and effectively.
One of the biggest challenges in cybersecurity is demonstrating improvement. BAS provides the concrete data you need to measure your security posture and track its progress. By establishing a baseline of your defensive capabilities, you can run simulations after making changes, like implementing a new security control or updating a policy, to see the tangible impact.
This gives you clear, quantifiable metrics to share with leadership, justifying security budgets and proving the value of your team’s efforts. With a platform that offers a unified view of cyber risks, you can easily monitor your performance, identify areas for improvement, and show a clear trend of risk reduction over time. It’s about making security a measurable and continuously improving function of the business.
Vulnerability scanners are great at finding flaws, but they often leave you with a mountain of data and not much direction. When every vulnerability is labeled “critical,” how do you decide what to fix first? This is where threat intelligence comes in. It adds the real-world context you need to move from a reactive, checklist-based approach to a proactive, risk-based one. Instead of just knowing you have vulnerabilities, you start to understand which ones actually pose a threat to your organization.
Think of it as a filter for the noise. Threat intelligence helps you see which vulnerabilities are being actively discussed by threat actors, which have public exploits available, and which are being used in current campaigns. This insight allows your team to stop chasing every potential issue and start focusing on the ones that are most likely to be exploited. By integrating this intelligence, you can transform your vulnerability management program from a simple scanning-and-patching cycle into a strategic defense mechanism that prioritizes the threats that matter most. This is the core of modern vulnerability and threat prioritization.
Your scanner just returned thousands of vulnerabilities, and hundreds are marked “critical.” The reality is, your team can’t fix all of them at once. Threat intelligence helps you answer the most important question: “What should we fix right now?” It shines a spotlight on the vulnerabilities that have known exploits and are being actively used by attackers in the wild. This allows you to shift the conversation from “We have 500 critical vulnerabilities” to “We have 15 vulnerabilities on revenue-generating systems that are being actively exploited, with a potential business impact of $2 million.” This change in perspective, backed by timely threat advisories, turns an overwhelming list into a manageable, prioritized action plan.
Without threat intelligence, remediation often feels like a guessing game. Teams might patch based on CVSS scores alone, which don’t account for the current threat landscape or the business context of the affected asset. This can lead to wasted effort on vulnerabilities that are unlikely to ever be exploited. By using intelligence from research teams like HiveForce Labs, you can focus your resources where they’ll have the greatest impact. You can prioritize patching a lower-scored vulnerability on a critical, internet-facing server over a higher-scored one on an isolated, internal system with no known exploit. This targeted approach ensures your remediation efforts are directly aligned with reducing your organization’s actual risk exposure.
Security teams are constantly bombarded with alerts, and it’s easy to become desensitized. Alert fatigue is a real problem that can cause critical threats to be overlooked. Threat intelligence provides the crucial context needed to validate and prioritize alerts, effectively cutting down on the noise. When you can see that a vulnerability alert is for a system with compensating controls, or that there’s no known exploit code available, you can safely de-prioritize it. A unified threat exposure management platform that incorporates this intelligence helps your team concentrate on legitimate threats, making them more efficient and effective while reducing the risk of burnout.
Switching from a familiar tool like Qualys is a big decision, and it’s worth taking the time to get it right. The market is full of options, each with its own strengths. To find the best fit for your organization, you need a clear set of criteria to measure each potential solution against. Think of this as your roadmap for evaluating alternatives. It’s not just about finding a tool that scans for vulnerabilities; it’s about finding a partner in your security program.
A great alternative should do more than just replicate what you already have. It should simplify your workflows, provide clearer insights, and integrate smoothly into the way your team already works. It needs to be able to grow with you as your attack surface expands and the threat landscape evolves. As you review different platforms, use this checklist to guide your conversations and demos. It will help you cut through the marketing noise and focus on the capabilities that will actually make a difference in strengthening your security posture and making your team’s life easier.
Your vulnerability management tool can’t operate in a silo. For it to be truly effective, it must connect seamlessly with the other security and IT tools you rely on every day. Think about your SIEM, SOAR, ticketing systems, and patch management solutions. A strong alternative will offer pre-built integrations or a flexible API that allows you to create a unified workflow. This ensures that vulnerability data flows where it needs to, enriching other systems and speeding up remediation. Without this, you risk creating information gaps and manual processes that slow your team down. Before you commit, map out your existing stack and verify that the new tool can become a central part of it.
Your business isn’t static, and your security platform shouldn’t be either. As your organization grows, so will your attack surface. You might expand into new cloud environments, adopt more IoT devices, or spin up new applications. Your chosen Qualys alternative must be able to scale effortlessly to cover all these new assets without a drop in performance. When evaluating options, ask about their capacity to handle a growing number of assets and data points. Consider whether you need a platform that offers more than just vulnerability management. A solution that provides a complete view of your attack surface can offer more long-term value as your security program matures.
Demonstrating compliance and communicating risk are two of the most important functions of any security program. Your vulnerability management tool should make this easy with clear, customizable reporting. You need dashboards that can give your technical team the granular details they need while also providing high-level summaries for executives and auditors. Look for a solution that can map vulnerabilities to specific compliance frameworks like PCI DSS, HIPAA, or NIST. A key metric like “total risk remediated” can powerfully illustrate the effectiveness of your program. The right reporting features transform raw data into a compelling story about how you’re reducing the organization’s risk.
Even the most intuitive platform can present challenges, and that’s when you’ll be glad you chose a vendor with excellent support. During your evaluation, dig into the quality of customer support. What are their response time SLAs? Do they offer a dedicated customer success manager? Look at reviews and ask for references to get a real sense of their reputation. The implementation process is just as important. A smooth and well-guided onboarding can set your team up for success from day one. Clarify what the deployment model looks like, whether it’s cloud-native, on-premises, or hybrid, and what level of assistance you can expect during the transition.
Making the move from a familiar tool like Qualys is a big decision, but it doesn’t have to be a painful one. A successful transition comes down to thoughtful planning and clear communication. When you know what to expect, you can anticipate challenges and set your team up for a smooth switch. Think of it less as ripping out an old system and more as upgrading your capabilities. By focusing on a few key areas, you can manage the process effectively and start seeing the benefits of a modern threat exposure management platform much faster.
Before you flip the switch, you need a solid plan for your data. Your historical vulnerability data, asset inventories, and remediation tickets hold valuable context. The key is to identify what you truly need to carry over. Start by asking what problem you’re trying to solve with the new tool and how it fits into your existing systems. You’ll want to migrate active vulnerability data and asset information, but you might decide to archive older, closed-out vulnerabilities. Work with your new vendor to understand their import processes and what data formats they support. A good partner will guide you through this to ensure a seamless transfer of essential information without cluttering your new platform.
One of the main reasons teams move on from older tools is their lack of connectivity. Qualys, for example, often struggles to integrate smoothly, which can create blind spots in your security coverage, especially in cloud environments. Switching platforms is your chance to build a more cohesive security stack. Begin by mapping out all your current integrations, from ticketing systems and SIEMs to patch management tools. Then, confirm your chosen alternative provides robust, pre-built integrations or a flexible API. A platform like Hive Pro Uni5 is designed to connect your tools, ensuring data flows freely and your security program operates as a single, unified system.
Even the most intuitive platform has a learning curve. To get the full value from your new investment, your team needs to know how to use it effectively. When evaluating options, consider the user interface and how well it aligns with your team’s current workflows. Will they need specialized training? Most modern vendors offer a variety of training resources, including live onboarding sessions, extensive documentation, and on-demand video tutorials. You can also implement a phased rollout, starting with a small group of power users who can then help train the rest of the team. This approach makes the transition more manageable and helps build internal expertise from day one.
A formal change management plan is your roadmap for a successful transition. This document should outline everything from timelines and key milestones to individual roles and responsibilities. It’s also your primary tool for communicating with stakeholders. Be sure to explain the “why” behind the switch, focusing on how the new platform will help the team work more efficiently and better protect the organization. An effective vulnerability management program relies on its team, and getting their buy-in is critical. A clear plan minimizes disruption, manages expectations, and ensures everyone understands their part in making the switch a success.
Switching your vulnerability management platform is a big move, and you’ll want to prove it was the right one. Success isn’t just about how your team feels using the new tool; it’s about demonstrating tangible improvements with clear data. Tracking the right key performance indicators (KPIs) will show you exactly how the new solution is impacting your security posture and team efficiency. By focusing on a few key areas, you can build a powerful case that showcases the value of your investment and helps justify the change to leadership. These metrics move the conversation from subjective opinions to objective facts, highlighting real progress in your security program.
How quickly can your team spot a new vulnerability, and how long does it take to fix it? These two questions are at the heart of Mean Time to Detect (MTTD) and Mean Time to Remediate (MTTR). These are some of the most critical vulnerability management metrics you can track because they directly measure your team’s agility. After switching to a new platform, you should see a significant drop in both of these numbers. A shorter detection time means your new tool provides better visibility, while a faster remediation time shows it’s helping your team prioritize effectively and take action. This is proof that you’re not just working, you’re working smarter and faster.
Speed is important, but so is thoroughness. Patch compliance measures how effectively you’re applying fixes across your environment, while vulnerability recurrence tracks whether old issues are popping back up. A great Qualys alternative should help you improve both. With better prioritization, your team can focus on the patches that matter most, leading to a higher compliance rate. You should also see fewer recurring vulnerabilities, which indicates that your fixes are sticking. This shows your remediation efforts are becoming more strategic and permanent, not just a temporary game of whack-a-mole. Tracking the total risk remediated gives you a powerful way to illustrate this progress to management.
Ultimately, the goal of any security tool is to make the business safer. The most impactful way to measure success is by showing a clear reduction in overall organizational risk. Instead of just reporting on the number of critical vulnerabilities you’ve patched, a modern platform helps you communicate risk in business terms. For example, you can shift from saying “we fixed 500 critical vulnerabilities” to “we reduced our potential financial exposure from key assets by 40%.” This approach connects security efforts directly to business outcomes, which is exactly what your leadership wants to see. A platform with strong vulnerability and threat prioritization capabilities is essential for achieving and demonstrating this kind of risk reduction.
My team is already overwhelmed with alerts. How does a modern platform help with that instead of just adding more noise? That’s a common and completely valid concern. A modern platform’s goal is to reduce noise, not add to it. It does this by adding layers of context that legacy scanners lack. Instead of just giving you a long list of technical flaws, it uses real-time threat intelligence to show you which vulnerabilities are actually being exploited by attackers right now. It also helps you map your assets to business functions, so you can see which flaws pose a genuine risk to your most critical systems. The result is a much shorter, more manageable list of priorities that allows your team to focus on the handful of threats that truly matter.
You mentioned Breach and Attack Simulation (BAS). How is that different from the penetration tests we already do? Think of it as the difference between an annual physical and a continuous heart rate monitor. A penetration test is a valuable, point-in-time assessment, usually done once or twice a year by an external team. Breach and Attack Simulation, on the other hand, is an automated and continuous process. It safely runs thousands of simulated attacks against your security controls every day, giving you constant, real-time feedback on whether your defenses are working as expected. This allows you to find and fix configuration drifts or security gaps as they happen, not months later.
We rely heavily on CVSS scores for prioritization. Why isn’t that enough anymore? CVSS scores are a good starting point for understanding the technical severity of a vulnerability, but they don’t tell the whole story. A high score doesn’t necessarily mean a high risk to your specific organization. It’s missing two crucial pieces of context: the threat landscape and your business environment. A vulnerability with a medium CVSS score on a critical, internet-facing server that is being actively exploited by ransomware groups is a much higher priority than a “critical” vulnerability on an isolated, internal test server with no known exploit. Modern platforms add this context to help you see your true risk.
Switching platforms sounds like a huge project. What’s the most important thing to get right during the transition? A successful transition really comes down to planning your integrations. A major reason teams look for alternatives is that their old tool didn’t connect well with their other systems, creating manual work and information silos. Before you switch, map out how your new platform will connect to your ticketing system, SIEM, and patch management tools. A smooth flow of data between these systems is what will ultimately make your team more efficient and speed up your response times. Getting this right from the start ensures you get the full value of your new investment.
How can I prove to my leadership that switching was the right decision? The best way is to show a measurable reduction in risk. Instead of just reporting on the number of patches you’ve applied, focus on metrics that connect to business outcomes. Track your team’s Mean Time to Remediate (MTTR) to show you’re fixing critical issues faster. You can also report on the reduction of risk for your most important assets, framing it in terms of protecting revenue-generating applications or sensitive customer data. When you can say, “We reduced the exposure on our most critical systems by 40% this quarter,” you’re speaking a language that clearly demonstrates the value of the new platform.