Comprehensive Threat Exposure Management
Uni5 Xposure is comprised of exposure assessment and cyber validation, two robust features that enable you to see every asset, scan from code to cloud, monitor external threats, test your defenses, prioritize your risks, and facilitate full remediation.
All of this in one platform and at an unbeatable value.
Integrate with your asset scanners, CMDB, and asset inventory tools to inventory and catalog all assets and configurations.
Wherever you deploy, leverage unmatched flexibility, scalability, and control to optimize security efficiency.
Evaluate your asset criticality, set your risk parameters, and define your regulatory alignment needs.
Involve SecOps, IT, DevOps, pentesters, and more with RBAC to ensure secure and enhanced collaboration.

Our native scanners and EASM seamlessly identify, assess, and report the vulnerabilities, misconfigurations, and security findings across code, web, mobile applications, networks, cloud and container services for comprehensive security management. See the attacker’s perspective with EASM.
Uni5 Xposure supports BYO scanners, testsm and tools, enhancing flexibility and integrating diverse security technologies for robust visibility and protection. Best yet, you can manage all of your scanners and tools from our platform.
Uni5 Xposure enables the upload of manual configuration tests, assessments and pen-tests, allowing for customized security evaluations and enhanced visibility into unique risks. No finding goes unnoticed.
Uni5 Xposure maps asset security coverage, identifying managed and unmanaged assets and detailing the reach and gaps of your scanning efforts across all assets.

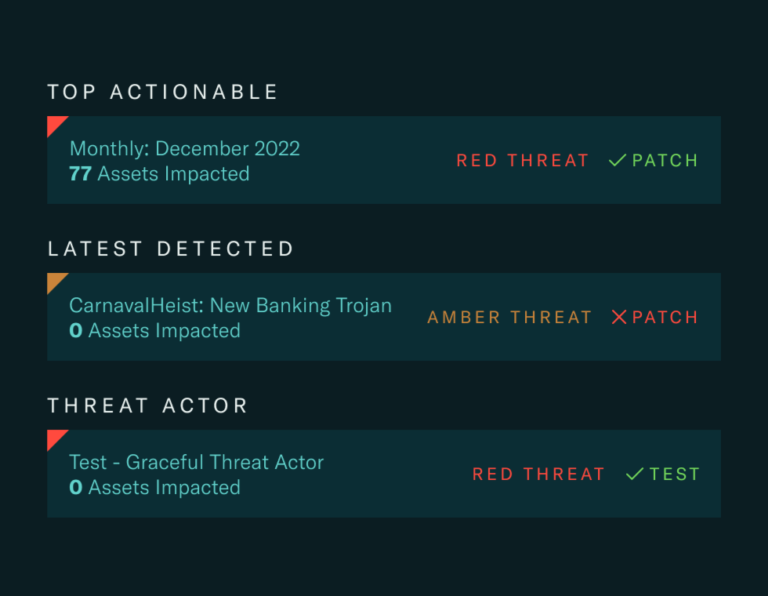
Incorporates multiple factors like wormability, zero-day status, and dark web discussions, offering a nuanced vulnerability risk assessment.
Analyzes vulnerabilities for exploitation likelihood by threat actors, tailoring responses to specific business verticals and geographic threats.
Adjusts vulnerabilities’ priorities based on real-time simulations and control effectiveness, ensuring prioritization mirrors the current security posture.
Combines over 210,000 CVEs, 210+ threat actors, and 3,000+ attacks with specialized intelligence for informed decision-making and targeted remediation.

Identifies what assets are currently covered by scanners and which are not, delineating managed versus unmanaged assets to highlight security blind spots.
Offers immediate feedback on the effectiveness of existing security measures, allowing for quick recalibration of defenses against identified weaknesses.
Adjusts the priority of vulnerabilities based on real-time simulation outcomes and the evolving landscape of threat actor tactics, providing a current view of the organization’s most pressing risks.
Regularly updates the validation process to incorporate new threat data and intelligence, ensuring the organization’s defenses evolve in step with the changing tactics of adversaries.

Utilizes advanced indicators of compromise (IoC) intelligence to provide detailed context for each threat, enhancing the specificity and relevance of remediation actions.
Leverages a vast repository of patch intelligence to inform remediation strategies, ensuring that all vulnerabilities are addressed with the most effective and up-to-date patches.
Bi-directional integrations with patch management, ITSM, and ticketing systems ensure that remediation efforts are synchronized across all operational platforms, enhancing the speed and efficiency of the security response.
Provides continuous feedback on the success of remediation efforts, allowing for real-time adjustments, patch revalidation, and ongoing improvement of the security posture.

Complete Asset Visibility
Integrate with your asset scanners, CMDB, and asset inventory tools to inventory and catalog all assets and configurations.
Deploy on Cloud-Hybrid-On Prem
Wherever you deploy, leverage unmatched flexibility, scalability, and control to optimize security efficiency.
Customize Your Risk Language
Evaluate your asset criticality, set your risk parameters, and define your regulatory alignment needs.
Involve The Right People w/ RBAC
Involve SecOps, IT, DevOps, pentesters, and more with RBAC to ensure secure and enhanced collaboration.

6 Out-of-the-Box Scanners & EASM
Our native scanners and EASM seamlessly identify, assess, and report the vulnerabilities, misconfigurations, and security findings across code, web, mobile applications, networks, cloud and container services for comprehensive security management. See the attacker’s perspective with EASM.
Uni5 Xposure supports BYO scanners, testsm and tools, enhancing flexibility and integrating diverse security technologies for robust visibility and protection. Best yet, you can manage all of your scanners and tools from our platform.
Uni5 Xposure enables the upload of manual configuration tests, assessments and pen-tests, allowing for customized security evaluations and enhanced visibility into unique risks. No finding goes unnoticed.
Uni5 Xposure maps asset security coverage, identifying managed and unmanaged assets and detailing the reach and gaps of your scanning efforts across all assets.

Incorporates multiple factors like wormability, zero-day status, and dark web discussions, offering a nuanced vulnerability risk assessment.
Analyzes vulnerabilities for exploitation likelihood by threat actors, tailoring responses to specific business verticals and geographic threats.
Adjusts vulnerabilities’ priorities based on real-time simulations and control effectiveness, ensuring prioritization mirrors the current security posture.
Combines over 210,000 CVEs, 210+ threat actors, and 3,000+ attacks with specialized intelligence for informed decision-making and targeted remediation.

Identifies what assets are currently covered by scanners and which are not, delineating managed versus unmanaged assets to highlight security blind spots.
Offers immediate feedback on the effectiveness of existing security measures, allowing for quick recalibration of defenses against identified weaknesses.
Adjusts the priority of vulnerabilities based on real-time simulation outcomes and the evolving landscape of threat actor tactics, providing a current view of the organization’s most pressing risks.
Regularly updates the validation process to incorporate new threat data and intelligence, ensuring the organization’s defenses evolve in step with the changing tactics of adversaries.
Utilizes advanced indicators of compromise (IoC) intelligence to provide detailed context for each threat, enhancing the specificity and relevance of remediation actions.
Leverages a vast repository of patch intelligence to inform remediation strategies, ensuring that all vulnerabilities are addressed with the most effective and up-to-date patches.
Bi-directional integrations with patch management, ITSM, and ticketing systems ensure that remediation efforts are synchronized across all operational platforms, enhancing the speed and efficiency of the security response.
Provides continuous feedback on the success of remediation efforts, allowing for real-time adjustments, patch revalidation, and ongoing improvement of the security posture.
Why Hive Pro?
Our company is built by a team of cybersecurity experts with decades of experience. We joined together on a mission to give you the best visibility of your threat exposure so that you can outpace threat actors and improve your cyber resilience.
About Us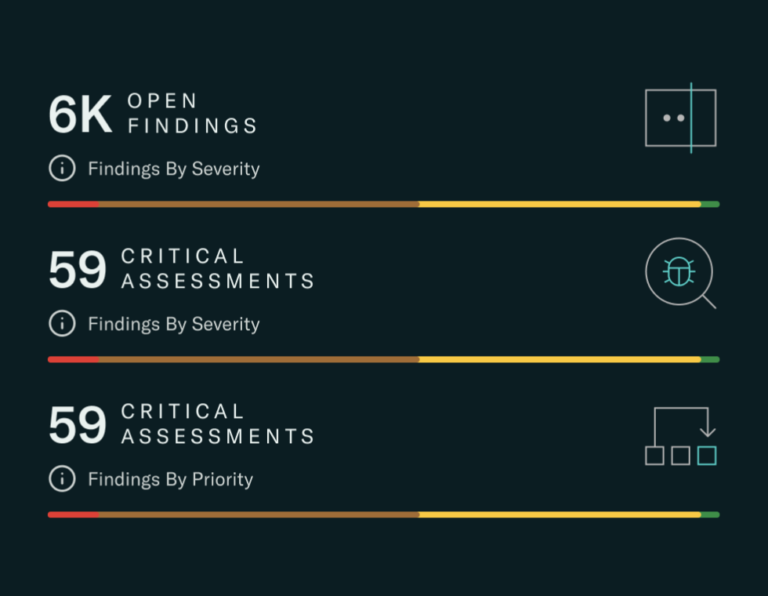
From Pen-Tests to Scans and Assessments
Your single source of truth for all manual pen tests, automated scans, external assessments cloud findings and attack surface management results from code-to-cloud.
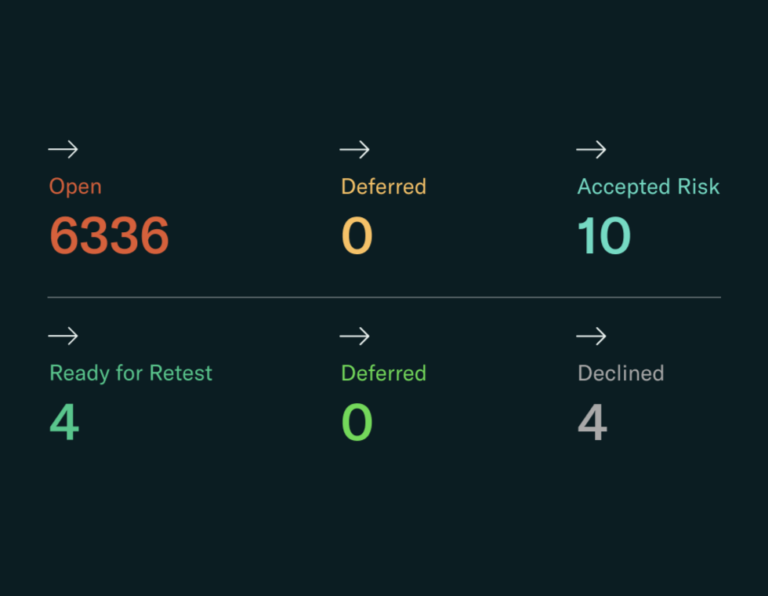
Proactively identify, prioritize, and remediate threat exposure all in one platform. Validate controls for their true efficacy and strength. Ensure continuous defense adaptation ahead of threats rather than responding post-incident.
Of The Evolving Threat Landscape
HiveForce Labs, our in-house intelligence services continuously update threat, attacker, attack, vulnerability, IoC, and patch intelligence in both platforms so you never miss a beat.

With built-in RBAC and multiple channels to alert, communicate and collaborate, Uni5 Xposure streamlines threat exposure management with the right stakeholders involved every step of the way towards remediation.
See how different teams benefit from Hive Pro
HiveForce Labs staying ahead of the evolving Threat Landscape
HiveForce Labs, our in-house intelligence services continuously embed threat, vulnerability, IoC, attack, threat actor and patch intelligence in Uni5 Xposure so you’re always informed.
Book a DemoUni5 Xposure
Perfect fit for every Industry
Eliminating threat exposure and building resilience across every industry.
Meet stringent compliance requirements (e.g., GDPR, SOX, PCI-DSS) through continuous monitoring and proactive vulnerability and exposure management.
Leverages threat intelligence and IoC data to anticipate and mitigate sophisticated cyber crime tactics.
Ensures the security and integrity of sensitive financial data with encrypted asset management and risk-based vulnerability prioritization.
Utilizes attack simulations to simulate financial-specific cyber threats, enhancing readiness and response strategies.
Prioritizes and addresses vulnerabilities that pose the highest risk to financial stability and customer trust.

Ensures high availability of network services through proactive exposure management and rapid remediation of vulnerabilities.
Identifies and mitigates risks to critical network infrastructure, preventing costly downtimes and service interruptions.
Supports large and complex network environments with scalable vulnerability assessments and security validations.
Conducts detailed breach simulations to test the resilience of network defenses against evolving cyber threats.
Maps and monitors every network component to ensure complete security coverage and control.
Strengthens defenses against state-sponsored cyber threats and espionage with high-level threat simulations and continuous exposure assessments.
Implements stringent controls to protect sensitive public sector information, ensuring trust and compliance with legal standards.
Employs prioritization algorithms to focus limited resources on mitigating the most critical vulnerabilities affecting public services.
Facilitates secure and efficient information sharing between governmental agencies with validated security controls.
Provides decision-makers with actionable insights for developing resilient long-term cybersecurity strategies in the public sector.

Helps maintain HIPAA compliance through continuous monitoring and validation of security controls.
Prioritizes the security of sensitive patient information through targeted vulnerability management and encryption.
Utilizes updated threat intelligence to prevent and respond to ransomware attacks, crucial for maintaining healthcare operations.
Uses enriched IoC intelligence to quickly detect and neutralize threats specific to healthcare systems.
Extends security measures to IoT and medical devices, protecting against unique vulnerabilities in healthcare technology.


Meet stringent compliance requirements (e.g., GDPR, SOX, PCI-DSS) through continuous monitoring and proactive vulnerability and exposure management.
Leverages threat intelligence and IoC data to anticipate and mitigate sophisticated cyber crime tactics.
Ensures the security and integrity of sensitive financial data with encrypted asset management and risk-based vulnerability prioritization.
Utilizes attack simulations to simulate financial-specific cyber threats, enhancing readiness and response strategies.
Prioritizes and addresses vulnerabilities that pose the highest risk to financial stability and customer trust.
Ensures high availability of network services through proactive exposure management and rapid remediation of vulnerabilities.
Identifies and mitigates risks to critical network infrastructure, preventing costly downtimes and service interruptions.
Supports large and complex network environments with scalable vulnerability assessments and security validations.
Conducts detailed breach simulations to test the resilience of network defenses against evolving cyber threats.
Maps and monitors every network component to ensure complete security coverage and control.

Strengthens defenses against state-sponsored cyber threats and espionage with high-level threat simulations and continuous exposure assessments.
Implements stringent controls to protect sensitive public sector information, ensuring trust and compliance with legal standards.
Employs prioritization algorithms to focus limited resources on mitigating the most critical vulnerabilities affecting public services.
Facilitates secure and efficient information sharing between governmental agencies with validated security controls.
Provides decision-makers with actionable insights for developing resilient long-term cybersecurity strategies in the public sector.

Helps maintain HIPAA compliance through continuous monitoring and validation of security controls.
Prioritizes the security of sensitive patient information through targeted vulnerability management and encryption.
Utilizes updated threat intelligence to prevent and respond to ransomware attacks, crucial for maintaining healthcare operations.
Uses enriched IoC intelligence to quickly detect and neutralize threats specific to healthcare systems.
Extends security measures to IoT and medical devices, protecting against unique vulnerabilities in healthcare technology.